Access OPT1 AP from LAN
-
Change your OPT1 rule so instead of allowing any as the destination, it allows 'not LAN net'.
-
I use these rules for some years on my Portal interface:
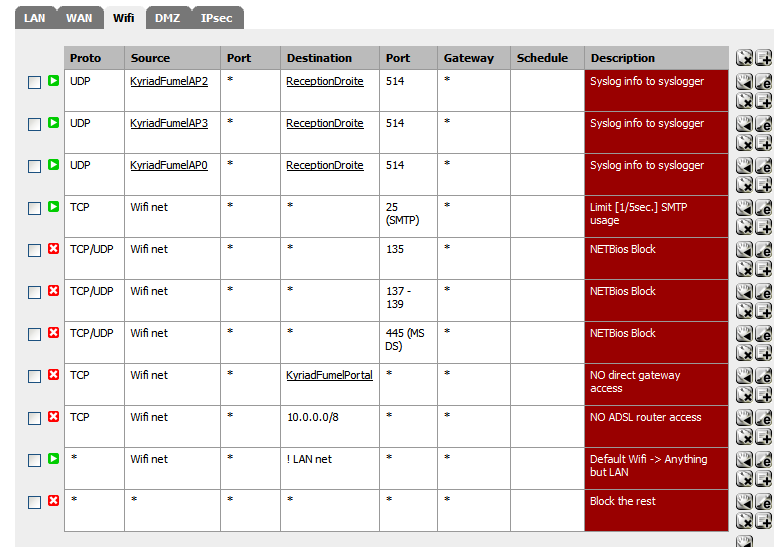
Rule 1/2/3: These are used for each AP so they can syslog to one of my PC's on the LAN
(note: and addionnel "Captive portal::allowed IP addresses will also be needed")Rule 4: Throttle SMTP 25 ;)
Rule 5/6/7: Block some very noisy "Dos/Win" ports
Rule 8: Block all direct access to the gateway (on 192.168.2.1 = pfSense)
Rule 9 : Block access to my WAN device (it's local IP)
Rule 10: Block all that isn't for destination not WAN
Rule 11: Block everything.
-
Done Ty.
Now to get a new better AP…
-
You can work around this.
Firewall –> nat --> outbound.
Enable manual rule generation.
Create a new rule for the opt interface with source LAN-subnet and destination IP_of_AP/32.
Like this you NAT all traffic to the AP, and it appears for it as if the pfsense is accessing it (to which it knows the way back since it's in the same broadcast-domain. -
@roi:
As much as I hate to accept it, since as for my understanding it was not supposed to be like that, it seem that you are correct. I can access other computers on that subnet, but from some reason still cant access the AP. Soooo it will have to be replaced.
It's a basic rule of networking, as others have described.
You can work around it by NATing all traffic from LAN to the AP using advanced outbound NAT on the AP's interface. It still may have other complications as previously mentioned, as the AP may need NTP to sync its time or other things, and it can't get to the Internet without a default gateway either.
-
What I was expecting to happen is since PFsense is a router that it will NAT the traffic as you just wrote.
then traffic from one subnet will be seen by the AP as virtually on the same subnet.
I was not aware that the other option exist.Since then I got a Level one WAB-3001 professional outdoors AP, that have the option for default GW input.
200$ for the parts and several hours of installing work later and the WiFi to the people at my B&B was never so good.No for solving other problems…..
-
@roi:
What I was expecting to happen is since PFsense is a router that it will NAT the traffic as you just wrote.
Only that which is destined to the Internet by default. You rarely want to NAT between your internal networks, it's unnecessary overhead, and causes problems with some services (Windows file sharing primarily).
Sounds like you have a much better setup now, NATing would be a hack in that scenario.
-
If I wanted Windows file sharing to work between these computers I'd put them on the same subnet…
The Idea is to separate the lab where I fix client's computers that many time have viruses on them and the B&B where I have kid's with daddy's laptop looking around and the home network.If I had another interface I'd even separate the B&B from the lab and put a capping on it so the kid's will not kill my connection downloading video's w/Utorrent. It seem that my next toy will be a managed switch with option for speed limiting for each port ;)
-
@roi:
If I had another interface I'd even separate the B&B from the lab and put a capping on it so the kid's will not kill my connection downloading video's w/Utorrent. It seem that my next toy will be a managed switch with option for speed limiting for each port ;)
Limiters on 2.0 make that really easy, and speed limits on managed switches tend to not be as configurable (depending on the switch), so you may want to check into that in the future.
-
the connections that I need are -
Wan - L2tp to ISP 1
Lan - home, need to be private
OPT1 - Lab and at the moment B&B Wifi
OPT2 - going to be connected to a routble /29 range with testing servers.
OPT3 - going to be connected to ISP 2, probably PPPoE and load balanced with the wan.I'd like to separate the B&B Wifi from the lab and put cap's and limit's on it but I run out of interfaces.