Make Remote Location available over VPN
-
Hello
We are currently using pfsense OpenVPN for a Site to Site Tunnel between two Locations and a VPN Access of Users.
Site to Site Tunnel
Location1 ============== Location2Location1 is 192.168.3.0/24
Location2 is 192.168.4.0/24If im in the LAN on Location1 and Location2 i can reach both Subnets.
Users with VPN are connected to Location1 but cant reach the subnet in Location2.
Any Ideas which Configuration am i missing?I dont have much experience with OpenVPN yet so Detail Information would be apprecatiated.
-
Make sure your User's VPN have a route to the Location 2, add the route push to the server side config. Assuming your client configs don't have the config entry "route-nopull"
-
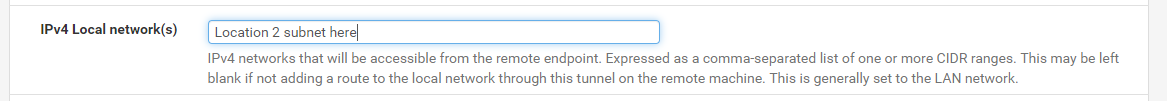
The above is where in your OpenVPN server settings for your remote VPN users where you need to add your Location 2 subnet.
Also make sure that if the subnet for the remote VPN users is different from Location 1 & 2 that a firewall rule permits that subnet to pass from location 1 to location 2 and back.
Also make sure that location 2 has the subnet route for the remote User VPN subnet added to its routing table. Location 2 needs to know how to send the packet back.
-
Thanks for your help.
So i Setup the following Config:
IpV4 Local Networks(your screenshot): 192.168.3.0/24,192.168.4.0/24
Advanced options:
push "route 192.168.3.0 255.255.255.0";
push "route 192.168.4.0 255.255.255.0";
push "dhcp-option DNS 192.168.3.2";And setup a Rule VPN Subnet to all but i somehow still cant reach the 4.0/24 subnet any ideas what im missing or see any mistakes?
-
What is your users vpn subnet? Is that route set up on Location 2 to point back to Location 1?
-
You do not need to mess about with the advanced options there.
IpV4 Local Networks(your screenshot): 192.168.3.0/24,192.168.4.0/24
will already do this:
push "route 192.168.3.0 255.255.255.0"; push "route 192.168.4.0 255.255.255.0";If anything someone will see error messages about not being able to add a route (because it has already been added) confusing them into clicking away to try to fix what isn't really broken in the first place.
push "dhcp-option DNS 192.168.3.2";will be added by setting the DNS Servers in the server configuration.
The main benefit to using the server and client configuration fields instead of Advanced Options is pfSense configuration upgrades can make changes as OpenVPN requires without trying to build an advanced options parser where it will be up to you to track and make changes. It also lets pfSense know what networks might need to be included for things like automatic outbound NAT.
@conor is on the right track. Location 2 also needs a route back to the tunnel network at Location 1.
-
Thanks for you help, so how do i configure the route from location 2 back to location 1 over vpn?
I checked and set the Pass rules so all traffic is on vpn is allowed and i also removed advanced options you mentioned.
Location1 is 192.168.3.0/24
Location2 is 192.168.4.0/24
VPN is 10.0.2.0/24 connected to location 1 -
@vertecpfsense
At location 2 device.
Goto: System > Routing > Static Routes
Click Add
Destination Network is the VPN off Location 1 network
Gateway is the interface for the OpenVPN site to site tunnel.
-
No.
Do NOT use static routes. Let OpenVPN add the routes to the routing table.
All you should have to do is add 10.0.2.0/24 to the Remote Networks in the OpenVPN configuration at Location 2.
-
I am attempting to have basically the same setup as the original poster. Also running into the same issue. I want my users VPN to direct ALL traffic through the vpn. As such you do not get the option to add the routes.
However even when I un-select the direct all traffic option and add the network subnets I still have the issue that OpenVPN users can not access the other end of the site-site vpn.
-
So post your configuration and explain exactly what you think should be working that isn't.
Be sure the other end of the site-to-site VPN has a route/traffic selector containing the remote access VPN tunnel network.
-
So the issue was I had on the far side Block BOGON networks turned on for the LAN interface.