Alias firewall block rule not blocked!
-
User error. Not understanding what you are looking at. State established before the rule was in place. Some other rule passing the traffic.
-
So the state stays established even after a reboot? I can't believe that...
-
No. The state was re-established after you rebooted because a firewall rule passed the traffic.
-
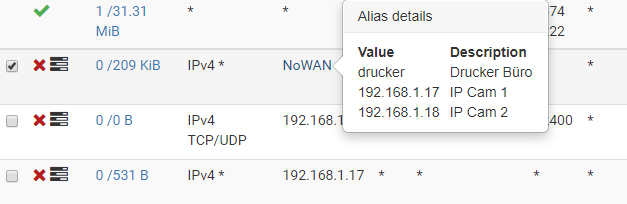
I restored the firewall rules to an earlier date and rebooted the machine. The alias is still the same and now the .17 again gets access. How to find out what rule is the problem?
-
pfctl -vvss | grep -A3 192.168.1.17Find the state you think should not be there out of that. Post it.
-
@Derelict said in Alias firewall block rule not blocked!:
pfctl -vvss | grep -A3 192.168.1.17
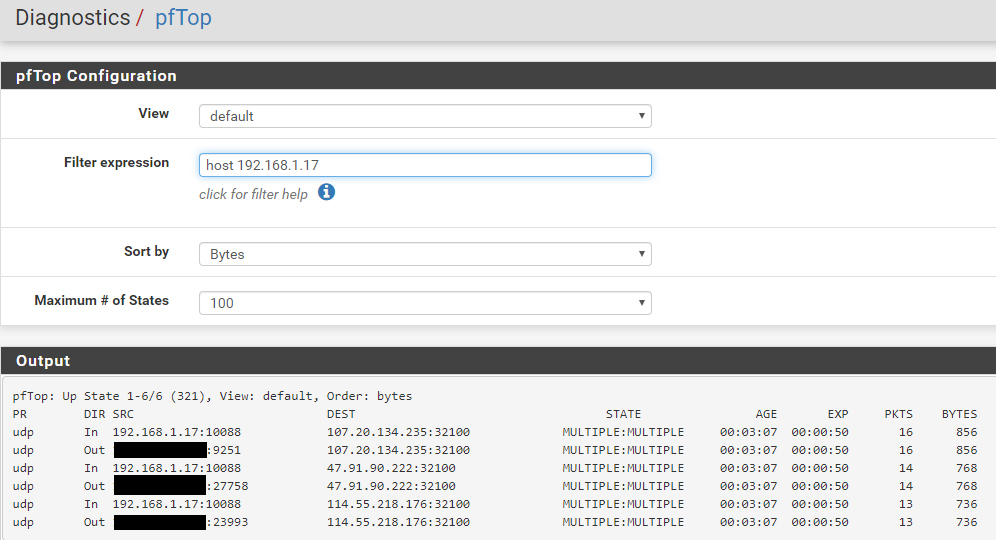
igb4 udp 192.168.1.1:53 <- 192.168.1.17:50872 NO_TRAFFIC:SINGLE age 00:00:55, expires in 00:00:05, 1:0 pkts, 56:0 bytes, rule 164 id: 010000005cd28985 creatorid: 3dddfb2a igb4 udp 192.168.1.255:32414 <- 192.168.1.10:55418 NO_TRAFFIC:SINGLE -- igb4 udp 192.168.1.1:53 <- 192.168.1.17:43906 NO_TRAFFIC:SINGLE age 00:00:55, expires in 00:00:05, 1:0 pkts, 59:0 bytes, rule 164 id: 010000005cd28988 creatorid: 3dddfb2a igb5 ipv6-icmp ff02::1[192] <- fe80::201:5cff:fe6b:e046[192] NO_TRAFFIC:NO_TRAFFIC -- igb4 udp 114.55.218.176:32100 <- 192.168.1.17:27288 NO_TRAFFIC:SINGLE age 00:00:48, expires in 00:00:12, 1:0 pkts, 32:0 bytes, rule 178 id: 010000005cd28a38 creatorid: 485eb46e igb4 udp 47.91.90.222:32100 <- 192.168.1.17:27288 NO_TRAFFIC:SINGLE age 00:00:48, expires in 00:00:12, 1:0 pkts, 32:0 bytes, rule 178 id: 010000005cd28a39 creatorid: 485eb46e igb4 udp 192.168.1.1:161 <- 192.168.1.10:56756 MULTIPLE:MULTIPLE -- igb4 udp 107.20.134.235:32100 <- 192.168.1.17:27288 NO_TRAFFIC:SINGLE age 00:00:48, expires in 00:00:12, 1:0 pkts, 32:0 bytes, rule 178 id: 000000005cd28acc creatorid: 485eb46e igb4.300 udp 8.8.8.8:53 <- 10.0.2.2:45009 NO_TRAFFIC:SINGLE -- igb4 udp 192.168.1.1:53 <- 192.168.1.17:51499 SINGLE:MULTIPLE age 00:00:33, expires in 00:00:00, 