OpenVPN with router behind pfsense.
-
Hi.
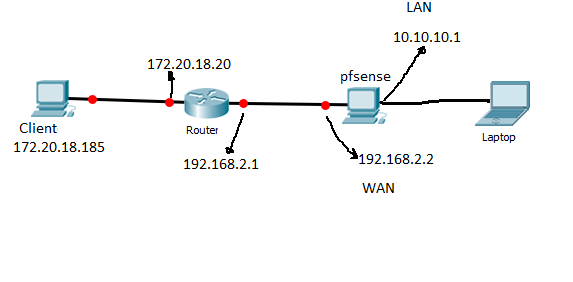
I have a router behind my pfsense and a im trying to administrate my pfsense using VPN. i am assuming that 172.20.18.0/24 is my internet.
ROUTER:
fastethernet_0 i gave 172.20.18.20
fastethernet_1 i gave 192.168.2.1
ps: there is no issue with routing table in my router.
PFSENSE:
wan i gave 192.168.2.2
lan i gave 10.10.10.1openVPN configuration seems to be good.
I configured my clients to connect via 172.20.18.20
So, i nat port forwarding my router like this:ip nat inside source static udp 10.10.10.1 1194 interface FastEthernet0/0 1194
The goal is reaching to my lan. My client has 172.20.18.185.
why can not i connect ? this is whati get:Tue Jul 17 16:25:06 2018 OpenVPN 2.3.18 i686-w64-mingw32 [SSL (OpenSSL)] [LZO] [PKCS11] [IPv6] built on Sep 26 2017
Tue Jul 17 16:25:06 2018 Windows version 6.2 (Windows 8 or greater) 32bit
Tue Jul 17 16:25:06 2018 library versions: OpenSSL 1.0.2l 25 May 2017, LZO 2.10
Tue Jul 17 16:25:51 2018 Control Channel Authentication: using 'pfSense-udp-1194-kalaneVPN-tls.key' as a OpenVPN static key file
Tue Jul 17 16:25:51 2018 UDPv4 link local (bound): [undef]
Tue Jul 17 16:25:51 2018 UDPv4 link remote: [AF_INET]172.20.18.20:1194
Tue Jul 17 16:26:51 2018 TLS Error: TLS key negotiation failed to occur within 60 seconds (check your network connectivity)
Tue Jul 17 16:26:51 2018 TLS Error: TLS handshake failed
Tue Jul 17 16:26:51 2018 SIGUSR1[soft,tls-error] received, process restarting
Tue Jul 17 16:26:53 2018 UDPv4 link local (bound): [undef]
Tue Jul 17 16:26:53 2018 UDPv4 link remote: [AF_INET]172.20.18.20:1194
Tue Jul 17 16:27:53 2018 TLS Error: TLS key negotiation failed to occur within 60 seconds (check your network connectivity)
Tue Jul 17 16:27:53 2018 TLS Error: TLS handshake failed -
Draw this up... If your pfsense wan is 192.168.2.2 why would you be trying to connect to 172.20.18.20?
172.20.18.0/24 is my internet
That is not internet - that is a rfc1918 address. There is no possible way to connect to that IP from the internet..
So unless your on this 172.20 network or on some local network that can get to that 172.20 network your never going to connect.
If pfsense wan is 192.168.x then its behind a NAT to get to pfsense from the internet you would have to forward to pfsense wan from the NAT device in front of pfsense and then access the PUBLIC IP from the internet.
10.x.x.x
172.16-31.x.x
192.168.x.xAre RFC1918 - they can not route on the internet and are only private IP space.
-
i am assuming that 172.20.18.0/24 is a public network (internet). So, in my case 172.20.18.20 is my public address.
-
@ruimiguel
172.20.18.185 is my client. So i have exported VPNclient and installed it on my client. it is set to try connection via 172.20.18.20. -
If you google "whats my IP address" I bet it doesn't come back with any of the following:-
10.x.x.x
172.16-31.x.x
192.168.x.xWhat you think is your Internet router isn't.
-
@nogbadthebad
ok. I understand. I am not doing real test. there is no real internet. the client 172.20.18.185 and 172.20.18.20 are in the same net....so it should work, because i am doing nat port forwarding in 172.20.18.20 -
Does it work if you connect your client to 192.168.2.x ?
You might find that the double NAT is causing issues.
-
If you want to call 172.20 the internet that is fine... But you will have to forward on that router in front of pfsense. If its doing nat - which I would be large sums of money that it is.
