Error: TLS Authentication Failed on OpenVpn, happens randomly
-
This is error is mostly just down to basic connection problems.
For testing I'd skip options like float and so on, try with some very basic setup.
Increase the verb level to get a more detailed Log.-Rico
-
I would get a permanent ping running from client to vpn host external ip and see if you had packet loss.
Failed tls negotiation doesn't have much to configure, once it works, always works. -
@rico please can you specify the options that I have to skip/remove?
The verbosity level changed to 5, so I will update you when I connect to the VPN -
@netblues Permanent ping is up and running. I will update you as soon as I have news.
-
For me a basic RA Server Config looks like this
dev ovpns1 verb 1 dev-type tun dev-node /dev/tun1 writepid /var/run/openvpn_server1.pid #user nobody #group nobody script-security 3 daemon keepalive 10 60 ping-timer-rem persist-tun persist-key proto udp4 cipher AES-256-GCM auth SHA256 up /usr/local/sbin/ovpn-linkup down /usr/local/sbin/ovpn-linkdown client-connect /usr/local/sbin/openvpn.attributes.sh client-disconnect /usr/local/sbin/openvpn.attributes.sh local 192.168.74.131 tls-server server 10.0.0.1 255.255.255.0 client-config-dir /var/etc/openvpn-csc/server1 username-as-common-name plugin /usr/local/lib/openvpn/plugins/openvpn-plugin-auth-script.so /usr/local/sbin/ovpn_auth_verify_async user TG9jYWwgRGF0YWJhc2U= false server1 1194 tls-verify "/usr/local/sbin/ovpn_auth_verify tls 'test' 1" lport 1194 management /var/etc/openvpn/server1.sock unix push "route 192.168.1.1 255.255.255.0" ca /var/etc/openvpn/server1.ca cert /var/etc/openvpn/server1.cert key /var/etc/openvpn/server1.key dh /etc/dh-parameters.2048 tls-auth /var/etc/openvpn/server1.tls-auth 0 ncp-disable compress topology subnet-Rico
-
This post is deleted! -
Guys I removed the flow option and I was disconnected again after 1 hour
Also I forgot to mention that I have implemented 802.1x security on my Juniper switches through the same NPS server. (windows 2012 R2) so that my colleagues can access network only after authentication.
So the difference on my NPS is that I have first my VPN policy then Wireless 802.1x and finally the wired 802.1x.
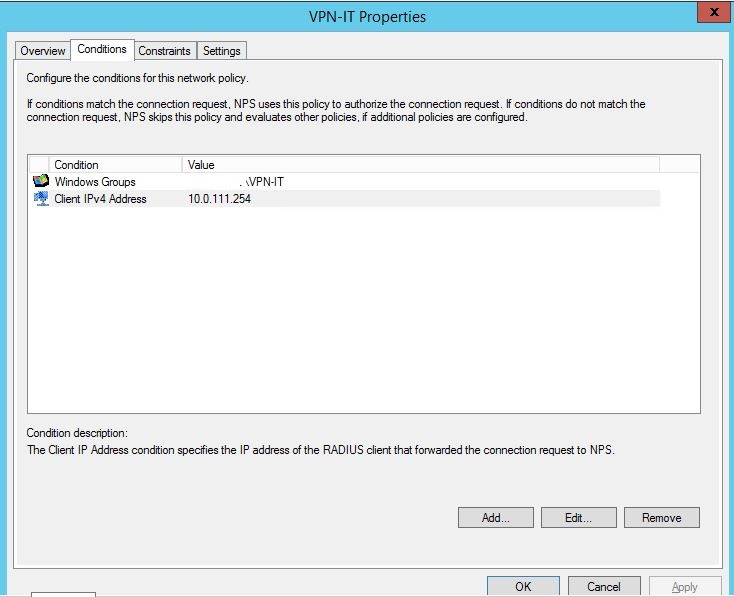
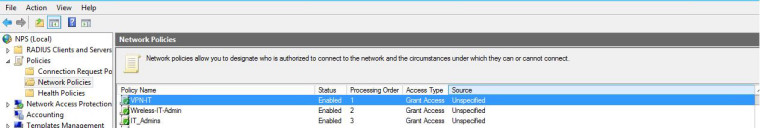
Is there any possibility that Radius/NPS looses connection (LAN) with openvpn server or the order of policies affect each other and automatically disconnects me?
