pfBlockerNG not logging anything by default?
-
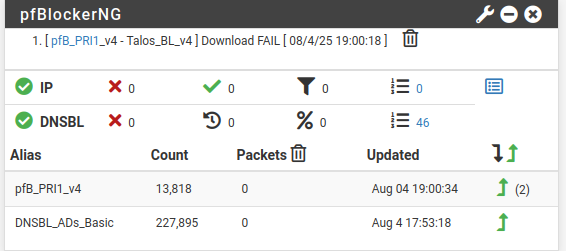
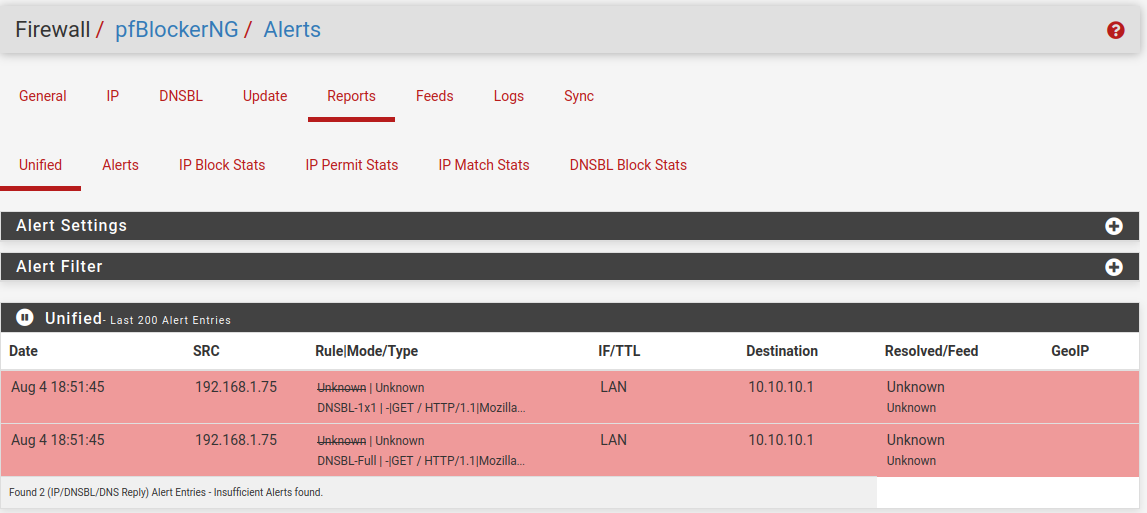
This :
did you execute that on the pfSense command line ?
This :
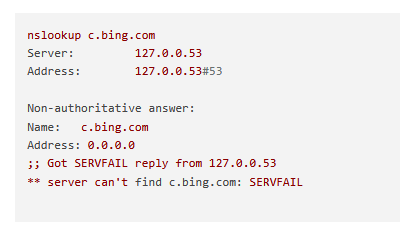
;; Got SERVFAIL reply from 127.0.0.53 ** server can't find c.bing.com: SERVFAILmeans that the device that you are using was told that its DNS is 127.0.0.53. (that is the device itself !)
But ... non DNS server is listing on that address.
That device, can't you set it to use DHCP ? If you do, it will get an IP, a network, a gateway and a DNS, where the last two will be the pfSense LAN IP. From then on, that device will have a working In tenet connection, local network and DNS. That's why every device you buy (create) use DHCP ... as it works out of the box.If I execute the same command on pfSense, I see :
[25.07-RELEASE][root@pfSense.bhf.tld]/root: nslookup c.bing.com Server: 127.0.0.1 Address: 127.0.0.1#53 Non-authoritative answer: c.bing.com canonical name = c-bing-com.ax-0001.ax-msedge.net. c-bing-com.ax-0001.ax-msedge.net canonical name = ax-0001.ax-msedge.net. Name: ax-0001.ax-msedge.net Address: 150.171.27.10 Name: ax-0001.ax-msedge.net Address: 150.171.28.10 Name: ax-0001.ax-msedge.net Address: 2620:1ec:33:1::10 Name: ax-0001.ax-msedge.net Address: 2620:1ec:33::10Your "127.0.0.53" tells me : the DNS request isn't asked from pfSense, which has some LAN IP and not a localhost IP - but a local DNS (resolver ? forwarder ?) - for for what I know, maybe this process doesn't use pfSense (== unbound => pfBLockerng ...)
hen I execute on a PC, situated on my pfSense LAN , I see :
C:\Users\Gauche>nslookup c.bing.com Serveur : pfSense.hf.tld Address: 2a01:cb19:dead:beef:92ec:77ff:fe29:392c Réponse ne faisant pas autorité : Nom : ax-0001.ax-msedge.net Addresses: 2620:1ec:33:1::10 2620:1ec:33::10 150.171.27.10 150.171.28.10 Aliases: c.bing.com c-bing-com.ax-0001.ax-msedge.netwhere "2a01:cb19:dead:beef:92ec:77ff:fe29:392c" is the LAN (IPv6) of my pfSense.
"pfSense.hf.tld" is the host name of my pfSense.This means my Windows PC uses pfSense as it's "DNS server", which is nice, as pfSense uses unbound as the server = the resolver, and unbound sues also pfBlockerng to filter.
My unbound settings are prertty default, I resolve with the resolver.@rasputinthegreatest said in pfBlockerNG not logging anything by default?:
Also any idea why I see this when I am not using google dns?
Not you, the person. Your devices, processes that are running on them, if you have something that is android (Google) base will use 8.8.8.8 as their role is : whatever you do, communicate it to Google (that is the deal). So, yeah, 8.8.8.8 (the reverse) can be looked up for.
It won't be pfSense that is looking for the reverse of 8.8.8.8. Netgate isn't Google, pfSense doesn't use 8.8.8.8. 8.8.8.8 is a resolver, pfSense has its own resolver (unbound). -
@Gertjan said in pfBlockerNG not logging anything by default?:
means that the device that you are using was told that its DNS is 127.0.0.53. (that is the device itself !)
