Blocked IP reaching server anyway
-
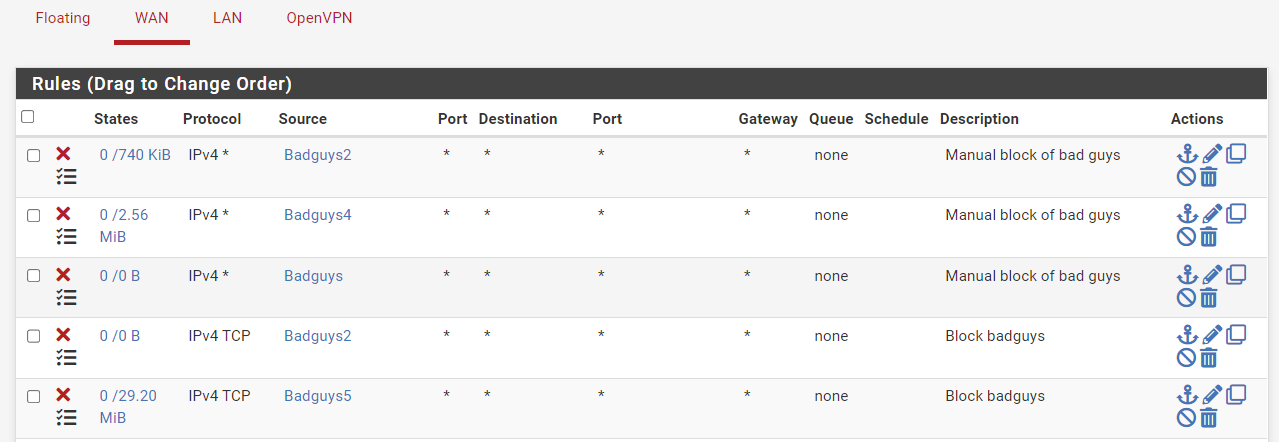
@cdsjerry see my example above - you have 2 rules with badguys alias that are not triggering.
-
@johnpoz I didn't know how to interpret those numbers. So the 0 is showing no "triggers" for that rule, yet the IPs inside that rule are still getting through. I still don't understand that. Why would it not be triggered if that IP is accessing my server? Are you saying a Floating rule is allowing it to pass before it reaches these rules? My Floating rules are posted above, I don't know how it would be getting past? I'm obviously missing something.. but what?
-
@cdsjerry said in Blocked IP reaching server anyway:
yet the IPs inside that rule are still getting through
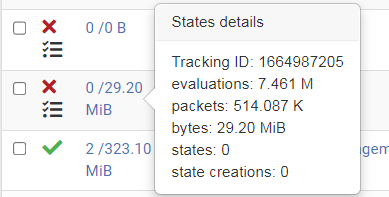
yea the first 0 is active states - but you would never see those on a block rule. the second 0 is how much traffic for that rule has been evaluated. If you see 0/0 means the rule never triggered so either the rule didn't match the traffic, or a state is allowing the traffic if that rule should block it. Or another rule allows it before that rule is evaluated.
-
@johnpoz OK, so Badguys 5 has been evaluated 7.461 M times since the reset but there are no current states active. Right? There are no WAN rules above this line that ever allow traffic to pass so I'd look at the Floating rules right? But I don't see a floating rule that would pass to the mail server. (picture above).
-
@cdsjerry yeah your badbuys5 has had lots of evaluations 29MBs worth.. and badbuys 2 has some above, so that would prob preven from the 2nd badguys 2 rule from ever seeing traffic. But that badbuys not seeing any evaluations on it..
-
@johnpoz But the IP that's reaching the firewall is in Badguys5, which IS getting evaluations... but is still passing traffic. I'm confused as to why it would pass traffic that's a block.
-
@cdsjerry it wouldn't unless it doesn't match, or there was a state. or some other rule allowed it..
-
@johnpoz The IP is a match. I reset the states so they'd be cleared. There are no pass rules above it, and don't see any floating rule pass. Is there some way to tell why its passing? The log doesn't seem to be any help.
-
@cdsjerry you could log all allow rules to see what is allowing it in..
You could also use pftop from cmd line on pfsense to see age of the state..
Maybe the state didn't get cleared when you tried to clear it, are you saying you actually rebooted pfsense?
-
@johnpoz No I didn't reboot pfSense. I went to Diagnostics / States / Reset States and checked the box to reset the firewall state table and then the reset button.
I haven't seen either of the two IPs that were attacking me for a while now. Maybe it's working or maybe they've just gone away for a while. Over they past few weeks they'll hit me with repeated attempts and then go away for a bit then come back again. Sometimes it's hours. Sometimes it's days. USUALLY when I enter their IP into the Badguys list they aren't able to get through starting right away. That's why these two caught my attention when they were still getting in.
Of course the mail server blocks them after a bit but they can sure slow things down with all their attempts.
