firewall routing problem
-
Good day,
I have a situation that i need your help with please
i have a pfsense firewall with a lan ip address of 172.23.56.0/24 network
on the firewall rules for the lan interface i allowed any to all for both ipv4 and iüpv6 .we have some computers on our network that are are using an accounting program that has to be connected to the private network of one of our customers
.
the customer has a vpn server on our network that has the ip address 172.168.56.10,
and the network behind the vpn server is the 10.10.0.0/15 network.the problem i am having is that whenever the clients want to connect to the servers that are behind the vpn server pfsense drops the connections.
please how do i allow the connections to work smoothly,
i have created the following rules
i have allowed all traffic from lan to the 10.10.0.0/15 network.. still on the firewall logs it is dropping themplease what am i doing wrong ?
-
@donmay said in firewall routing problem:
the customer has a vpn server on our network that has the ip address 172.168.56.10
Which subnet is that connected to?
You LAN is 172.23.56.0/2, as you stated.@donmay said in firewall routing problem:
i have allowed all traffic from lan to the 10.10.0.0/15 network.. still on the firewall logs it is dropping them
Post a screenshot.
-
thank you for your replay.. it is actually connected in our internal network it has an internal ip of 172.23.56.10/24 and it serves as a gateway for all other devices that want to connect to the 10.10.0.0/15 network
-
So all LAN devices that want to connect to an IP in 10.10.0.0/15 have a static route for that network directing packets to 172.23.56.10?
If so, it has nothing to do with pfSense, since that traffic won't pass it.Consider that there will be a static route for your LAN needed on the destination devices in 10.10.0.0/1 as well.
-
Hi ,Thanks very much for the reply,
The static route is actually been set up on the pfsense itself,
i actually created a gateway ip pointing to the 172.23.56.10 computer locally and then i created a static route on the firewall that if it recieved from the lan interface a traffic that should go to the 10.10.0.0/15 network, it should forward it to the 172.23.56.10 internal vpn server. -
With the static route on pfSense you will get an asymmetric routing issue, cause packets from your LAN devices will pass pfSense while responses from the remote site won't.
If you're using a DHCP server in your LAN and the concerned computers are configured to pull network settings from it, you may distribute the route by the DHCP server. So you don't have to add a route to each of the concerned devices.
-
@donmay said in firewall routing problem:
The static route is actually been set up on the pfsense itself,
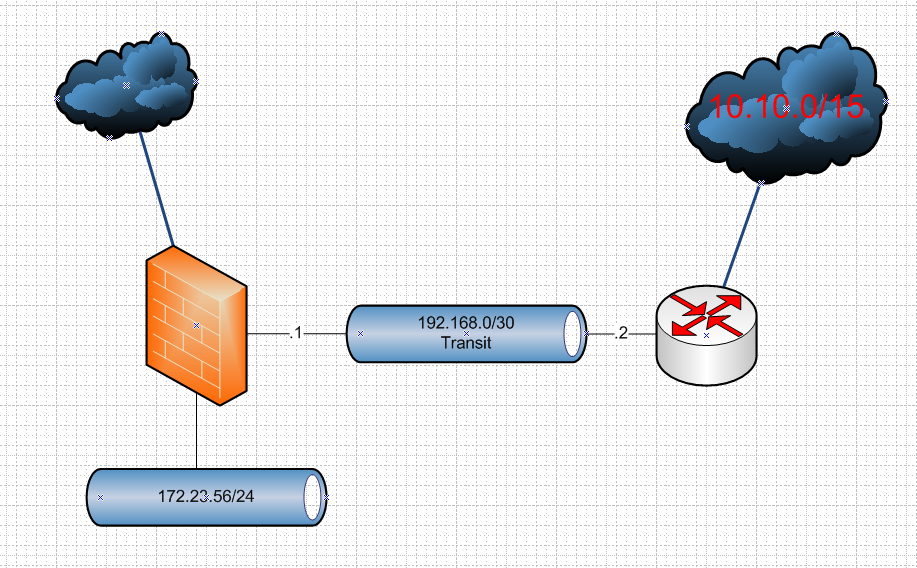
Yeah as mentioned by @viragomann that is asymmetrical and going to be problematic.. If you have a different gateway downstream of pfsense, it should be connected to pfsense via a transit network vs doing routing on the host.
Say something like this
This is a typo right?
172.168.56.10You meant 172.23.56.10, it has an IP on your lan network. 172.168 is public address space. And would amount to you running multiple L3 on a single L2, your lan network.
-
I would like to use this opportunity to say thank you all for your wonderful help on this issue. i think i have been able to know more about asymmetrical routing now

i decided to go for the first option in this article
https://docs.netgate.com/pfsense/en/latest/firewall/troubleshooting-blocked-log-entries-due-to-asymmetric-routing.html
i am truly grateful -
You went with sloppy state? That is not a "fix" that is a work around.. And to be honest it shouldn't even be mentioned in how to fix asymmetrical traffic. It amounts to a MacGyver solution using rubberbands and bubblegum..
You should correct your overall network design vs using bandaids.
-
what will you recommend i do then.. because i have this situation and the internal lan devices need access to this internal ...
what do i do then please ? -
You create a transit network as I showed in my drawing..
Now clients that want/need to go too this 10 network, can just be allowed via simple firewall rule. If you don't want everyone to be able to get there.
Transit network can be just a vlan if you want, or if you have an another interface on pfsense can just connect the downstream router there..