But ... non DNS server is listing on that addressBut internet is working. It already uses DHCP. It is a Ubuntu device and afaik that's how the network manager works in Ubuntu. It is a link to another file in the conf. It still resolves to my pfsense 192.168.1.1 and I can see resolves from the Ubuntu devices IP in the logs. It might be a Ubuntu setting but I am not sure.
@Gertjan said in pfBlockerNG not logging anything by default?:
Serveur : pfSense.hf.tld
Address: 2a01:cb19:dead:beef:92ec:77ff:fe29:392cRéponse ne faisant pas autorité :
Nom : ax-0001.ax-msedge.net
Addresses: 2620:1ec:33:1::10
2620:1ec:33::10
150.171.27.10
150.171.28.10
Aliases: c.bing.com
c-bing-com.ax-0001.ax-msedge.netI am getting the same response on a Windows 10 device but c.bing.com is on the blocklist of DNSBL. So it should not work, right?
Maybe the issue comes from running Double-NAT? I have my ISP router (running Quad9DNS) and Pfsense sits behind it with a local IP as WAN IP.
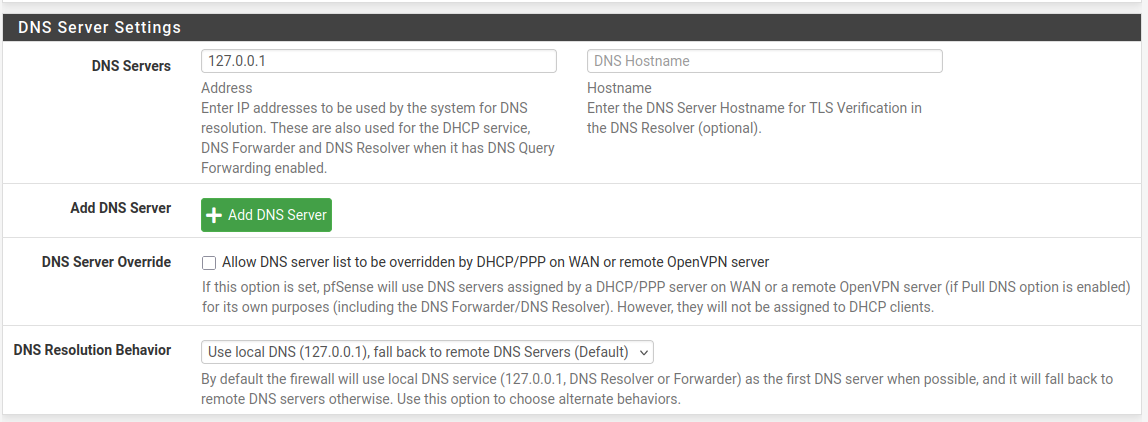
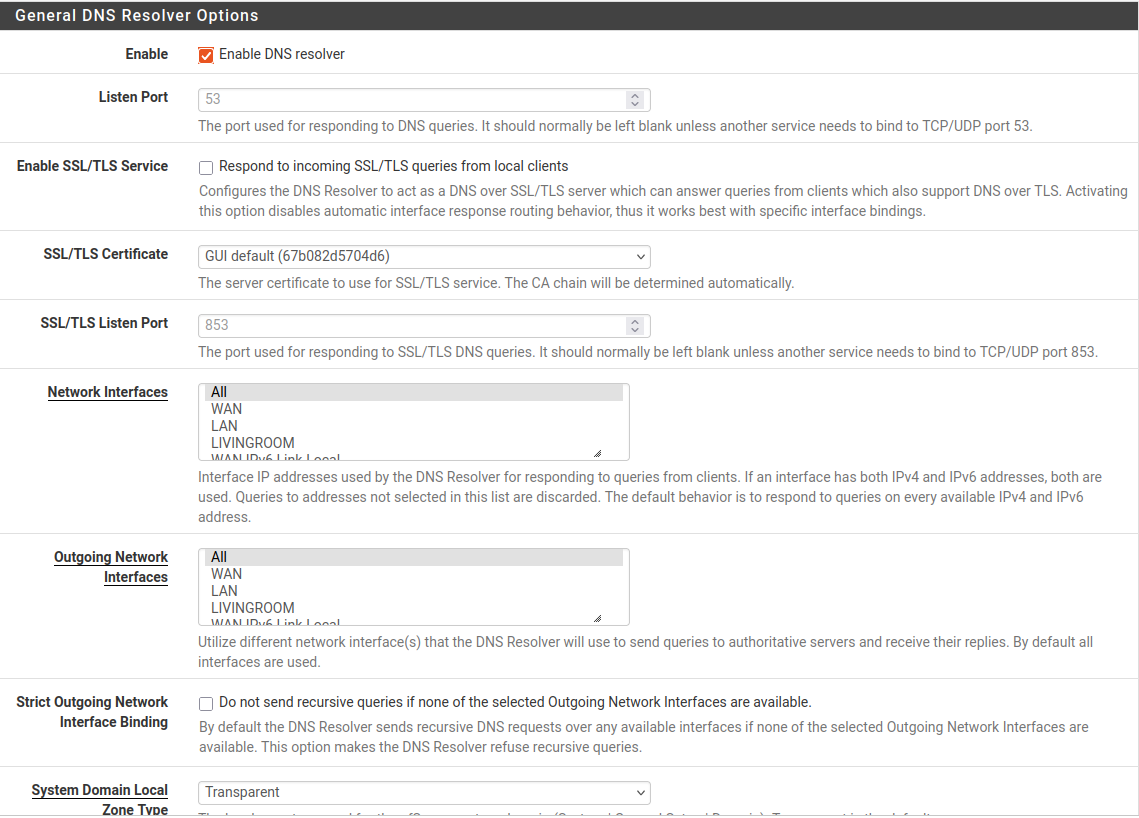
Here are my Unbound settings. General Setup I already showed above.
