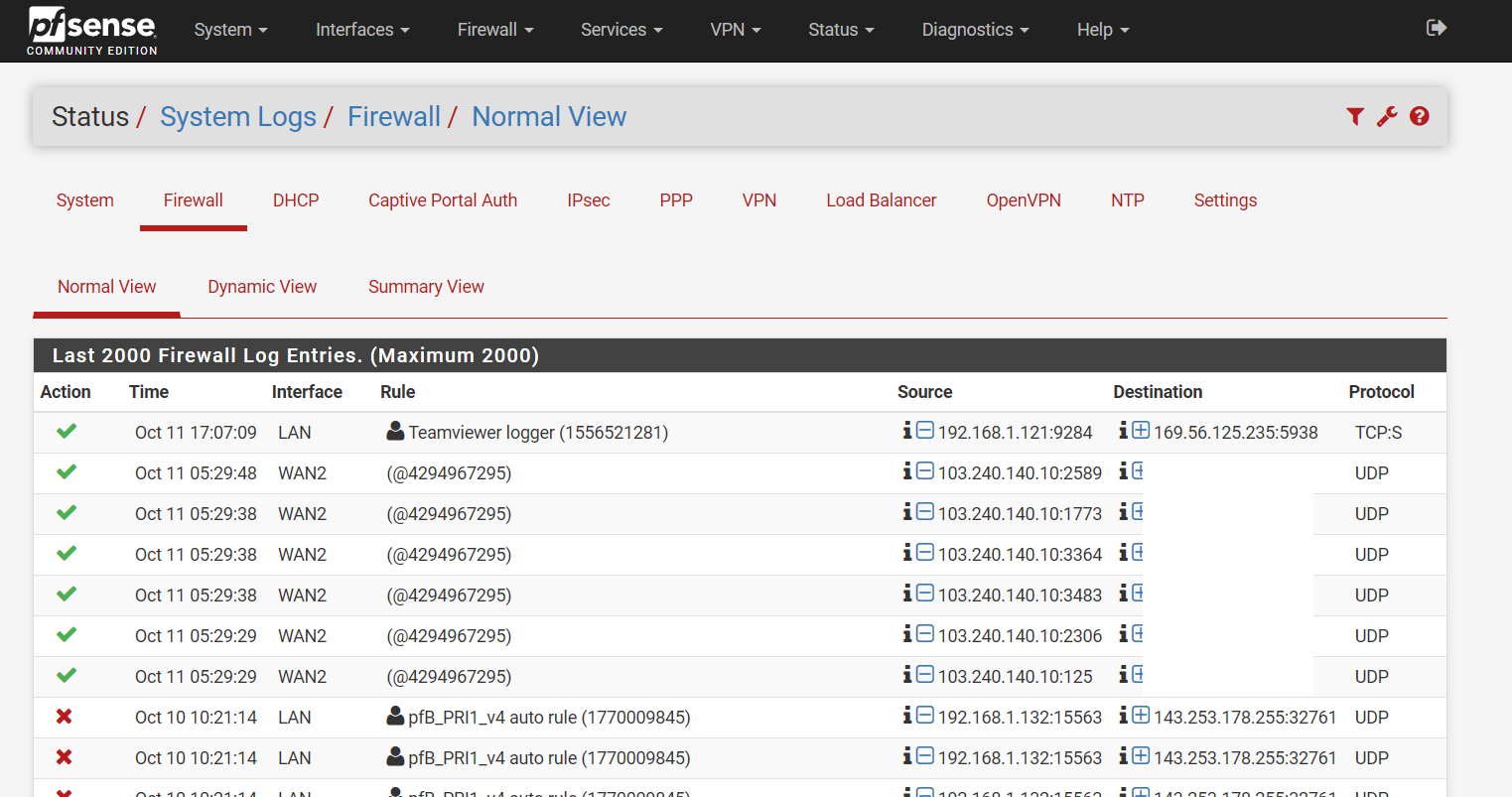
Had my pfSense been compromised?
