Using Managed Switch for Company and Private Networks
-
@JKnott said in Using Managed Switch for Company and Private Networks:
@bookie56 said in Using Managed Switch for Company and Private Networks:
LAN_PRIVATE
LAN_COMPANY
WIFI_PRIVATE
WIFI_COMPANYAs mentioned, you can use VLANs. You might also want to combine the LAN & WiFi networks, so you only have one each for private and company.
And when you do move to VLAN, you only need one port instead of all 4. It may simplify things a bit and will save you three ports on the switch.
What are you using for WiFi AP's today? If that equipment is capable of VLAN, you can use the same AP for private and corporate, just separate SSID's and subnets.
Perhaps create a diagram showing your setup which will help in restructuring, and deciding what size switch you need.
-
Hi guys...Sorry have been busy....
Ok further to what we discussed earlier..
As shown I have my quad network card that is divided up into the 4 networks as shown below:
LAN_PRIVATE 192.168.120.1 (example)
LAN_COMPANY 192.168.121.1 (example)
WIFI_PRIVATE 192.168.122.1 (example)
WIFI_COMPANY 192.168.123.1 (example)
I am happy with that setup and don't really want to mess with it...I have assigned static IP's in pfsense for several computers and for arguments sake I can assign 192.168.120 10 to keep it on my private system for ease of access...
Now in the TL-SG1024DE I can create vlans...which I need some help with...
on port 1 I have the link from pfsense so that would be used for this port...
I would like to assign 2-16 with my vlan for LAN_PRIVATE...is that possible?I have port17-24 left and would like to assign them to my LAN_COMPANY and use port 17 as the link from pfsense...is that possible?
I have under VLAN: MTU VLAN, Port Based VLAN, 802.1Q VLAn, and finally 802.1Q PVID Setting..
This would mean I can remove three swithches and replace it with just this one...It would be nice to utilise the one swithch for different vlans so that I can keep my private network away from the company one...
How do I proceed?
Or do you need more info?bookie56
-
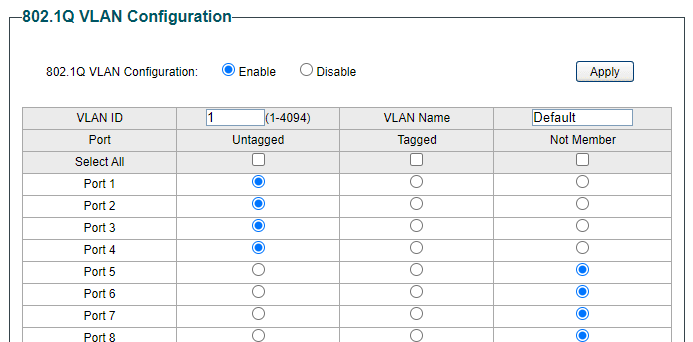
@bookie56 Fist off all, you use 802.1Q VLAN, which involves two separare Tabs in the TPLink UI (802.1Q VLANS and 802.1Q PVID Settings).
You will need to make Port 1, connecting to pfsense, into a TRUNK port for the VLAN traffic that you want so it can pass to and from pfsense. All ports already handle default VLAN ID 1, so lets say you chose the following:
LAN/WIFI_PRIVATE - default (no changes)
LAN/WIFI_COMPANY - VLAN ID 10And then you need to make ports 17-24 into Untagged ports for VLAN 10.
You could create separate VLANs for WIFI as well but is that really necessary? I guess you want anywone connecting to COMPANY to be able to talk to each other without any special arrangements?
To get started and have pfsense setup for your VLANs you go to Interfaces > VLANs and add a VLAN. Select your LAN interface as your parent interface and enter e.g. 10 for the ID, give it a "name" in the description, like COMPANY, click save.
Now under Interfaces > Assignments there is a new entry where you select your new VLAN and click Add. Then you can Edit this entry and fill in the IP (subnet) for example 192.168.10.0/24 (different from 192.168.1.0/24 as in your default LAN). Simply make it so it mimics what you have under LAN.
