ACCESS DIFFERENT VLAN ON A DIFFERENT PORT OF PFSENSE
-
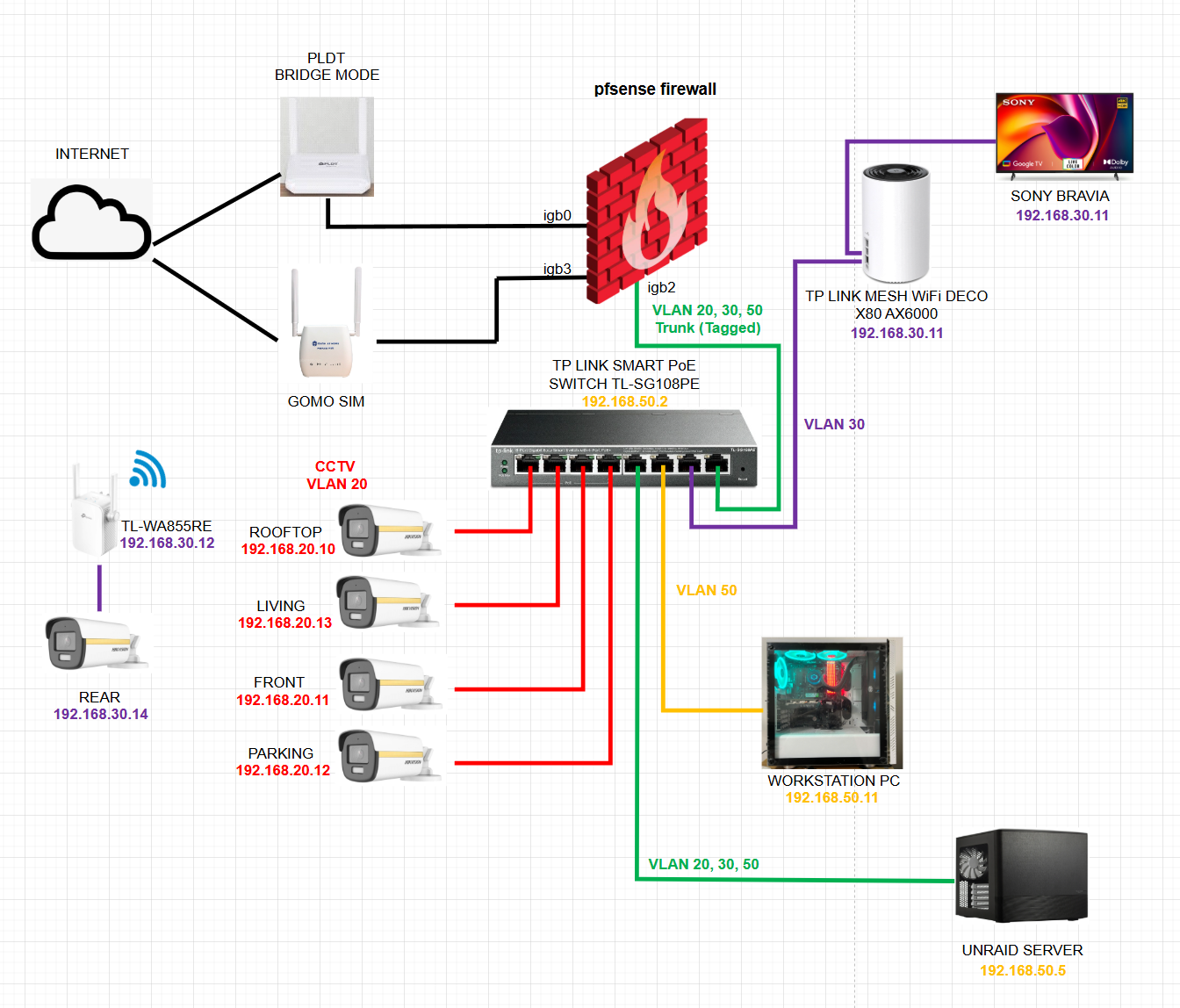
Here's my current setup:
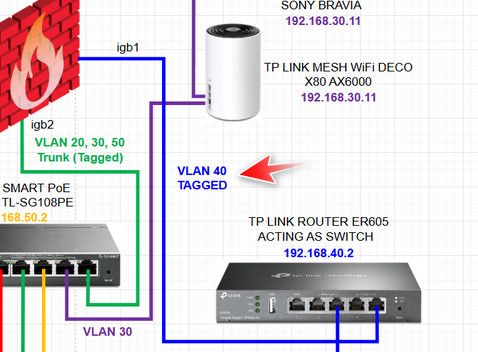
Now, I'm adding PiKVM to my setup, but I want to place it in a separate VLAN (VLAN40), and I will put it in the igb1 port of pfsense. However, I have no other switch port on my current setup, but I have a