@Gertjan said in pfBlockerNG not logging anything by default?:
Your devices, processes that are running on them
There should be no device running google anywhere in my network.At least nothing behind pfsense.
-
@rasputinthegreatest said in pfBlockerNG not logging anything by default?:
It is a Ubuntu device
Ah, ok. I'm not familiar with Unbuntu but I do use Debian myself.
Like pfSense (based upon FreeBSD) there is file called /etc/resolv.conf which contains something like :nameserver 127.0.0.1 nameserver ::1 ....which means that programs process running on that system know where to go with their DNS requests.
Guess who listens on port 127.0.0.:53 on pfSense ?
Let's ask ;)
[25.07-RELEASE][root@pfSense.bhf.tld]/root: sockstat -4 | grep ':53'
avahi avahi-daem 61533 13 udp4 *:5353 :
unbound unbound 14531 5 udp4 *:53 :
unbound unbound 14531 6 tcp4 *:53 :
....If you Ubuntu was told that DNS requests have to send to 127.0.0.53 (probably port 53) then there must be a process that handles DNS requests listening on that address:port. If there is none, then you get a service fail or "SERV FAIL" as no DNS service is avaible.
That needs to be set up correced ^^@rasputinthegreatest said in pfBlockerNG not logging anything by default?:
I have my ISP router (running Quad9DNS)
I have also a ISP 'upstream' router. Somewhat mandatory for me as that device knows how to talk to the 'laser led wire' (fiber) and handles the login against my ISP.
My ISP router probably uses the ISP's DNS servers, I'm not sure.
pfSense gets a WAN IP from this ISP router, which will be a RFC1918 like 192.168.10.4.
By default, pfSense won't use an DNS suggestion that comes with the lease from the ISP routers DHCP server, as (my) pfSense resolves.Here are my Unbound settings. General Setup I already showed above
Pretty default so you're good.
-
@Gertjan In my resolv.conf I see this:
GNU nano 7.2 /etc/resolv.conf # /etc/resolv.conf and seeing this text, you have followed the symlink. # # This is a dynamic resolv.conf file for connecting local clients to the # internal DNS stub resolver of systemd-resolved. This file lists all # configured search domains. # # Run "resolvectl status" to see details about the uplink DNS servers # currently in use. # # Third party programs should typically not access this file directly, but only # through the symlink at /etc/resolv.conf. To manage man:resolv.conf(5) in a # different way, replace this symlink by a static file or a different symlink. # # See man:systemd-resolved.service(8) for details about the supported modes of # operation for /etc/resolv.conf. nameserver 127.0.0.53 options edns0 trust-ad search .If I follow the commentary and use "resolvectl status" I get this:
Global Protocols: -LLMNR -mDNS -DNSOverTLS DNSSEC=no/unsupported resolv.conf mode: stub Link 2 (wlp4s0) Current Scopes: DNS Protocols: +DefaultRoute -LLMNR -mDNS -DNSOverTLS DNSSEC=no/unsupported Current DNS Server: 192.168.1.1 DNS Servers: 192.168.1.1DNSSEC is enabled in Pfsense but doesnt seem to work in Ubuntu. Maybe DNSOverTLS is the issue? I read about that somewhere in regards to DNSBL.
Your sockstat command does not work on Ubuntu. I only see an active TCP connection from google that contains 53 in the port number
So you are pretty much running the same setup as me. I don't know what I am missing that is not working here.
-
@rasputinthegreatest said in pfBlockerNG not logging anything by default?:
Your sockstat command does not work on Ubu
That's normal. pfSense isn't Ubunutu (Debian, = Linux based).
It's using another ODS : FreeBSD.
So some commands look the same, some don't.This returns somewhat the same results :
netstat -naptul | grep ':53'Is this "Link 2 (wlp4s0)" your Ubuntu interface ?
The option "-DNSOverTLS" mighty in indicate that DNSOverTLS should be used ?
You are the Unbun user, so you tell me.
I know that the pfSense unbound doesn't use the TLS port :
as that port (TCP, port 953) needs to be activated so DNS TLS is supported.
As pSense uses a DNSSEC capable resolver, no need to for Ubuntu to deal with DNSSEC.
Use this https://wander.science/projects/dns/dnssec-resolver-test/ from a LAN 'PC' device and a browser and you'll see ;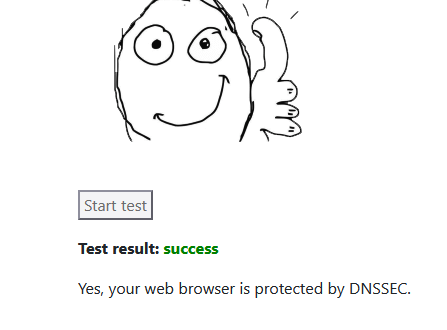
If your PC (or browser settings !!) use another DNS - not pfSense, well, that you might see different results.
-
@Gertjan I am suddenly seeing werid resolves:
192.168.1.31 reply A | A 86400 ipv4only.arpa 192.0.0.170 unkWhat could that be?
I also saw192.168.1.85 reply A | SOA 3140 desktop-AbTuMTYW.local SOA unkNone of these things exist on my network. Why is it resolving these things?
@Gertjan said in pfBlockerNG not logging anything by default?:
As pSense uses a DNSSEC capable resolver, no need to for Ubuntu to deal with DNSSEC.
Use this https://wander.science/projects/dns/dnssec-resolver-test/ from a LAN 'PC' device and a browser and you'll see ;This succeded
@Gertjan said in pfBlockerNG not logging anything by default?:
Is this "Link 2 (wlp4s0)" your Ubuntu interface ?
Yes it is. If I use the netstat command I see:
tcp 0 0 127.0.0.53:53 0.0.0.0:* LISTEN 792/systemd-resolve tcp 0 0 127.0.0.54:53 0.0.0.0:* LISTEN 792/systemd-resolve udp 0 0 127.0.0.54:53 0.0.0.0:* 792/systemd-resolve udp 0 0 127.0.0.53:53 0.0.0.0:* 792/systemd-resolve udp 0 0 0.0.0.0:5353 0.0.0.0:* 1071/avahi-daemon: udp6 0 0 :::5353 :::* 1071/avahi-daemon: -
@rasputinthegreatest said in pfBlockerNG not logging anything by default?:
What could that be?
