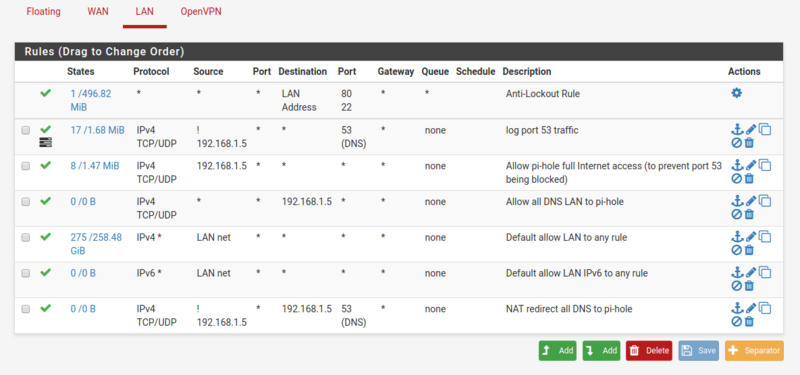
Block all port 53 DNS traffic that isn't bound for LAN pi-hole DNS Server
-
hi -
I have a pretty vanilla residential install of pfsense (2.4.2-RELEASE-p1). (internet <-> Cable modem <-> Pfsense <-> single wired/wireless LAN).
I have been playing with a local pi-hole DNS server, and it works well. I have my pfsense hand out DHCP addresses that include the DNS server @ 192.168.1.5. For clients that are set to use the automatic DNS server, this works great.
However, I have realized that some clients (chromebooks, i think) use the google DNS servers by default. I'd like to have ALL DNS queries on my LAN handled by the pi-hole. This would also provide some protection against one of my kids trying to set their own DNS server manually someday.
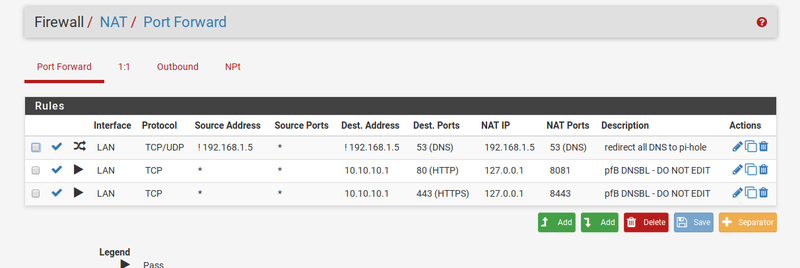
I set up a Firewall NAT redirect to bounce DNS traffic that ISN'T bound to 192.168.1.5 to be forwarded to that address. I can see that the forwarded queries are getting to the pi-hole, but the client isn't able to resolve the URL. (even though I can see that the pi-hole sends out the query to the internet DNS server, and a seemingly-valid response returns, clients aren't able to make a connection to the IP address.)
I'm sure that the rules aren't as clean as they could be, but here is what I have. Any obvious issues here that would keep the DNS queries which are destined for, say, 8.8.8.8, and are being forwarded to pi-hole, but eventually fail?
-
So I assumed that this was a firewall issue, and something was getting blocked accidentally along the way, but as I played with it a little more, I see that maybe the clients don't like to get a response from an unexpected DNS server.
Correctly set DNS server:
matt@matt-ThinkPad-T61 ~ $ nslookup www.ebay.com
Server: 192.168.1.5
Address: 192.168.1.5#53Non-authoritative answer:
www.ebay.com canonical name = slot9428.ebay.com.edgekey.net.
slot9428.ebay.com.edgekey.net canonical name = e9428.b.akamaiedge.net.
Name: e9428.b.akamaiedge.net
Address: 23.46.56.131DNS Server set to 8.8.8.8
matt@matt-ThinkPad-T61 ~ $ nslookup
www.ebay.com
;; reply from unexpected source: 192.168.1.5#53, expected 8.8.8.8#53
;; reply from unexpected source: 192.168.1.5#53, expected 8.8.8.8#53
;; reply from unexpected source: 192.168.1.5#53, expected 8.8.8.8#53
^C
matt@matt-ThinkPad-T61 ~ $Anyone have any thoughts?
thanks
Matt -
"Anyone have any thoughts?"
Well looking at your rules - first thing that comes to mind is they are mostly pointless
Clearly you do not understand how the rules are evaluated - don't feel bad it seems to be a common theme with users and firewalls.. Rules are evaluated top down, first rule to trigger wins - no other rules are evaluated.
Your allow all dns lan to pihole would never trigger. Devices on the LAN network would never talk to pfsense to talk to devices on the lan network.. They only talk to pfsense to talk to stuff NOT on the lan network.. This also seems to be a common misunderstanding.
Your rule below the any any rule is pointless.. So your nat redirect - again never going to be evaluated..
-
I would second your rule issues…super easy to bipass any of your DNS restrictions you are trying to do.
Dig into this thread some it might help you out...
https://forum.pfsense.org/index.php?topic=132542.msg759743#msg759743
(Still can't thank you enough Johnpoz for the help you gave me!!)
-
Guess were were lucky to be able to see his images - now getting a update your account to enable 3rd party hosting on his images ;)
How hard is it to just post your image to the thread? ;) That seems more difficult then understanding the firewall rule evaluation order ;) heheheeh
Your more than welcome to any help I might have given….