Firewall Rule to Allow RDP from WAN to LAN......Need help
-
Source port is not set it is any (*)
Let me check the advanced settings...
-
How abouts you post an actual screen capture of the rule instead of a textual approximation of the same.
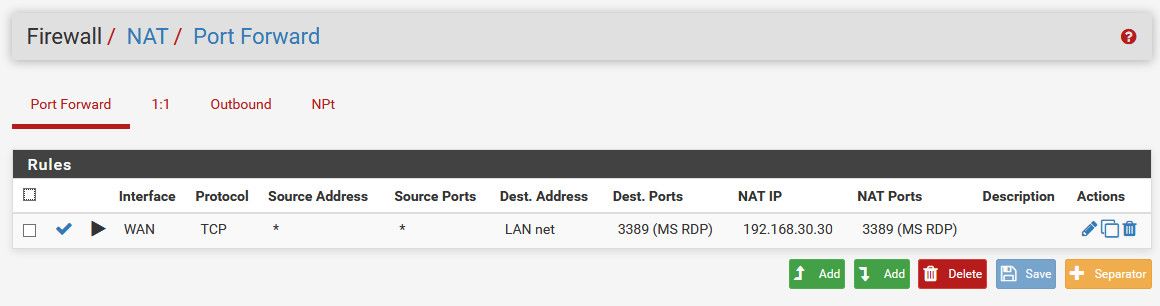
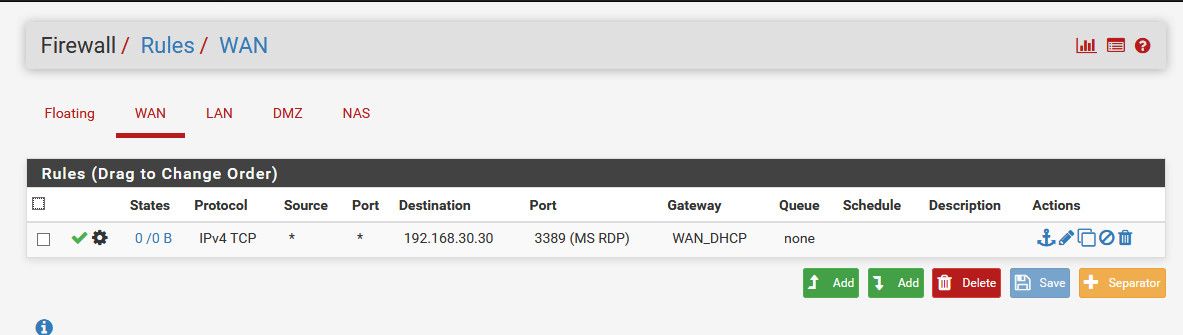
And there are two parts to a port forward. The NAT/PAT rule and the firewall rule. Best you post both.
-
Attach firewall rule & NAT == > WAN
-
OK so you have a port forward on WAN with a destination address of LAN Net. How exactly do you expect that to work?
Why did you set the rule association to Pass? No docs state to do that.
And you are forcing the connection out WAN by setting that gateway on the rule.
-
Any update ???
-
Update? How exactly do you expect such a mess to work??
If you have questions about what something is or means, you need to ask.. Don't just go random clicking shit and picking stuff from the drop down..
To create a port forward in pfsense, really the only thing you have to touch is the port, redirect port, and the IP you want to send it too.. Everything else is going to be pretty much default.
And let the port forward create the firewall rule - which is default..
-
Turn the firewall off on the machine that your are trying to RDP into.
It will treat anything outside its own subnet as public and block it.
Your post with the graphic looks correct although MS recommends a TCP/UDP connection. I do not believe I ever have though. I normally do not leave such a rule in place any longer than I need it.
-
^ looks correct? What are you looking at? It sure not the mess he posted.. Has gateway set on his wan rule, the dest is Lan Net vs wan address in his port forward.
Here is the 3 things that need to be touched to port forward rdp
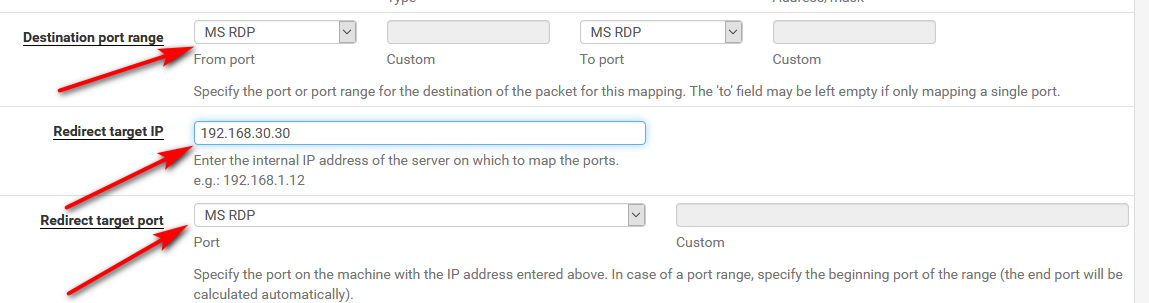
That is it, don't touch anything else - the defaults are all you need. It will create the firewall rule for you. You just need to make sure you turn off the default block rfc1918 rule because your source is actually rfc1918.
edit: Lets get tcp working before he worries about having a UDP connection ;) But sure if he wanted he could change it from default of tcp to tcp/udp.