Locate the device "192168.1.31", it's a device on your LAN. That 's the one who wanted to, knwo the 'A' or IPv4 of the host name "ipv4only.arpa".
Unbound was just answering : it's "192.0.0.170" to 192.168.1.31.@rasputinthegreatest said in pfBlockerNG not logging anything by default?:
None of these things exist on my network. Why is it resolving these things?
192.168.1.85 doesn't exist on your LAN ?
Not in the arp cache ?
Not a DHCP lease (might be a device with a static setup) ?@rasputinthegreatest said in pfBlockerNG not logging anything by default?:
tcp 0 0 127.0.0.53:53 0.0.0.0:* LISTEN 792/systemd-resolve
tcp 0 0 127.0.0.54:53 0.0.0.0:* LISTEN 792/systemd-resolve
udp 0 0 127.0.0.54:53 0.0.0.0:* 792/systemd-resolve
udp 0 0 127.0.0.53:53 0.0.0.0:* 792/systemd-resolveWell well, there you have you Ubuntu DNS !
You saw the name of the system process, : is "systemd-resolve" a resolver ? If so, then your Ubuntu totally bypasses the pfSense resolver (and pfBlockerng) . This means that DNS requests made by your Unbuntu are being handled by Ubuntus own resolver.edit : when your Ubuntu tries to use this 127.0.0.53 ( systemd/resolve ) it errors out .... (the serv fail)
Without details, set your system to, use 192.168.1.1 = pfSense, and you'll be good.
That said, it's your system. Time to check things out ?! -
@Gertjan said in pfBlockerNG not logging anything by default?:
192.168.1.85 doesn't exist on your LAN ?
This IP does exist on my LAN but why it resolves some weird random desktop-sdshdsd.local?
I am overwhelmed by the logs and see so much weird stuff like this. None of these things are on my network. Also no 192.168.51.5 exists on my network either.
DNS-reply,Aug 5 12:42:25,reply,A,NSEC,1835,desktop-A5k217Qu.local,192.168.1.86,NXDOMAIN,unk DNS-reply,Aug 5 10:09:22,reply,A,SOA,2942,hometheater-tQNIYv.local,192.168.1.86,SOA,unk DNS-reply,Aug 5 14:22:28,reply,A,SOA,3146,desktop-ZmWfGXFW.local,192.168.1.86,SOA,unk DNS-reply,Aug 5 10:38:49,local,PTR,PTR,Unk,10.34.1.10.in-addr.arpa,192.168.1.86,NXDOMAIN,unk DNS-reply,Aug 5 10:39:03,local,PTR,PTR,Unk,5.51.168.192.in-addr.arpa,192.168.1.86,NXDOMAIN,unk DNS-reply,Aug 5 10:39:09,local,PTR,PTR,Unk,10.170.0.10.in-addr.arpa,192.168.1.86,NXDOMAIN,unk DNS-reply,Aug 5 11:21:24,reply,A,SOA,2827,hometheater-WADQ2.local,192.168.1.86,SOA,unkI checked the pfblockerng logs and at 11:59:58 I see all these resolve. I assume it is related to time servers? I cant find any good info on what zorac.sf-bay.org is for example?
EDIT: Seems to be related to Perl which is used by pfsense plugins. But just a guess.DNS-reply,Aug 5 11:59:58,resolver,AAAA,AAAA,86400,anyns.pch.net,127.0.0.1,2001:500:14:6004:ad::1,unk DNS-reply,Aug 5 11:59:58,resolver,A,A,86400,anyns.pch.net,127.0.0.1,204.61.216.4,unk DNS-reply,Aug 5 11:59:58,resolver,A,A,57600,f.ntpns.org,127.0.0.1,139.178.72.201,unk DNS-reply,Aug 5 11:59:58,resolver,AAAA,AAAA,57600,f.ntpns.org,127.0.0.1,2a05:dfc1:cb1:123::,unk DNS-reply,Aug 5 11:59:58,resolver,A,A,86400,dns2.udel.edu,127.0.0.1,128.175.13.17,unk DNS-reply,Aug 5 11:59:58,resolver,AAAA,SOA,600,dns1.udel.edu,127.0.0.1,SOA,unk DNS-reply,Aug 5 11:59:58,resolver,AAAA,SOA,600,dns2.udel.edu,127.0.0.1,SOA,unk DNS-reply,Aug 5 11:59:58,resolver,A,A,86400,ns1.eu.bitnames.com,127.0.0.1,165.227.133.206,unk DNS-reply,Aug 5 11:59:58,resolver,AAAA,AAAA,86400,ns1.eu.bitnames.com,127.0.0.1,2a03:b0c0:3:d0::c0:4001,unk DNS-reply,Aug 5 11:59:58,resolver,A,A,3600,osdn.services.net,127.0.0.1,192.55.226.68,unk DNS-reply,Aug 5 11:59:58,resolver,A,A,57600,e.ntpns.org,127.0.0.1,45.33.123.43,unk DNS-reply,Aug 5 11:59:58,resolver,A,A,57600,c.ntpns.org,127.0.0.1,2.59.255.53,unk DNS-reply,Aug 5 11:59:58,resolver,AAAA,SOA,600,dns2.udel.edu,127.0.0.1,SOA,unk DNS-reply,Aug 5 11:59:58,resolver,AAAA,SOA,600,dns1.udel.edu,127.0.0.1,SOA,unk DNS-reply,Aug 5 11:59:58,resolver,AAAA,SOA,300,zorac.sf-bay.org,127.0.0.1,SOA,unk DNS-reply,Aug 5 11:59:58,resolver,A,SOA,300,zorac.sf-bay.org,127.0.0.1,SOA,unk DNS-reply,Aug 5 11:59:58,resolver,A,A,10400,g.ntpns.org,127.0.0.1,212.12.50.229,unk DNS-reply,Aug 5 11:59:58,resolver,A,A,3600,sdn.iecc.com,127.0.0.1,72.249.171.254,unk DNS-reply,Aug 5 11:59:58,resolver,AAAA,AAAA,57600,e.ntpns.org,127.0.0.1,2400:6180:0:d1::695:5001,unk DNS-reply,Aug 5 11:59:58,resolver,AAAA,AAAA,3600,sdn.iecc.com,127.0.0.1,2606:4300:0:4::106e,unk DNS-reply,Aug 5 11:59:58,resolver,A,A,3600,sdn.iecc.com,127.0.0.1,72.249.171.254,unk DNS-reply,Aug 5 11:59:58,resolver,AAAA,AAAA,3600,osdn.services.net,127.0.0.1,2001:470:1f07:1126:4e:6f74:6269:6e64,unk DNS-reply,Aug 5 11:59:58,resolver,AAAA,AAAA,57600,c.ntpns.org,127.0.0.1,2600:3c02::f03c:92ff:fe5f:baf1,unk DNS-reply,Aug 5 11:59:58,resolver,AAAA,AAAA,3600,ns2.everett.org,127.0.0.1,2001:470:1:205::230,unk DNS-reply,Aug 5 11:59:58,resolver,A,A,86400,ns2.us.bitnames.com,127.0.0.1,107.170.182.174,unk DNS-reply,Aug 5 11:59:58,resolver,AAAA,SOA,300,zorac.sf-bay.org,127.0.0.1,SOA,unk DNS-reply,Aug 5 11:59:58,resolver,AAAA,AAAA,3600,sdn.iecc.com,127.0.0.1,2606:4300:0:4::106e,unk DNS-reply,Aug 5 11:59:58,resolver,A,A,86400,ns3.us.bitnames.com,127.0.0.1,68.183.187.150,unk DNS-reply,Aug 5 11:59:58,resolver,A,A,57600,d.ntpns.org,127.0.0.1,86.109.15.15,unk@Gertjan said in pfBlockerNG not logging anything by default?:
