Pfsense block ICMP echo reply from WAN to OPT1
-
@bhjitsense said in Pfsense block ICMP echo reply from WAN to OPT1:
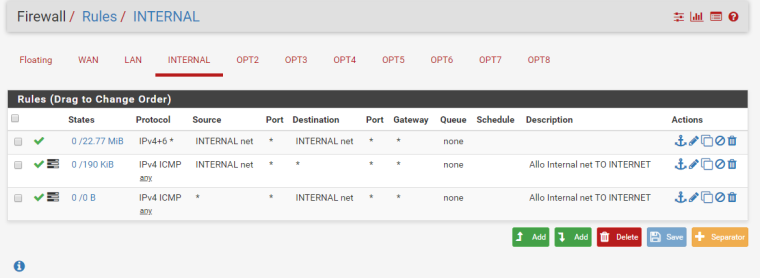
Interface rules
The interface is INTERNAL (OPT1)
FLOATING RULES/
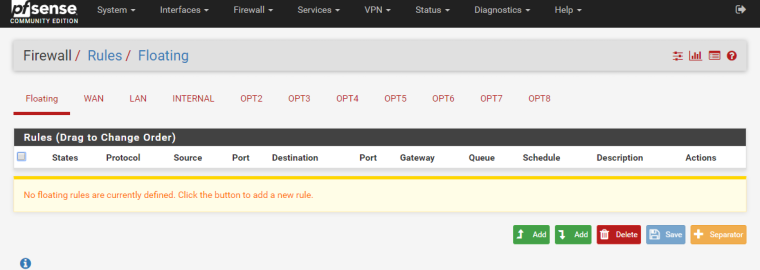
-
@tmedtcom said in Pfsense block ICMP echo reply from WAN to OPT1:
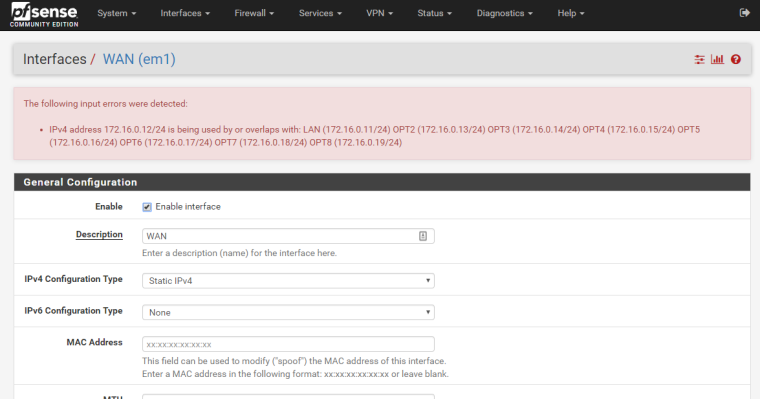
LAN interface 172.16.0.11
WAN interface 172.16.0.12What? Sorry it doesn't work that way you can not have the same network on wan and lan interface..
And those rules on your internal are just BORKED..
When would internal need to talk to pfsense to talk to other internal?
-
@johnpoz
LAN interface: this interface it is configured to just connecting to pfsense (ssh/web interface) just for admin.
WAN interface to allow users to connect to many VMs via NAT.
INTERNAL OPT1 this network is reserved to VMs servers on my VMware ESXI HOST. -
And AGAIN you can not have the same network on 2 different interfaces... This basic routing 101... I don't even think pfsense will let you do that..
-
@tmedtcom
You don't nee the third rule if you have that first rule. Also, change the first rule to be INTERNAL net > INTERNAL address. Or ANY > INTERNAL address.Also, post your WAN rules.
-
WAN interface to allow users to connect to many VMs via NAT.
Huh? Why would you be natting between local rfc1918 networks or vm networks?
I have run pfsense on esxi for many years through multiple versions of esxi going back to 4.. Before that even ran it on the old school vmware server 1 and 2..