Then you go to Services > DHCP Servers and edit the DHCP Server for that VLAN. Finally you need to create rules for the VLAN under Firewall > Rules > COMPANY_VLAN or what that interface ended up being called. Add at least a default allow all rule, but preferably also block rules above that to stop that VLAN from reaching your LAN, and perhaps vice versa.Then, in the TPLink UI, you go to 802.1Q VLANS and start by entering ID 10, COMPANY and tick the TAGGED
So it looks something like this: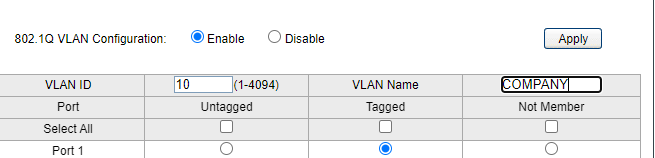
Click Add/Modify.
Then enter 10 again in the box for VLAN ID. Now you click the Untagged button for all the ports that you want to use for COMPANY (17-24) and again Add/Modify, and then Apply.Now go to 802.1Q PVID Settings and tick all the ports you want to make into VLAN ID 10. Enter 10 in the ID-box and click Apply and now anything you connect to those ports will "see" the COMPANY DHCP Server and receive an IP from192.168.10.0/24.
Not sure what you have for WIFI, but there are two alternatives.
- If you have "dumb" AP's you connect them to either a PRIVATE or COMPANY port, and set it's SSID name to something corresponding.
- If you use AP's that can handle VLAN's you need additional TRUNK ports (like port 1) on the TPLink switch for the APs as well. And in the AP(s) you create two wifi networks (separate SSIDs) for PRIVATE and COMPANY. And for the COMPANY network, you give it VLAN ID 10.
The AP will then set any traffic on that wifi network to VLAN ID 10 and it's ethernet port will be set to be able to TRUNK that traffic connected to your switch.
That should do it...
-
Hi Gblenn

Sorry not following much of what you have written...
I reserved port 1 on my private network by using a static IP and Mac address...
I then logged into the switch and applied the settings to keep that IP assigned to port 1
This info?
LAN/WIFI_PRIVATE - default (no changes)
LAN/WIFI_COMPANY - VLAN ID 10
In pfsense I chose my company lan as said for my vlan and as suggested I gave it 10 as an ID and called it Company...
I clicked on Interfaces > Assignments and added the new entry.....
Under Vlan Company I chose IPv4 as my configuration type but couldn't add my company ip subnet because it was the same or being used by LAN_COMPANY...
I want the subnet to reflect my original LAN_COMPANY or am I thinking wrong?
I have 192.168.121.2 to 192.168.121.20 as my range for that card...
Sorry....this is not my best area of expertise....bookie56
-
@bookie56 Ok, as I read your first post again I realize there might be a mixup between ports on pfsense and the TPLink switch.
I was referencing Ports on the switch, not pfsense. And I was assuming only one LAN port being used on pfsense.
Your current setup however is if I understand it correctly, utilizing all four ports on the Quad Card that you have.What are you using for wifi? Some AP's like Unifi or TPLink perhaps?
Do you agree that it can be a good idea to maintain only two "networks". One for Private and one for Company? That means LAN and Wifi are on the same subnet...
Anyway, if you want to keep COMPANY in 192.168.121.0/24 range that can be done, if you need it. But then you need to remove or change your current COMPANY LAN to something else. Doesn't matter what. Because you want to use that subnet for the VLAN instead...
Same thing with both your WIFI networks. There I assume the subnet doesn't matter that much, right?? No static leases for servers etc?So let's say igb0 is your WAN and igb1 is your LAN used for PRIVATE today. Let's say that interface has IP 192.168.1.0/24, and your pfsense web interface is accessed at 192.168.1.1
So igb1 will need to be connected to Port 1 on the TPLink switch. None of the other ports on the Quad card need to be connected.
Here's the documentation on VLAN configuration.
https://docs.netgate.com/pfsense/en/latest/vlan/configuration.html#web-interface-vlan-configurationStep 1: Create the VLAN to be used for COMPANY, using VLAN ID 10. The only difference from the picture in the documentation is that you select igb1 (if that is your LAN).