1:1 pkts, 56:72 bytes, rule 181 id: 000000005cd28c1a creatorid: b13ad8d2 igb5 udp 2a02:8071:800:0:527:2af9:a20f:552a[41679] -> 2001:8d8:fe:53:0:d9a0:52c2:100[53] MULTIPLE:SINGLE -- igb4 udp 107.20.134.235:32100 <- 192.168.1.17:25029 SINGLE:MULTIPLE age 00:00:33, expires in 00:00:00, 1:1 pkts, 32:48 bytes, rule 181 id: 000000005cd28c1b creatorid: b13ad8d2 igb5 udp xxx:64148 -> 217.160.83.194:53 MULTIPLE:SINGLE -- igb5 udp xxx:57526 (192.168.1.17:25029) -> 107.20.134.235:32100 MULTIPLE:SINGLE age 00:00:33, expires in 00:00:00, 1:1 pkts, 32:48 bytes, rule 141 id: 000000005cd28c1c creatorid: b13ad8d2 igb5 udp 2a02:8071:800:0:527:2af9:a20f:552a[45428] -> 2001:503:e239::3:2[53] MULTIPLE:SINGLE -- igb4 udp 192.168.1.1:53 <- 192.168.1.17:35486 SINGLE:MULTIPLE age 00:00:33, expires in 00:00:00, 1:1 pkts, 61:77 bytes, rule 181 id: 010000005cd28c21 creatorid: b13ad8d2 igb4 udp 107.20.134.235:32100 <- 192.168.1.18:10092 MULTIPLE:MULTIPLE -- igb4 udp 114.55.218.176:32100 <- 192.168.1.17:25029 NO_TRAFFIC:SINGLE age 00:00:33, expires in 00:00:27, 1:0 pkts, 32:0 bytes, rule 181 id: 010000005cd28c22 creatorid: b13ad8d2 igb5 udp xxx:41955 (192.168.1.18:10092) -> 107.20.134.235:32100 MULTIPLE:MULTIPLE -- igb5 udp xxx:10147 (192.168.1.17:25029) -> 114.55.218.176:32100 SINGLE:NO_TRAFFIC age 00:00:33, expires in 00:00:27, 1:0 pkts, 32:0 bytes, rule 141 id: 010000005cd28c23 creatorid: b13ad8d2 igb4 udp 2a02:8071:889:c500:4262:31ff:fe07:2bdc[53] <- 2a02:8071:889:c500:f525:878c:30fa:1bb5[50603] SINGLE:MULTIPLE -- igb4 udp 47.91.90.222:32100 <- 192.168.1.17:25029 SINGLE:MULTIPLE age 00:00:33, expires in 00:00:00, 1:1 pkts, 32:48 bytes, rule 181 id: 010000005cd28c24 creatorid: b13ad8d2 igb4 udp 192.168.1.1:53 <- 192.168.1.122:53655 SINGLE:MULTIPLE -- igb5 udp xxx:51011 (192.168.1.17:25029) -> 47.91.90.222:32100 MULTIPLE:SINGLE age 00:00:33, expires in 00:00:00, 1:1 pkts, 32:48 bytes, rule 141 id: 010000005cd28c25 creatorid: b13ad8d2 igb4 udp 114.55.218.176:32100 <- 192.168.1.18:21763 NO_TRAFFIC:SINGLE -
@mrsunfire OK, help me out. Which state should not be there?