Without details, set your system to, use 192.168.1.1 = pfSense, and you'll be good.
I did that but it hasn't changed anything. This was a default Ubuntu install and it has something to do with systemd-resolve but I can't figure it out myself.
@Gertjan said in pfBlockerNG not logging anything by default?:
You saw the name of the system process, : is "systemd-resolve" a resolver ? If so, then your Ubuntu totally bypasses the pfSense resolver (and pfBlockerng) . This means that DNS requests made by your Unbuntu are being handled by Ubuntus own resolver.
But why do I see stuff being resolved in pfblockerNG if it should be bypassed?
-
I am seeing all these strange things resolve in pfblockerNG like
devmachine-FKcElwG.local hometheater-wadq2.localWhy am I seeing this? Does this mean my network is compromised?
-
The situation is getting worse. I now see alot of strange stuff from 127.0.0.1
DNS-reply,Aug 6 09:10:26,resolver,A,A,299,fueled.byhamsters.net,127.0.0.1,69.65.50.223,unkAlienvault says Suspicious Dynamic DNS Update Request
https://otx.alienvault.com/indicator/ip/69.65.50.223Also I see this. Constantly newly named .local adresses despite having blocked port 5353 on the firewall.
devmachine-FKcElwG.local mypc-DogOjT5.local desktop-ZmWfGXFW.local desktop-A5k217Qu.local hometheater-WADQ2.local hometheater-tQNIYv.local hometheater-ejsl1t.local surveillance-GanzOF.local mediacenter-VAY4Bk.localI don't see any of these things in the Status -> DNS Resolver nor in any active states on my firewall.
Its very mysterious and I only see this now with pfblockerNG. My work computer but also my private laptop made some of these DNS requests or just picked up some broadcast? But most of the stuff I see originates from 127.0.0.1. All these names seem so randomly generated but the surveillance part makes me extra worried. Or are the DNSBL lists generating them somehow?Any help is appreciated since it is unnerving me.
EDIT: I found this which seems to be somewhat related https://serverfault.com/questions/1053970/weird-wpad-dns-queries-anyone-seen-this
-
@rasputinthegreatest said in pfBlockerNG not logging anything by default?:
This IP does exist on my LAN but why it resolves some weird random desktop-sdshdsd.local?
Then it's time to visit that device "192.168.1.85", and inspect it.
pfSense was just replies on a DNS request coming from it.
Loads of DNS request is 'normal' these days.Btw : buy yourself a big collection of connected devices (preference : 'foreign origin") and you wind up with loads of bizarre DNS requests.
For example, a classic "Windows 11 Home" PC is already considered as 'bloated', which means that the list of all these xbox, candy store and other 'essential' processes is quiet big? And they all call 'home'.
And ask yourself this question : "do you really know what users actually do with their devices" ?@rasputinthegreatest said in pfBlockerNG not logging anything by default?:
Also no 192.168.51.5 exists on my network either
Is "192.168.51.5" a typo ? It doesn't show up in any logs ...
If your pfSense LAN uses the 192168.1.1/24 network, and a device connected to that LAN using the 192.168.51.5, it can't communicate.
A network with statically assigned IP info (IP, mask/network, gateways and DNS) is hard to manage. That's why DHCP was invented, and activated by default for every device you buy.@rasputinthegreatest said in pfBlockerNG not logging anything by default?:
I assume it is related to time servers?
Why do you presume that ?
Look them up and you'll see."ntpns.org" is probably the NS server of ntp.org

A lot of devices want to know the exact time.
Even when DHCP can propose a time server - you can set up pfSense as a time server for your LAN devices - many devices will disregard this info, an insist in using their own hard coded time server source.
For example, a Microsoft PC will default to time.microsoft.com, but you can set it to 192.168.1.1 or pfsense.your-sense-domaine.tld (which will point to 192.168.1.1 = pfSense).