Step 2: Interfaces > Assignments will show a new item at the bottom where you click +Add. Then you edit this new interface and call it COMPANY and set it to static IP 192.168.121.0/24. (Assuming this is not already used elsewhere, in which case you need to change or delete the other interface).
Step3: Services > DHCP Server, edit the new COMPANY DHCP Server as you need.
Step4: Firewall > Rules > COMPANY_VLAN, create a pass all rule. Later on when you have it working you should consider adding a block rule for other VLAN's.
Now you log into the TPLink switch and follow the instructions I had before, starting with the picture I pasted and then to the end of that post.
-
@Gblenn Hi again...
When I was looking for a setup at home ...run business from home...
I mentioned I would like a private network and a company one...plus I wanted en access point for private and one for company...they are tp-link men not at home at the moment...so not sure...
I was told that a quad would suit my needs....
Because I only thought logically...that is why I bought the quad...
Anyway I will be at home later and can work with your info...
I had a thought...I only have reserved ip addresses on my private network so it doesn't matter what I name the range for company....
Just that port1 is directly linked to the private network and all computers that are linked to the private network already have reserved ip adressen and I would like to keep them as such...Thank you so much for your time
bookie56
-
@bookie56 said in Using Managed Switch for Company and Private Networks:
@Gblenn Hi again...
When I was looking for a setup at home ...run business from home...
I mentioned I would like a private network and a company one...plus I wanted en access point for private and one for company...That is perfectly understood and makes complete sense. However access point and wifi access can mean slightly different things.
Most Access Points (AP's) can serve multiple SSIDs = multiple wifi networks. So one single AP can let you have several wifi-networks with different passwords. Depending on the capabilities you could then have them separate the traffic by VLAN.they are tp-link men not at home at the moment...so not sure...
Ok so check out what model it is so we can figure out the capabilities... Also, how many do you have? And where are they located? Not that it matters from the perspective of VLANs but it may matter from a radio coverage perspective. Are they in different parts of the home for example? My point is that if you have two AP's, at either ends of your house, they can still serve both Private and Company needs.
Also on the Private side you may have connected TV's, Receivers and the likes that are connected via cable (Ethernet). Or you have a media server in your NAS perhaps. Then it will help if your phone ends up on the same subnet as the server, so they can "find each other" without any additional work from your side.I was told that a quad would suit my needs....
Because I only thought logically...that is why I bought the quad...No worries, might prove to be useful at some point. Are you running pfsense directly on the PC/Server or is it perhaps virtualized?
Anyway I will be at home later and can work with your info...
I had a thought...I only have reserved ip addresses on my private network so it doesn't matter what I name the range for company....
Just that port1 is directly linked to the private network and all computers that are linked to the private network already have reserved ip adressen and I would like to keep them as such...Sure, that is no problem at all. So the way forward is to keep Port 1 as it is. And I was anyway assuming it is actually the default LAN that you started out with, when you first set up pfsense. That will be your LAN also going forward, so no changes there. And the Company network will run as a VLAN on top of that, clean and simple.
And I have to ask, are you located in Sweden by any chance?
-
@Gblenn Sweden....what ever gave you that idea

I have 2 x TP-Link EAP245 AP's
My wifi doesn't get affected by this switch at all...they have there connections to:
WIFI_PRIVATE and WIFI_COMPANY on my quad...
This switch is mainly for the LAN side of things...most computers are LAN_PRIVATE.
