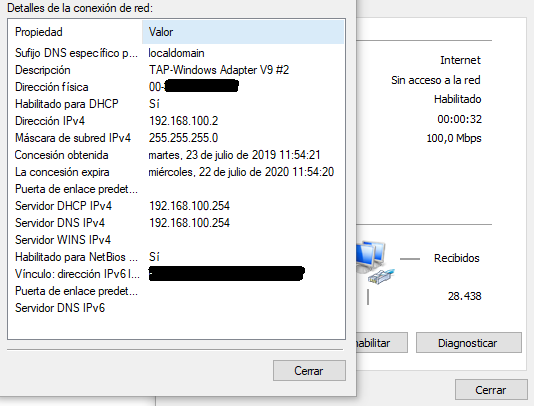
Only first connected user got DNS domain resolution.
-
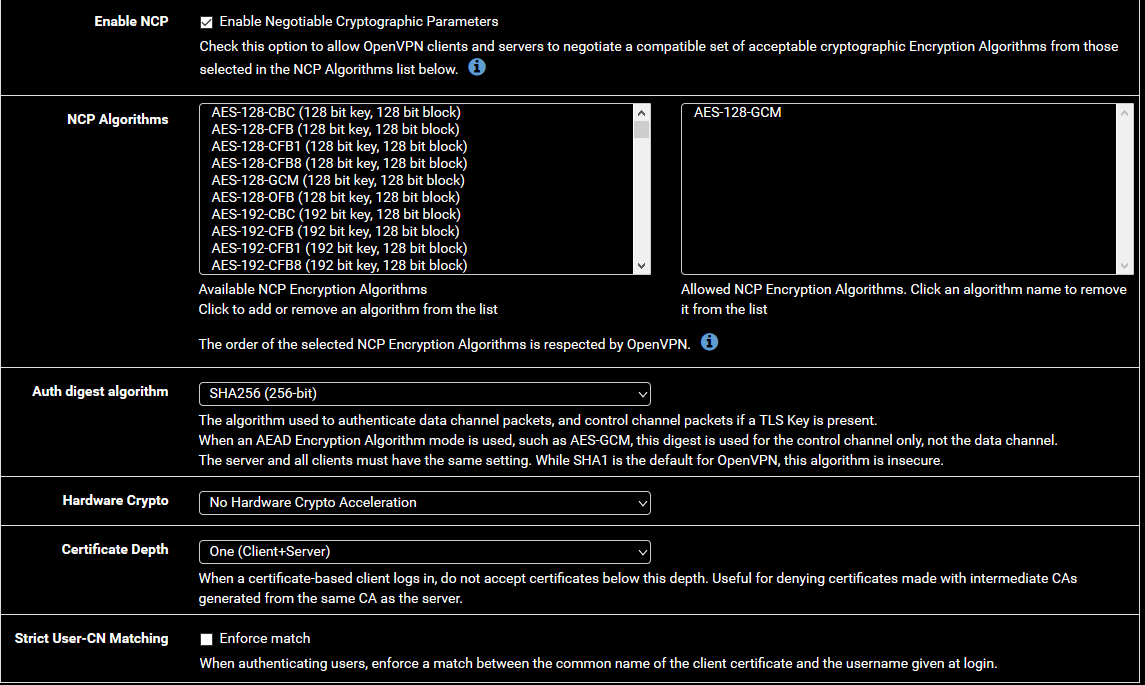
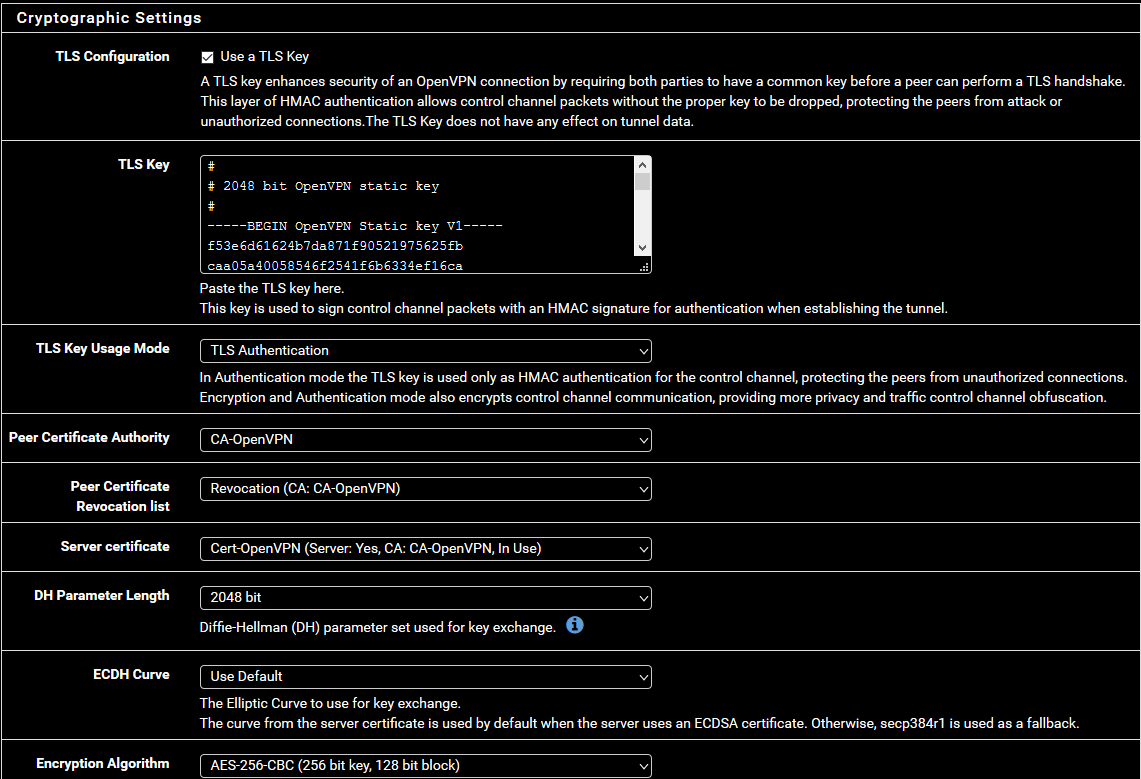
This :
