None of my firewall rules are working on VLANs
-
@johnpoz said in None of my firewall rules are working on VLANs:
@ErniePantuso it would be much easier to help you if you actually just posted a screen shots of your rules.
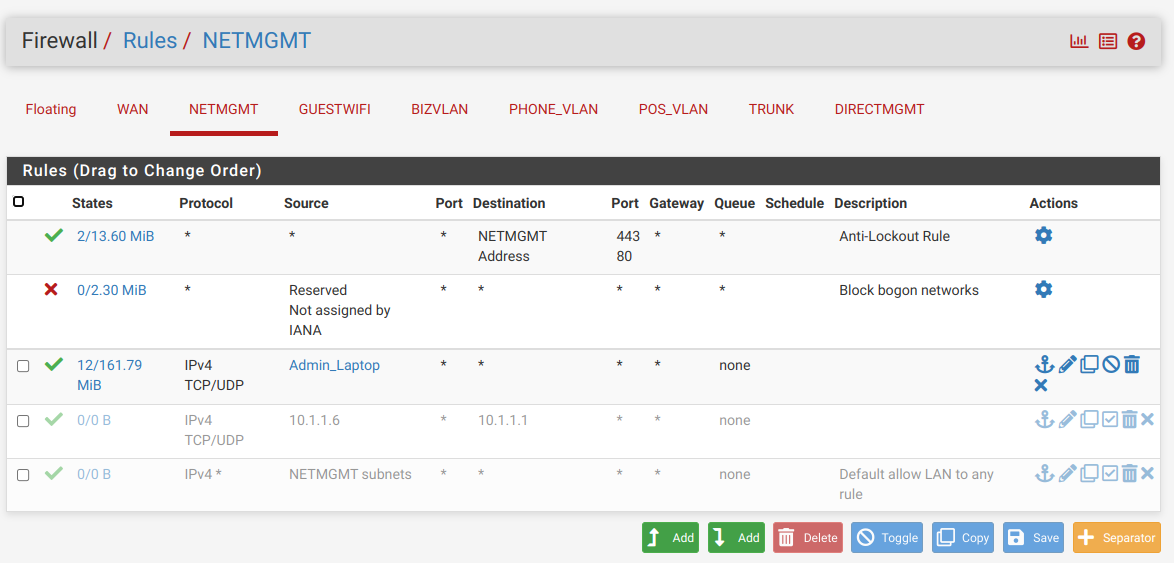
Sorry, I should have thought of that. I'll post screenshots of both the NetMgmt segment (which is working fine) and the BizVLAN segment (which doesn't work at all.)
But when I assign it an IP of 10.1.10.33 (BizVLAN), I can access my Proxmox server (10.1.10.10) but nothing on the NET_MGMT segment and nothing on the web
The wording of how you changed over to different IP, gets me thinking your not actually running vlans, but just multiple networks on the same L2?
I don't know the answer to that.
Are you doing any policy routing out a vpn?
No. (Don't even know what that is.)
Or different gateway
No
Do you have any rules in floating
None
And dns is pretty simple to diagnose.. Can you ping 8.8.8.8, can you do a dns query to www.google.com - use your fav tool, nslookup, dig, host, doggo, etc. etc.
With a 10.1.1.6 (NetMgmt) IP, I can ping whatever with no problems. With a 10.1.10.33 (BizVLAN) IP, I can't ping anything. I also tried it from the shell on my Proxmox server. It can't ping anything, either.
I do understand about DNS and pinging; I just have no clue how I give my VLAN different DNS settings.
