Routing OpenVPN not working
-
Hi!
I have a tunnel peer-to-peer (shared key) by OpenVPN on PFSense 2.3.5 as server and 2.1.5 as client.
Tunnel is working, ping is both from the client side to the server network and back, but there is only it from the gateways. If I start ping from the client's network to the server's network, there is no connection.
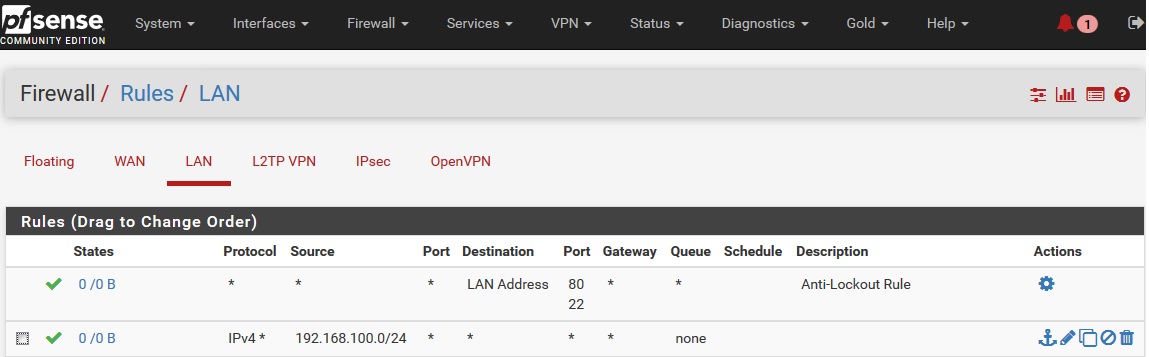
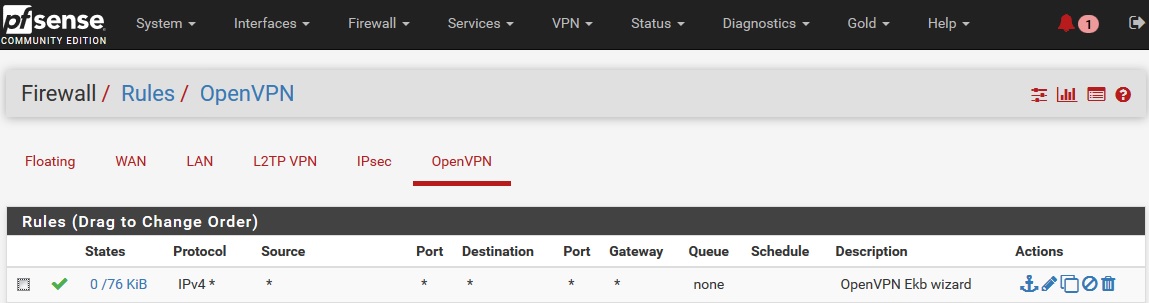
I create rule in server side firewall - rules - OpenVPN
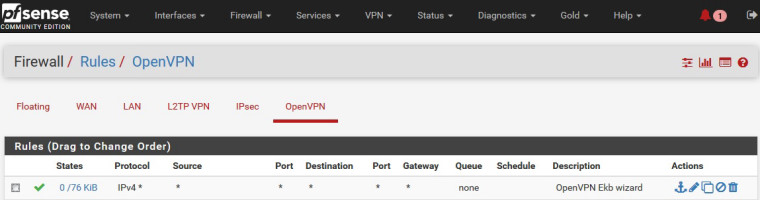
and same rule at client.
