amazon prime does not work with pfsense (openvpn)
-
Hi,
I am on pfsense 2.4.4 and using expressvpn for client vpn.
When I connect to Amazon Prime (USA) using express vpn desktop application, I am able to connect and access prime, however when I use pfsense openvpn to connect to amazon. I get the below message:
Your device is connected to the Internet using a VPN or proxy service. Please disable it and try again. For more help, go to amazon.com/vpn.
The expressvpn server on both expressvpn app and on pfsense openvpn client are the same.
In DNS Resolver, network interface selected are LAN and local host. The outward interface = VPN_WAN.
I am using google and cloudfare dns on pfsense. I tested for dns leak - I don't see my local ip or ISP DNS or my location. I changed the system time to match the target...didn't solve the problem.The below are enbled
DNSSEC, DNS query forwarding, Use SSL/TLSIn advanced, the below are checked
Hide Identity, Hide Version, Query Name Minimization, prefetch DNS Key support, Harden DNSSEC dataWhat could be the reason from expressvpn app, amazon works fine, however with pfsense it doesn't.
Any help is appreciated.
Thx.
-
i have this problem with any provider that advertises streaming capabilities with pfsense.
i tried for a year. tried multiple providers that DO work with their app. but with pfsense i get your same message. i ended up setting rules for smart TV's to only utilises the WAN. none of the openvpn tunnels
hopefully i will learn something new in this thread...
-
And how is this anything to do with pfsense - NO SHIT the streamers are blocking vpn services.. Complain to your service you choose that the streamers are blocking them ;)
Pick a different vpn service - you understand its going to be a wack-a-mole game with the vpn services and the streaming services right ;)
Fire up your own vps in the country you want to look like your coming from to access the streaming service you want.. This has zero to do with pfsense, and nothing pfsense can do to help you with such a problem.
This should be moved to general and your subject should be amazon prime doesn't work with vpn service XYZ... I can tell you I watch amazon video almost every day.. Going to go finish off sneaky pete with the wife here in a few minutes. Works just FINE using pfsense..
-
Hi,
You could try port forwarding DNS requests from your smart TV to the dns server of your vpn provider.
If that doesn’t work try DNS over TLS (port 853) in unbound and use VPN-WAN as outbound if.Put in a floating rule to stop dns (853) exiting via WAN....
-
@johnpoz said in amazon prime does not work with pfsense (openvpn):
And how is this anything to do with pfsense - NO SHIT the streamers are blocking vpn services.. Complain to your service you choose that the streamers are blocking them ;)
Pick a different vpn service - you understand its going to be a wack-a-mole game with the vpn services and the streaming services right ;)
Fire up your own vps in the country you want to look like your coming from to access the streaming service you want.. This has zero to do with pfsense, and nothing pfsense can do to help you with such a problem.
This should be moved to general and your subject should be amazon prime doesn't work with vpn service XYZ... I can tell you I watch amazon video almost every day.. Going to go finish off sneaky pete with the wife here in a few minutes. Works just FINE using pfsense..
i disagree. its a configuration issue within Pfsense/ Openvpn somehow
if i setup 2 tunnels with difference providers (who state the service works) according to the leak tests are not leaking. but i get a message from amazon i am using a vpn using Pfsense. something still is not setup right.
as posted by the OP and myself. if you use their software from the VPN provider it does work. so that is not a provider issue, i still think it is configuration.
where would be the correct place to post this?
-
@DMZ-008 said in amazon prime does not work with pfsense (openvpn):
I am using google and cloudfare dns on pfsense. I tested for dns leak - I don't see my local ip or ISP DNS or my location
But the dns query is from a location..
If your in region A, and you query dns for streamer.com - you get back an IP 1.2.3.4 that is for your region A..
I you then hit that strteamer.com IP 1.2.3.4 from a vpn IP of 4.5.6.7 what do you think the streamer thinks?
If you route ALL your traffic, even your query of dns through the vpn - then your query for dns comes from IP 4.5.6.7, and your connection comes to streamer comes from 4.5.6.7
You need to make sure your dns query and your actual connection come from the same region.. And even then its still a wack-a-mole your playing with the streamer service and the vpn IPs, etc.
The streamer has zero clue to if your using pfsense or not.. So this is not a pfsense issue...
Streamers are all hosted off CDNs - and globally... But if your in region A, they don't give you an IP to hit the CDN in B.. IP from A hitting CDN in B is a clear sign of someone trying to circumvent their restrictions.
