Strange DNS lookups
-
Yes, where do I ask this question. I'm trying here. ;o)
I'm testing the ADGUARD DNS service, and have set up Pfsense to handle all DNS queries to their DNS IP. And it seems to work fine.
However, I have become curious as I can see that periodically, as shown in the photo, 3 DNS lookups are made with approx. 15 minute intervals, mind you, when all equipment is switched off, except Pfsense of course.
I have tried to pull out the LAN plug, and this causes these DNS lookups to not occur. Next I have (I user denies everything, except what is allowed) set all allow rules to log traffic. But nothing is still shown in the firewall log, when I compare the times shown in the photo, but DNS lookups occur, as described.
I can see that when I turn on my PC to check the log, all traffic appears as it should in the log as I have set it to (set all allow rules to log traffic), so it works.
Is there anyone here who can see what kind of DNS lookup that occurs, only when the LAN interface is online, but which does not appear in the log.
It annoys me a lot that I can't find the reason/source of what generates those DNS lookups.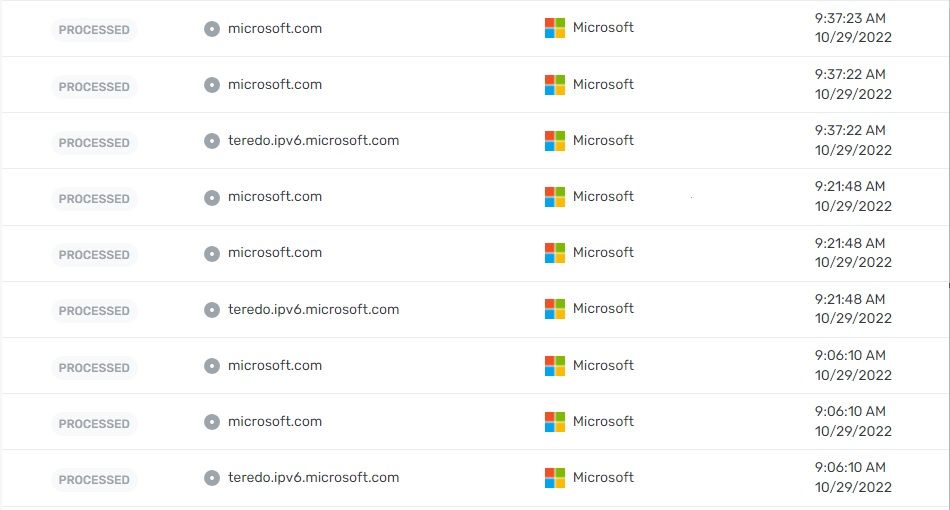
-
@felix-4 said in Strange DNS lookups:
Is there anyone here who can see what kind of DNS lookup that occurs
A lookup for teredo.. I thought that service was disabled in like version 1803 of windows 10. What version of windows are you running? 1803 was end of life like end of 2019
If your looking to see what clients are asking pfsense for those.. You can log dns queries in unbound. In the options section of unbound
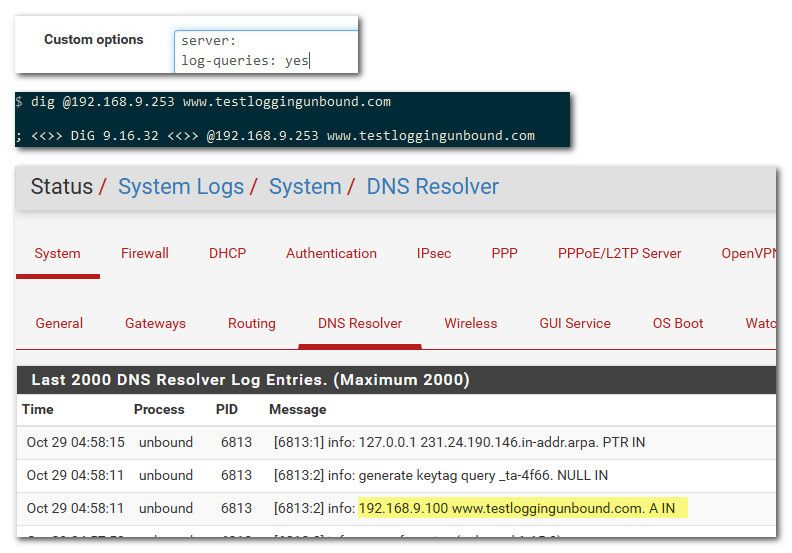
See I set it to log queries, then do a lookup for something from my 192.168.9.100 pc. Then in the log of unbound I can see what IP asked for that.
-
@johnpoz
Many thanks for the detailed answer. The command you describe is exactly what I'm looking for to clear it up.
I have set it up as you describe, and tested it, it works fine.I run a small NOC PC with windows 7 ultimate, which I use for some monitoring. I have blocked access to the internet as it only needs to work on LAN, but in case of error it needs to send an email so port 587 and 53 are open there. That's probably where it is. and I had not included it in my test.
I am very happy for quick reply, thank you. ;o)
-
@felix-4 windows 7 - ugggh..
You can stop those terdo queries if you disable it.. I find it unlikely you would want that running.
On your windows 7 box.
netsh interface teredo set state disabled -
I have just replied to you, and am looking in the log, and it is clearly stated there:
Oct 29 12:56:46 unbound 14546 [14546:0] info: 192.168.12.150 teredo.ipv6.microsoft.com. A IN
And yes, I will stop it as you describe. Can you tell me what function it has, I have not encountered it before.
-
@felix-4 teredo was a ipv6 transition technology to tunnel IPv6 through a ipv4 connection.. It was a horrible idea if you ask me, and was not very well thought out that tunneling ipv6 through ipv4 can be a security concern.
edit:
If it was actually functioning - your client that your wanted to stop from going to the internet, could access anything it wanted via the teredo tunnel.With the worse part being, that unsolicited inbound to this box could also work through the tunnel. Now the "idea" was that there are so many IPv6 addresses you would be hiding like a needle in a haystack. But quite often you tell someone your address when you access something.. So say you went to a website via your tunnel, now that site knows your IPv6 address and could probe it for something they might want to exploit..
From a security point of view, it should never be enabled. The good thing was it was easy enough to disable at your firewall.
-
It is interesting to hear the background, and yes it definitely sounds like a very unfortunate feature to have running, and not know about.
Due to the lack of time to familiarize myself thoroughly with IPV6, I have chosen to disconnect IPV6 in my Pfsense 4100, in all the places where it can be disconnected. So I reckon that I am safe for such cases. Hmmm But if it is routed through IPV4, well ok that's not good.. -
@felix-4 said in Strange DNS lookups:
Hmmm But if it is routed through IPV4, well ok that's not good..
exactly.. If your limiting outbound, it prob would have never worked. I believe the port was UDP 3544 To be honest I would of hoped MS would of shut down all their relays by now..
And that teredo.ipv6.microsoft.com no longer actually even resolves..
But that doesn't stop old clients from still asking for it ;)