I have firewall rules in place so that those networks don't talk to each other... or with LAN_COMPANYWhen I work on customer computers I either connect to the WIFI_COMPANY which is just above my head....
 or the LAN_COMPANY which up and til now has been two standard unmanaged switches.... hence my interest to get rid of them and replace them with the new one...
or the LAN_COMPANY which up and til now has been two standard unmanaged switches.... hence my interest to get rid of them and replace them with the new one...This is only an 84 square meter flat so one AP is in the living room behind the tv and the other above my head in the office....YES I understand what you are saying about using both to feed both networks....but because of the size of the flat I have very good connections speeds where ever I am...(Good point though)
If I run speed tests from my kitchen to the living room which is around the corner....YES I lose some speed - but we have 500 up and 500 down so it doesn't really affect us...Like I said the Wifi AP's are directly fed by network cables coming from my pfsene router which at the moment is an old Asus Gaming:
Motherboard 1155
Processor i7-3770 3.4GHz
2 x 4 GB PC3-1200
Intel 520 Series SSD
Dell Pro 1000 VT PCieI even have a reserve router with pfsense that I keep updated so that if something goes pear shaped I am up and running quite quickly
All private connections are ip and mac reserved in pfsense....I have a cubiQ CS 1794 from Aten on an adjustable height bench which is always up....
Under there I have several feeds that come from this switch so I can work on several computers at once...
These cable feeds have two network cables that serve the private or company LANS depending what I have connected at the time..bookie56
-
@bookie56 Sorry just a quick update to information....
I have the quad card just for my networks and the inbuilt network is for WAN which keeps it totally separate from the quad Card...Not to complicate things ....just a thought....I really only need max 10 ports for my LAN_PRIVATE and I hve a server which has two network ports one for main incoming (connected by reserved ip on LAN_PRIVATE) and the other for Clonezilla...it would be nice to utilise 4 ports for that....one for the link from the server and the other 3 for cloning...never going to need to clone more at once than that....
Is that possible in this setup.... I then have got rid of a third switch ?bookie56
-
@bookie56 said in Using Managed Switch for Company and Private Networks:
@Gblenn Sweden....what ever gave you that idea

Two tiny skrivfel...

plus I wanted en access point for private and one for company...
they are tp-link men not at home at the moment...so not sure...I have 2 x TP-Link EAP245 AP's
My wifi doesn't get affected by this switch at all...they have there connections to:
WIFI_PRIVATE and WIFI_COMPANY on my quad...
This switch is mainly for the LAN side of things...most computers are LAN_PRIVATE.
I have firewall rules in place so that those networks don't talk to each other... or with LAN_COMPANYOk so if you don't want to touch that, it's fine but I'm just saying it would perhaps streamline and simplify things from a rules perspective. And it would free up two additional ports on your pfsense... With that CPU/Motherboard you have plenty power to run other things on it as well. Why not Omada controller for your AP's...? Then you can manage both AP's from one single interface.
When I work on customer computers I either connect to the WIFI_COMPANY which is just above my head....
 or the LAN_COMPANY which up and til now has been two standard unmanaged switches.... hence my interest to get rid of them and replace them with the new one...
or the LAN_COMPANY which up and til now has been two standard unmanaged switches.... hence my interest to get rid of them and replace them with the new one...This is only an 84 square meter flat so one AP is in the living room behind the tv and the other above my head in the office....YES I understand what you are saying about using both to feed both networks....but because of the size of the flat I have very good connections speeds where ever I am...(Good point though)
If I run speed tests from my kitchen to the living room which is around the corner....YES I lose some speed - but we have 500 up and 500 down so it doesn't really affect us...Sounds like you are all good then, wrt wifi...
Like I said the Wifi AP's are directly fed by network cables coming from my pfsene router which at the moment is an old Asus Gaming:
Motherboard 1155
Processor i7-3770 3.4GHz
2 x 4 GB PC3-1200
Intel 520 Series SSD
Dell Pro 1000 VT PCieI even have a reserve router with pfsense that I keep updated so that if something goes pear shaped I am up and running quite quickly
All private connections are ip and mac reserved in pfsense....I have a cubiQ CS 1794 from Aten on an adjustable height bench which is always up....
Under there I have several feeds that come from this switch so I can work on several computers at once...
These cable feeds have two network cables that serve the private or company LANS depending what I have connected at the time..Ok so then you will only drop one of the connections from pfsense, the COMPANY port.
This since you will be basing the COMPANY VLAN on the same Port you use for PRIVATE.Basically no changes at all on the PRIVATE side, rules, DHCP or anything. If you are ok using a new subnet for COMPANY, I suggest you do that. Then you can just disable the current COMPANY interface and leave it until you might need it for something else.