Here - perfect example
Here is query from NL for www.amazon.com, I have box over there I can route through..$ dig @8.8.8.8 www.amazon.com ; <<>> DiG 9.14.1 <<>> @8.8.8.8 www.amazon.com ; (1 server found) ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 14254 ;; flags: qr rd ra; QUERY: 1, ANSWER: 3, AUTHORITY: 0, ADDITIONAL: 1 ;; OPT PSEUDOSECTION: ; EDNS: version: 0, flags:; udp: 512 ;; QUESTION SECTION: ;www.amazon.com. IN A ;; ANSWER SECTION: www.amazon.com. 1257 IN CNAME www.cdn.amazon.com. www.cdn.amazon.com. 26 IN CNAME d3ag4hukkh62yn.cloudfront.net. d3ag4hukkh62yn.cloudfront.net. 59 IN A 52.222.154.143 ;; Query time: 136 msec ;; SERVER: 8.8.8.8#53(8.8.8.8) ;; WHEN: Sun May 19 07:04:40 Central Daylight Time 2019 ;; MSG SIZE rcvd: 124Where is that 55.222 IP located..
Now do a dns query from my actual IP.
$ dig @8.8.8.8 www.amazon.com ; <<>> DiG 9.14.1 <<>> @8.8.8.8 www.amazon.com ; (1 server found) ;; global options: +cmd ;; Got answer: ;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 57579 ;; flags: qr rd ra; QUERY: 1, ANSWER: 3, AUTHORITY: 0, ADDITIONAL: 1 ;; OPT PSEUDOSECTION: ; EDNS: version: 0, flags:; udp: 512 ;; QUESTION SECTION: ;www.amazon.com. IN A ;; ANSWER SECTION: www.amazon.com. 1558 IN CNAME www.cdn.amazon.com. www.cdn.amazon.com. 46 IN CNAME d3ag4hukkh62yn.cloudfront.net. d3ag4hukkh62yn.cloudfront.net. 59 IN A 99.84.250.155 ;; Query time: 35 msec ;; SERVER: 8.8.8.8#53(8.8.8.8) ;; WHEN: Sun May 19 07:05:15 Central Daylight Time 2019 ;; MSG SIZE rcvd: 124Where do you think that 99.84 is actually located?
Can tell you that if ping IP that is 55, its a long way from my actual location
Pinging 52.222.154.143 with 32 bytes of data: Reply from 52.222.154.143: bytes=32 time=126ms TTL=237 Reply from 52.222.154.143: bytes=32 time=118ms TTL=237 Reply from 52.222.154.143: bytes=32 time=122ms TTL=237If I ping the 99 address is a lot closer
Pinging 99.84.250.155 with 32 bytes of data: Reply from 99.84.250.155: bytes=32 time=12ms TTL=242 Reply from 99.84.250.155: bytes=32 time=13ms TTL=242 Reply from 99.84.250.155: bytes=32 time=9ms TTL=242If I do a traceroute from my actual location I can tell its for sure in EU somewhere..
10 11 ms 11 ms 11 ms chi-b21-link.telia.net [213.248.90.181] 11 118 ms 118 ms 117 ms nyk-bb4-link.telia.net [62.115.137.58] 12 125 ms 124 ms 132 ms ldn-bb3-link.telia.net [62.115.113.21] 13 116 ms 125 ms 117 ms prs-bb3-link.telia.net [62.115.134.92]You can see where it leaves the states and goes over to london and then look like that 62.115 address "prs-bb3-link.telia.net"
Is in Helsinki, Finland...
If you do a PTR on those IPs you can work out where in the world they are located..
server-99-84-250-155.ord50.r.cloudfront.net [99.84.250.155]
See the ord50, that would mean its in Chicago area - which is me ;)
server-52-222-154-143.fra53.r.cloudfront.net [52.222.154.143]
See that fra53, that would tell me its in Frankfort, DE... Which would make sense if I was asking for where to go to amazon.com from EU..
-
How do you connect to your VPN providers Server ? Hostname or IP ?
My provider offers hostnames. E.g. country.provider.com or city.provider.com
It will then distribute (or maybe load balance) incoming connections and resolve to a specific IP.If a streaming provider had blacklisted a specific IP you may get the VPN warning....
I suggest the following. Connect to the VPN provider via desktop app. In pfsense check which destination ip the tunnel is using.
Configure the ovpn client in pfsense to use the same IP and test.
-
@gcu_greyarea Hi, my vpn provider does not share the DNS servers. They asked to use google dns instead.. which I am already using
-
@DMZ-008 said in amazon prime does not work with pfsense (openvpn):
They asked to use google dns instead.. which I am already using
And you need to make sure the google servers are actually queried via the vpn connection - or your going to get different CDN locations for the vpn region and your location.. Went into great detail on this in my previous post.
