Setting up OpenVPN for new remote office
-
So I've been trying to set up an Site-to-Site Static Key OpenVPN Instance, in order to connect two sites, using this documentation : https://docs.netgate.com/pfsense/en/latest/vpn/openvpn/configuring-a-site-to-site-static-key-openvpn-instance.html
What I'm trying to accomplish:
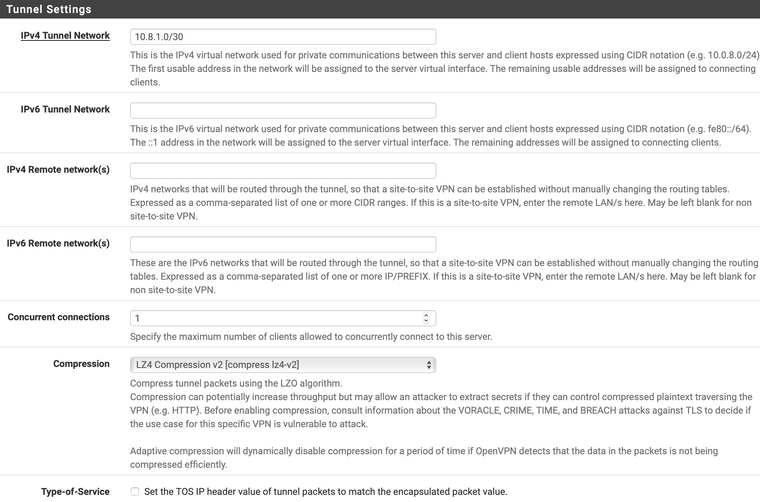
I want to make available 10.0.3.XXX and 10.0.4.5 on the service side, to the client side.
I don't need anything available from the client side to the server side.
I want all other traffic to go OUT of the tunnel.So I can get the connection up and running, but from the client side, I cannot connect to 10.0.3.XXX or 10.0.4.5
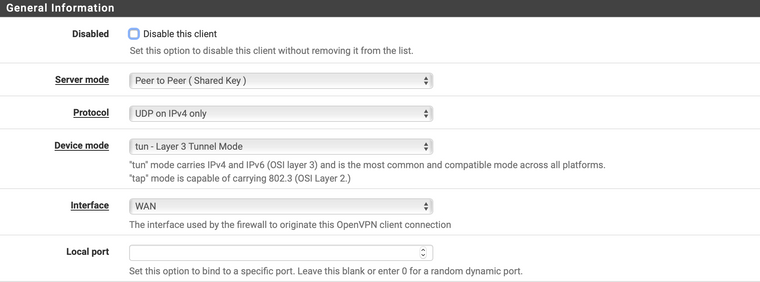
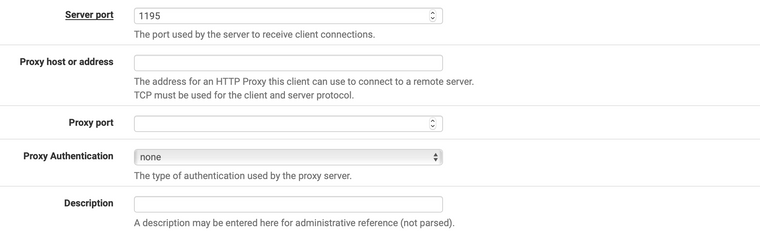
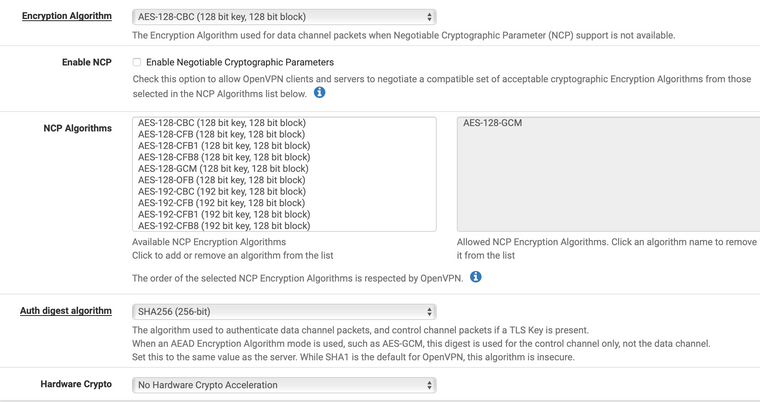
Here are my configs, I really don't know what I did wrong??
I only took out the shared key and the hostname, everything else is below.
Note: I haven't done anything on the client side firewall, should there be a rule?
