NAT forwarding into WireGuard Interface as LAN Interface
-
@viragomann said in NAT forwarding into WireGuard Interface as LAN Interface:
However, if you don't and want to see the real source address on the server at B, you would need some additional settings.
Beside HAProxy what would be your suggestion?
-
@Bronko
You mean, to get the public source IP on the server and get it work without masquerading?As mentioned, HAproxy does this anyway. Didn't ever configure it with forwarding across WG, but I guess it might use the WG interface IP as source. So it would be the same as your outbound NAT rule does and you'll can probably remove it.
Without masquerading you would have to assign an interface to the WG instance at B. I'll call it wg_sa here as exampel.
Then move over all firewall rules from the Wireguard tab to wg_sa.
Ensure the pass rule on wg_sa allow any source address to access the server.
There must be no pass rule on the Wireguard or on floating tab matching the forwarded traffic from A, otherwise the communication with the server will fail. -
@viragomann said in NAT forwarding into WireGuard Interface as LAN Interface:
Without masquerading you would have to assign an interface to the WG instance at B. I'll call it wg_sa here as exampel.
tun_wg0 is right in place on Site-B for sure, but you mean a second, Virtual IP interface there?
-
@Bronko
No. You should find tun_wg0 in Status > Interface. Then it's a dedicated interface. Otherwise you have to assign one. -
@viragomann said in NAT forwarding into WireGuard Interface as LAN Interface:
You should find tun_wg0 in Status > Interface. Then it's a dedicated interface.
Yes, it is already there due to the WireGurad setup.
Thanks @viragomann !
-
On Site-B at server net one machineMX is configured like these:
# netstat -rn Kernel IP routing table Destination Gateway Genmask Flags MSS Window irtt Iface 0.0.0.0 10.200.0.2 0.0.0.0 UG 0 0 0 eth0 10.0.0.0 0.0.0.0 255.255.255.0 U 0 0 0 eth0 10.200.0.2 10.0.0.1 255.255.255.255 UGH 0 0 0 eth0 10.200.0.2 0.0.0.0 255.255.255.255 UH 0 0 0 eth0 # ip addr 1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000 link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00 inet 127.0.0.1/8 scope host lo valid_lft forever preferred_lft forever inet6 ::1/128 scope host valid_lft forever preferred_lft forever 2: eth0@if36: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP group default qlen 1000 link/ether 82:08:92:77:f8:80 brd ff:ff:ff:ff:ff:ff link-netnsid 0 inet 10.0.0.102/24 brd 10.0.0.255 scope global eth0 valid_lft forever preferred_lft forever inet6 fe80::8008:92ff:fe77:f880/64 scope link valid_lft forever preferred_lft forever # ping 10.200.0.2 PING 10.200.0.2 (10.200.0.2) 56(84) bytes of data. 64 bytes from 10.200.0.2: icmp_seq=1 ttl=63 time=25.4 ms 64 bytes from 10.200.0.2: icmp_seq=2 ttl=63 time=25.5 ms 64 bytes from 10.200.0.2: icmp_seq=3 ttl=63 time=25.3 msBut outgoing internet traffic doesn't goes through Site-A tun_wg0: 10.200.0.2
# curl ifconfig.me curl: (7) Failed to connect to ifconfig.me port 80 after 3093 ms: No route to hostHAproxy on Site-A managed incoming traffic as awaited, but on machineMX initiated internet connections (like postfix) on Site-B should go on WAN interface at Site-A.
