[SOLVED] Do not log TCP packets with flags TCP:RA / TCP:PA etc.
-
Are you using that "Invert match" option for source or destination in that rule ? So far, I'm unable to replicate this behavior here but I'm not using those options.
-
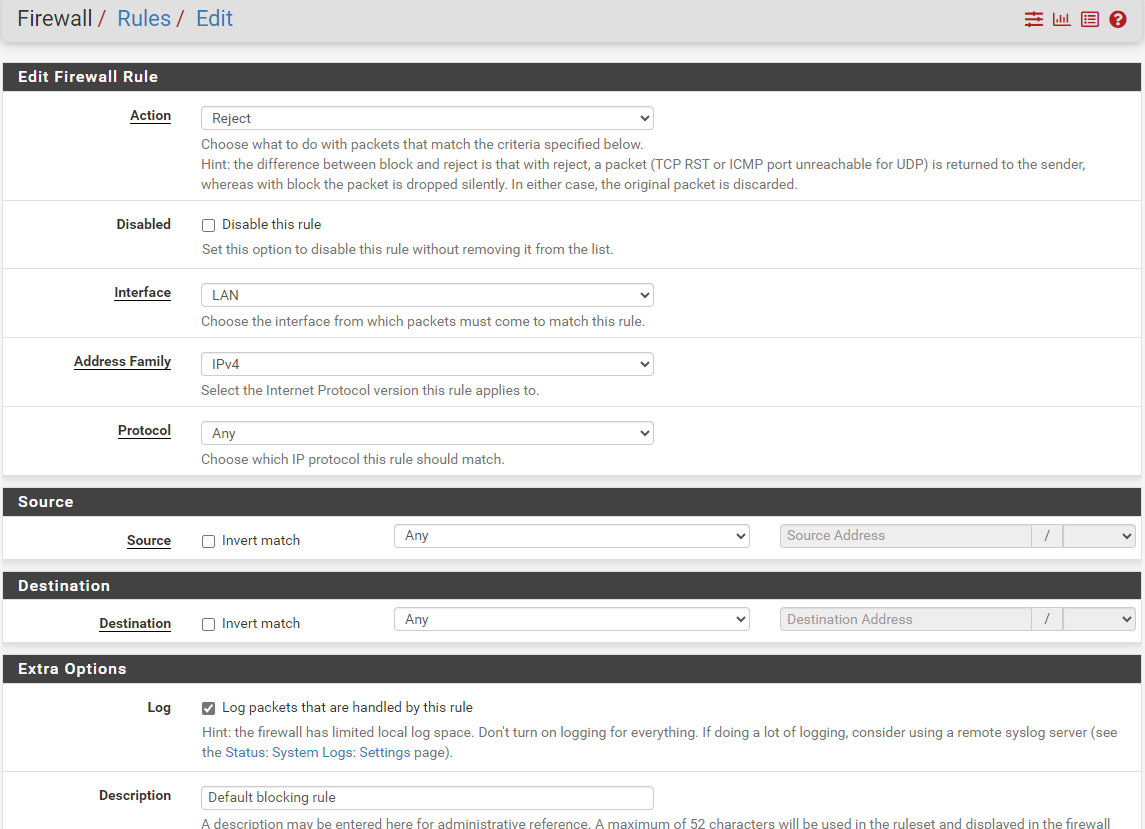
@mcury No, I do not use "Invert Match". That is my definition, together with that TCP Flags option mentioned above:
-
@mcury ah, maybe this does not work if protocol set to "Any"? I will try with Protocol set to "TCP" ...
-
No, unfortunately that did not change anything. These kind of packets are still logged by that rule:
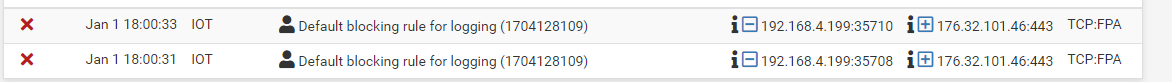
You you explain me a bit more, what how this "TCP flag" setting is working? I still did not get it. What exactly is meant by "set" and "out of"?
