VPN rules do nothing
-
I have a strange issue I can't figure out.
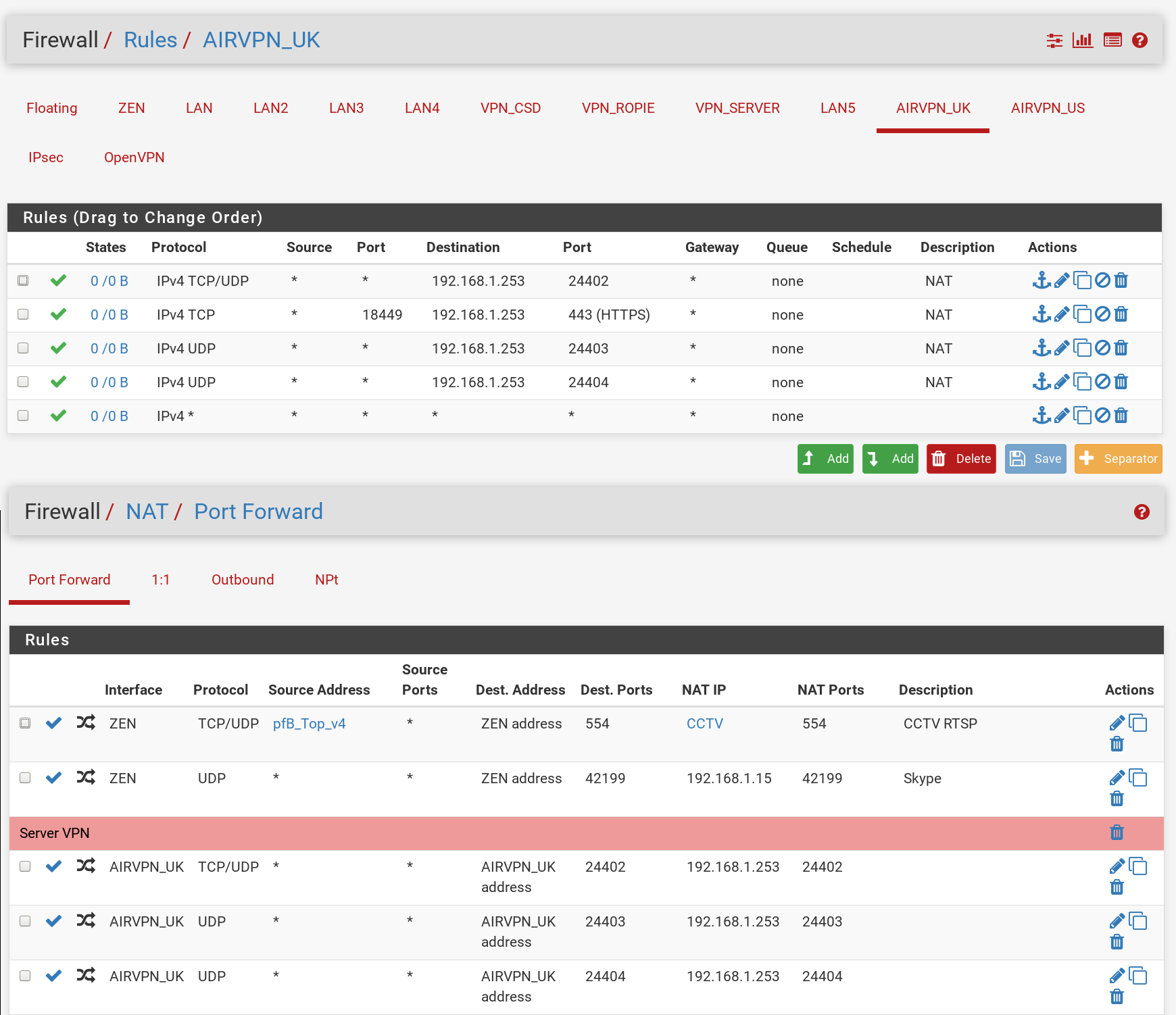
I have one specific host on the network routed via an OpenVPN client with a LAN rule and that same host has some incoming port forwards from the WAN (ZEN) which also work fine. The trouble is, port forwards for the VPN are not working. Incoming connections on the VPN public IP just timeout.
I have had the VPN provider (AirVPN) check things their side and also done some tests on a VPN endpoint I have control over and indeed it seems the port forwards simply do not work. I'm seeing evaluations on the VPN rules but no state creations or traffic, nothing in the firewall logs either.
I double-checked my floating rules only apply to LAN and WAN, I even had the entire LAN routing over the OpenVPN connection for a while to no avail.