TP-Link router that was used before, and I can use it as a switch. I disabled its DHCP server setting, and the setup now looks like this:
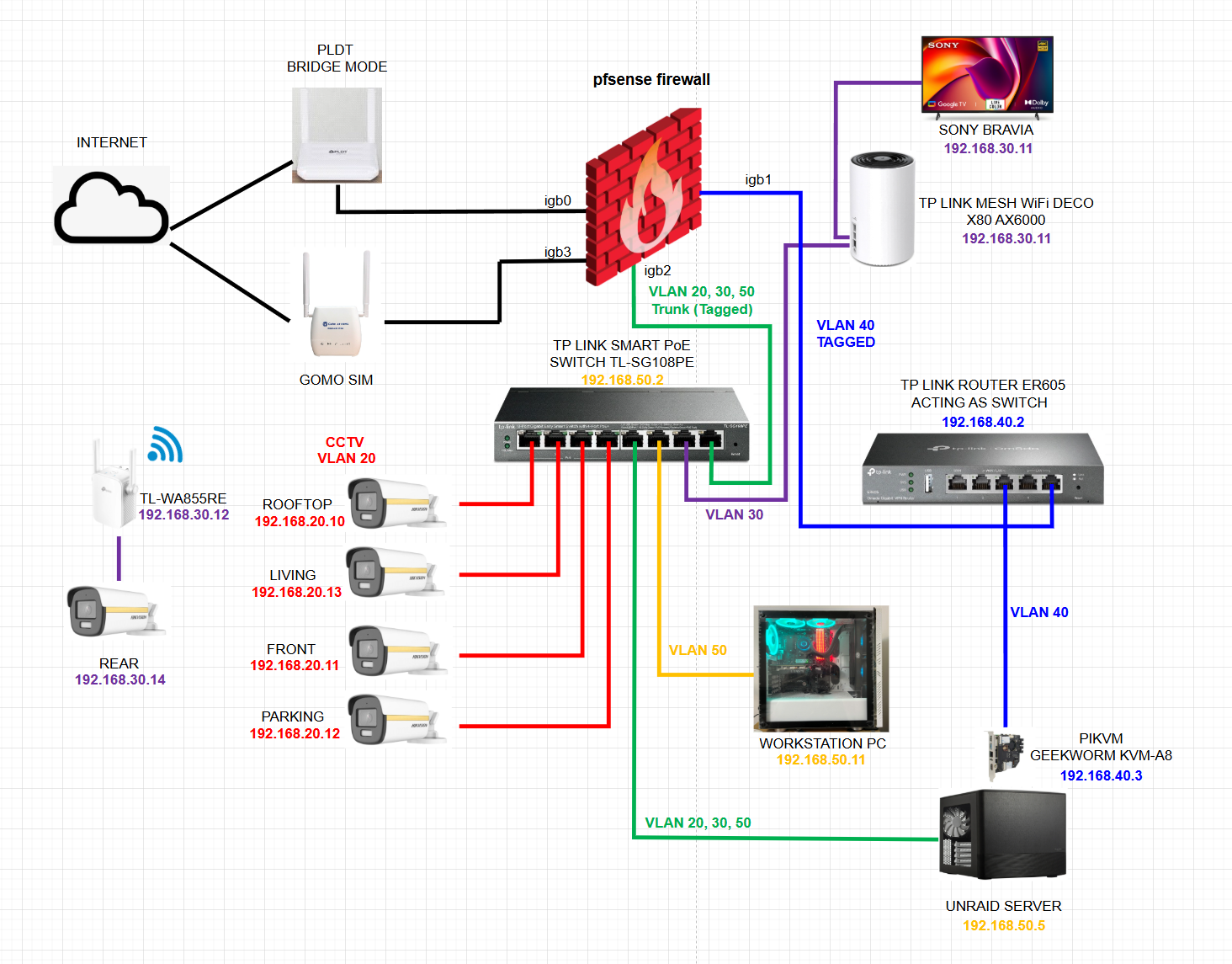
The PiKVM is working well. It's getting IP from pfsense (192.168.40.x), has internet access, can ping and access all other devices in different VLANs, and can even access pfsense itself.
