Suricata 6.0.4_1 - problem under legacy IPS mode
-
I am using Pfsense with Suricata package version 6.0.4_1, and blocking mode activated (legacy) in my WAN interface.
It works very well blocking many attacks from internet, but after some days, normaly 15 a 20 days, the block list gets void, and suricata do not work correctly anymore, ignoring everything.To make it work correctly again, I have to manually update all ruleset.
Is someone facing this same issue, or know if this is some kind of bug, and how to solve it? -
@tchadrack Running it on WAN is going to scan any arriving packet even if it would be blocked by the firewall. So you may end up with a lot of extra blocks. (and extra work scanning the packets)
What do you have set for Remove Blocked Hosts Interval? If that is Never, then I would expect you'd eventually run out of memory, or at least firewall table entries.
-
Running out of table entry space is my first suspicion if you have a busy network with lots of blocks.
Go to the GLOBAL SETTINGS tab and set the Clear Blocked Hosts interval parameter to something like 1 hour. That will automatically clear out the blocked IP addresses that have not seen any traffic for the last hour. There is no reason to persist blocks forever. One hour is usually plenty of time to discourage a persistent knocker. And Suricata can certainly detect and block the host again if malicious traffic recurs (after all, it blocked it the first time didn't it?).
Like @SteveITS stated, you really should run Suricata on the LAN and not the WAN. Suricata is not there to protect your firewall, it's there to protect your LAN and other internal interfaces. Running it there is better for several reasons. When on the WAN, it is going to detect and block stuff the firewall is also going to block, so you are doing double work for no extra gain in security.
-
Thank you for the replies, I have tried already with just the 1 hour setting, that was my first attempt indeed, but even then after some days suricata started behaving that way.
I get many hacking and scanning attempts from internet, they never passed the firewall, but the attempts are always occurring; because of that I wanted to block that ip addresses and stop them from reaching my firewall as soon they try to scan me.
I wanted to get invisible to them as soon as any hack or scanning attempt is detected, so that my machine stops responding them imediately.
That was the motive I enabled suricata in wan interface and tuned it.
-
Unless you have open and forwarded ports on your firewall, it is going to drop all unsolicited inbound traffic anyway. So, really Suricata is not doing anything worthwhile running on the WAN (unless you do have open and forwarded inbound ports on the WAN).
One big issue when it runs on the WAN is that it sees outbound traffic after NAT has been applied, and it sees inbound traffic before NAT is unwound. So, you can never see what internal host (on the LAN, for example) is participating in the conversation. But when you run Suricata on the LAN, then it sees the real native host IP address and the alert logs will show both the local internal host's IP address as well as that of the external participant in the traffic. So, much easier to see what internal hosts may have issues when you run Suricata on the LAN.
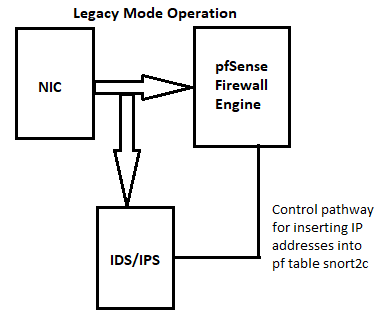
This diagram illustrates what I mean. This is how traffic flows with Suricata running in Legacy Blocking Mode. Suricata gets a copy of every packet, examines that packet, and then determines if it should signal a block. But notice the firewall gets the original packet. So, if the firewall drops it anyway due to the default rule dropping unsolicited inbound traffic, there is no point in having Suricata issue a second block for the same traffic.