-
@bcruze Hi, I agree. This is a pfsense / openvpn configuration issue rather than a vpn provider issue. Something seems to be leaking from pfsense/ openvpn which the dns leak tests are not able to detect but amazon is.
-
@johnpoz Hi..In DNS Resolver, network interface selected are LAN and local host. The outward interface = VPN_WAN. The DNS traffic is going through the VPN tunnel.
-
@gcu_greyarea Hi..I am using server hostname.
sorry..how do I check the destination ip the tunnel is using.
-
If the dns traffic is going through the vpn, and the actual traffic is going through the vpn.. And your being blocked by the streamer.. How do you think it could be a pfsense issue.
But your streamer complains that your using a vpn - how and the hell do you think this has something to do with pfsense?
-
@johnpoz I tried to both ways (dns traffic through tunnel and w/o) ..the end result is the same. I seek opinion from the forum on what pfsense configuration has worked for others.
-
There is no magic here... If all your traffic both dns and actual traffic is going through the vpn.. And the streamer says your using a VPN... Then what do you think you could do on pfsense to circumvent that?
Pfsense is a router/firewall distro... Not sure why the community should help you use the tool to circumvent some streamers geoip restriction policy in the first place to be honest.
Contact your vpn service - since they seem to be in the circumvention business.
Here simple google finds this.
Amazon Prime Video streams great on select US servers. These change occasionally, so we recommend hitting up ExpressVPN’s 24-hour live chat support to ask which servers currently work with Prime Video
As previous stated this is always going to be a wack-a-mole game..
-
@DMZ-008 said in amazon prime does not work with pfsense (openvpn):
sorry..how do I check the destination ip the tunnel is using.
Have a look at the state table. "Show states" on the pfsense Dashboard.
You can then filter by Interface or search for IP Adresses/Ports.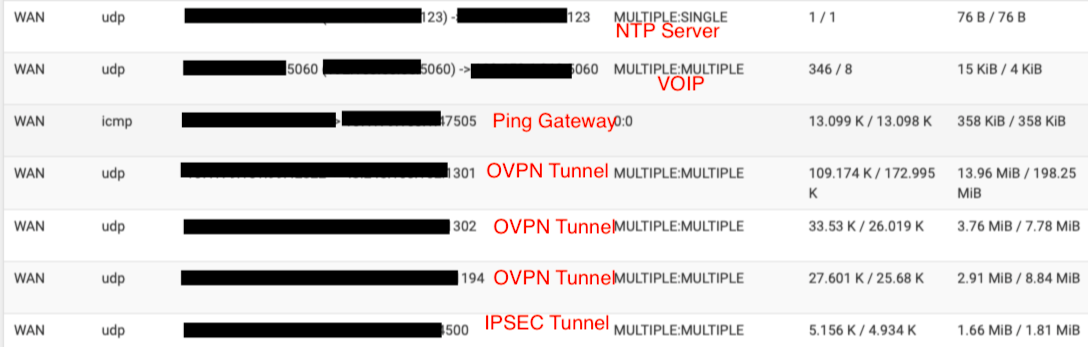

You can see that there are no DNS Requests on the WAN interface, but going through the VPN Tunnel instead (Port 853)
-
Well when I go home in two days I think I will have it working..the android Sony TV is the final test
I read a command used by another provider and it works when I remote into my Mac and use the chrome browser
Read this page : https://openvpn.net/community-resources/pushing-dhcp-options-to-clients/
For the record it has Never worked in chrome before making this change to dns in the advanced configuration window
EDIT.
it still does not work. Amazon Prime and Netflix both detect a VPN. so frustrating and makes NO sense
-
What if we could just allow the amazon server to bypass the vpn, like we could do with selected clients?
I have 1 laptop and 2 tablets that bypasses my vpn. I created a firewall rule to bypass the traffic on those devices though the WAN gateway and made a alias list of those devices.
Is there a way to do that with Prime?
I used packet capture on my device and looks like these are the ip's used by prime, did an arin search and found the net range, which is huge.(54.176.0.0-54.191.255.255) -
@edwardnizz you can check out this video https://www.youtube.com/watch?v=cX1_f-KRJhY
-
I just got my pfSense/NordVPN client setup. I'm routing ALL DNS traffic over the VPN, which I think solves the DNS leak issue. Only selected/tagged/aliased (VPN_HOST) LAN hosts have other TCP4+UDP4 traffic routed through the VPN.
I have verified that no host can access even https://amazon.com until it become a VPN_HOST.
In other words, if the DNS used is somehow whack (sorry I'm missing the lexicon to describe) compared to the WAN IP, amazon is confused.