@Pippin said in Only first connected user got DNS domain resolution.:https://www.youtube.com/watch?v=PtZxuC9IyTg
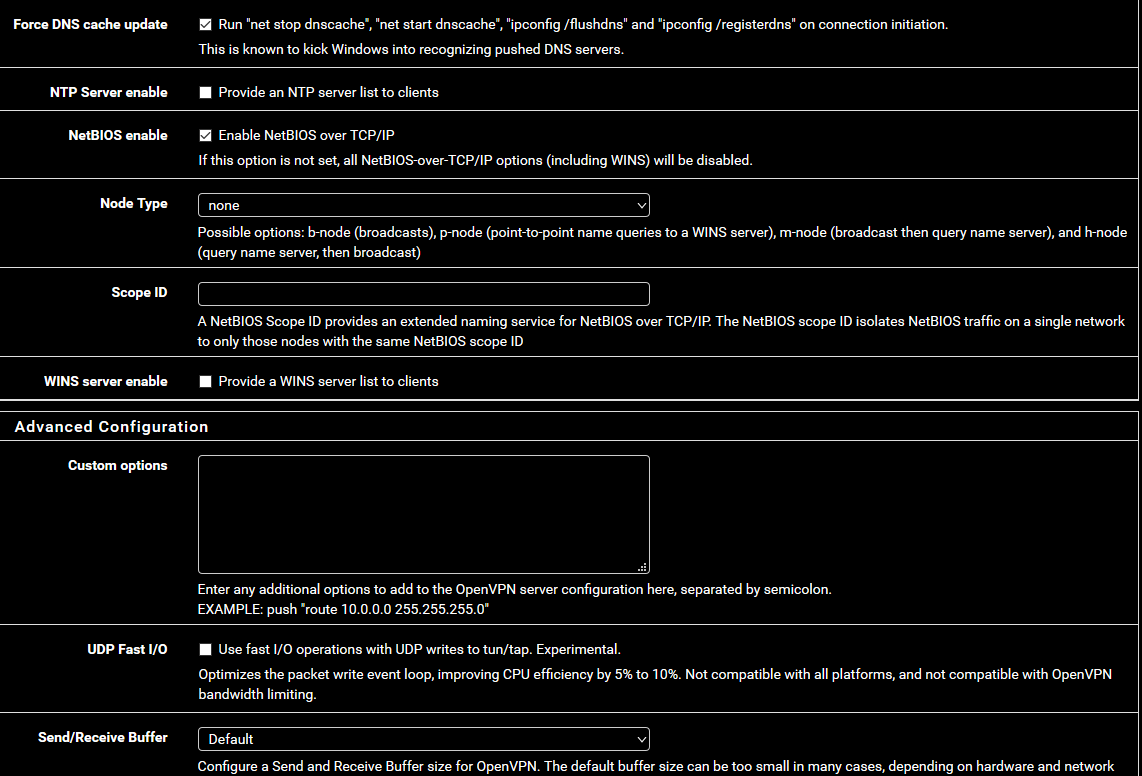
192.168.100.254
192.168.100.1are valid addresses.