So all you need then is to create the VLAN for COMPANY as per the Netgate documentation, making sure you select the right parent interface (the one used for PRIVATE LAN).Edit the rule on PRIVATE (if you have one) so that it can't access COMPANY_VLAN), and add a rule for COMPANY_VLAN so that it can't connect to PRIVATE and you are done...
-
@Gblenn Sorry I am lost...
I was hoping to have the link for the LAN_PRIVATE which goes to Port 1 on the switch
I then was hoping to have the link for the LAN_COMPANY go to Port 17 on the switch...
If the above can't be done then I will have a separate switch for LAN_COMPANY and leave everything else on the new switch...This is why I have the quad using all 4....
bookie56 -
@bookie56 said in Using Managed Switch for Company and Private Networks:
If the above can't be done
Why do you think that can not be done? You can for sure have multiple uplinks from your switch to different interface on pfsense - when they are different networks..
Where you would run into some issues if you also want to connect your APs to other ports on pfsense and those were wanting to be on either lan private or lan company. For that to work you would need to create a bridge on pfsense which is not optimal. But if you have these AP providing 2 different networks ie wifi private and wifi work that are different networks than lan company and lan private you would be fine.
-
@johnpoz so how do I set up the switch with both of these networks?
bookie56
-
@bookie56 your port 1 would be connected to lan_private interface on pfsense with whatever vlan you want that network to be on your switch.. this would be untagged and pvid would be whatever vlan your using on your switch.