-
I have tried with NAT Rule that did not helped so used PASS and took the screen shot at that time..
In one of the forum in netgate to mentioned gateway instead of default so I have tried that as well whether it may help...
-
List of things to check is here:
https://docs.netgate.com/pfsense/en/latest/nat/port-forward-troubleshooting.html
-
It should take you like 2 minutes top to trouble shoot a port forward..
Sniff on wan, do you see traffic to 3389? Sniff on Lan - do you see pfsense sending 3389 on to IP you want to send it to..
If you do - your problem is prob firewall on host your sending too, maybe rdp isn't even listening? Maybe it is using a different gateway other than pfsense? Maybe where you wanted to send it is now on a different IP? etc. etc..
Troubleshooting a port forward does not mean randomly changing settings ;)
-
Hi,
And make sure you have enabled "Remote Desktop" on your computer you are trying to RDP :) -
Thanks friends for the help, I can able to access my Windows Machines from WAN to LAN..
Two things I have done one is enabled firewall rules in WAN and added route in my source machine (ie) in WAN network.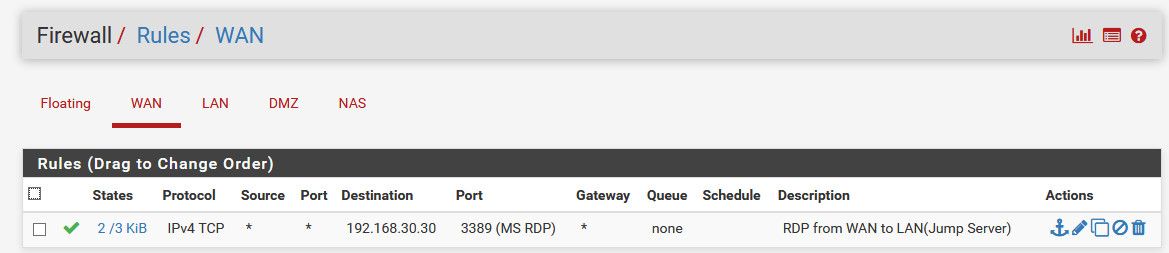
route add 192.168.30.0 mask 255.255.255.0 192.168.50.100
-
So you turned off NAT in pfsense?
-
Yes I have turned off NAT in pfsense...
now I need help in configuring Open VPN for my mentioned design... to access my LAN network through Internet...
Airtel Internet Modem -->Asus RT-AX88U Wireless Router --->PFsense-->LAN and DMZ..
I need to do triple NAT here.. apart from doing this ... can you suggest some other good options...
-
Well if you turned off nat in pfsense, then you would need to route.. And you would really need to be connected via a transit network or your going to run into issues with asymmetrical traffic unless you do host routing on each box that actually sits in any transit network (the network between routers)..
-
@DINU said in Firewall Rule to Allow RDP from WAN to LAN......Need help:
I need to do triple NAT here.. apart from doing this ... can you suggest some other good options...
i went back and read the entire thread again. Why do you need this part: Asus RT-AX88U Wireless Router?
Jeff
-
I doubt he does to be honest... Should just be used as AP to be honest... And now that he has nat turned off good luck getting that modem and asus to actually route and not nat ;)
He should put his modem into bridge mode, and just use pfsense as his edge nat and firewall, and wireless should just be AP... Simplifies the whole mess.
-
I want my family to connect their internet directly without PFsense..SO I have connected Asus RT-Ax88U router between Airtel internet moden and Pfsense...
-
@DINU said in Firewall Rule to Allow RDP from WAN to LAN......Need help:
I want my family to connect their internet directly without PFsense..SO I have connected Asus RT-Ax88U router between Airtel internet moden and Pfsense...
I'm assuming wirelessly, like for mobile devices and stuff? Or wired into the Asus? Is this so they aren't filtered or less confusing for them, or what?
You should, like @johnpoz says above, change it up a little bit.
Airtel Internet Modem (in bridge mode) -> pfsense -> LAN -> Asus RT-AX88U (VLAN'd for only your family to use)
That would make NAT-ing and VPN-ing (like you say you want to do) and etc. into or out of your network so much easier, promise.
Jeff