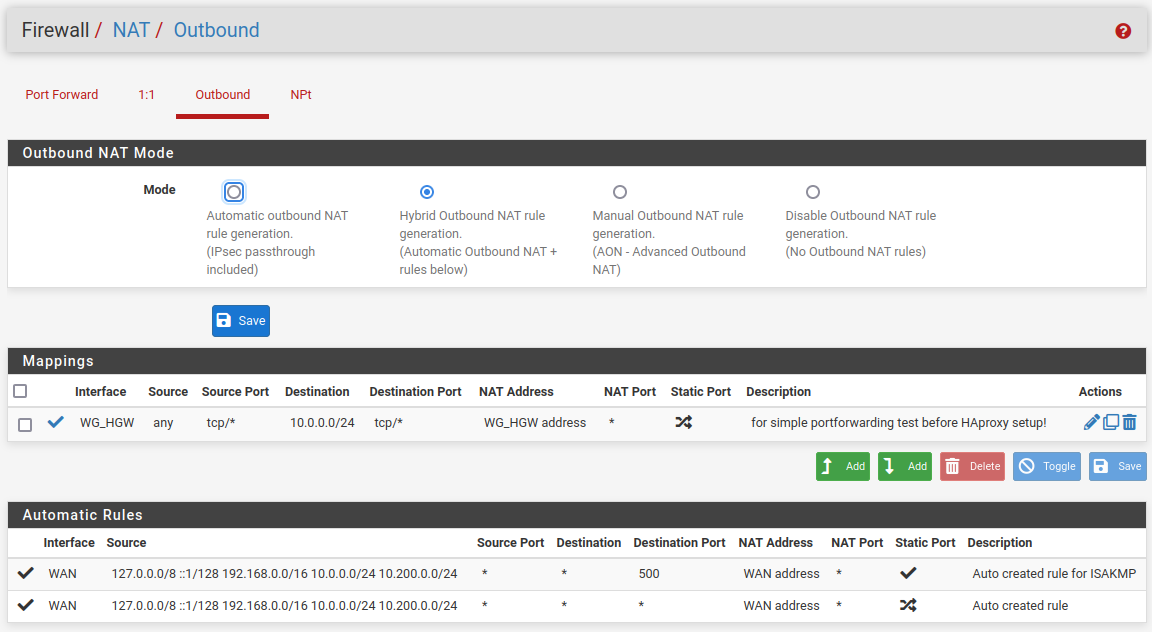
Outbound NAT for masquerading at Site-A for servers IP at Site-B temporarily (HAproxy doesn't need it as you mentioned above) activated, but doesn't changed the behavior.
There are some routing/gateway configuration steps in Site-B still open for these scenario?
Do you have some hints here too?
-
@Bronko TLDR but I have that running now, what you have described at first and I don't see any problems. I don't NAT anything inside this whole network, only towards public addresses on WAN.
Also make sure that on B the peer-config off A has 0.0.0.0/0 as allowed IPs and that in A all the routes are set in System-Routing-Static Routes. -
@Bob-Dig said in NAT forwarding into WireGuard Interface as LAN Interface:
Also make sure that on B the peer-config off A has 0.0.0.0/0 as allowed IPs...
That was missing!
Thanks to @Bob-DigBut machineMX doesn't knows anymore tun_wg0: 10.200.0.2 for routing (DNS only), solved by Policy Routing on Site-B as described here for ex.
-
@Bob-Dig said in NAT forwarding into WireGuard Interface as LAN Interface:
@Bronko TLDR but I have that running now, what you have described at first and I don't see any problems. I don't NAT anything inside this whole network, only towards public addresses on WAN.
Routing is fine, but I have to see the source IP address of sending mail server at the internet on machineMX on Site-B server net (10.0.0.0/24). Currently the 10.200.0.2 (tun_wg0) is present because of NAT.
@viragomann said in NAT forwarding into WireGuard Interface as LAN Interface:
This replaces the source IP anyway.
You are right, the source IP is replaced by 10.200.0.2 (tun_wg0). How to avoid it?
Any hints for me?
-
@Bronko said in NAT forwarding into WireGuard Interface as LAN Interface:
Any hints for me?
Don't NAT, like I said before and don't use haproxy for email.
-
@Bronko said in NAT forwarding into WireGuard Interface as LAN Interface:
This replaces the source IP anyway.You are right, the source IP is replaced by 10.200.0.2 (tun_wg0). How to avoid it?
HAproxy has to replace the source IP with its outgoing interface IP to get the routing work reliably.
You can avoid this though by enabling the transparent mode in the concerned backend settings. But I don't know if the routing across the VPN will work properly then.
Anyway you would have to obey my suggestions regarding interface assignment and filter rules at B above.If it's a http frontend it's rather recommended to add a forward-for header, which would get the clients IP as value. However, the backend server would have to interpret this to get the client IP in the log.
-
@Bob-Dig said in NAT forwarding into WireGuard Interface as LAN Interface:
Don't NAT, like I said before and don't use haproxy for email.
That is what I have learned here, using haproxy for SMTP isn't comfortable...
Therefore I have been already created a forwarding rule for WAN on Site-A to machineMX on Site-B server net (10.0.0.0/24) and re-configured the mapping suggested by:
@viragomann said in NAT forwarding into WireGuard Interface as LAN Interface:
So configure the outbound NAT for masquerading at A even now.