Please draw up how you have this stuff connected in esxi with your vswitches and connected to pfsense and how your vswitches are connected to your physical network.. Port groups, are you doing any vlan tagging anywhre or different vswitches - are they standard or distributed switches, etc. etc.
-
My bet is on NAT being borked. You are allowing the ICMP traffic out of INTERNAL, but it doesn't know its way back for the reply.
-
@bhjitsense said in Pfsense block ICMP echo reply from WAN to OPT1:
@tmedtcom
You don't nee the third rule if you have that first rule. Also, change the first rule to be INTERNAL net > INTERNAL address. Or ANY > INTERNAL address.Also, post your WAN rules.
WAN Rules:
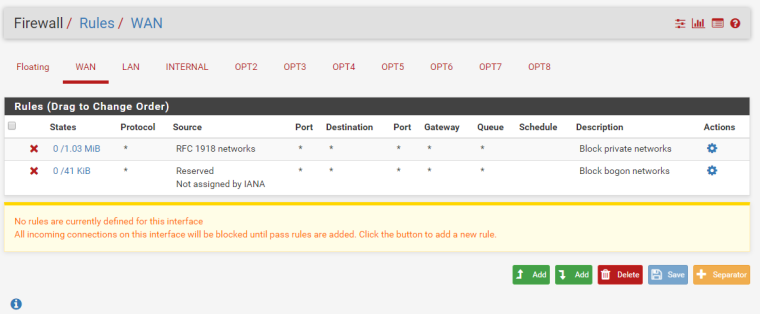
-
@johnpoz said in Pfsense block ICMP echo reply from WAN to OPT1:
Huh? Why would you be natting between local rfc1918 networks or vm networks?
In the internal Network I have multiple web servers and in the WAN network I have a users on laptop connected to Cisco for Internet and I would like to allow users to access to my Web servers via NAT on WAN: 172.16.0.12:8080
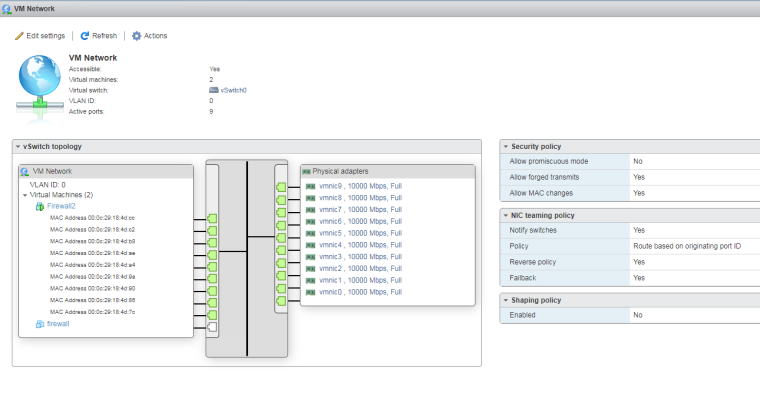
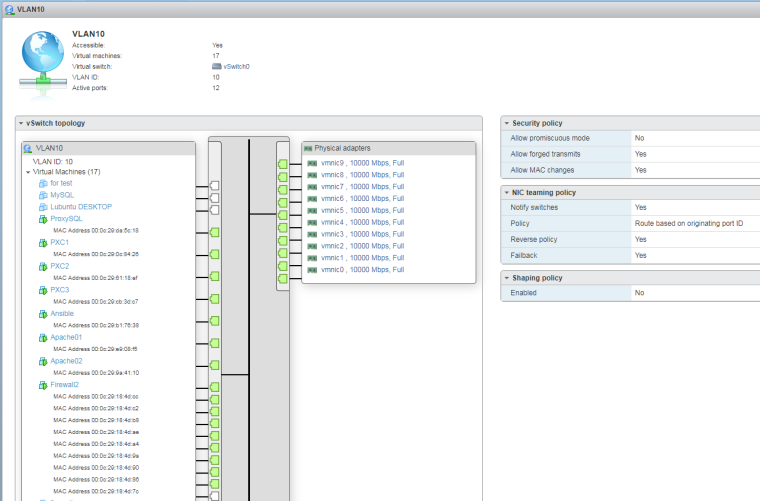
So pfsense it is the intermidiate router between 2 network 172.16.0.0/24 (WAN) and 192.168.10.0/24Also in ESXI 6.5 I have a standard virtual switch with 2 group port:
- VM network bridget to phisical card
- VLAN 10 => this is my Internal network
-
@bhjitsense said in Pfsense block ICMP echo reply from WAN to OPT1:
My bet is on NAT being borked. You are allowing the ICMP traffic out of INTERNAL, but it doesn't know its way back for the reply.