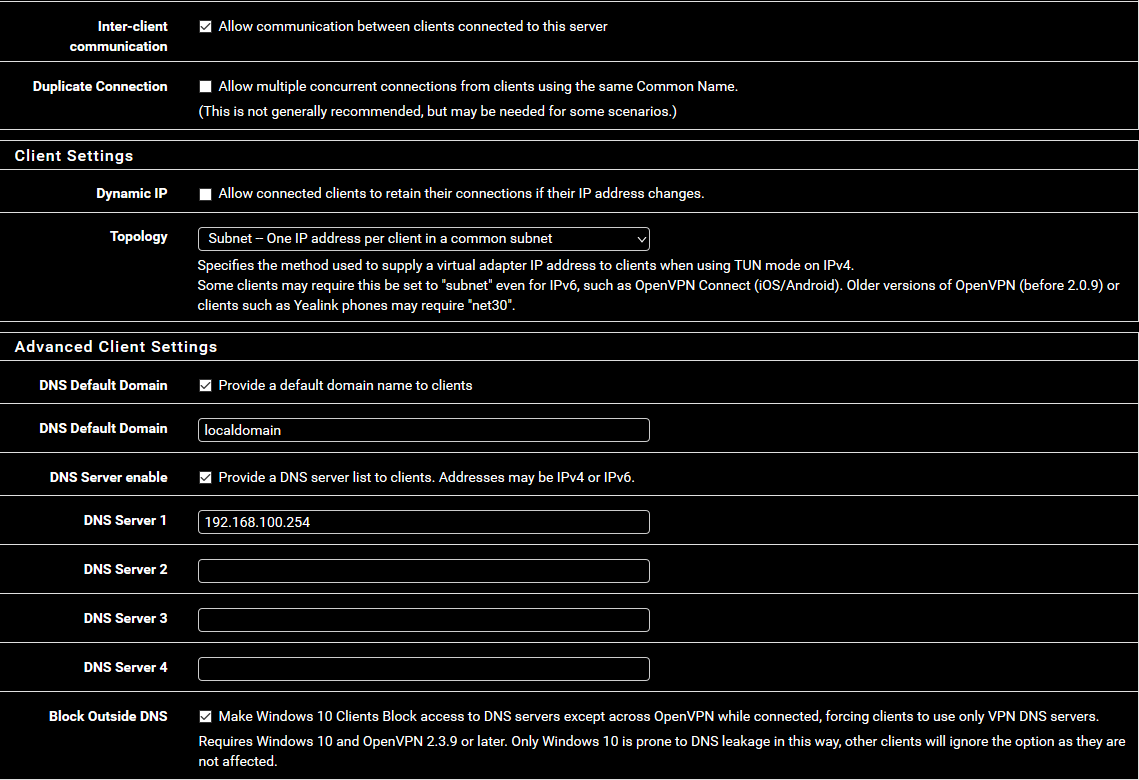
pfSense is delivered with a 192.168.1.1 on it's LAN."WINS" servers still exists these days ?
-
Thanks for the answers.