But I cannot access PiKVM from the WORKSTATION PC or my UNRAID server. In pfsense, I added rules that ALLOW ALL traffic IN and OUT from VLAN 40 and VLAN 50. What could be the problem?
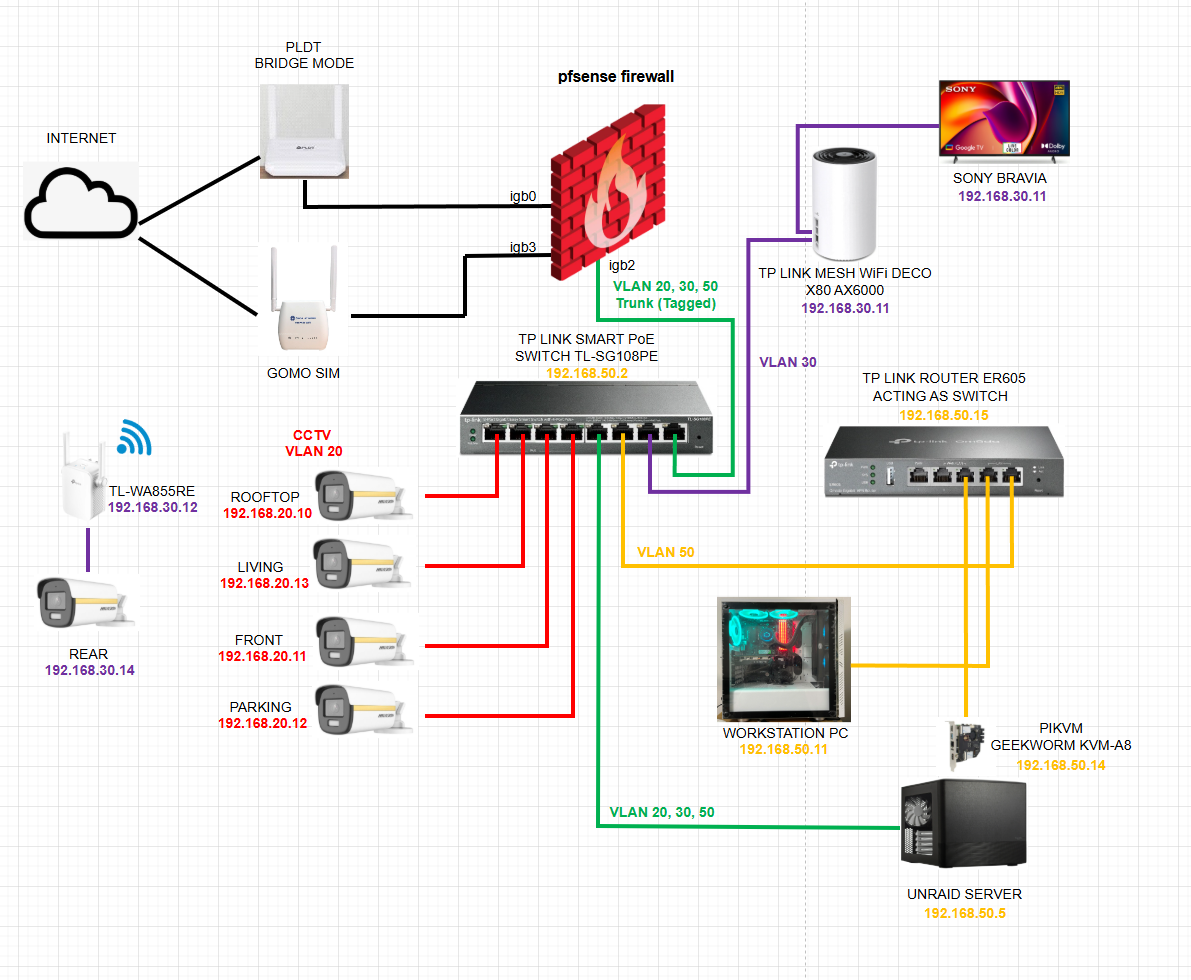
I ended up with the setup below. But I want to place PiKVM as much as possible in a different VLAN so I can add its own rules.
