Connection issues with pf enabled LAN to LAN
-
Hi All.
I have implemented pfSense as an internal router between two LANs. I have an ESXi server running a couple of VMs where I wanted to be able to control the network access of these VMs. A couple of services running on these VMs are made available externally and I am trying to keep everything nice and secure.
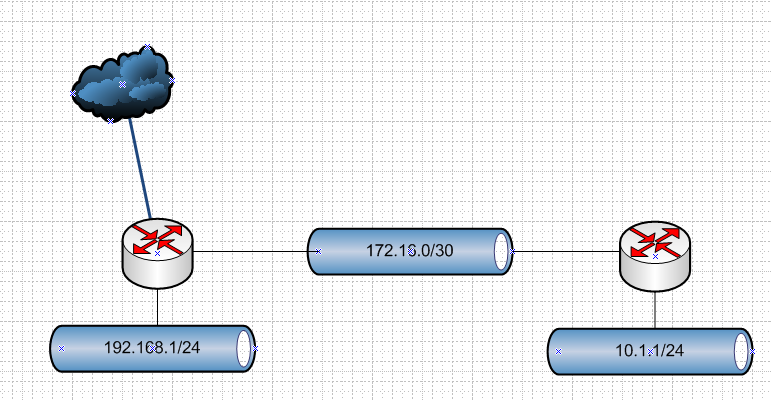
pfSense is configured with the 'WAN' interface connected to the existing LAN (LAN #1 192.168.1.0/24), and the pfSense 'LAN' interface created the new LAN (LAN #2 10.1.1.0/24). This is an overview of how I have everything setup:

I have static routes configured on the primary router to redirect any 10.1.1.x traffic to gateway 192.168.1.2 (pfSense WAN), and in pfSense to direct any 192.168.1.x to 192.168.1.1.
I have a DNS server running on the primary router with entries for the 192x and the 10x networks. I can resolve DNS entries and ping to the correct IP from machines running in both LANs, also from the pfSense shell directly.
The problem that I am having is that services are not communicating with pf enabled. For example, with pf running I can RDP from Server #1 to Server #2 and #3 but I cannot RDP from Server #2 or #3 to Server #1. I have the same issue connecting to SQL Server. For example Server #1 is a MSSQL server, I cannot connect to the MSSQL service from Server #2 or Server #3. I can ping and get a response and see the ICMP entries in the firewall log.
However, if I disable packet filtering and use pfSense as a router only, I am able to successfully RDP and connect to MSSQl in both directions.
Strangely I do not see any blocked connections in the firewall logs. This is what I am getting when trying to establish a RDP connection from a 10x machine to a 192x machine:
With the static route on pfSense enabled:

With the static route on pfSense enabled:

But - the RDP connection is never successful. The MSSQL behaves simularly however the error I receive at the client is due to handshake response timeout.
My firewall rules are currently open-slather - WAN:

LAN:

Ordinarily I would replace the primary router with pfSense but the ESXi host is a development environment and I want to be able to take the whole thing offline without impacting the internet connection to everything else. So insdead I am trying to keep everything on the host secured in a bubble or at least having explicit access granted where needed. I don't want to rely solely on routing as I want to be able to implement access control to specific external sites. I am open to alternatives setup ideas too.
Thanks, Rob.
-
@robbith said in Connection issues with pf enabled LAN to LAN:
I have static routes configured on the primary router to redirect any 10.1.1.x traffic to gateway 192.168.1.2
No need to read past this - this is asymmetrical and is going to cause you nothing but grief. If you want a downstream router, then it would be connected via a transit network.. If your going to put hosts on the transit, then you would have to do host routing on each host telling them how to get to your downstream network.
Your downstream route would not be doing nat either..
btw: Great drawing.. Thanks for that, makes it quite clear where your problem is.
This is how you would do a downstream router.
This is your problem
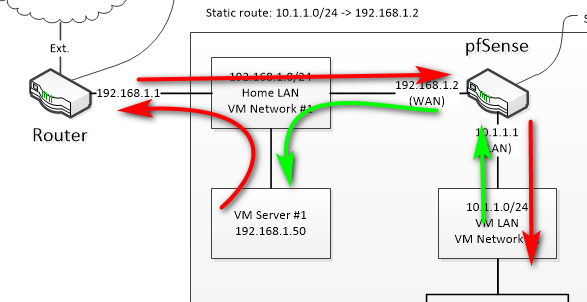
See the traffic flow.
-
@johnpoz thanks heaps for the comprehensive reply - that makes sense. I just did some reading up on asymmetric routing and it's clear that this is the issue.
I do have one question regarding the transit network - I am assuming this is a separate interface/vlan - basically a link that joins the two routers together? If this is the case, Router #1 doesn't support VLANs (yet), nor can I allocate a second interface. So, I might head back to the drawing board or just consider using a pfSense VM as a single gateway with WAN and two LAN interfaces (this would be the ideal setup anyway).
@johnpoz said in Connection issues with pf enabled LAN to LAN:
btw: Great drawing.. Thanks for that, makes it quite clear where your problem is.
Glad it was clear. I have spent enough time in support to know the pain of having to spend hours going back and forward requesting more information.
Thanks for your help.
-
Yeah just use pfsense, with multiple lans is the way to go.. Get rid of whatever shit router that can not do vlans
You can do it the way your doing it, but you have to route on each host in the transit network (home lan) in your setup. Telling them to get to 10.1.1. go to 192.168.1.2 vs bouncing it off their default gateway.
Other option is to nat at pfsense, and to get to stuff on 10.1.1 just hit pfsense wan IP 192.168.1.2... You have to do port forwards on pfsense for anything you want to able to get to on the network behind it.