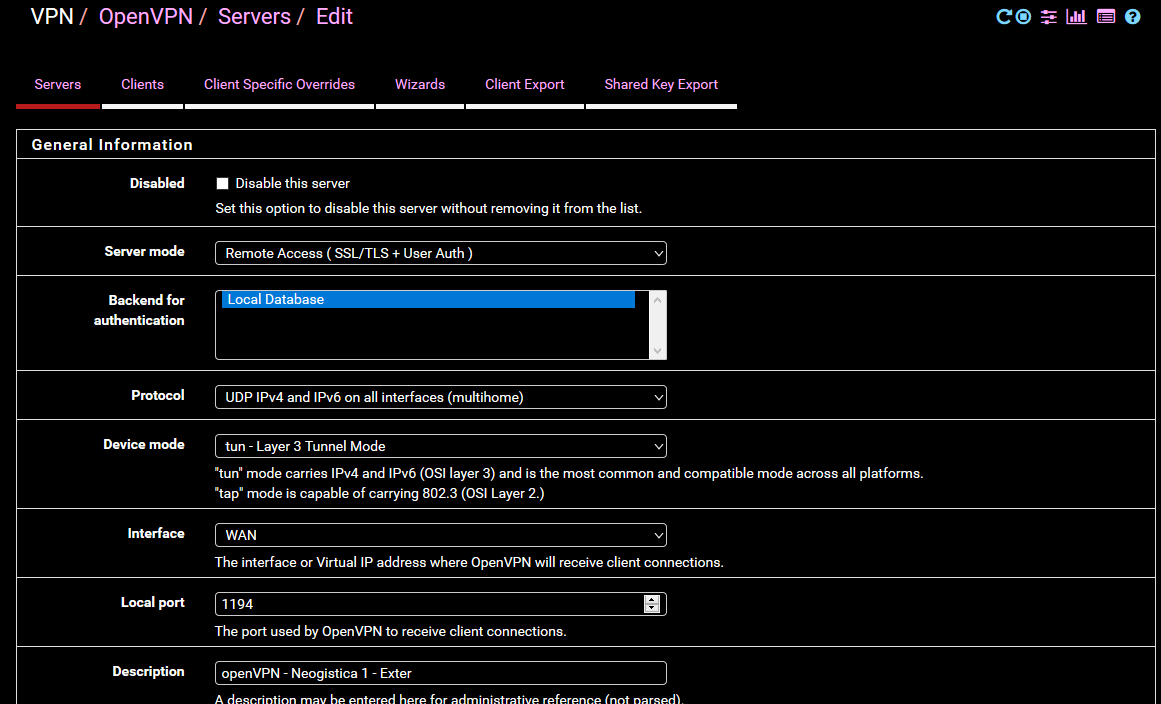
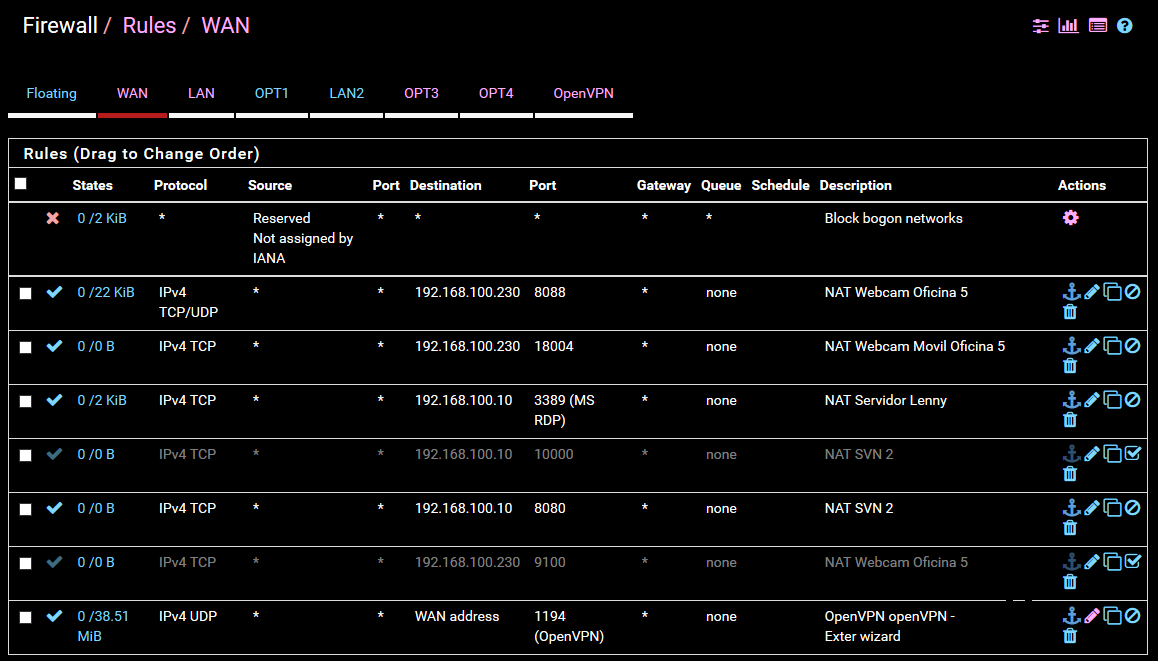
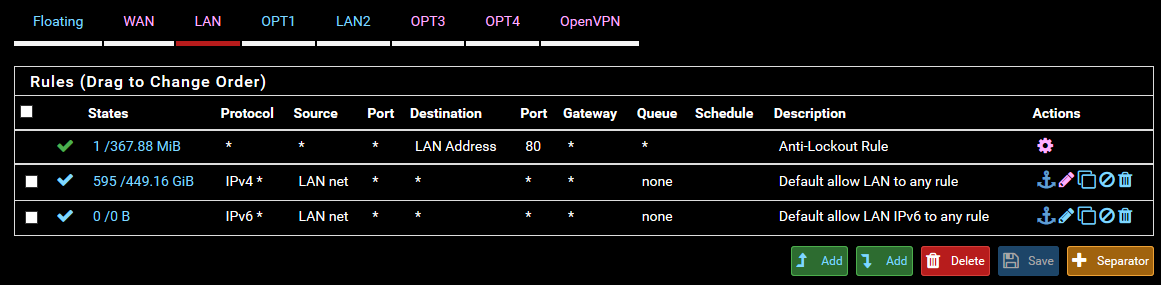
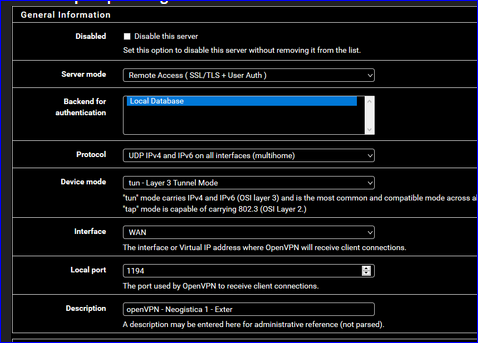
I'm attaching the rules for firewall view.
Please let me know if its needed more information.
Wan
Lan
Openvpn Tab

-
Your OpenVPN firewall rule looks fine.
33,86 MB of traffic passed by : ok.It's time to make this :
readable.
-
@Gertjan It must be your settings because his updated images look good to me. I can read every line, and I have pretty thick glasses.
-
Thanks for your comments again.
Ive just edited images at full image size, hope it works this time.
-
Images look fine here too.
@Gertjan said in Only first connected user got DNS domain resolution.:
This :
@Pippin said in Only first connected user got DNS domain resolution.:https://www.youtube.com/watch?v=PtZxuC9IyTg
192.168.100.254
192.168.100.1are valid addresses.
pfSense is delivered with a 192.168.1.1 on it's LAN."WINS" servers still exists these days ?
It won't work...