The server config is just like @Rico but with the below differences on servertun-mtu 1500 fragment 1300 mssfix keepalive 30 120and on my client
tun-mtu 1500 fragment 1300 mssfix ping 10 ping-restart 30Server logs
Jan 3 20:04:40 demovpn openvpn[23620]: secret/x.x.x.x:1194 MULTI: Learn: 192.168.95.2 -> secret/x.x.x.x:1194 Jan 3 20:04:40 demovpn openvpn[23620]: secret/x.x.x.x:1194 MULTI: primary virtual IP for secret/x.x.x.x:1194: 192.168.95.2 Jan 3 20:04:40 demovpn openvpn[23620]: secret/x.x.x.x:1194 PUSH: Received control message: 'PUSH_REQUEST' Jan 3 21:03:04 demovpn openvpn[23620]: secret/x.x.x.x:1194 TLS: new session incoming connection from [AF_INET]x.x.x.x:1194 Jan 3 21:04:04 demovpn openvpn[23620]: secret/x.x.x.x:1194 TLS Error: TLS key negotiation failed to occur within 60 seconds (check your network connectivity) Jan 3 21:04:04 demovpn openvpn[23620]: secret/x.x.x.x:1194 TLS Error: TLS handshake failed Jan 3 21:04:39 demovpn openvpn[23620]: secret/x.x.x.x:1194 TLS: soft reset sec=0 bytes=66431304/-1 pkts=230648/0 Jan 3 21:05:39 demovpn openvpn[23620]: secret/x.x.x.x:1194 TLS Error: TLS key negotiation failed to occur within 60 seconds (check your network connectivity) Jan 3 21:05:39 demovpn openvpn[23620]: secret/x.x.x.x:1194 TLS Error: TLS handshake failed Jan 3 21:05:39 demovpn openvpn[23620]: secret/x.x.x.x:1194 TLS: move_session: dest=TM_LAME_DUCK src=TM_ACTIVE reinit_src=1 Jan 3 21:06:54 demovpn openvpn[23620]: secret/x.x.x.x:1194 TLS Error: TLS key negotiation failed to occur within 60 seconds (check your network connectivity) Jan 3 21:06:54 demovpn openvpn[23620]: secret/x.x.x.x:1194 TLS Error: TLS handshake failed Jan 3 21:06:55 demovpn openvpn[23620]: secret/x.x.x.x:1194 TLS: Initial packet from [AF_INET]x.x.x.x:1194, sid=51757c47 f972d37e Jan 3 21:07:08 demovpn openvpn[23620]: secret/x.x.x.x:1194 TLS: new session incoming connection from [AF_INET]x.x.x.x:1194 Jan 3 21:07:55 demovpn openvpn[23620]: secret/x.x.x.x:1194 TLS Error: TLS key negotiation failed to occur within 60 seconds (check your network connectivity) connectivity) Jan 3 21:09:08 demovpn openvpn[23620]: secret/x.x.x.x:1194 TLS Error: TLS handshake failed Jan 3 21:10:23 demovpn openvpn[23620]: secret/x.x.x.x:1194 TLS Error: TLS key negotiation failed to occur within 60 seconds (check your network connectivity) Jan 3 21:10:23 demovpn openvpn[23620]: secret/x.x.x.x:1194 TLS Error: TLS handshake failed Jan 3 21:11:23 demovpn openvpn[23620]: secret/x.x.x.x:1194 [UNDEF] Inactivity timeout (--ping-restart), restarting Jan 3 21:11:23 demovpn openvpn[23620]: secret/x.x.x.x:1194 SIGUSR1[soft,ping-restart] received, client-instance restarting -
Is there any possibility the issue of "Tls key negotiation failed" to start from the NPS server?
I mean, if for some reason NPS server looses connection with the Openvpn server, is it possible my connection to go down? or nps is just for the initial authentication? -
Update: From Public Static IP I have not been disconnected since yesterday morning.
So, all the disconnections are from Dynamic Public ip -
Guys any update???? Your help will be appreciated