You connect port 17 on your switch to the pfsense interface that is lan company.. This port would be on some other vlan you create on the switch, this port would also be untagged and with a pvid of whatever vlan you created on your switch for this network.
So as example
Here is 3 different networks on pfsense, igb0, 3 and 5
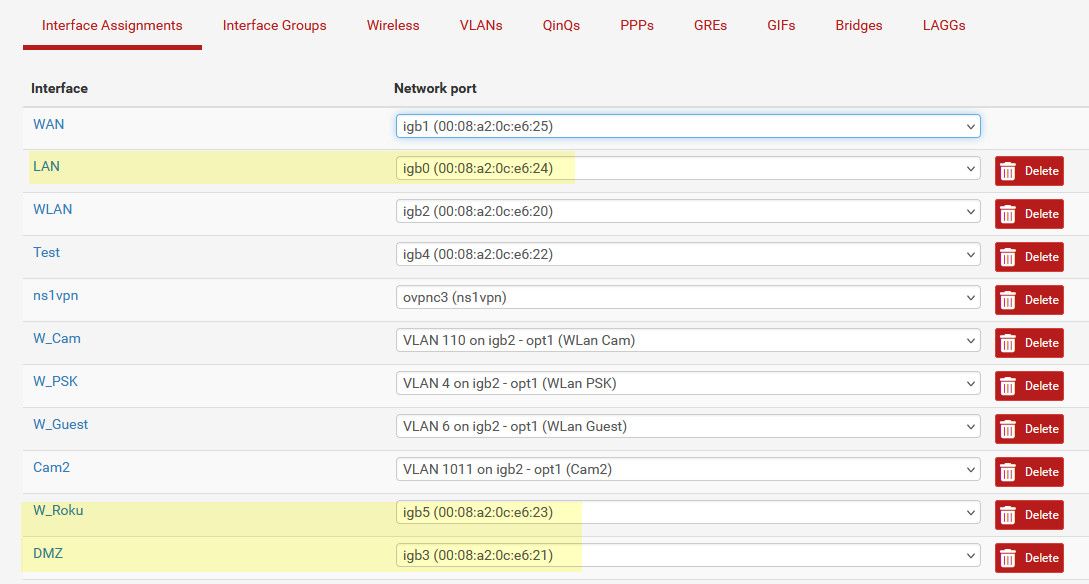
On my switch I have 3 different vlans created 9, 3 and 7 for these networks. I just used the 3rd octet number so its easy to remember.. my lan network is 192.168.9/24 my dmz is 192.168.3/24 and my roku is 192.168.7/24
Might make it easier for you to see if show this on the switch gui vs cli
These are the 3 ports on the switch those pfsense interfaces are connected too
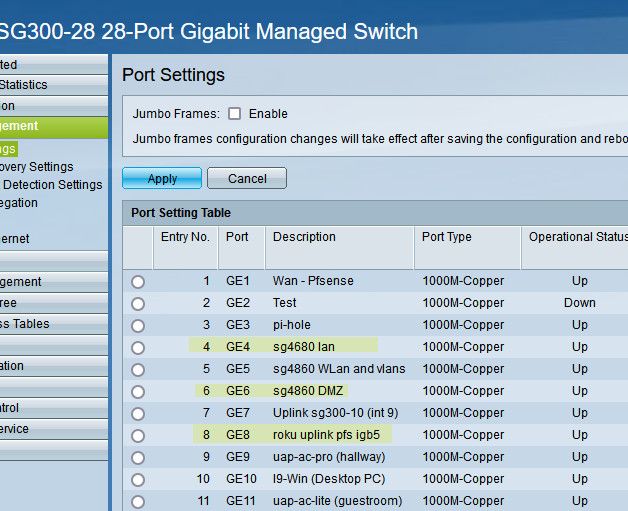
Now those ports on the switch are configured like this
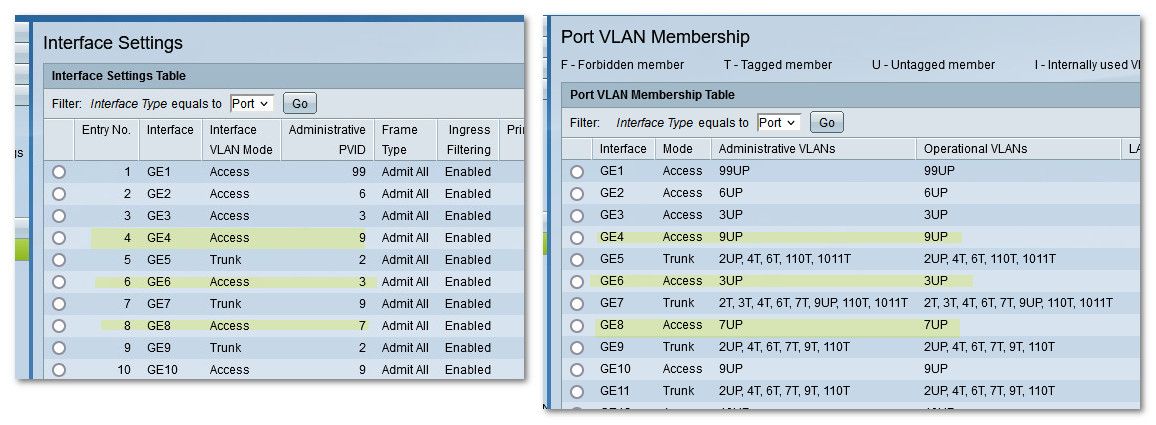
see pvid that is set, which is also shown on the vlan membership page as the P, the UP means Untagged and PVID vlan ID. All a pvid is what vlan on the switch the switch will put traffic that it sees coming in on that port untagged. Before you were isolating your networks with physical different switches. But when you want to keep these networks isolated on a vlan swtich, you have to tell the switch what vlans are what ports, etc even if the traffic is not tagged.
Even if the networks on pfsense are not actually vlans on pfsense, ie no TAG.. You still have to isolate that traffic on the switch by creating vlans..