You could to do this for every LAN device.@rasputinthegreatest said in pfBlockerNG not logging anything by default?:
.local addresses
What is your pfSense domain set to ?
@rasputinthegreatest said in pfBlockerNG not logging anything by default?:
Its very mysterious and I only see this now with pfblockerNG.
Set : Services > DNS Resolver > Advanced Settings : Log Level to :
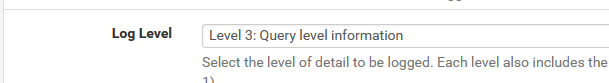
and save, apply.
Now have a loo here : Status > System Logs > System > DNS Resolveror better : console :
tail -f /var/log/resolver.logDon't forget to set back the Log Level to 1 !! ( !! ) as the resolver.log will get very big very fast.
Conclusion : there is a lot of DNS traffic. These are all small packets, and finally just a small percentage of the total traffic.
-
@Gertjan said in pfBlockerNG not logging anything by default?:
Is "192.168.51.5" a typo ? It doesn't show up in any logs .
DNS-reply,Aug 5 10:39:03,local,PTR,PTR,Unk,5.51.168.192.in-addr.arpa,192.168.1.86,NXDOMAIN,unkIt does but with reverse DNS
This all seems to happen since changing to Unbound Python mode. Or has a Hacker created a subnet? I can't see anything in pfsense related to that subnet or those domains being looked up. I also see for the first time in my firewall logs the information next to WAN saying "Direction is out". Never saw this before. I feel like something opened up since installing pfblockerNG .
I am the only one using the devices behind pfsense. Its just a work computer and a laptop. Both create these weird DNS requests to hometheater-%RANDOMSTRING%.local for example. But its mostly my work computer doing these lookups@Gertjan said in pfBlockerNG not logging anything by default?:
What is your pfSense domain set to ?
mypfsense.arpa not even .local. But I see these logged by pfblockerNG with "local.home.arpa"
AAAA,AAAA,Unk,hometheater-wadq2.local.home.arpa,127.0.0.1,ServFail,unkI just don't understand all these domains and they sound sus if you take a look:
devmachine-FKcElwG.local mypc-DogOjT5.local desktop-ZmWfGXFW.local desktop-A5k217Qu.local hometheater-WADQ2.local hometheater-tQNIYv.local hometheater-ejsl1t.local surveillance-GanzOF.local fileshare-7JksiB.local mediacenter-VAY4Bk.localCan this just be randomly generated with no purpose? I tried packet captures of DNS traffic and these things dont show up there since they often orginate from 127.0.0.1
Or could it come from the ISP router in front of my pfsense? But it should block mDNS already afaik and even after blocking port 5353 I still see these .local things.
EDIT: Found something by @johnpoz here
https://forum.netgate.com/topic/146509/strange-dns-queries-from-pfsense/11
But the strings are much more random and less concrete in his example with gibberish.local.lan -
So something showed up again and the Unbound log shows nothing useful. No IP or who requested it. I guess the log level is not enough?
Aug 6 11:40:26 mypfsense unbound[24282]: [24282:0] debug: worker request: max UDP reply size modified (1472 to max-udp-size) Aug 6 11:40:28 mypfsense unbound[24282]: [24282:0] debug: validator[module 1] operate: extstate:module_state_initial event:module_event_pass Aug 6 11:40:28 mypfsense unbound[24282]: [24282:0] info: validator operate: query networkhub-Hfl1Jc.local. A IN Aug 6 11:40:28 mypfsense unbound[24282]: [24282:0] debug: iterator[module 2] operate: extstate:module_state_initial event:module_event_pass Aug 6 11:40:28 mypfsense unbound[24282]: [24282:0] info: resolving networkhub-Hfl1Jc.local. A IN Aug 6 11:40:28 mypfsense unbound[24282]: [24282:0] info: finishing processing for networkhub-Hfl1Jc.local. A IN Aug 6 11:40:28 mypfsense unbound[24282]: [24282:0] debug: validator[module 1] operate: extstate:module_wait_module event:module_event_moddone Aug 6 11:40:28 mypfsense unbound[24282]: [24282:0] info: validator operate: query networkhub-Hfl1Jc.local. A IN Aug 6 11:40:28 mypfsense unbound[24282]: [24282:0] info: validate(nxdomain): sec_status_secure Aug 6 11:40:28 mypfsense unbound[24282]: [24282:0] info: validation success networkhub-Hfl1Jc.local. A IN Aug 6 11:40:28 mypfsense unbound[24282]: [24282:0] debug: cache memory msg=124942 rrset=239262 infra=87934 val=85965 Aug 6 11:40:58 mypfsense unbound[24282]: [24282:1] debug: validator[module 1] operate: extstate:module_state_initial event:module_event_passNow i saw this with log level 2. Very little information still. I don't know what is being resolved here and why.