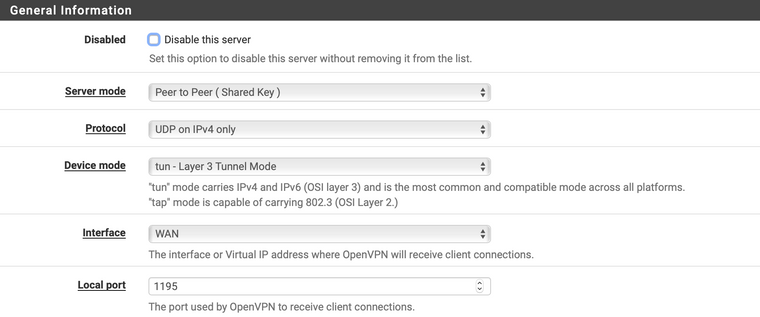
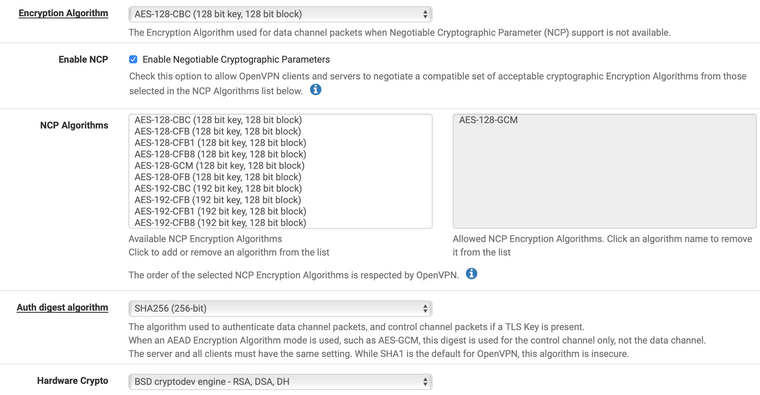
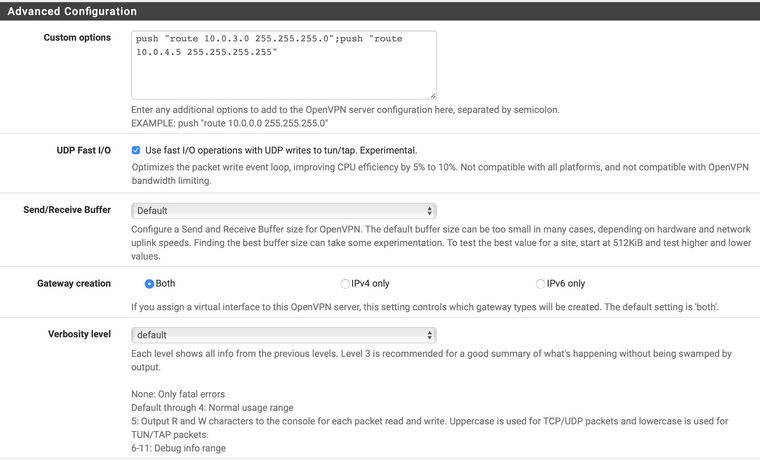
Server side
Client side
-
You cannot push routes using shared key. OpenVPN does not support it.
Set those networks as "Remote Networks" on the other side.
-
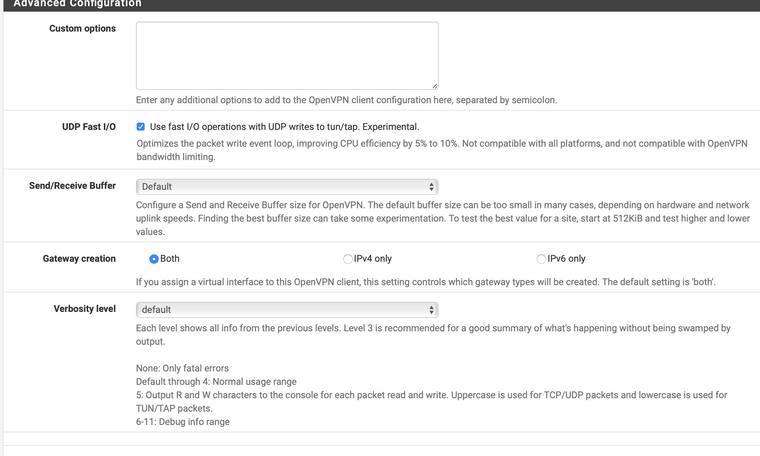
Get rid of the custom options. You do not need that there.
Use " 10.0.3.0/25,10.0.4.0/28" on the IPv4 Remote Networks line at the office opposite of those. Do the same for the office where those are with the subnet of the opposite office on the other end. Yes you have to.
