filter reload allows persistent TCP traffic to be established
-
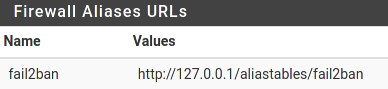
I'm facing the following dilemma: we maintain a local URL Table alias of IPs banned by fail2ban:
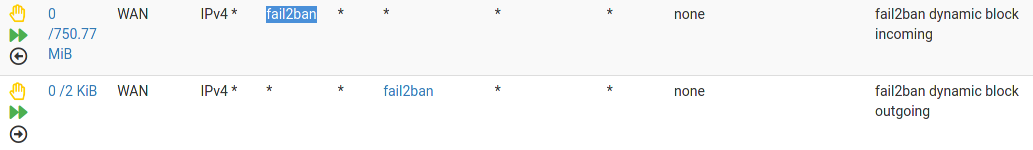
used by the following floating firewall rules:
the problem is when pfsense does a filter reload, that rule appears to briefly no longer take effect long enough for attackers to establish persistent TCP connections to a public facing proxy server and hammer it until it crashes.
Is it expected that the firewall would be open like that or could something else be going on (disconnect between the active and persistent fail2ban list for example)?
If it is, it seems my only recourse would be to somehow kill any active states for the IPs in that list after reload. Is there a way I can hook into that process?
Thanks for any help.
Copyright 2025 Rubicon Communications LLC (Netgate). All rights reserved.