Aug 6 12:48:34 mypfsense unbound[35444]: [35444:3] info: resolving desktop-Am6uk.local. A IN Aug 6 12:48:34 mypfsense unbound[35444]: [35444:3] info: validate(nxdomain): sec_status_secure Aug 6 12:48:34 mypfsense unbound[35444]: [35444:3] info: validation success desktop-Am6uk.local. A IN -
Now i saw this with log level 2. Very little information still. I don't know what is being resolved here and why. I have found a correlation with my firewall in that moment. I see port 5353 being blocked by my user rule but also see port 5335 being blocked by a default rule
Aug 6 12:48:34 mypfsense unbound[35444]: [35444:3] info: resolving desktop-Am6uk.local. A IN Aug 6 12:48:34 mypfsense unbound[35444]: [35444:3] info: validate(nxdomain): sec_status_secure Aug 6 12:48:34 mypfsense unbound[35444]: [35444:3] info: validation success desktop-Am6uk.local. A IN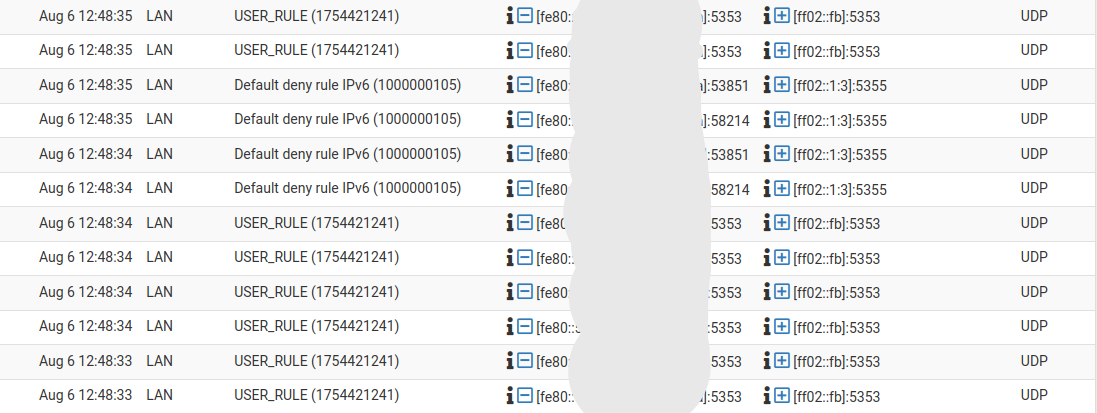
Is Unbound using port 5335? Would this be helpful to dig deeper?
-
@rasputinthegreatest said in pfBlockerNG not logging anything by default?:
It does but with reverse DNS
No.
It's :@rasputinthegreatest said in pfBlockerNG not logging anything by default?:
192.168.1.86
asking for the reverse (see the "PTR,PTR" indication) of
5.51.168.192.in-addr
@rasputinthegreatest said in pfBlockerNG not logging anything by default?:
This all seems to happen since changing to Unbound Python mode
Unbound didn't change.
When you activate 'python mode' - see the config file /var/unbound/unbound.conf, last 3 lines - you tell unbound that it should activate the Python extension of unbound. "Python" is what unbound uses to communicate with external modules (also called addons, or extensions etc). pfb_unbound.py is such an extension, and is present with pfBlockerng for faster integration.
This "pfb_unbound.py" is used by pfBockerng so it can sneak peak what DNS requests are handled for stats purposs, what to block, etc.@rasputinthegreatest said in pfBlockerNG not logging anything by default?:
devmachine-FKcElwG.local
mypc-DogOjT5.local
desktop-ZmWfGXFW.local
desktop-A5k217Qu.local
hometheater-WADQ2.local
hometheater-tQNIYv.local
hometheater-ejsl1t.local
surveillance-GanzOF.local
fileshare-7JksiB.local
mediacenter-VAY4Bk.localI think (
 ) that these have to do with Avahi. And you use (you know why ?) Avahi on your Ubuntu .... I could be wrong of course.
) that these have to do with Avahi. And you use (you know why ?) Avahi on your Ubuntu .... I could be wrong of course.@rasputinthegreatest said in pfBlockerNG not logging anything by default?:
Or could it come from the ISP router in front of my pfsense?
No.
Look at your WAN firewall rule. Normally, there are .... none !
So, the default firewall behavior applies : No traffic initiated on the pfSense WAN side can enter.@rasputinthegreatest said in pfBlockerNG not logging anything by default?:
Now i saw this with log level 2
That's why I proposed '3'.
Don't forget to revert it.And keep in mind : pfSense => Unbound (and thus pfBlockerng) only see DNS traffic that is received by unbound.
Devices on LAN(s) that ask DNS info from other DNS servers like 8.8.8.8 - their requests will never show up under unbound/pfBlockerng. -
@Gertjan said in pfBlockerNG not logging anything by default?:
I think (
 ) that these have to do with Avahi. And you use (you know why ?) Avahi on your Ubuntu .... I could be wrong of course.
) that these have to do with Avahi. And you use (you know why ?) Avahi on your Ubuntu .... I could be wrong of course.I dont think so.It happens from my Windows 10 computer. It orginates from the IP 192.168.1.86
@Gertjan said in pfBlockerNG not logging anything by default?:
Look at your WAN firewall rule. Normally, there are .... none !
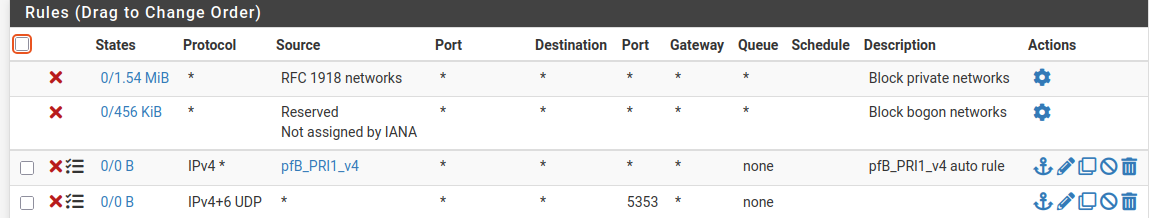
These are my WAN rules
@Gertjan said in pfBlockerNG not logging anything by default?:
That's why I proposed '3'.