-
@ErniePantuso
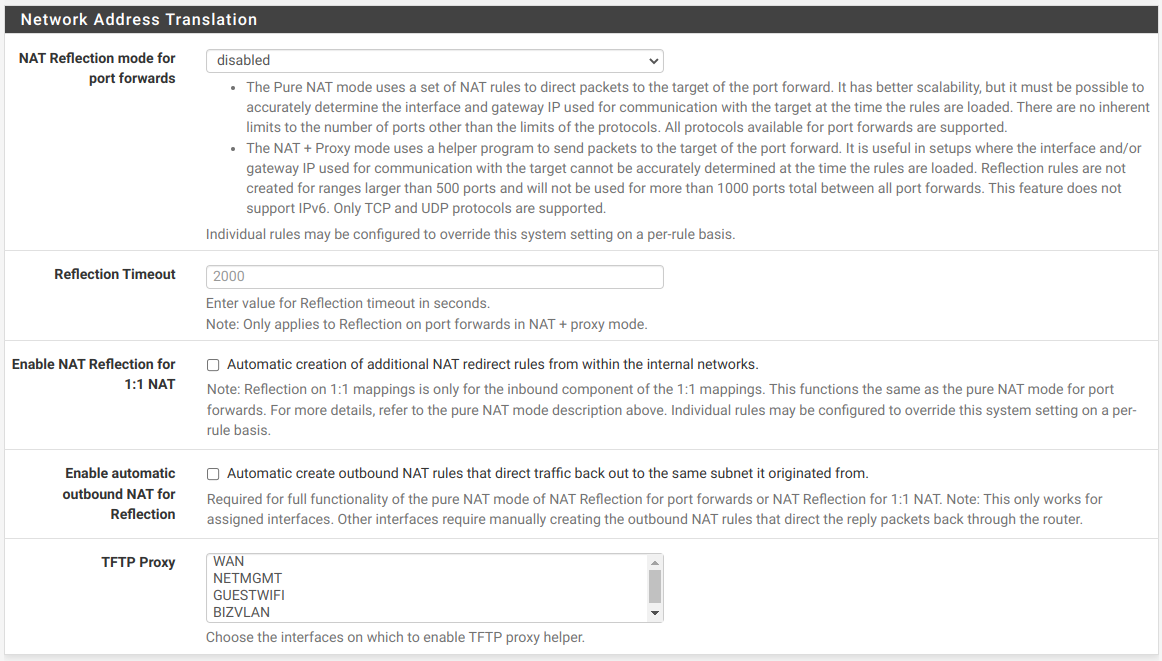
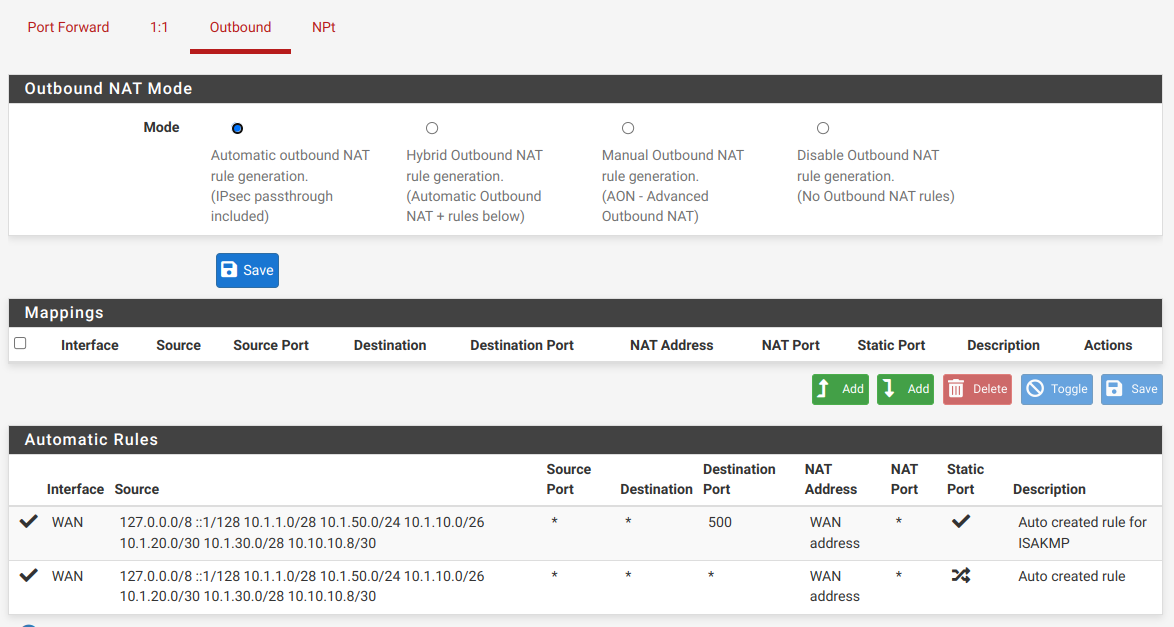
Is your outbound NAT running in automatic mode?
And if so, is there a rule in place for this subnet? -
@viragomann I haven't made any changes to NAT so no, it's not in automatic mode.
-
Another piece of the puzzle? I have a TP-Link Omada controller running in a container. I gave it a static IP of 10.1.1.10 to keep it on the NetMgmt segment but of course, it exists within Proxmox which lives on a box with a BizVLAN IP. I tried to ping from the shell of this container and it can't ping anything.
-
@ErniePantuso
It's in automatic mode by default.And if you go to the outbound NAT page, you can see the automatically added rules at the bottom. Please check, if all your subnets are shown up there.