-
@johnpoz said in Had my pfSense been compromised?:
Then the rule was deleted, make sure your grep is working by using a ID in your command that you see when just looking at the output.
Are you currently seeing logs for this?
grep works for other id e.g. the teamviewer logger.
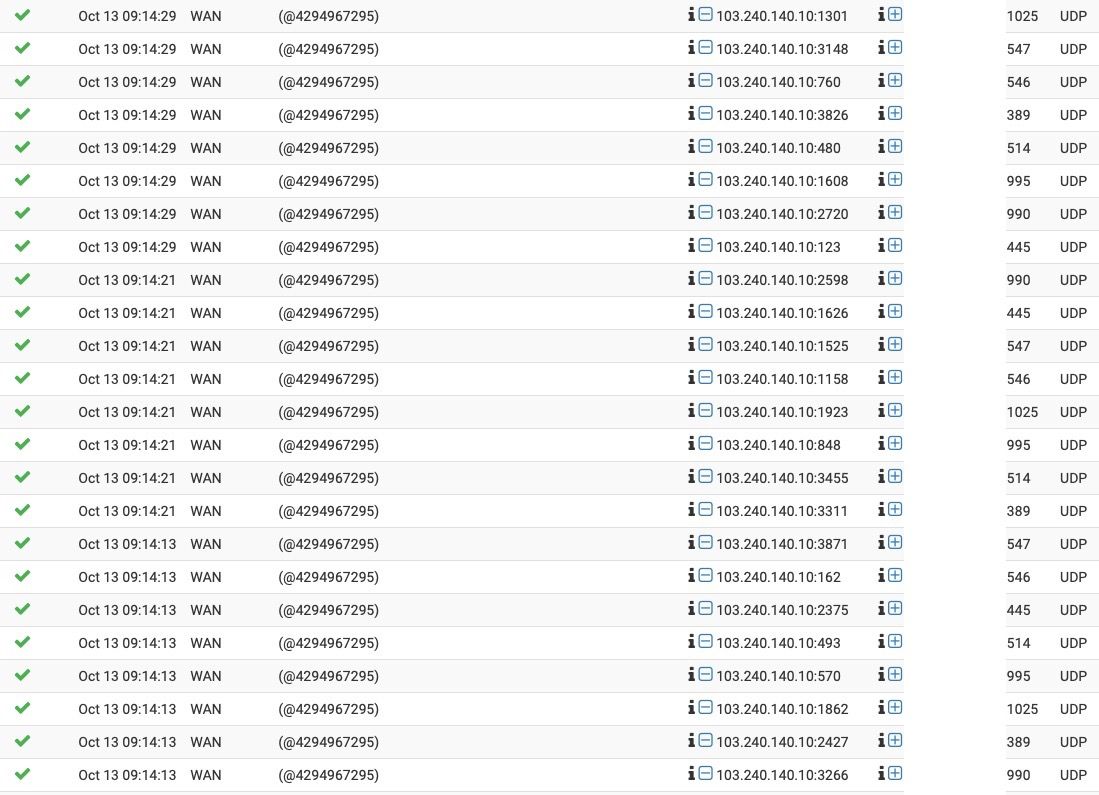
I have 2 WANs for months. This incident was the first time I saw incoming traffic to WAN2 and were logged.
As you can see from my rules, I don't have anything that will log incoming traffic for WAN2. -
Do you have UPnP enabled? Do you have it set to use WAN2, and to log connections?
That's the most likely explanation.
-
That would be my guess as well... You might be able to glean a bit more info by looking at the raw log in output.
-
When I manually trigger something like that (for example, open Deluge, go into settings, and trigger a port test), I get a similar log message with a random-ish ID.
Since the UPnP rules don't have a description, and have random IDs, and are probably short-lived, they wouldn't have a visible description in the logs even if you caught them when they were active.
-
@jimp said in Had my pfSense been compromised?:
Do you have UPnP enabled?
No I have not enabled UPnP.