What I posted was log level 3. Doesn't give any information. It just appears
Aug 6 11:40:26 mypfsense unbound[24282]: [24282:0] debug: worker request: max UDP reply size modified (1472 to max-udp-size) Aug 6 11:40:28 mypfsense unbound[24282]: [24282:0] debug: validator[module 1] operate: extstate:module_state_initial event:module_event_pass Aug 6 11:40:28 mypfsense unbound[24282]: [24282:0] info: validator operate: query networkhub-Hfl1Jc.local. A IN Aug 6 11:40:28 mypfsense unbound[24282]: [24282:0] debug: iterator[module 2] operate: extstate:module_state_initial event:module_event_pass Aug 6 11:40:28 mypfsense unbound[24282]: [24282:0] info: resolving networkhub-Hfl1Jc.local. A IN Aug 6 11:40:28 mypfsense unbound[24282]: [24282:0] info: finishing processing for networkhub-Hfl1Jc.local. A IN Aug 6 11:40:28 mypfsense unbound[24282]: [24282:0] debug: validator[module 1] operate: extstate:module_wait_module event:module_event_moddone Aug 6 11:40:28 mypfsense unbound[24282]: [24282:0] info: validator operate: query networkhub-Hfl1Jc.local. A IN Aug 6 11:40:28 mypfsense unbound[24282]: [24282:0] info: validate(nxdomain): sec_status_secure Aug 6 11:40:28 mypfsense unbound[24282]: [24282:0] info: validation success networkhub-Hfl1Jc.local. A IN Aug 6 11:40:28 mypfsense unbound[24282]: [24282:0] debug: cache memory msg=124942 rrset=239262 infra=87934 val=85965 Aug 6 11:40:58 mypfsense unbound[24282]: [24282:1] debug: validator[module 1] operate: extstate:module_state_initial event:module_event_passBut do you understand why I see port 5353 and port 5355 in my firewall log?
-
@rasputinthegreatest said in pfBlockerNG not logging anything by default?:
But do you understand why I see port 5353 and port 5355 in my firewall log?
Check : port 5353
so what is mDNS ? => More fact checking : Avahi (software) and now you reached the point why I was thinking about Avahi (Bonjour etc).
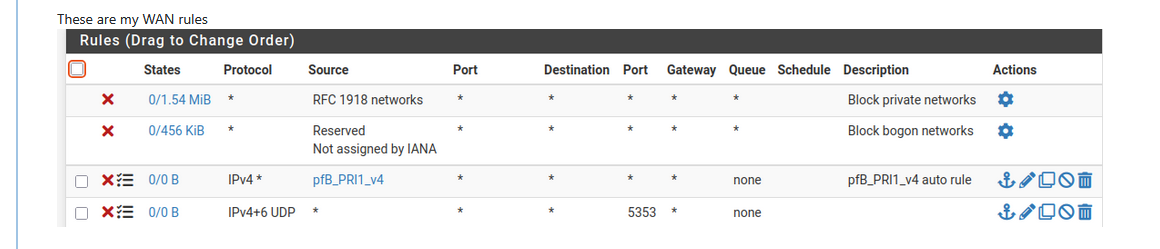
Normally, there would be pass rules, for example if you have NAT rules.
Blocking stuff that will get blocked anyway : ok, but not needed.
So KIS wins : don't even bother to blocking what will get blocked anyway.The counters show :
these two rules didn't capture any traffic.
@rasputinthegreatest said in pfBlockerNG not logging anything by default?:
It just appears
So shown is all the DNS traffic and other internal stages) that unbound received from 11:40:26 to 11:40:58, about 30 seconds.
That's close to 'nothing'. -
@Gertjan said in pfBlockerNG not logging anything by default?:
The counters show :
Yeah it didn't happen on WAN. And on LAN the counter also shows nothing for the 5353 rule I setup despite it being blocked in the firewall log. I guess it was redundant.
@Gertjan said in pfBlockerNG not logging anything by default?:
so what is mDNS ? => More fact checking : Avahi (software) and now you reached the point why I was thinking about Avahi (Bonjour etc).
I read about this as well and often people say it relates to Apple devices but my Apple devices are in front of pfsense and not behind the firewall. And the DNS queries still sound fishy to me especially coming from my work computer. I asked my IT if these domains sound familiar to them but obviously not so it must be inside my LAN. I did Wireshark captures but nothing shows up or is encrypted.
I know you say it's nothing but why am I even seeing this in the first place? It makes me feel uneasy and still would like to know if this is just random or something nefarious. My Windows desktop is using FortiClient and MS Sharepoint and I have read about a lot of attacks on both of these lately.
I don't know why the names would be so specific like "surveillance", "desktop", "hometheater","networkhub", "fileshare" and "devmachine". There is nothing on my network that ever used any of these terms.
It seems a little like wildcard poking I see by bots if you own your own website on Cloudflare. They try out all sorts of names to see if anything is there. -
@rasputinthegreatest said in pfBlockerNG not logging anything by default?:
I know you say it's nothing but why am I even seeing this in the first place?
Test this :
Install a pfSense with its WAN into an existing network. Default, the pfSense WAN uses DHCP, so it's "plug and play".
Hook up a switch to LAN - don'(t sue any other of the switch port. Leave them empty.
Use the pfSense console access to analyze logs.
Make sure that .... there are very few or no DNS look ups.
May one ne in a while, asking for abcd.netgate.com or some other pfsense.org domain as pfSense tests ones in a while if upgrades are avaible.
If you have set up a time service, you'll see that a time server is contacted.
And that's it.Now, populate your LAN.
All kind of traffics starts to show up. These come from your LAN devices.@rasputinthegreatest said in pfBlockerNG not logging anything by default?:
if you own your own website on Cloudflare. They try out all sorts of names to see if anything is there.
"Cloudflare" lives on the WAN side, also known as the Internet.
Nothing that lives out there can come into the WAN - not one bit. Ever.
( well, admins can do strange things, true, so lets presume a default pfSense install )
So, what can these bots do ? They can't use your resolver (unbound) to resolve stuff. They can't access your pfSense unbound from the outside.Bots that live on devices on your LAN : that's another story. All your other LAN devices are exposed now and pfSense can't do anything about it. That's why most devices have their own firewall.
-
@Gertjan said in pfBlockerNG not logging anything by default?:
Install a pfSense with its WAN into an existing network. Default, the pfSense WAN uses DHCP, so it's "plug and play".
So you mean build a new computer with pfsense again? My pfsense is already part of an existing network since I run double-nat. I have only my ISP network to test from. Could a managed switch be the culprit somehow?
@Gertjan said in pfBlockerNG not logging anything by default?:
Use the pfSense console access to analyze logs.
Don't I have to connect a device to access pfsense or how would I do that?