FW Logging a Block when Rule is Permit?
-
I have a NAT rule setup to forward from my VPN provider, to my box on https.
The FW rule in place is as follows:

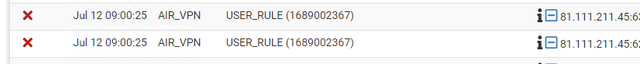
But in the logs it states:

If I press the "easy add" rule next to the log, it then makes this for me:

It looks like my initial rule should allow the traffic but it doesn't?
-
@Deadringers
It's ever a good advice to state a description for created filter rules.Since you haven't pick the rule ID and check if the block rule is either one on the OpenVPN tab or the floating tab.
Consider that rules on both have priority over ones on the interface tab. -
@viragomann said in FW Logging a Block when Rule is Permit?:
@Deadringers
It's ever a good advice to state a description for created filter rules.Since you haven't pick the rule ID and check if the block rule is either one on the OpenVPN tab or the floating tab.
Consider that rules on both have priority over ones on the interface tab.Not sure I understand mate - why should there be no description? Or are you saying I should put a description?
-
@Deadringers
I'm talking about the block rule.
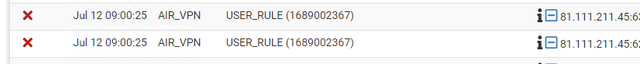
If pfSense only shows "USER_RULE" in the log there is probably no description stated. -
@Deadringers so does that auto rule work? You need to look up what rule is blocking that, via the ID.. As mentioned by @viragomann do you have any rules in floating? The openvpn tab that could be blocking it - those would both be evaluated before the interface rules.
-
@viragomann said in FW Logging a Block when Rule is Permit?:
@Deadringers
I'm talking about the block rule.
If pfSense only shows "USER_RULE" in the log there is probably no description stated.Ahh thank to you and @viragomann for clarifying!
I've given them descriptions now, and I see that weirdly, the interface in the logs is stated as "AIR_VPN", but the rule is coming from "OpenVPN".



I created an allow any/any for testing on the "OpenVPN" Interface, and it does say allowed/passed, but the traffic is not turning up on the LAN at the 192.168.0.221 device as far as I can see.
Any logs I can look at to see where that traffic is going?

-
@Deadringers said in FW Logging a Block when Rule is Permit?:
I've given them descriptions now, and I see that weirdly, the interface in the logs is stated as "AIR_VPN", but the rule is coming from "OpenVPN".
It just shows the incoming interface, even if the rule is on an interface group.
I created an allow any/any for testing on the "OpenVPN" Interface, and it does say allowed/passed, but the traffic is not turning up on the LAN at the 192.168.0.221 device as far as I can see.
Any logs I can look at to see where that traffic is going?
As I told you in your other thread, this doesn't work if a pass rule on the OpenVPN tab is applied to the forwarded traffic.
-
@viragomann said in FW Logging a Block when Rule is Permit?:
@Deadringers said in FW Logging a Block when Rule is Permit?:
I've given them descriptions now, and I see that weirdly, the interface in the logs is stated as "AIR_VPN", but the rule is coming from "OpenVPN".
It just shows the incoming interface, even if the rule is on an interface group.
I created an allow any/any for testing on the "OpenVPN" Interface, and it does say allowed/passed, but the traffic is not turning up on the LAN at the 192.168.0.221 device as far as I can see.
Any logs I can look at to see where that traffic is going?
As I told you in your other thread, this doesn't work if a pass rule on the OpenVPN tab is applied to the forwarded traffic.
Sorry if I'm not understanding you correctly... but are you saying this isn't possible?
I would like: VPN Provider Public IP <---Open VPN Tunnel ---> pfSense <---Server
I want to port forward incoming traffic from the VPN provider, to my pfSense box, and then onto the server.
The VPN provider has done their part, and the traffic is coming in, I just need to get the pfSense box to send the traffic to the server, and then allow it to return over the VPN.
-
@viragomann OH SORRY!
I see what you're saying...
I've deleted all rules on my "OpenVPN" interface, and only have rules on my "AIR_VPN" interface...
it's now working as inteded - thank you very much for the help !
-
@Deadringers
It's possible, but you have to obey a configuration rules:The firewall rule, which is passing the forwarded packets has to be on the interface tab.
Check your log. This is not the case.
As already mentioned twice, rule on the OpenVPN tab have priority over rules on the interface tab. Refer: Ordering of NAT and Firewall Processing
OpenVPN is an interface group including all OpenVPN instances running on pfSense.
So remove the pass rule from there and it should work.