Redirecting all DNS to Pihole
-
Hey,
I'm looking to make sure all DNS is getting sent to the pihole server on my local LAN with the exception of the pi-hole server itself. I already setup DHCP to point to the pi-hole server but i notice devices like the chromecast are bypassing my local DNS server.
I know this might break things but i would like to give it a shot. What's the best way to do this?
Thanks in advance.
-
You can do dns redirection, or just block them to force them to use your internal assigned dns via dhcp.
https://docs.netgate.com/pfsense/en/latest/dns/redirecting-all-dns-requests-to-pfsense.html
You can redirect to other dns on your network, say pihole - but pihole would need to be on a different vlan then the clients your redirecting.
If you setup pfsense to forward to pihole, you need to make sure pihole doesn't just forward back to pfsense.. For example if pihole is forwarding to say 8.8.8.8 ie not pfsense, or resolving on its own via unbound on pihole. Then you can just redirect to loopback, and pfsense will ask pihole, etc.
-
After a bit of googling i think i figured it out... required 3 rules though. If anything body knows a better way to get this done please share :)
- Allow single IP (pihole) to access pfsense
- NAT redirect rule that points to pihole
- Blocking DNS Queries to External Resolvers
- Also had to make sure the rules are placed in the correct order
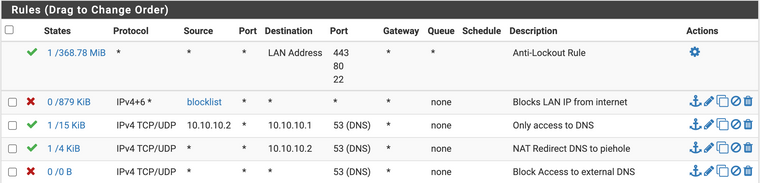
Did some testing and i think it looks good
blablablablabla:~ blablablablabla$ dig google.com @8.8.8.8
;; reply from unexpected source: 10.10.10.2#53, expected 8.8.8.8#53
;; reply from unexpected source: 10.10.10.2#53, expected 8.8.8.8#53
;; reply from unexpected source: 10.10.10.2#53, expected 8.8.8.8#53; <<>> DiG 9.10.6 <<>> google.com @8.8.8.8
;; global options: +cmd
;; connection timed out; no servers could be reached
blablablablabla:~ blablablablabla$ dig google.com @10.10.10.2; <<>> DiG 9.10.6 <<>> google.com @10.10.10.2
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 1958
;; flags: qr rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 1;; OPT PSEUDOSECTION:
; EDNS: version: 0, flags:; udp: 4096
;; QUESTION SECTION:
;google.com. IN A;; ANSWER SECTION:
google.com. 197 IN A 172.217.165.142blablablablabla:~ blablablablabla$ ping google.com
PING google.com (172.217.165.142): 56 data bytes
64 bytes from 172.217.165.142: icmp_seq=0 ttl=118 time=5.369 ms
64 bytes from 172.217.165.142: icmp_seq=1 ttl=118 time=9.040 ms
64 bytes from 172.217.165.142: icmp_seq=2 ttl=118 time=7.514 ms -
I think I got this working with 2 rules. Everything seems to be working as expected based on logs and nslookup from various hosts, but this is my first time doing anything with firewalls.
Rule 1: NAT Redirect/Port Forward
ipv4 TCP/UDP LAN
Source: (Invert) pihole:any
Destination: (Invert) pihole:DNS
Redirect IP/port: pihole:DNS
NAT Reflection: disableRule 2: Firewall
Action: Block
LAN, IPv4, TCP/UDP
Source (Invert) pihole:any
Destination: any:DNSWhat is the use of the Block rule, shouldn't the rule above have redirected everything? I suppose i can use it to monitor for anything weird happening since as I understand it nothing should hit that rule
I also used this article a bit https://blog.flippedbits.io/2020/07/wrangling-dns-on-your-network-part-2-forcing-pfsense-dns/
-
Hey all,
Saw this topic. I used it to redicrect my chromecasts to one of my pihole instances and it works!
Now, the problem is, I have two piholes. Is it possible to just add a same rule to make both available for the chromecasts, in case one pihole fails?