-
All of the igb5 (WAN) connections from or to the 192.168.1.17.
-
@mrsunfire Pick one.
-
@mrsunfire said in Alias firewall block rule not blocked!:
igb5 udp xxx:10147 (192.168.1.17:25029) -> 114.55.218.176:32100 SINGLE:NO_TRAFFIC
age 00:00:33, expires in 00:00:27, 1:0 pkts, 32:0 bytes, rule 141
id: 010000005cd28c23 creatorid: b13ad8d2igb5 udp xxx:10147 (192.168.1.17:25029) -> 114.55.218.176:32100 SINGLE:NO_TRAFFIC
age 00:00:33, expires in 00:00:27, 1:0 pkts, 32:0 bytes, rule 141
id: 010000005cd28c23 creatorid: b13ad8d2 -
@mrsunfire said in Alias firewall block rule not blocked!:
pfctl -vvsr | grep -A3 '^@141('pfctl -vvsr | grep -A3 '^@181(' -
@Derelict said in Alias firewall block rule not blocked!:
pfctl -vvsr | grep -A3 '^@141('
@141(1000011161) pass out route-to (igb5 134.3.212.1) inet from xxx to ! 134.3.212.0/22 flags S/SA keep state allow-opts label "let out anything from firewall host itself" [ Evaluations: 1218 Packets: 12419 Bytes: 8152153 States: 167 ] [ Inserted: pid 49753 State Creations: 183 ] @142(1000011162) pass out route-to (igb5 fe80::201:5cff:fe6b:e046) inet6 from 2a02:8071:xxx to ! 2a02:8071:xxx::/56 flags S/SA keep state allow-opts label "let out anything from firewall host itself" -
[insert final jeopardy theme here.]
-
Right now the alias is working again and I can't get it to not work. I did nothing but now it is blocking. Sorry, I don't see the error there and will give it a try again in the future. Thanks for your help so far.
-
What was rule 181 in that rule set? Inquiring minds want to know!
-
This is a rule that passed the traffic from one client on LAN to my Cable Modem interface:
@181(1526110841) pass in quick on igb4 route-to (igb5 134.3.212.1) inet from 192.168.1.20 to 192.168.100.1 flags S/SA keep state label "USER_RULE: PC TC4400 Modem" [ Evaluations: 1048 Packets: 0 Bytes: 0 States: 0 ] [ Inserted: pid 79204 State Creations: 0 ] @182(1417115627) pass in quick on igb4 inet from 192.168.1.0/24 to any flags S/SA keep state label "USER_RULE: Allow ALL IPv4" -
@mrsunfire said in Alias firewall block rule not blocked!:
Does
pfctl -vvsr | grep -A3 1526110841show anything more? -
Are you mixing and matching current data with old?
-
Right now the old config works. But I post it anyways:
@181(1526110841) pass in quick on igb4 route-to (igb5 134.3.212.1) inet from 192.168.1.20 to 192.168.100.1 flags S/SA keep state label "USER_RULE: PC TC4400 Modem" [ Evaluations: 946 Packets: 0 Bytes: 0 States: 0 ] [ Inserted: pid 41920 State Creations: 0 ] @182(1417115627) pass in quick on igb4 inet from 192.168.1.0/24 to any flags S/SA keep state label "USER_RULE: Allow ALL IPv4" -
Are the states that you posted citing rule 181 old data or new?
We need to be looking at the same rule set as the state table or we are just wasting time.