Control access with firewall rules on the OpenVPN tab. OpenVPN interface comes from the opposing side.
Source (IP subnet or addresses from opposite address) Destination (LAN Subnet) ect.
Edit- beat me to it. :)
-
Thanks @Derelict
So on the server side, I got rid of the custom options.
On both side, IPv4 Remote network(s) are set to:
10.0.3.0/24,10.0.4.5/30I reloaded OpenVPN server and OpenVPN client services.
Again, the VPN can connect, but I can't access 10.0.3.XXX or 10.0.4.5
The logs don't show much except the connections.
Is there anything I need to do with the firewall rules?
The only thing I did was on the server side :
PASS / WAN / IPv4 / UDP / Destination : port 1195I didn't do anything on the client side.
-
You need rules on the OpenVPN tab on each side passing traffic you want to be allowed into the firewall.
You also need to be sure the firewalls on the target hosts pass traffic from "foreign" networks. Think windows firewall here.
10.0.4.5/30 is not a valid /30 subnet. The proper /30 containing 10.0.4.5 is 10.0.4.4/30. Doubt that is interfering with your ability to connect to 10.0.3.0/24 though.
-
Hey @Derelict,
I just noticed something.
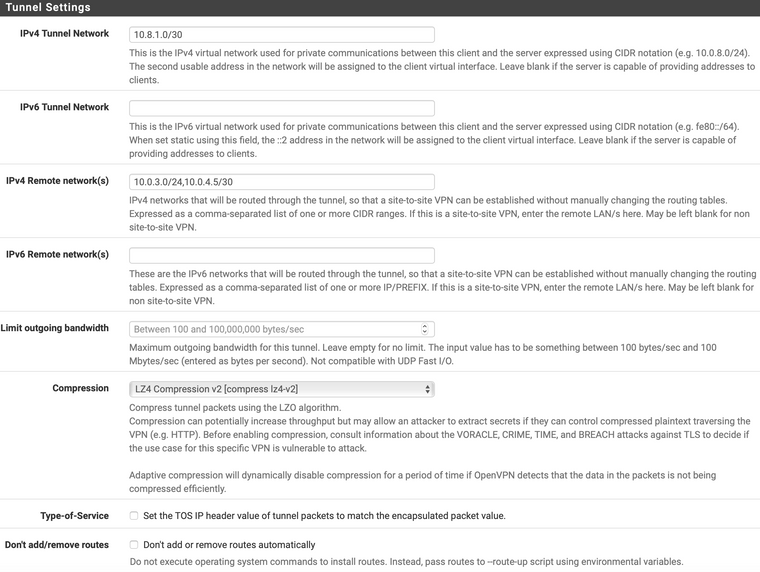
I have two OpenVPN servers running on the "server side"
One is a remote access (SSL / TLS + User Auth) server for "road warriors", running on port 1194 and with a subnet of 10.8.0.0/24
The second one is a shared key server for the remote site (the one I'm trying to set up right now), running on port 1195 and with a subnet of 10.8.1.0/24
Now I've just noticed that when both servers are running, it's impossible to connect to 10.0.3.XXX or 10.0.4.5!
So there must be some kind of conflict but I can't figure it out.
For exemple, I was not able to connect using my "road warrior" setup.
But I disabled the 1195 server (shared key) and immediately, my road warrior setup was connecting successfully.Any idea how I can fix the so-called conflict?
-
Anyone has an idea for my two Open VPN servers conflict?
Please

-
Based on the information given, no.
There is no problem having multiple OpenVPN servers running on different ports.
If traffic enters an OpenVPN interface, there must be a rule allowing it.
If traffic is to be sent out an OpenVPN interface, there must be a route. You do not set the remote networks the same on both sides of a tunnel. You set the remote networks to the networks on the other side you want to route to. (aka the remote networks).
You will probably want to include the current configurations and a specific example (including source and destination addresses, etc) that cannot communicate.
-
Hey @Derelict, thank you so much for your help.
So I'm trying to figure out what you're saying, sorry for being a n00b.
Based on the information given, no.
There is no problem having multiple OpenVPN servers running on different ports.
If traffic enters an OpenVPN interface, there must be a rule allowing it.
On the server side, there are two firewall rules :
- PASS / IPv4 UDP / WAN / 1194
- PASS / IPv4 UDP / WAN / 1195
No rules on the client side (SG-1100).
I think on the firewall side everything seems correct?
If traffic is to be sent out an OpenVPN interface, there must be a route. You do not set the remote networks the same on both sides of a tunnel. You set the remote networks to the networks on the other side you want to route to. (aka the remote networks).