-
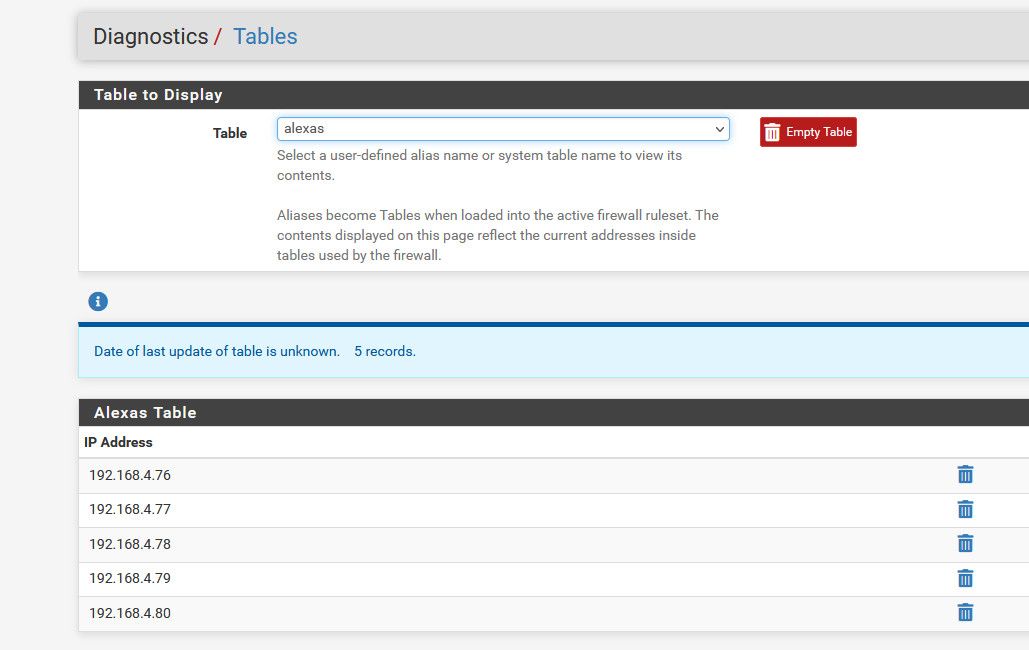
@cdsjerry Are you positive the IP address in question is actually in the Badguys5 alias? See Diagnostics > Tables and check the actual contents table/alias in question.
You can also do this in Diagnostics > Command prompt:
pfctl -vvss | grep -A3 inter.esting.ip.addressThat will show you any matching states along with the firewall rule that passed the traffic when the state was created.
You can then
pfctl -vvsr | grep -A3 '^@RULENUMBER'to identify the rule. -
@derelict I'm sure that both examples I've been watching are in Badguys5. I've checked a dozen times or more just to make sure I didn't fat-finger it. I even copied / pasted it directly from the server log a couple of times. That's one thing I am sure of.
Our office is closed for the weekend (love / hate holidays). I'll try the commands when I get back but of course I'll need to wait until I also catch them hitting the server close enough to still be in the logs / states.
I know the mail server is blocking them so they aren't actually doing any harm other than slowing down the server or else I'd be in the office after-hours trying to solve this.
-
@cdsjerry said in Blocked IP reaching server anyway:
both examples I've been watching are in Badguys5
but you want to make sure its actually loaded in the table.. This is what he was mentioning. Just looking the alias doesn't mean its actually loaded in the table.
Under diagnostics - look under tables and make sure its loaded there and correct.
example of one of my aliases
-
How come your Badguys5 (and Badguys2) rules are only blocking IPv4 TCP traffic, not all IPv4 like the others?
Yeah, SMTPD should only be listening on TCP 25 but . . .
P.S. Is that an IPSwitch/Progress IMail Server?
-
I have a Netgate 6100 (v22.05 stable) I had a similar issue. I found that copying a firewall rule and adding different address's or ports was not actually creating a new rule. :) When I discovered this, I manually entered the new rules across the board and fixed the problem. Could be related from what I've read, shrugs.
-
@euman Yes, it does.
-
@Derelict I'm sorry to inform you that the firewall did NOT properly manage the creation of a new rule and Tracking ID via a copy of similar rule. What 'was' strange is that this only affected my LAN-2 rules.. I digress, you know better. however, we all are aware there are no bugs in NG software.. smirks, I'd love to spin up the development version but my appliance coughed and said no thanks.
back to lying now, hagd
-
@euman There is a known (fixed) issue regarding copying multiple rules all getting the same rule ID but they still function.
-
@biggsy Good catch on the TCP only traffic. I've fixed that so it's now blocking all traffic instead.
Yes, I am running IPSwitch/ Progress IMail server. Any hints or tricks about that? I'm REALLY hoping someone buys that product line. It's a great mail server. Progress is making a mistake by saying they're going to EOL it.