Here are the vlans I have created on the switch
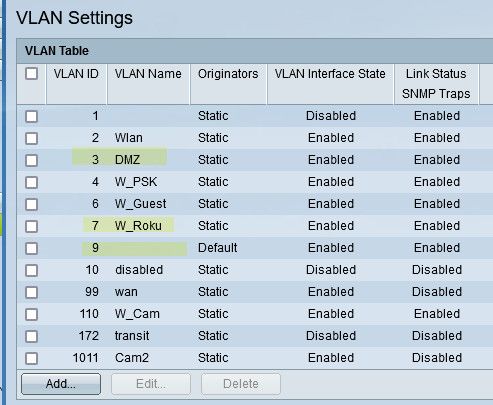
In my case my default vlan is set to 9 on the switch vs 1, the default vlan on most switches is 1 and many do not even allow you to change that.. I just changed mine so the ID would match up with the network I use on my lan of 192.168.9.0/24
You could prob do this on your switch with port vlans.. But using 802.1q is better option. Because now it will allow you in the future maybe to create a vlan on pfsense and carry this over the same physical port.. See for example those ports that are trunked and have multiple vlans listed on them.. Like port 7 on my switch that has 2,3,4,6,7,9,110 and 1011 all Tagged, see the T next to the number other than vlan 9 which is untagged.. you can only ever have 1 untagged vlan on a port.
That port 7 on my switch is an uplink to another switch that sits in my AV cabinet in my living room.. And I can put a port on that switch in any of those vlans.. For example one of my APs connects to that switch in the AV cab, and depending on what SSID you connect to puts you on that network/vlan.
-
@bookie56 said in Using Managed Switch for Company and Private Networks:
@Gblenn Sorry I am lost...
I was hoping to have the link for the LAN_PRIVATE which goes to Port 1 on the switch
I then was hoping to have the link for the LAN_COMPANY go to Port 17 on the switch...
If the above can't be done then I will have a separate switch for LAN_COMPANY and leave everything else on the new switch...This is why I have the quad using all 4....
bookie56Ah of course that's perfectly possible, exactly like @johnpoz describes it. You will essentially split your 24 port switch into two logical partitions, replacing your current dumb switches. And for that to work like you want, you don't need to do anything on the pfsense side at all.
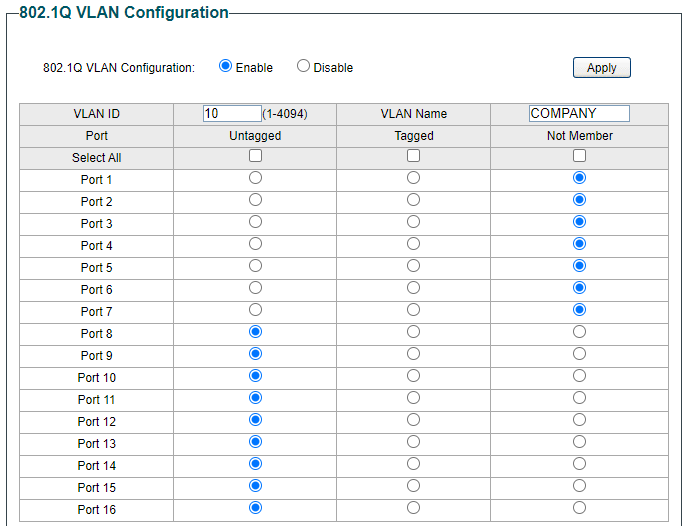
So going back to my example with the picture of the TPLink interface, you will do this (using my 16 port switch as an example)
First for PRIVATE (using VLAN tag 5 here)
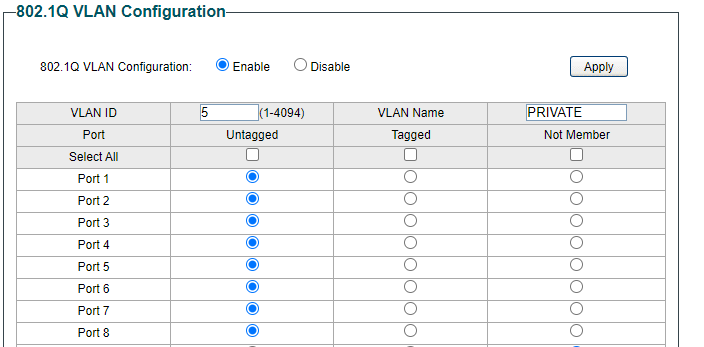
Then Update and Apply and then similarly for COMPANY (using VLAN tag 10)
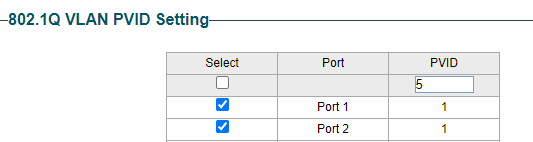
Then on the 802.1 VLAN PVID page you make ports 1-16 members of VLAN 5
And then ports 17 to 24 members of VLAN 10..Like this:
-
@Gblenn yup that works - only thing with those entry level vlan capable switches. He prob wants to use just the default vlan 1 as one of his network. Because this is the vlan the management of the switch will be on..