On my "road warrior" set up (Remote Access (SSL/TLS + User Auth)), I set up IPv4 Local network(s) to:
10.0.3.0/24,10.0.4.0/24Everything works perfect: I can connect to a host on 10.0.3.XXX using OpenVPN client on Windows and Viscosity on MAC. We've been using it for years successfully.
As soon as I fire up the second OpenVPN service (openvpn_2), nothing works anymore.
You will probably want to include the current configurations and a specific example (including source and destination addresses, etc) that cannot communicate.
The current configuration is up there:
https://forum.netgate.com/topic/146151/setting-up-openvpn-for-new-remote-office/3With the exception that now on both sides of the Peer to Peer (Shared Key) Open VPN configuration, the IPv4 Remote network(s) are set to:
10.0.3.0/24,10.0.4.0/24So for example, I have a NAS server on 10.0.3.20
I want to connect to it with SMB.
Normally, I would fire up my OpenVPN client, connect through 1194 to my OpenVPN server with Remote Access (SSL/TLS + User Auth) and I can easily connect to my shares, no problem.
Now as soon as the second OpenVPN server on 1195 with Peer to Peer (Shared Key) configuration is running on the server side: I will still be able to connect like I usually do to my 1194 OpenVPN server I will not be able to connect with SMB to my 10.0.3.20 host.
I'm not sure if that's the info you wanted? If not, let me know and I'll be happy to provide more.
-
Why are you setting the remote networks on both sides of a p2p connection to the same networks? Set each side to list the networks on the other side.
-
@Derelict that's because of that:
@chpalmer said in Setting up OpenVPN for new remote office:
Get rid of the custom options. You do not need that there.
Use " 10.0.3.0/25,10.0.4.0/28" on the IPv4 Remote Networks line at the office opposite of those. Do the same for the office where those are with the subnet of the opposite office on the other end. Yes you have to.
So I set it up on both sides.
Now I'm assuming I need to get rid of it on the client side, right?
-
The networks that are on the other side of the tunnel go in the remote networks setting on each side. Consult your network diagram to determine which networks are where.
-
On the client side, I don't want to make anything available.
On the server side, I just want to make 10.0.3.0/24,10.0.4.0/24 available.
-
You have to put the networks you are sourcing from in the remote networks on the other side in order to route traffic. Else you have to assign an interface and perform outbound NAT to the tunnel address.
You can determine what connections can be made into that side using firewall rules on the OpenVPN tab.
-
So basically, on the CLIENT side I should put 10.0.3.0/24,10.0.4.0/24 in IPv4 Remote network(s)
and on the SERVER side I should leave blank.
Right?
-
Check out
https://www.netgate.com/resources/videos/site-to-site-vpns-on-pfsense.html
to get a basic understanding how it works. :-)-Rico
-
@BlazeStar said in Setting up OpenVPN for new remote office:
So basically, on the CLIENT side I should put 10.0.3.0/24,10.0.4.0/24 in IPv4 Remote network(s)
and on the SERVER side I should leave blank.
Right?
No. You have to put the remote networks on each side to be able to route traffic (or implement tunnel address NAT). You control who can connect to what using firewall rules.
Yeah, some study into exactly what is going on is likely in order.
-
@Rico said in Setting up OpenVPN for new remote office:
Check out
https://www.netgate.com/resources/videos/site-to-site-vpns-on-pfsense.htmlThat's the video I watched to set up my stuff.
Yet I'm still very puzzled why it doesn't work.
Around the end of the video, a few tests are recommended, and when I try them they fail.
