OpenVPN DNS simple question
-
Hi,
just a simple (hope) question about DNS and OPENVPN.
In the VPN/OPENVPN/Server I've successfully configured an OpenVPN Server.
Home connections towards company LAN through that VPN works great and so do the split tunnel: internet traffic goes outside the tunnel (0.0.0.0), private lan traffic goes into the tunnel (192. etc etc)
Is there a way to split also DNS traffic?
8.8.8.8 for DNS query of public domains and my internal dns (192. etc etc) for query about mydomain.local?
I've tried to push both (primary, secondary and vice-versa) in the Server configuration and also in the Client override but it doesn't work as I would like...
The final configuration is obviously internal DNS as a primary to resolve private domain and public domains too, but it also resolve all other queries...Thanks in advance.
ivan
-
@vaz1970 said in OpenVPN DNS simple question:
In the VPN/OPENVPN/Server I've successfully configured an OpenVPN Server.
At home or at the company?
How do you connect to the server?
Is there a way to split also DNS traffic?
8.8.8.8 for DNS query of public domains and my internal dns (192. etc etc) for query about mydomain.local?No. How should that work?
At the time the client need to resolve a host name, he cannot determine if it's public or private. He has to request a DNS server to check this out.You can only go with domain overrides. E.g. so that you use your home DNS and this forward request to certain domains to the company DNS.
-
@viragomann said in OpenVPN DNS simple question:
@vaz1970 said in OpenVPN DNS simple question:
In the VPN/OPENVPN/Server I've successfully configured an OpenVPN Server.
At home or at the company?
At the company
How do you connect to the server?
With Tunnelblink for MAC OSx
Is there a way to split also DNS traffic?
8.8.8.8 for DNS query of public domains and my internal dns (192. etc etc) for query about mydomain.local?No. How should that work?
At the time the client need to resolve a host name, he cannot determine if it's public or private. He has to request a DNS server to check this out.You can only go with domain overrides. E.g. so that you use your home DNS and this forward request to certain domains to the company DNS.
You're right. Home DNS Overrides for certain domains is the only way.
Thank you very much indeed for your time. -
@viragomann
Just another thing for you :)
A client at home is connected to OpenVpn server.
It uses its home ISP/DNS for resolving every DNS name except something.mycompany.lan (DNS intranet zone)
In that unique case I want that request for something.mycompany.lan are resolved by my internal DNS (192.etc.etc)
I've tried to set in Advanced Client Setting "DNS Default domain/Provide a default domain name to clients" and "DNS Server enable/Provide a DNS server list to clients..."
But It seems not working.
I'm going to test further more...
Can you suggest me something else?Thanks
-
@vaz1970
If you run the VPN client on computer I know no way to split the DNS requests, unless you can configure domain overrides on it.It might be easier if you have a pfSense at home which connects to the VPN server. So you can use its DNS Resolver on the client and forward company's domains to the remote DNS server with domain overrides.
Or you have a way to add domain overrides to the remote DNS server for your home domain.
-
@vaz1970 said in OpenVPN DNS simple question:
Is there a way to split also DNS traffic?
Why not just use the home DNS for everything? It should have both home and public names available. That's what I do.
-
Dear all,
I've discovered with plenty of pleasure that is possible to split DNS traffic.
You just need to associate a zone to DNS :)
https://openvpn.net/vpn-server-resources/troubleshooting-dns-resolution-problems/
(-> "Split-DNS when using DNS Resolution Zones")if you configure on your firewall (Pfsense or what else) that for a specific "intranet" zone you have to query a specific DNS, that's work!
I've verified directly on the firewall (.91 is my IP address from the OpenVpn assigned subnet)
tcpdump -i ovpns1 src 10.x.y.91 and port 53
DNS queries for xyz.lan appear in the dump otherwise not (ISP DNS are used)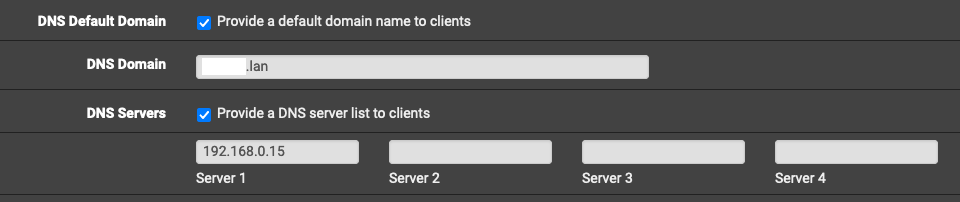
Although you'll have to use OpenVpn client... (with tunnelblick, e.g., it will not split DNS)
That's all I needed.
Thanks to all