Activate the hybrid mode, save this and add a new rule:
interface: tun_wg0 (or whatever the WG is)
protocol: TCP (or what you forward)
source: any
destination: the servers IP at B or an alias for multiple destination IPs
translation: interface addressby the option Do not NAT. But these option breaks the traffic flow, no more connection from outside to SMTP on machineMX.
What I have to learn here...?
-
@Bronko said in NAT forwarding into WireGuard Interface as LAN Interface:
by the option Do not NAT. But these option breaks the traffic flow, no more connection from outside to SMTP on machineMX.
I didn't mention that option.
And the NAT might be superfluous if you're driving this traffic over HAproxy, as mentioned. The suggestion was meant for the time to be. -
Just to recap, you have a VPS in the internet, just with pfSense on it.
At home you have a pfSense too and an email-server behind that.
You have made a WireGuard tunnel between the two sites.Now what you can do is a port 25 forward from the VPS to your email-server at home. Also you can route outgoing traffic to port 25 using the VPS over that WG tunnel.
Have a look at this video how to do a Site-to-Site VPN Using WireGuard and pfSense even if you don't have any other hosts on the VPS.
-
@viragomann said in NAT forwarding into WireGuard Interface as LAN Interface:
I didn't mention that option.
I know, but it was my first run to disable NAT for a specific connection only, to avoid to disable NAT entirely given by the fact not only public routable interfaces on pfsense at Site-A.
@Bob-Dig said in NAT forwarding into WireGuard Interface as LAN Interface:
Just to recap, you have a VPS in the internet, just with pfSense on it.
At home you have a pfSense too and an email-server behind that.
You have made a WireGuard tunnel between the two sites.Perfect recap!
@Bob-Dig said in NAT forwarding into WireGuard Interface as LAN Interface:
Now what you can do is a port 25 forward from the VPS to your email-server at home. Also you can route outgoing traffic to port 25 using the VPS over that WG tunnel.
Exactly my current configuration with NAT enabled at VPS (Site-A here).
@Bob-Dig said in NAT forwarding into WireGuard Interface as LAN Interface:
Have a look at this video how to do a Site-to-Site VPN Using WireGuard and pfSense even if you don't have any other hosts on the VPS.
Already done.
(and mentioned here:)
@Bronko said in NAT forwarding into WireGuard Interface as LAN Interface:But machineMX doesn't knows anymore tun_wg0: 10.200.0.2 for routing (DNS only), solved by Policy Routing on Site-B as described here for ex.
Resuming:
How to disable NAT for these specific SMTP traffic flow to log real source IP of connecting mail server - currently replaced by 10.200.0.2 (tun_wg0 at Site-B) - at my machineMX? -
@Bronko said in NAT forwarding into WireGuard Interface as LAN Interface:
How to disable NAT for these specific SMTP traffic flow to log real source IP of connecting mail server - currently replaced by 10.200.0.2 (tun_wg0 at Site-B) - at my machineMX?
Please show your Port Forward on your VPS and also the config of your WG Interface for both. Outbound NAT for both should be automatic, nothing else. It is that easy...
-
@Bronko said in NAT forwarding into WireGuard Interface as LAN Interface:
Resuming:
How to disable NAT for these specific SMTP traffic flow to log real source IP of connecting mail server - currently replaced by 10.200.0.2 (tun_wg0 at Site-B) - at my machineMX?If you direct this connection over HAproxy read again, what I wrote above.
-
@Bob-Dig said in NAT forwarding into WireGuard Interface as LAN Interface:
Please show your Port Forward on your VPS and also the config of your WG Interface for both. Outbound NAT for both should be automatic, nothing else. It is that easy...