Is there anything else that might be blocking this? It seems very odd that WAN port forwards work while VPN ones do not.
My configuration seems to match several guides I have seen for VPNs and even AirVPN specifically on pfSense.
-
If you are port forwarding into an OpenVPN connection from arbitrary addresses:
- There must be an assigned interface on the OpenVPN client or server receiving the connections
- The traffic must be passed on the OpenVPN assigned interface
- The traffic MUST NOT also match any rules on the OpenVPN group tab.
-
-
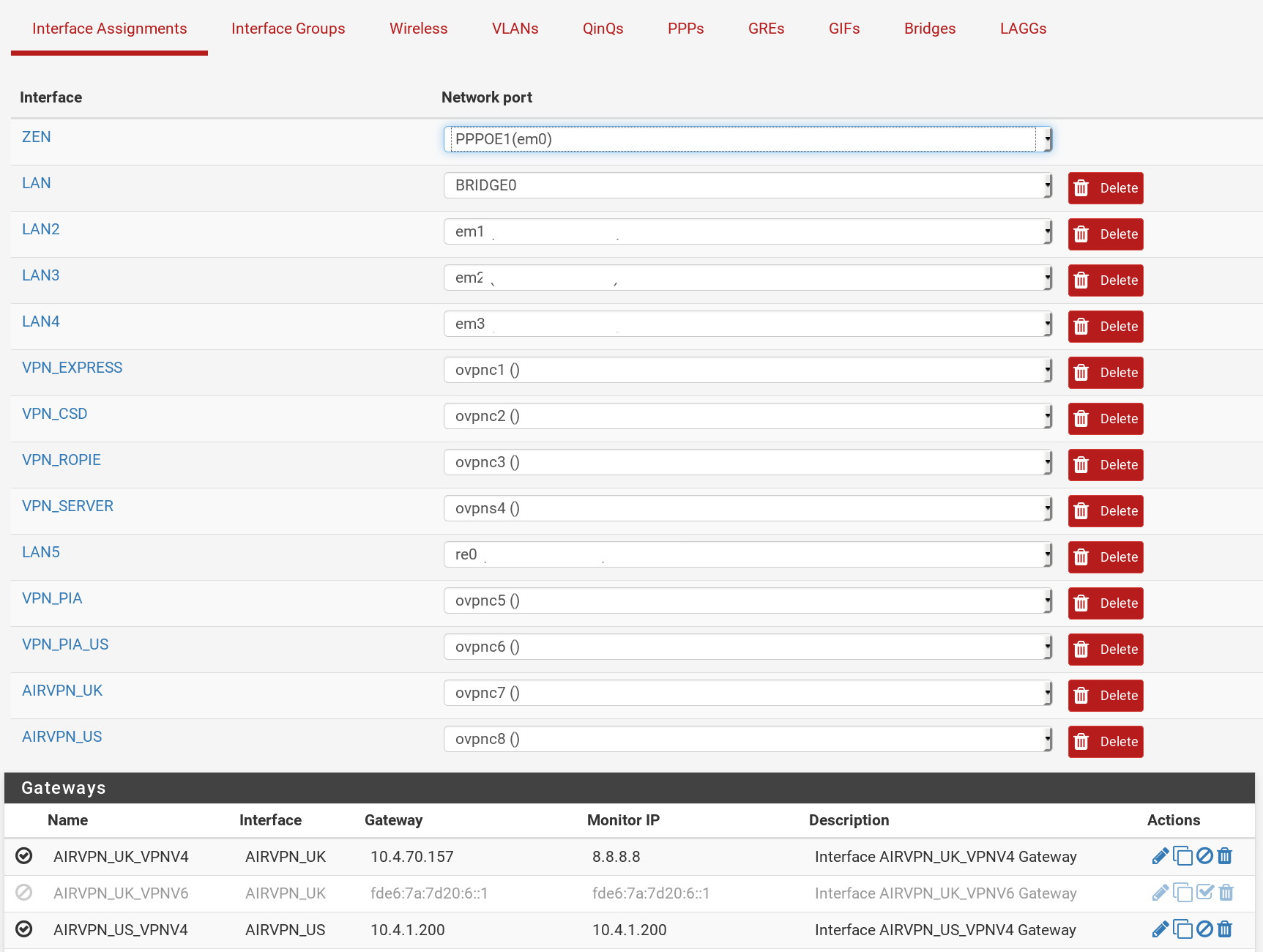
Doesn't the above show the interface assigned or am I missing something?
-
Am I correct in this is the right way to be passing the traffic to the OpenVPN interface?