-
@HHUBS said in ACCESS DIFFERENT VLAN ON A DIFFERENT PORT OF PFSENSE:
But I cannot access PiKVM from the WORKSTATION PC or my UNRAID server.
On vlan 50 rules in pfsense - are you policy routing, ie sending traffic out some specific gateway/vpn
Your vlan 40 rules could be empty as long as rules on your vlan 50 allow the access to vlan 40.
If you are policy routing on vlan 50, you would need to bypass the policy route to talk to vlan 40
https://docs.netgate.com/pfsense/en/latest/multiwan/policy-route.html#bypassing-policy-routing
-
@johnpoz said in ACCESS DIFFERENT VLAN ON A DIFFERENT PORT OF PFSENSE:
@HHUBS said in ACCESS DIFFERENT VLAN ON A DIFFERENT PORT OF PFSENSE:
But I cannot access PiKVM from the WORKSTATION PC or my UNRAID server.
On vlan 50 rules in pfsense - are you policy routing, ie sending traffic out some specific gateway/vpn
Your vlan 40 rules could be empty as long as rules on your vlan 50 allow the access to vlan 40.
If you are policy routing on vlan 50, you would need to bypass the policy route to talk to vlan 40
https://docs.netgate.com/pfsense/en/latest/multiwan/policy-route.html#bypassing-policy-routing
I have only 1 rule in both VLAN 40 and 50, and to pass all traffic(for testing purposes). I will try your suggestion tomorrow using the bypass rule and will let you know then. BRB.
-
@HHUBS if all you have is any rule - not going to be a problem.. But if you have a gateway set on the rule that sends all traffic out your wan or vpn, then not going to work.. And you would need a bypass rule before you policy route out some specific gateway
-
@johnpoz said in ACCESS DIFFERENT VLAN ON A DIFFERENT PORT OF PFSENSE:
@HHUBS if all you have is any rule - not going to be a problem.. But if you have a gateway set on the rule that sends all traffic out your wan or vpn, then not going to work.. And you would need a bypass rule before you policy route out some specific gateway
I have only one any rule on VLAN 50. No other rules. If this is not going to be a problem, what problem could my setup be? Why on VLAN 50 can't access VLAN 40, but VLAN 40 can access all?
-
@HHUBS do you have any floating rules?
If your not sending out a gateway on your vlan 50 rules, and you have no floating..
I would sniff on pfsense vlan 40 interface - now run a ping from your say your pc on vlan 50 to the IP of your kvm 192.168.40.3 - do you see pfsense send out the ping request. Do you see a response?
oh:
Why are you tagging vlan 40 to that er605, you sure you have the vlans setup correctly on it.. if your directly connected to igb1 on pfsense - that network should/could just be just native, it should not be a vlan in pfsense. If your not going to put more networks on that specific interface there is little reason to tag it, especially if your sending to some switch that only will have that network on it, etc. -
@johnpoz said in ACCESS DIFFERENT VLAN ON A DIFFERENT PORT OF PFSENSE:
@HHUBS do you have any floating rules?
If your not sending out a gateway on your vlan 50 rules, and you have no floating..
I would sniff on pfsense vlan 40 interface - now run a ping from your say your pc on vlan 50 to the IP of your kvm 192.168.40.3 - do you see pfsense send out the ping request. Do you see a response?
I have no floating rules.
Why are you tagging vlan 40 to that er605, you sure you have the vlans setup correctly on it.. if your directly connected to igb1 on pfsense - that network should/could just be just native, it should not be a vlan in pfsense. If your not going to put more networks on that specific interface there is little reason to tag it, especially if your sending to some switch that only will have that network on it, etc.
If I don't tag vlan40 on switch er605, the PiKVM is not getting IP address from pfsense.
-
@HHUBS well I would do the sniff then.. So you can know for sure that pf is sending the traffic, and if the switch answers you. Maybe it has acl for its admin interface, and only local networks can access it.
You won't be 100% sure pfsense is actually sending, and to the right mac, etc..