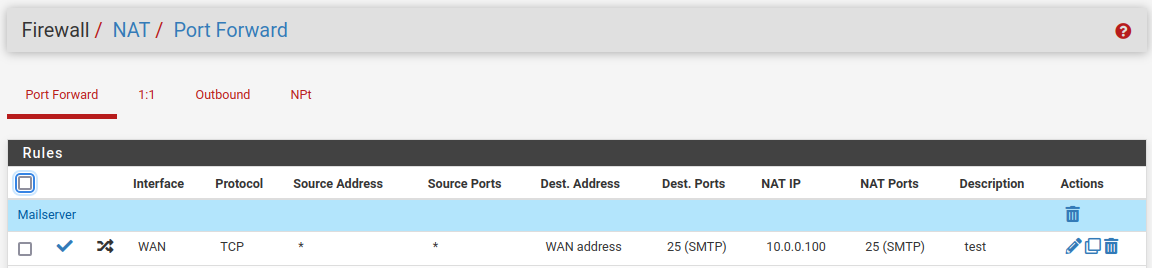
Site-A (VPS):
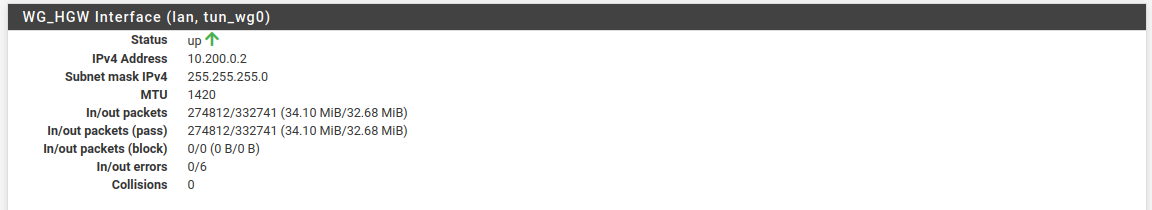
Site-B (home):
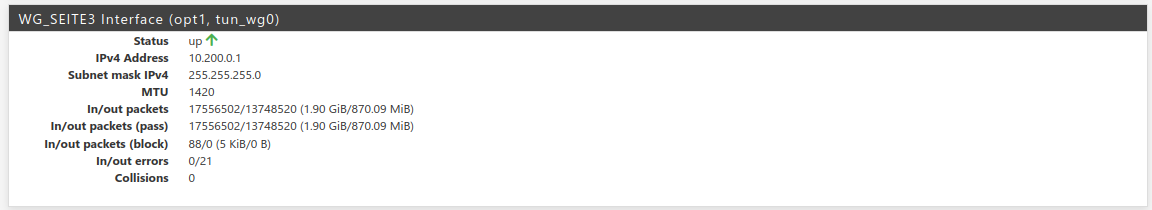
As mentioned, mail server at home - machineMX (at LAN_SEITE3) - is working for in- and outbound mails, but the replaced source ip of incomming mail server connections.
@viragomann said in NAT forwarding into WireGuard Interface as LAN Interface:
If you direct this connection over HAproxy read again, what I wrote above.
Will double check it but to use HAProxy as a reverse proxy for the Postfix SMTP server, you need to enable Postscreen in Postfix. This doesn't worked for me at the first run...
-
@Bronko I meant the complete IP-config from those interfaces, not their status.
Also remove the manual outbound NAT rule and forget haproxy.
And what rule is the last one? For the tunnel use an allow any rule for testing. -
@Bob-Dig said in NAT forwarding into WireGuard Interface as LAN Interface:
I meant the complete IP-config from those interfaces, not their status.
The tunnel is working fine, no problem here... isn't it?
@Bob-Dig said in NAT forwarding into WireGuard Interface as LAN Interface:
Also remove the manual outbound NAT rule and forget haproxy.
Without this rule @viragomann (above) incomming conntections via VPS at Site-A to machineMX at Site-B doesn't work.
@Bob-Dig said in NAT forwarding into WireGuard Interface as LAN Interface:
And what rule is the last one? For the tunnel use an allow any rule for testing.
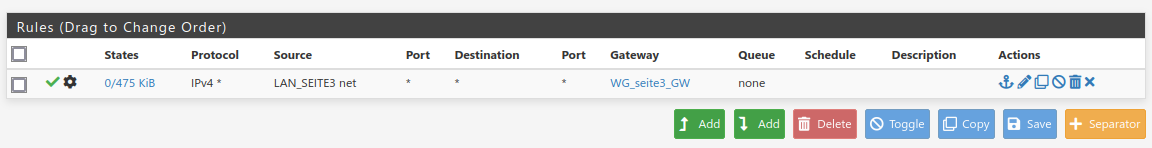
An allow any rule for wg_tunnel is in place. These last one is policy routing for server net (LAN_SEITE3). Without these the outgoing traffic at server net is routed via default gateway at Site-A.