Remote Access / TLS + User Auth - Connection up but no LAN
-
@Jarhead and @viragomann
I have checked it and corrected it. Yes you were right I messed it up.
I still get on the client this "Authenticate/Decrypt packet error: packet HMAC authentication failed" error. So i exported the CA and Client certifcate new.
Could it be because I used an ECDSA?
Keytype: ECDSA
secp521r1 [IPsec][OpenVPN]
Digest Algorithn: sha512I also don't see on the server side no route to the 192.168.20.0/24 network into the tunnel: 10.0.5.0/24. So I think there is a problem. I also have to set the gateway manual on each interface on the server side because of my WAN configration which uses configuration override.
-
Breakthrough
Custom options on the server Side:
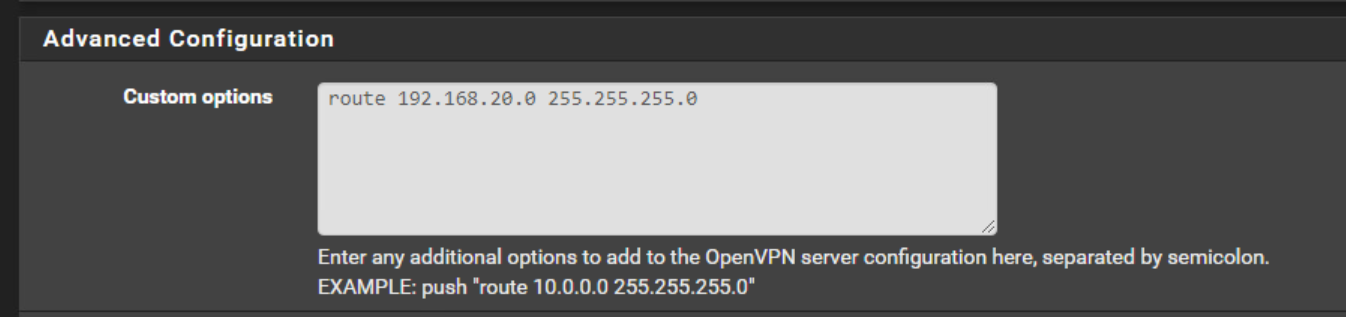
i added it but not on CSO config.
Now I can connect to the client side.
But why?
I see this has now ben created in Diagnostics / Routes:
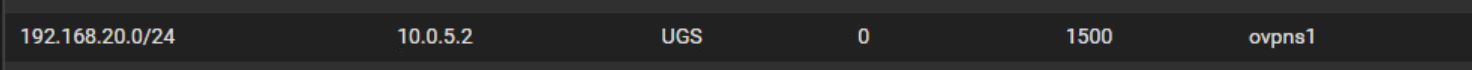
-
@hispeed said in Remote Access / TLS + User Auth - Connection up but no LAN:
I still get on the client this "Authenticate/Decrypt packet error: packet HMAC authentication failed" error. So i exported the CA and Client certifcate new.
Could it be because I used an ECDSA?I'm still on older OpenVPN versions which have no support for this. So I don't know.
Custom options on the server Side:
i added it but not on CSO config.
Now I can connect to the client side.
Yes, I think, that was the missing link, but didn't consider this.
As far as I know, the route option is necessary to add the route in pfSense to OpenVPN. But also in the CSO you need to enter the clients network into "IPv4 Remote Networks", which is needed to set the route to the proper client within OpenVPN.
-
@hispeed So I tried this in my lab last night and could not get it working although it should.
To be honest, you're wasting your time. Just do a peer to peer with a /31 and be done with it.
But if you want to keep trying....
First, you do not need a CSO with only one client connecting. As I said, get rid of it. Not doing any good.
Second, with remote access as the type, you're basically creating a "road warrior" vpn. Typically meant for one client to connect to one site. It doesn't enable other clients on the remote network access to the vpn. That's why I say just do the peer to peer as it's meant to be used. But you can configure a remote access for the entire remote LAN, see here:https://community.openvpn.net/openvpn/wiki/HOWTO#IncludingmultiplemachinesontheclientsidewhenusingaroutedVPNdevtun
Again, I tried it, it's a waste of time when there's an option made explicitly for what you want.
The biggest problem with remote access is the config doesn't give you the option to set "Remote IPv4 Networks" and peer to peer does.By the way, that error you're seeing has to do with the certificates. Did you create all certs on the server, then export the needed certs to the client, or did you create certs on server and create certs on client?