You wouldn't have to tag on your switch if you didn't tag on pfsense..
That er605 has a firewall.. Maybe it only allows local network access to the web gui.. You could always do a source to pfsense IP on this vlan kvm is - so to the kvm your just coming from an IP on its local network.
-
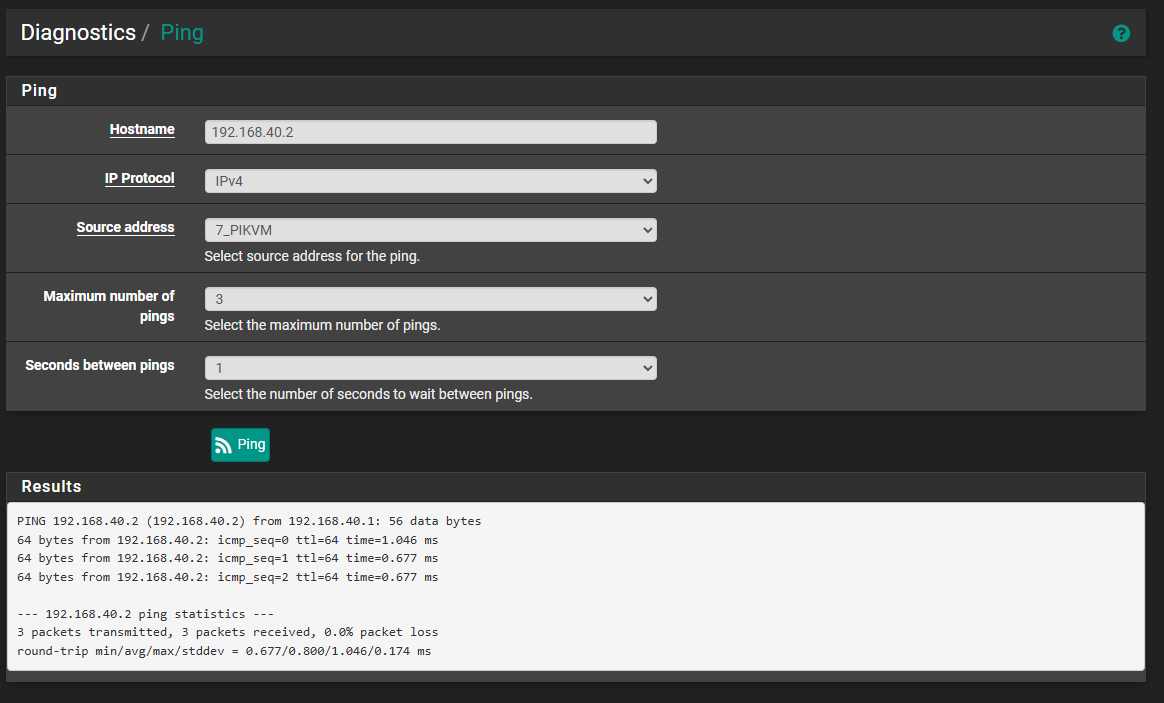
@johnpoz Hey brother, I can ping using the interface IP 192.168.40.1 to the TPLINK ER605 192.168.40.2
But I cannot ping the PiKVM(which for the mean time I use a laptop), 192.168.40.50 which is connected to ER605.