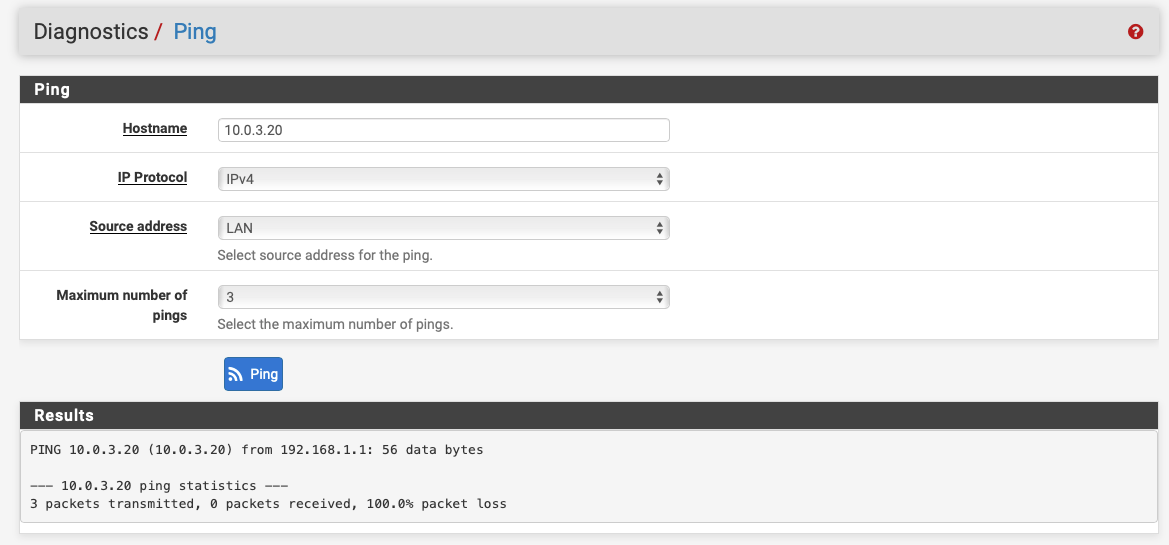
For example, I try to ping host 10.0.3.20 which is a server I have on the server-side.
On the client-side, from pfSense, it works:
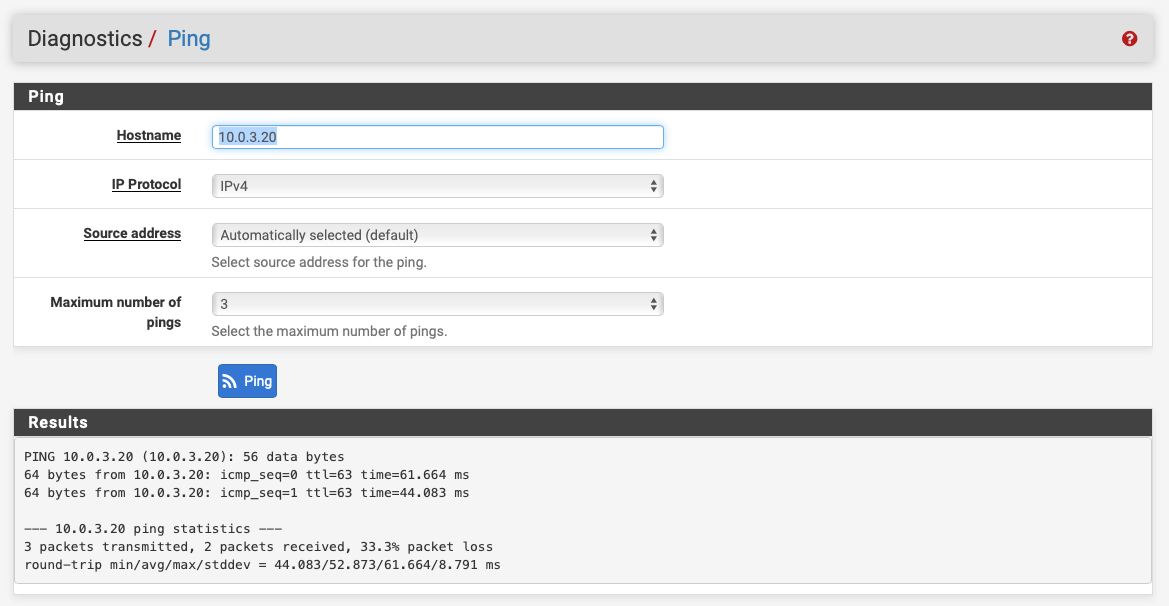
On the client-side, from LAN, it fails!!
And in the routing tables I see this:
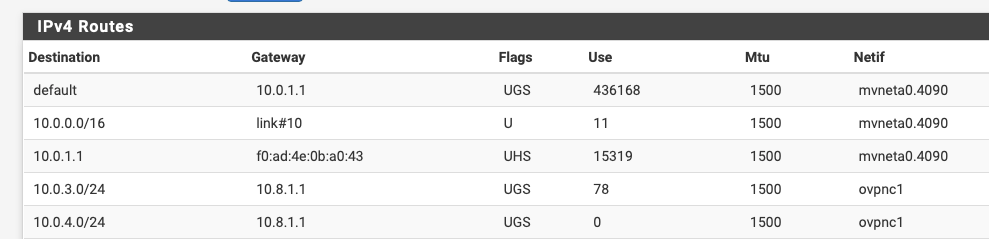
Which appears to me like, once again, this should work!
Anything I'm not seeing here??
-
Does the server side have a route back to 192.168.1.1?
-
@Derelict on the server-side I can see this entry in my routing table:

So I would say yes there's a route back.
Is that what you meant?