IoT Network Firewall Rules
-
I have an IoT VLAN that I would like to allow full access out to the Internet and limited access to the rest of my LAN. Here is what I've setup:
VLAN90 10.1.90.1/24 IoT Network
LAN 192.168.1.1/24 Contains the pfSense, switch and Unifi Controller. I have other VLANs but they're not relevant for this issue.Firewall Alias: LAN_NETWORKS
192.168.1.1/24, 192.168.10.1/24, 192.168.20.1/24, 192.168.30.1/24, 192.168.50.1/24VLAN90 firewall rules
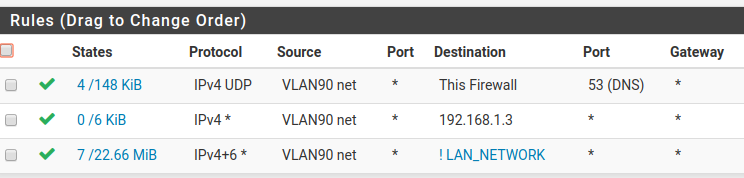
When I connect to the IoT network, I obtain the correct IP address, am able to query DNS servers and I can access the outside world. What has me stumped is I cannot ping 192.168.1.3, which as I understand it should be allowed as the 2nd rule is prior to the inverse LAN_NETWORK rule. What am I missing here?
-
Out of desperation, I stripped back all rules on VLAN90 (guest) and enabled an allow all rule; any protocol from any source to any destination.
I can still access the Internet from devices on this VLAN but cannot ping any device that is on another subnet and nothing is appearing in the logs.
Could this be a routing issue?
-
And does 192.168.1.3 allow ping from this vlan? Windows for example default firewall does not allow pings from other networks.
btw:
192.168.1.1/24, 192.168.10.1/24, 192.168.20.1/24, 192.168.30.1/24, 192.168.50.1/24Those are not networks, those are host addresses the 192.168.1.0/24 would be the network., 10.0/24, 20.0/24, 30.0/24, 50.0/24 etc
When you call out a IP with a /mask and its not the actual wire or network address, all you calling out is a host with a mask.
-
@johnpoz Remember my Unifi issue in a separate thread relating to mDNS. Well, Unifi strikes again.
The guest network is setup on my Unifi Controller with guest policies enabled. There is an Access Control section within Guest Control named 'Post-Authorization Restrictions' which was blocking any traffic to 192.168.0.0/24
No wonder I couldn't see anything in the firewall logs. I was able to get to the bottom of this by plugging directly into a switch, tagging the port with the VLAN ID and running the same ping test. When it worked, I had narrowed it down to the guest wifi.
Stung twice by Unifi in a few days

-
Yeah not understanding how something works or is setup can be frustrating ;)
I don't see the point of guest networks other than for say a hotspot or something.. Create a guest vlan for your "guests" and limit them to what you want - give them your guest psk.. Why force them to go through a captive portal sort of nonsense - is this some sort of hotel ;) Or a starbucks ;)
You sure wouldn't want to use such a setup for iot devices.
-
@johnpoz A hotel would be nice, where is room service!
There is no captive portal for the guest network but it is tagged as a guest network in the Unifi controller, which introduces it's own restrictions. I have now disabled this and have implemented all rules in pfSense
-
there is little reason to run guest network mode on unifi unless you were going to be running captive portal. It a performance hit btw.. Enabling guest services.