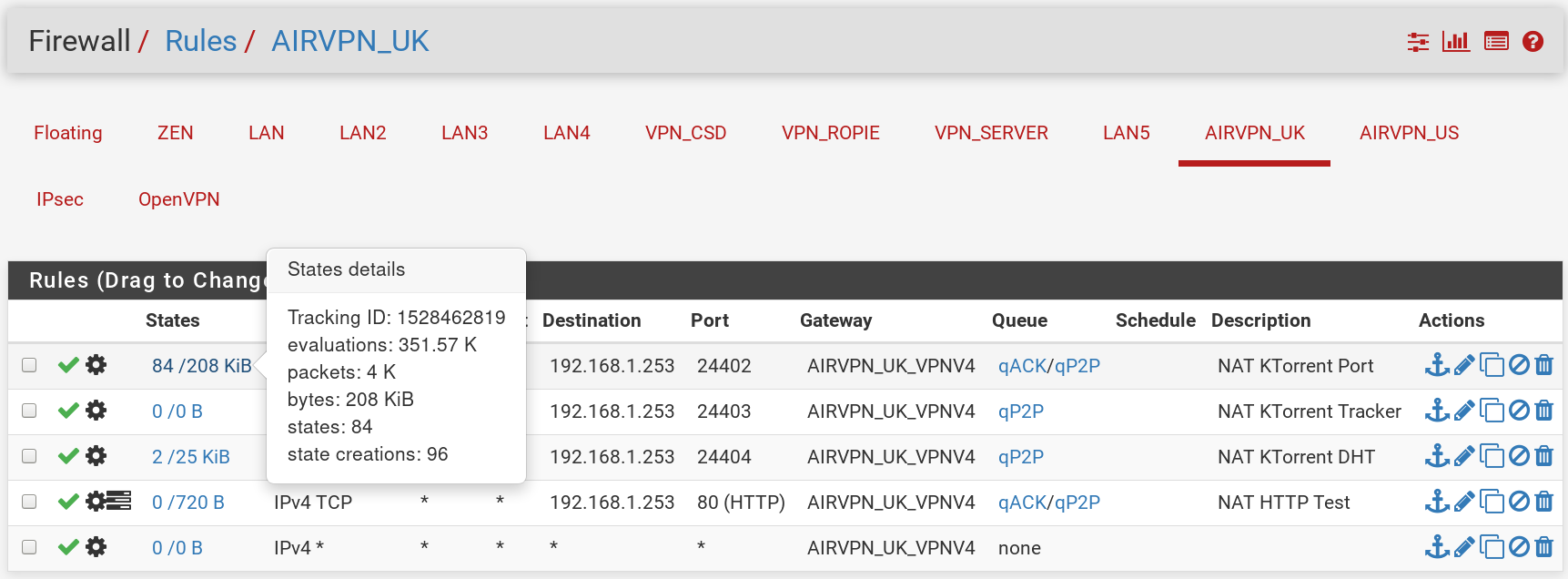
- I had pass all on the OpenVPN tab. I removed it and I'm seeing a little traffic and state matches but nothing making it to the host the ports are pointing to as far as I can tell. AirVPN test still reports timeout.
-
-
-
Yes. I still listed all of the required elements.
-
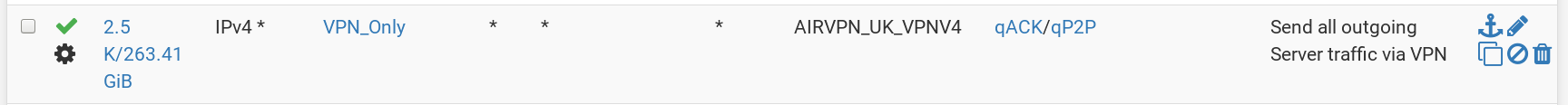
That has nothing to do with connections coming in from the outside. Those policy-route connections originating from the inside out the VPN.
-
How about you post the "state matches" you are seeing? Maybe they are not what you think they are.
-
-
@derelict I must be misunderstand something as surely that interface is the VPN endpoint, nothing can be coming from outside that?
AirVPN reported the iptables rules on their end and clearly that side must be working as surely no traffic would be hitting the port forwarding rules otherwise?
The HTTP test is curious as no state matching is occurring there and I have tested it from a web browser and it times out.
-
Why are you setting a gateway on those rules to be the gateway of the interface the traffic is coming in on? You are forcing that traffic back out the way it came. Remove the gateways from those rules. Nobody nowhere said that is what you needed to do.
-
@derelict Oops, I did that while desperately throwing things at the wall trying to see what would stick and forgot to revert it back. ;)
Switched it back to how it was in the first post and that seems to have done the trick. Thanks for your help.