Yes I also see that there is no return in the logs:
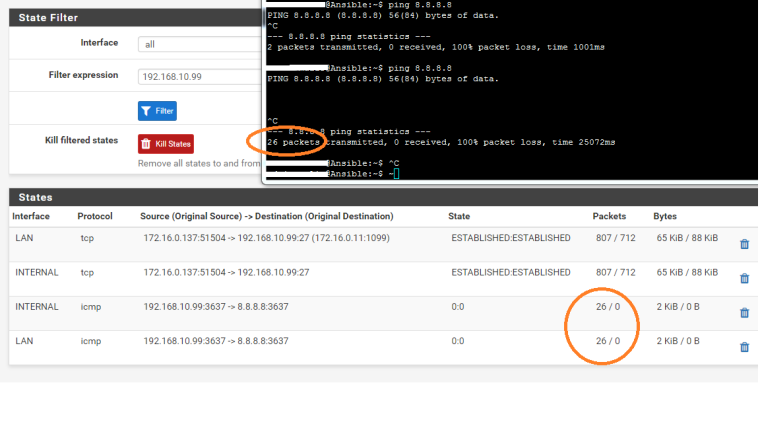
But why and how to solve it? -
well if you want to access from rfc1918 to networks behind pfsense via your going to have to remove that rfc1918 block for starters.
If you want to use pfsense as a downstream network from your cisco then there should be a transit network and nat should only happen then talking to the internet and your cisco should nat all your downstream networks, etc.
Or you should just double nat everything behind pfsense, etc.
Why are you using vlan 10? Are you setting the vlans up in pfsense - what does your vswitch/port group do with the vlan(s) what do you have set on this port group, etc. etc..
But you do NOT put the same network on multiple interfaces... And if your wanting to nat from rfc1918 to rfc1918 you going to have to remove that rfc1918 block.
-
-
I tried to disable the blocking of rfc1918 but here is the error message:
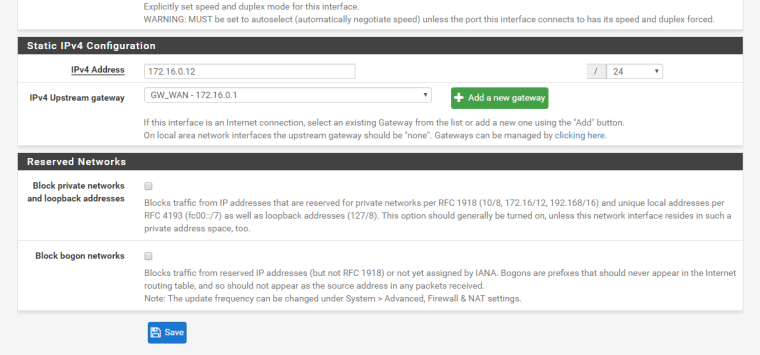
-
Dude why do you have so many physical interfaces?
And you firewall 2 with how many interfaces? All in the same network?
Then you have all of those same interfaces in firewall 2 also in vlan port group..
Yeah that screams a MESS!!
And yeah told you pfsense shouldn't even let you put overlapping networks on multiple interfaces!!
-
I guess you already have a working LAN adapter on pfsense and OPT1 is your additional lan network.
if that is the case then please create a new firewall rule to allow packets to pass(which you told you created already) and then in your newly created firewall rule , try changing/selecting the protocols which should be set as any by default).