-
-
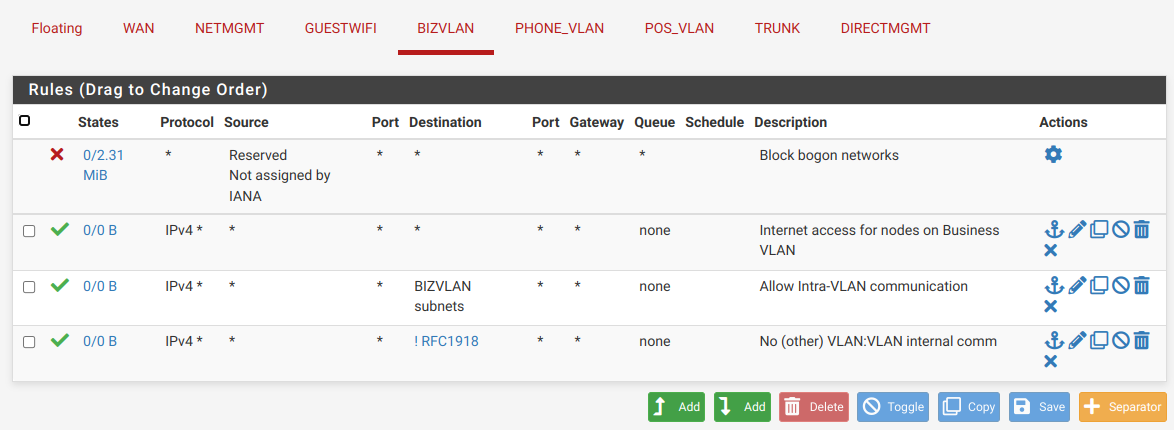
@ErniePantuso You need to read up on rules. They need to be on the interface the traffic originates on. You have a rule on bizvlan with a destination of bizvlan. Not gonna work.
You have an any/any rule with other pass rules below it. Not gonna work.
If you want to block (or allow) the bizvlan access to LAN, the rule goes on bizvlan.You have no traffic shown on the bizvlan rules. Are you sure you're even connecting to it? Does it get a DHCP address if you connect to it?
-
@ErniePantuso Why are blocking bogon on your lan side interfaces? How would bogon ever be on your lan side as a source? You understand rfc1918 is bogon.. That anything at all can work is pfsense pulls rfc1918 out of the bogon rule.. There is no point to putting bogon on any of your lan side interfaces.
-
@ErniePantuso
This one:
Firewall > NAT > Outbound -
-
@johnpoz said in None of my firewall rules are working on VLANs:
@ErniePantuso Why are blocking bogon on your lan side interfaces?
That was the default so I left it.
There is no point to putting bogon on any of your lan side interfaces.
Got it. Fixed. Thanks!
-
@ErniePantuso said in None of my firewall rules are working on VLANs:
That was the default so I left it.
No it is not that is for sure.. It is default on the WAN, not any other interface.
-
@johnpoz said in None of my firewall rules are working on VLANs:
@ErniePantuso said in None of my firewall rules are working on VLANs:
That was the default so I left it.
No it is not that is for sure.. It is default on the WAN, not any other interface.
OK. I guess I don't remember when or why that got changed. I've really struggled to learn all this stuff; I've asked for and received help from a lot of different sources. Either I got some bad information or (more likely) I misunderstood the info I got.
-
@ErniePantuso It has never been the default, ever - because it make no logical sense at all.. I have been running pfsense pretty much since it has come out.. And never has block bogon been a thing on the lan side.. It only makes sense on the wan. And even then its not very useful or needed..
If you mean when you changed it ok ;) its not a thing anyone would ever have need to do.. And if pfsense didn't pull out rfc1918 from the bogon list you would of broken your network.. Would of remembered then when you changed it ;) hehehe
They enable you to be able to check it - because maybe its a transit network, and you have no idea what the source would be, or maybe its an actual wan and you would want to enable it.
-
@johnpoz said in None of my firewall rules are working on VLANs:
@ErniePantuso . . . And if pfsense didn't pull out rfc1918 from the bogon list you would of broken your network.. Would of remembered then when you changed it ;) hehehe
Not necessarily. In the first place, I've never really had the network setup. It's been in an alpha state for months as I slog my way through learning this stuff. And within that framework, I've broken my network and restored pfSense from backed up configurations numerous times - so it could have been any of those and I don't know which! hahaha
-
@Jarhead said in None of my firewall rules are working on VLANs:
@ErniePantuso You need to read up on rules. They need to be on the interface the traffic originates on. You have a rule on bizvlan with a destination of bizvlan. Not gonna work.