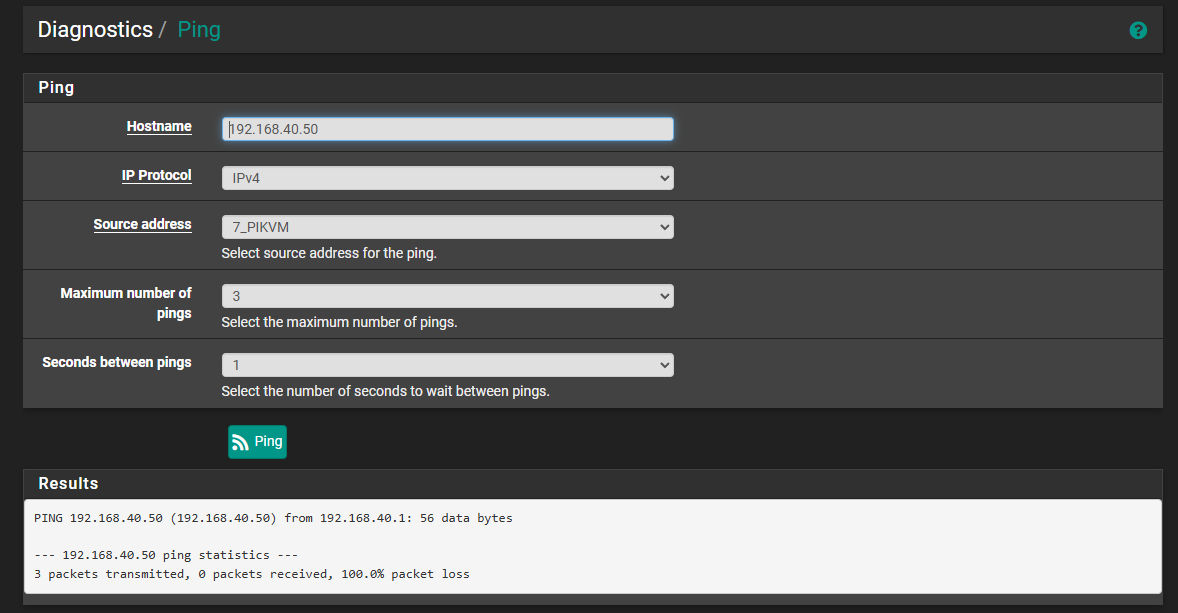
I also cannot ping 192.168.40.2 if my source address is the other VLAN except VLAN40.
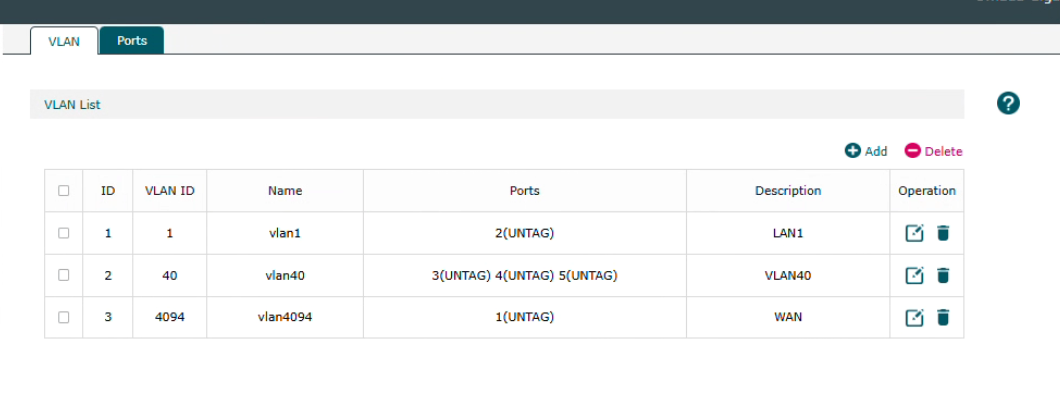
I have not use TAG VLAN40 in pFsense. It was directly connected and This is my settings in the ER605.
I can ping all other VLANs from the laptop 192.168.40.50.
-
@HHUBS and where is the simple packet capture I told you to do? We already knew your device didn't answer.. I just want to show you its not pfsense problem..
If your tagging out of pfsense?
Which port on the er605 is connected to pfsense - that port would have to be tagged for 40. The port connected from the er605 to your kvm wouldn't be tagged.
I don't show any ports tagged with 40 on your er605.. I show port 3,4 and 5 untagged 40.. So then your setup on pfsense that port should be just a native network and not a vlan.
if you connect pfsense igb1 to port 3 on your er605 and your tagging on pfsense (ie a vlan) then port 3 should be tagged 40 in your er605,f and then if port 5 is connected to your kvm - that would untagged 40.
If your going to set the er605 up with 3 ports in vlan 40 as untagged then pfsense interface needs to be just native untagged network.
-
I managed to solve this myself today. The reason I can't ping the client directly connected to the igc1 of pfsense is because of the Bitdefender stealth mode setting. Once I turned it off, I can now ping the client.
I came up with this solution because I tried Ubuntu on a flash drive, and I can ping it, so there is a problem with the firewall of the Windows machine.
That's why I checked all the firewall settings one by one on the Windows client.