-
@m0urs said in Do not log TCP packets with flags TCP:RA / TCP:PA etc.:
What exactly is meant by "set" and "out of"?
https://docs.netgate.com/pfsense/en/latest/firewall/configure.html#tcp-flags
-
"By default, new pass rules for TCP only check for the TCP SYN flag to be set, out of a possible set of SYN and ACK."
Hm, so I would say that I just need to create a normal rule without any options enabled in "TCP flag"? In this case I do get a logging entry if there is something blocked with SYNC flag and no more logging entries for all the other packtes?
That would be what I wanted?
Update: It says "new PASS rules", but I have a REJECT rule?
-
@m0urs said in Do not log TCP packets with flags TCP:RA / TCP:PA etc.:
"By default, new pass rules for TCP only check for the TCP SYN flag to be set, out of a possible set of SYN and ACK."
Hm, so I would say that I just need to create a normal rule without any options enabled in "TCP flag"? In this case I do get a logging entry if there is something blocked with SYNC flag and no more logging entries for all the other packtes?
That would be what I wanted?
Yes, try that and report back.
Other option would be to create a new rule below that one, and set flags to all but SYN, and set to no log. -
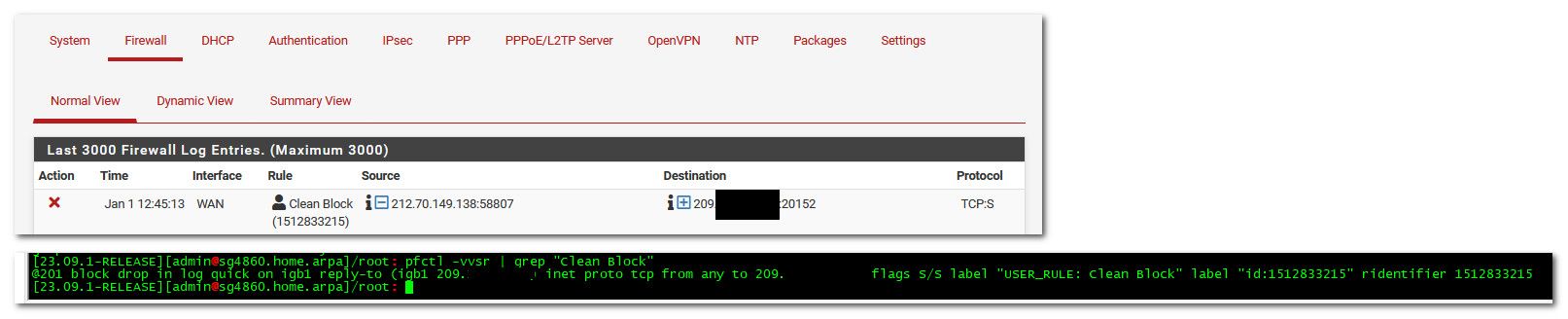
@mcury I had a look into the Packet Filter rules generated by pfSense.
Could it be that these options are only used for PASS rules but not for BLOCK rules?
Here is the output for that rule either with PASS:
[2.7.2-RELEASE][root@router02.urs.lan]/root: pfctl -vvsr | grep "33276" @177 pass in log quick on igb2.20 inet all flags S/SA keep state label "USER_RULE" label "id:1704133276" ridentifier 1704133276and with BLOCK:
[2.7.2-RELEASE][root@router02.urs.lan]/root: pfctl -vvsr | grep "33276" @177 block drop in log quick on igb2.20 inet all label "USER_RULE" label "id:1704133276" ridentifier 1704133276 -
@m0urs not sure what your looking at exactly - but those rules block and only syn..
-
Notice the "flag s/s" in your blocking rule?
Compare it with my blocking rule above, which is missing that ...
So I guess that is the reason, why it is not working for me.
If I change the rule to "PASS" then the "flag s/s" is added. If I change it back to "BLOCK", it is missing!?
-
@johnpoz Ok, I think I need to set that rule to protocol "TCP" and not "ANY". In this case the "flag s/s" is added. I will try again an recreate the rules.
-
@m0urs yeah tcp is what has syn.. so that is prob a requirement
-