So for his say lan private, just use vlan 1, then create a new vlan be it 5 or 10 or whatever other ID he wants to use for his lan company..
But I like the idea of just splitting the switch into 2 vlans.. Ie 2 switches in 1 box, which is what vlans are - the ability really to create multiple switches (virtual lans) in one box..
And its also a good idea to keep all the ports in 1 vlan together.. So ports 1-8 are vlan 1, and ports 9-16 are the other vlan.. So ports 1-8 are his lan private "switch" and ports 9-16 are his lan company switch.. then port 1 connected to pfsense lan private interface, and say port 9 connected to his lan company interface on pfsense... Easy peasy, lemon squeezy ;)
edit - personally I would connect his AP to the switch as well.. This allows him then to put wired devices on either his wifi private or company network.. He could still leave his pfsense as is without having to create vlans on it.. And just 2 more uplinks from the switch for wifi private and company.
And if he ever wants more network than his 4 ports, then he can start tagging those vlans and use one of the physical uplinks from switch to pfsense to carry that vlan. I would hope his APs allow for vlans - this way he could place his AP in different parts of the house and client can connect to which ever one is closer and provides the best signal - doesn't matter if client is wifi private or company, etc.
-
@johnpoz Yes I just realized that and was meaning to edit my post accordingly, but you beat me to it...

So what johnpoz is saying is to keep the switch at default VLAN settings for all ports except 17-24. Only those ports do you make the changes I showed in the pictures...
You also need to do one more thing, which is to remove the VLAN 1 membership from those ports. So type 1 in the VLAN ID field and click Not Member for ports 17-24.
Similar to this (using 5-8 as an example for your COMPANY ports)
-
@Gblenn great reminder about removing vlan 1 from the ports you put into different vlan.. You would hope the switch would be "smart" enough to not allow you to have more than 1 untagged vlan on the same port.. But those tplinks don't have a great track record for understanding vlans to be honest ;)
There was a whole issue quite some time ago, where they wouldn't even let you remove vlan 1 if you put the port into a different vlan.
-
@johnpoz said in Using Managed Switch for Company and Private Networks:
@Gblenn yup that works - only thing with those entry level vlan capable switches. He prob wants to use just the default vlan 1 as one of his network. Because this is the vlan the management of the switch will be on..
edit - personally I would connect his AP to the switch as well.. This allows him then to put wired devices on either his wifi private or company network.. He could still leave his pfsense as is without having to create vlans on it.. And just 2 more uplinks from the switch for wifi private and company.
Agree but I guess he wants to keep the setup on pfsense untouched, with any rules etc that have already been created for the 4 subnets.
Perhaps move the COMPANY AP to the switch ports 17-24, and drop the WIFI_COMPANY interface on pfsense. There are no static leases on either of the COMPANY networks so why make it more complicated than needed.And if he ever wants more network than his 4 ports, then he can start tagging those vlans and use one of the physical uplinks from switch to pfsense to carry that vlan. I would hope his APs allow for vlans - this way he could place his AP in different parts of the house and client can connect to which ever one is closer and provides the best signal - doesn't matter if client is wifi private or company, etc.
Exactly, and those AP's do actually allow for VLANs and are compatible with Omada centralized management.
-
@Gblenn said in Using Managed Switch for Company and Private Networks:
setup on pfsense untouched, with any rules etc that have already been created for the 4 subnets.
He really wouldn't have to change anything on the pfsense side, he would just move the AP from the port on pfsense to port on the switch.. This would really give him more flexibility going forward.