-
@nogbadthebad
Ok. I decided to put a real public ip. Now in this configuration, what should i do to make it work. I can not eliminate the router bacause it is part of the work they want me to do. So have to make it work as it is.
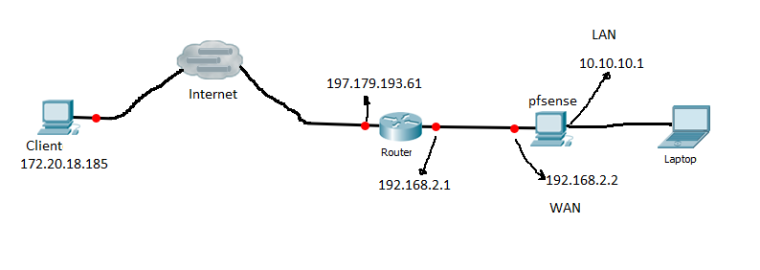
openVPN configuration is set and seems to be good.
I configured my clients to connect via 197.179.193.61
So, i nat port forwarding my router like this:ip nat inside source static udp 10.10.10.1 1194 interface 197.179.193.61 1194
The goal is reaching to my LAN. My client has 172.20.18.185.
why can not i connect ? This is what i am getting:Tue Jul 17 16:25:06 2018 OpenVPN 2.3.18 i686-w64-mingw32 [SSL (OpenSSL)] [LZO] [PKCS11] [IPv6] built on Sep 26 2017
Tue Jul 17 16:25:06 2018 Windows version 6.2 (Windows 8 or greater) 32bit
Tue Jul 17 16:25:06 2018 library versions: OpenSSL 1.0.2l 25 May 2017, LZO 2.10
Tue Jul 17 16:25:51 2018 Control Channel Authentication: using 'pfSense-udp-1194-kalaneVPN-tls.key' as a OpenVPN static key file
Tue Jul 17 16:25:51 2018 UDPv4 link local (bound): [undef]
Tue Jul 17 16:25:51 2018 UDPv4 link remote: [AF_INET]197.179.193.61:1194
Tue Jul 17 16:26:51 2018 TLS Error: TLS key negotiation failed to occur within 60 seconds (check your network connectivity)
Tue Jul 17 16:26:51 2018 TLS Error: TLS handshake failed
Tue Jul 17 16:26:51 2018 SIGUSR1[soft,tls-error] received, process restarting
Tue Jul 17 16:26:53 2018 UDPv4 link local (bound): [undef]
Tue Jul 17 16:26:53 2018 UDPv4 link remote: [AF_INET]197.179.193.61:1194
Tue Jul 17 16:27:53 2018 TLS Error: TLS key negotiation failed to occur within 60 seconds (check your network connectivity) -
So you just picked some random public IP.??.. OMG!!!
inetnum: 197.176.0.0 - 197.179.255.255
netname: SFC-GPRS-EDGE-3G-SERVICE-POOL-SEG1
descr: SAFARICOM LTD KENYAYour not getting it!!!
What part did you not get about port forwarding at the router?? Why would you be trying to portforward to the lan IP?? When you have pfsense there natting as well?
ip nat inside source static udp 10.10.10.1 1194 interface 197.179.193.61 1194
That makes ZERO sense...
How is that your rfc1918 client is going to talk to that IP? What is routing between them? Did you change the clients IP to be on that 197.x network?
Your packet hitting the WAN IP of your router... Where does it have to go to get to pfsense.. The 10 network which is pfsense lan, or pfsense WAN IP... Think about it for a few seconds ;)
Maybe they should get someone with better understanding of the basics to do whatever it is your trying to do.
-
@johnpoz
Mister.
U r just complicating the thing. I choose a random ip because u r just soo obcessed with public ip. Maybe if u were just a little humble u would really understand that i am using abstration. There is no real public ip. Anyway, thenkx for your golden time! -
@johnpoz
The is no problem in my teste. The only problem was in router forwarding configuration. It should be:
ip nat inside source static udp 192.168.2.2 1194 interface 197.179.193.61 1194
This way it is up and running. client (172.20.18.185); immaginary public ip address 172.20.18.20.
I have some limitations that oblige me do things like i did.
So now if i manage to change 172.20.18.20 for a real public ip i would be able to connect to my pfsense from anywhere. i suppuse.
Correct me if i am wrong, please -
I understand your testing of rfc1918 as "internet" I even stated such..
I am not complicating anything... You put up a drawing with
client rfc1918 --- internet --- made up public IP..
How are they suppose to talk to each other if on the same L2?
Yes if your test shows you can connected through your router to pfsense, then yes if you put actual public IP on it - you should be able to get to it from the internet.