-
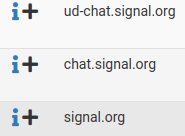
Hello. For reasons unknown at the time of this post, I stopped receiving iPhone Signal app incoming texts while using my WLAN; cell service works just fine. The only 2 firewall options I have that I believe could be causing messages to be blocked is pfBlockerNG and Suricata. When I launch signal on my iPhone, I check the pfBlockerNG Reports and it looks like it's passing the Signal traffic with no issues. In the pfBlockerNG > Reports > Unified, the entries are:
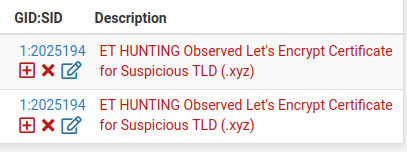
As far as Suricata, the following are the only entries I'm dropping on my WLAN:
#SURICATA STREAM Packet with invalid timestamp
suppress gen_id 1, sig_id 2210044#SURICATA STREAM TIMEWAIT ACK with wrong seq
suppress gen_id 1, sig_id 2210042#SURICATA STREAM ESTABLISHED SYN resend
suppress gen_id 1, sig_id 2210026#SURICATA STREAM CLOSEWAIT FIN out of window
suppress gen_id 1, sig_id 2210016#SURICATA STREAM FIN out of window
suppress gen_id 1, sig_id 2210038#SURICATA STREAM Packet with invalid ack
suppress gen_id 1, sig_id 2210045#SURICATA STREAM ESTABLISHED invalid ack
suppress gen_id 1, sig_id 2210029#SURICATA STREAM FIN invalid ack
suppress gen_id 1, sig_id 2210030#SURICATA STREAM 3way handshake SYNACK with wrong ack
suppress gen_id 1, sig_id 2210007#SURICATA TLS invalid record/traffic
suppress gen_id 1, sig_id 2230010#SURICATA TLS invalid handshake message
suppress gen_id 1, sig_id 2230003#SURICATA STREAM bad window update
suppress gen_id 1, sig_id 2210056#SURICATA STREAM reassembly overlap with different data
suppress gen_id 1, sig_id 2210050#SURICATA STREAM ESTABLISHED SYNACK resend with different ACK
suppress gen_id 1, sig_id 2210023#SURICATA STREAM FIN2 FIN with wrong seq
suppress gen_id 1, sig_id 2210035#SURICATA STREAM ESTABLISHED packet out of window
suppress gen_id 1, sig_id 2210020#SURICATA STREAM 3way handshake wrong seq wrong ack
suppress gen_id 1, sig_id 2210010#SURICATA STREAM 3way handshake right seq wrong ack evasion
suppress gen_id 1, sig_id 2210002#SURICATA STREAM 3way handshake with ack in wrong dir
suppress gen_id 1, sig_id 2210000#SURICATA HTTP unable to match response to request
suppress gen_id 1, sig_id 2221010#SURICATA STREAM SHUTDOWN RST invalid ack
suppress gen_id 1, sig_id 2210046#SURICATA Applayer Wrong direction first Data
suppress gen_id 1, sig_id 2260001#SURICATA Applayer Detect protocol only one direction
suppress gen_id 1, sig_id 2260002#SURICATA TLS invalid record type
suppress gen_id 1, sig_id 2230002#SURICATA STREAM ESTABLISHED SYNACK resend with different seq
suppress gen_id 1, sig_id 2210024#SURICATA STREAM 3way handshake excessive different SYN/ACKs
suppress gen_id 1, sig_id 2210055#SURICATA TLS certificate invalid der
suppress gen_id 1, sig_id 2230027Anyone have any ideas on what may be blocking incoming Signal app messages? Thanks.
-
R rcoleman-netgate moved this topic from Firewalling on
-
Well, the first thing you need to do is determine which of the installed packages is actually blocking your traffic (if any of them). To do that, disable both of them, verify Signal works, then enable just one of the packages and test. The outcome of that test will likely tell you which package is the problem (if it is one of the packages).
When you stop the Suricata service, be sure you go to the BLOCKS tab and remove all blocks. Simply stopping Suricata does NOT remove already implemented blocks. They will remain until manually cleared.
And I will make an editorial comment here as well: you should not install packages that block traffic until you fully understand both how to operate them and how to quickly determine if and what they may be blocking. Just installing such packages and blindly enabling rules and lists of IPs is a recipe for a broken network with no idea why it's broken.
-
@bmeeks Hi Bill. There is nothing listed in the Suricata Blocks tab. I've been managing all of the drops in SID Mgmt. If I disable Suricata on the WLAN interface, do I have to delete all of the entries from SID Mgmt?
-
@newuser2pfsense said in Signal iPhone App Not Receiving Incoming Texts:
@bmeeks Hi Bill. There is nothing listed in the Suricata Blocks tab. I've been managing all of the drops in SID Mgmt. If I disable Suricata on the WLAN interface, do I have to delete all of the entries from SID Mgmt?
If you are using Inline IPS Mode, then there will be nothing on the BLOCKS tab as that is only used for Legacy Mode Blocking. Instead, look on the ALERTS tab for drops. Any rule that dropped (blocked) traffic will be shown in red text.
You do not need to change anything on SID MGMT. When running with Inline IPS Mode, simply stop the service on the interface. My earlier instructions assumed Legacy Blocking Mode as that is what most users configure.
And none of those rules whose alerts you show in your original post should be enabled for DROP mode. Those are informational rules and should just be left at the default of ALERT. Configured that way they will not block traffic with Inline IPS Mode enabled.
-
@bmeeks It seems like it's with Suricata. I disabled Suricata on the WLAN, restarted pfSense, opened Signal on my iPhone and wallah - messages. Hmm. Now I'll have to figure out which rule signature ID that was dropped that's blocking the incoming messages.
-
As a side note, I just tried to add a dropped entry into the Suppress list and when clicking the + button, it's not adding the entry. It used to work but now it doesn't. Odd.
Copyright 2025 Rubicon Communications LLC (Netgate). All rights reserved.