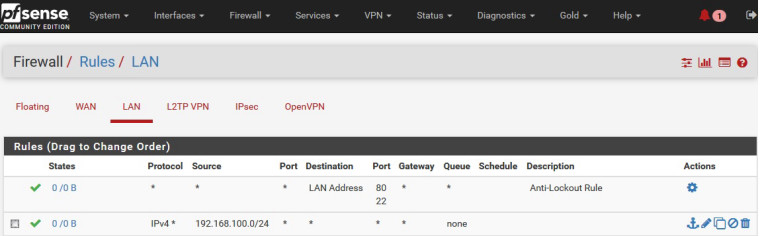
In LAN there is rule
Port 1194 in WAN interface is opened.
maybe I'm missing something? I ask for helpSettings on server side:
Server mode - Peer to peer (Shared key)
Protocol - UDP
Device mode - Tun
Local net - 192.168.72.0/24
Remote net - 192.168.166.0/24
Tunnel net - 192.168.100.0/24Settings on client side:
Server mode - Peer to peer (Shared key)
Protocol - UDP
Device mode - Tun
Local net - 192.168.166.0/24
Remote net - 192.168.72.0/24
tunnel net - 192.168.100.0/24 -
Don't use the tunnel net in any Firewall rule.
For testing:
Interface LAN both sides Source Local net to Destination any.
Interface OpenVPN both sides any to any (like you show in the first screen, put in on both sides).-Rico
-
@desroze said in Routing OpenVPN not working:
PFSense 2.3.5 as server and 2.1.5 as client
A good starting point would be : do not mix recent and ancient software.
2.1.5 is way to old. -
@rico said in Routing OpenVPN not working:
Don't use the tunnel net in any Firewall rule.
For testing:
Interface LAN both sides Source Local net to Destination any.no result of this rule, I tested it before
Interface OpenVPN both sides any to any (like you show in the first screen, put in on both sides).
-Rico
in both sides work such rule
@gertjan said in Routing OpenVPN not working:
@desroze said in Routing OpenVPN not working:
PFSense 2.3.5 as server and 2.1.5 as client
A good starting point would be : do not mix recent and ancient software.
2.1.5 is way to old.I know it, but it's time solution, because 2.1.5 was installed very very before, now I will upgrade it, but it will not be immediately, this PFSense not in my physical nearaing
-
When you Ping from Client side 192.168.166.0/24 to server side 192.168.72.0/24 do you see anything in the Firewall Logs (pfSense side 192.168.72.0/24) ?
Are you maybe on manual NAT?
You use pfSense on both sides as your local Gateway for the Clients?-Rico
-
@rico said in Routing OpenVPN not working:
When you Ping from Client side 192.168.166.0/24 to server side 192.168.72.0/24 do you see anything in the Firewall Logs (pfSense side 192.168.72.0/24) ?
nope, in firewall log I have nothing events, wich contains my local\WAN\tunnel IP-addresses, and I understanding that problem in this, not not understand where exactly
Are you maybe on manual NAT?
You use pfSense on both sides as your local Gateway for the Clients?-Rico
I use PFSense as GW at local network, with the exception of DNS, this function performs AD.
Config from local PC at server sideDEVICE=eth0 BOOTPROTO=none ONBOOT=yes TYPE=Ethernet USERCTL=no IPV6INIT=no PEERDNS=yes NETMASK=255.255.255.0 IPADDR=192.168.72.5 GATEWAY=192.168.72.1Client side
DEVICE=eth0 TYPE=Ethernet ONBOOT=yes NM_CONTROLLED=yes BOOTPROTO=none IPADDR=192.168.166.3 PREFIX=24 GATEWAY=192.168.166.1 DEFROUTE=yes IPV4_FAILURE_FATAL=yes IPV6INIT=no NAME="System eth0" NETMASK=255.255.255.0 -
No more assumptions?
How I read in another topic "It is a canonical task from ANY manuals", but why it not working? Maybe anyone know actuall manual for this task, with detail instructions, or another forum for my question? -
Not sure what you want when you're using an ancient version like 2.1.5. Not a lot of people want to spend time chasing long-fixed bugs and problems. You should consider upgrading and seeing if the issue is fixed.
-
@derelict said in Routing OpenVPN not working:
Not sure what you want when you're using an ancient version like 2.1.5. Not a lot of people want to spend time chasing long-fixed bugs and problems. You should consider upgrading and seeing if the issue is fixed.
I wrote earlyer, upgrade is in my plans, but NOW I can't do it so fast, so I need solve this question.
I understand your answer, thanks