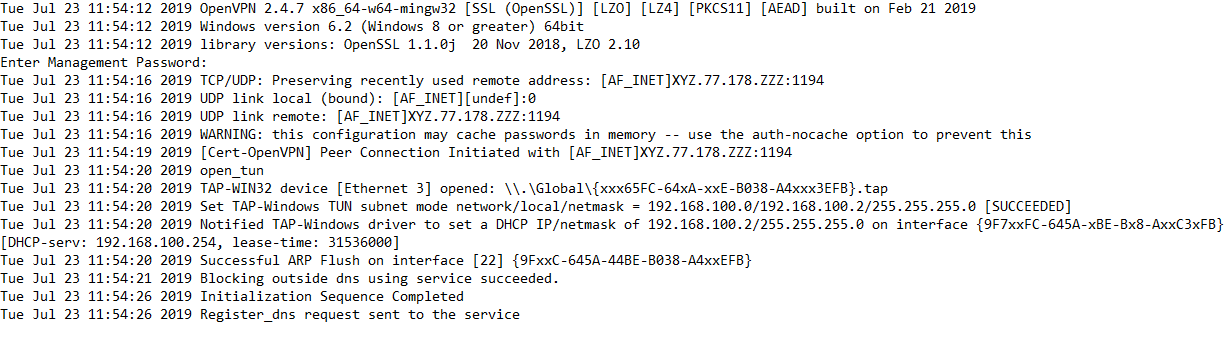
.0 is the tunnel network designation
.1 is the servers tunnel IP
.254 is OpenVPNs internal DHCP server
.255 is broadcast
Leaving 252 addresses for clients.There is an exception though. The servers tunnel IP could be used to point to a service if that service is running on the OpenVPN host.
Pointing to a service is typically not done on tunnel addresses. -
@Pippin said in Only first connected user got DNS domain resolution.:
It won't work...
.0 is the tunnel network designation
.1 is the servers tunnel IP
.254 is OpenVPNs internal DHCP server
.255 is broadcast
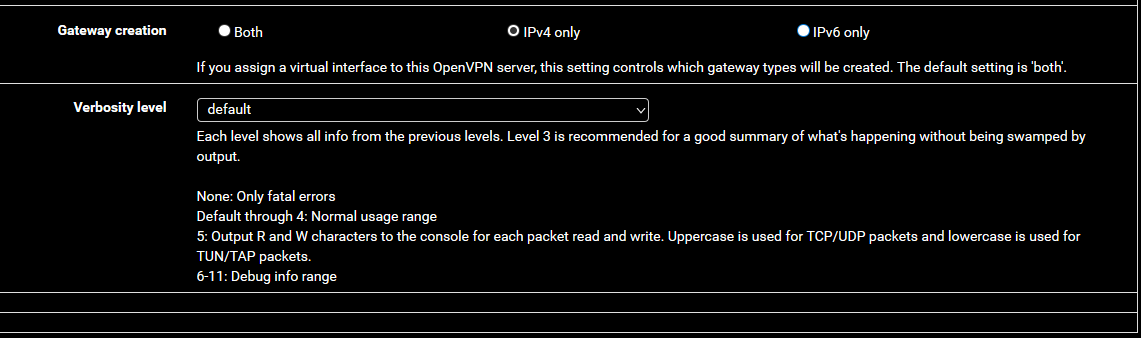
Leaving 252 addresses for clients.192.168.100.254 it's the pfsense gateway and we put the " IPv4 Tunnel Network " as 192.168.100.0/24 for supposedly new openvpn clients get an IP from the same Pfsense LAN ( 192.168.100.0/24 ).
Thanks for your comments.
-
That's not how it works.
Your tunnel network cannot be your LAN network...case of conflicting subnets.
-
@Pippin said in Only first connected user got DNS domain resolution.:
That's not how it works.
Your tunnel network cannot be your LAN network...case of conflicting subnets.
@Pippin thanks for the clarification. Could you confirm to me if, after changing the ' Virtual Tunnel Network ' to anything else ( ie: 10.0.8.0/24 ), will be needed to add any rule to firewall/openvpn in order to that change work ?.
Regards,
-
All rules related to the virtual tunnel network.
-
@Pippin said in Only first connected user got DNS domain resolution.:
All rules related to the virtual tunnel network.
@Pippin really appreciate all comments. Works great now. As you mention, the error were putting the LAN network as the Virtual Network. Now, all clients connects, resolve domains and ping lan ips : ).
Thank u all for the time.
Regards,
-
Glad you got it working.