You have an any/any rule with other pass rules below it. Not gonna work.
If you want to block (or allow) the bizvlan access to LAN, the rule goes on bizvlan.You have no traffic shown on the bizvlan rules. Are you sure you're even connecting to it? Does it get a DHCP address if you connect to it?
I'm not a complete idiot. ;D I do have a basic understanding of rules. I understand that any pass rules after the any/any rule are superfluous. I put the any/any rule there as a troubleshooting measure. And I understand that rules for BizVLAN have to go on BizVLAN. My rule on BizVLAN with a destination of BizVLAN subnets was intended to allow nodes on that VLAN to be able to talk to each other. I thought it was blocked otherwise. But I now know that's not correct because I tried disabling ALL the rules on BizVLAN and (with a static IP in that subnet), I can still access my Proxmox server. That confuses the heck out of me!
How/where do you see that I have no traffic shown on the bizvlan rules? Am I connected to it? Well, again, with a static IP in that subnet, I can access my Proxmox server - and when I go back to a NetMgmt IP, I can't. That would seem to indicate that I'm connected, wouldn't it? I wasn't worrying yet about DHCP but now that you asked, when I switch my laptop to DHCP, it does not pull an IP address.
So what does all that tell me? I keep trying to download an LXC container template from my Proxmox server and it continues to give me a DNS error - even when the only rule on BizVLAN is the pass any/any. If it's allowed to pass any/any, shouldn't that include DNS server(s)?
-
@ErniePantuso said in None of my firewall rules are working on VLANs:
was intended to allow nodes on that VLAN to be able to talk to each other.
Doesn't work like that, but it comes up quite often here to be honest..
it does not pull an IP address.
This is the big clue that you have something at L2 borked.. If you have a dhcp running and you don't get an IP.. Look to the dhcp server - did it see the discover, and not an IP to hand out is that why? Or did it never get the discover, so your L2 is borked.
If dhcp is not working, setting a static isn't going to work either. Unless it was a failure of the actual dhcp server. Again looking to see if you saw discover in the logs.
As to your dns error - well yeah if you can't talk to the dns, your never going to get an answer.. Simple check for this is, can you ping your gateway for checking connectivity, can you ping the dns IP if different than your gateway.. Can you do a dns query with nslookup, dig, there are many tools you can use to validate dns is working while at the same time checking the other aspects of your connectivity..
-
@ErniePantuso said in None of my firewall rules are working on VLANs:
It's been in an alpha state for months as I slog my way through learning this stuff.
Learning pfSense and routing and proxmox and virtualization at the same time might be to much for you.
-
@ErniePantuso See the 0/0 B on the left of the rules? That means that rule has never been hit, unless you just rebooted before that pic was taken.
You definitely have a layer 2 problem as John said.Not trying to say you're an idiot here. Don't take it that way, but you clearly are confused.
Do you realize that setting a static IP doesn't put you on a different network? You have to physically connect to it still.
I never understand why anyone would want a router to run as a VM, it's your main entrance to your network, it should be a separate machine. But if that's what you want, you will have to learn about virtual switches too then. Just guessing you don't have the vSwitch configured correctly which is why you aren't connecting to the vlan.
Start small. Just put an any/any rule on both interface, turn on the DHCP server on both, then connect a device to each and go from there. Once you have both networks working you can then lock them down as needed. -
@Jarhead said in None of my firewall rules are working on VLANs:
Do you realize that setting a static IP doesn't put you on a different network?
Yeah I brought that up right away - his wording of how he was changing "vlans" was off - just saying he changed his ip?
Running a router as VM can have some advantages - but you better be fairly knowledgeable on what has to be done to do that for vlans or other networks, and fully understand networking to be honest. I ran mine as vm on esxi for a while, and did setup one on proxmox to ship to another location for work.
Proxmox was a bit of learning curve from esxi.
As a vm there are some advantages - I could easy switch from one instance of pfsense to another, so allowed for easy testing of some new version or even other flavors of router distros. Very easy backup with just a snapshot I could roll back too. But they do have some draw backs. To do anything with the vm host my whole network was down. There is a learning curve on how the vm host software handles vlan tags, etc. Which can be different than just your typical vlan switch.
Much better setup when I moved pfsense to hardware for my edge router that is for sure. I still play with different versions of pfsense as VM but they are just on my nas and for testing. If I have to do something with my nas (vm host) my whole network isn't down ;) I wouldn't go back to on a VM as my main router.