-
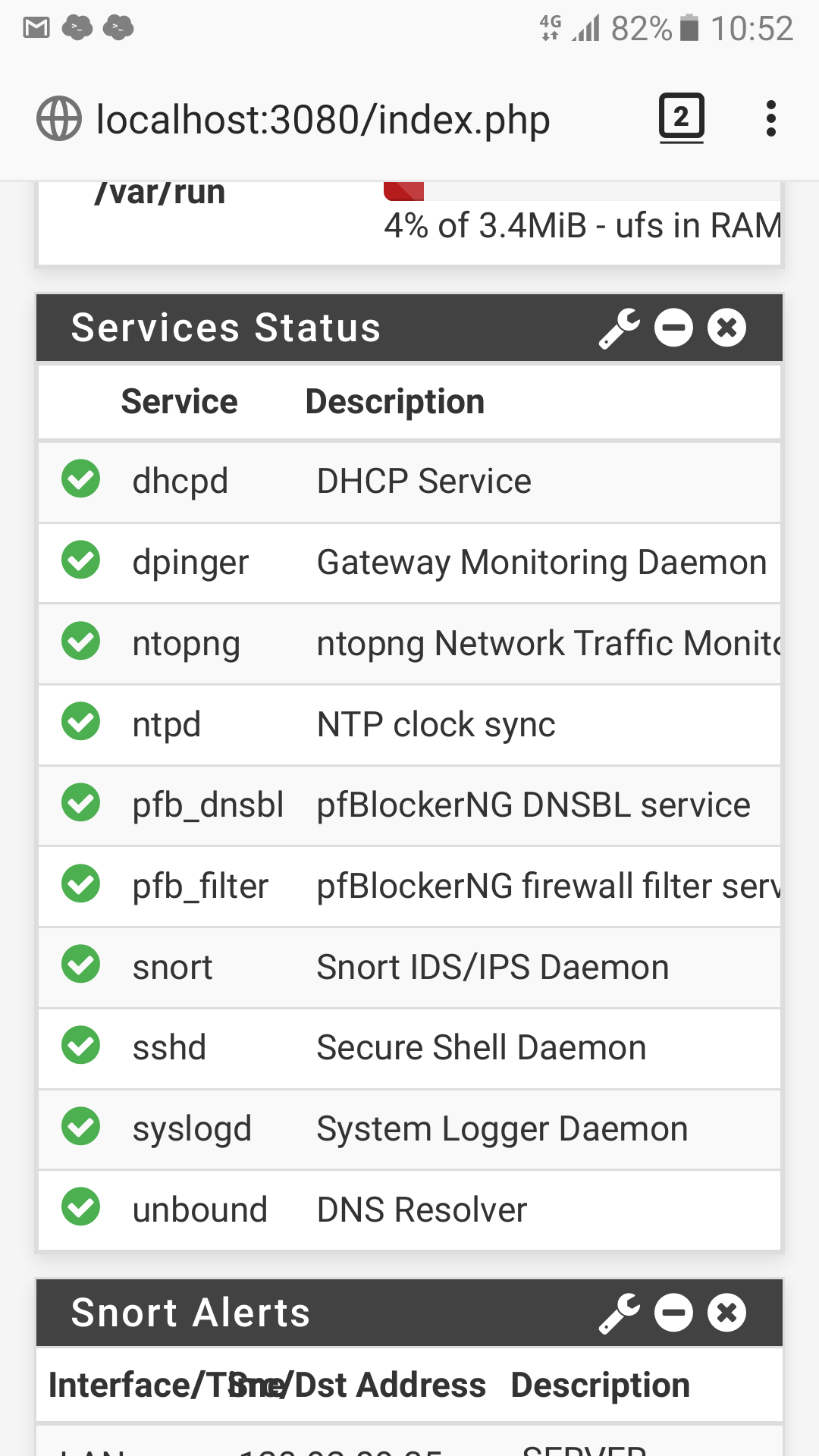
That doesn't actually mean its not running - that is a wiget that can be edited to not show specific services.
-
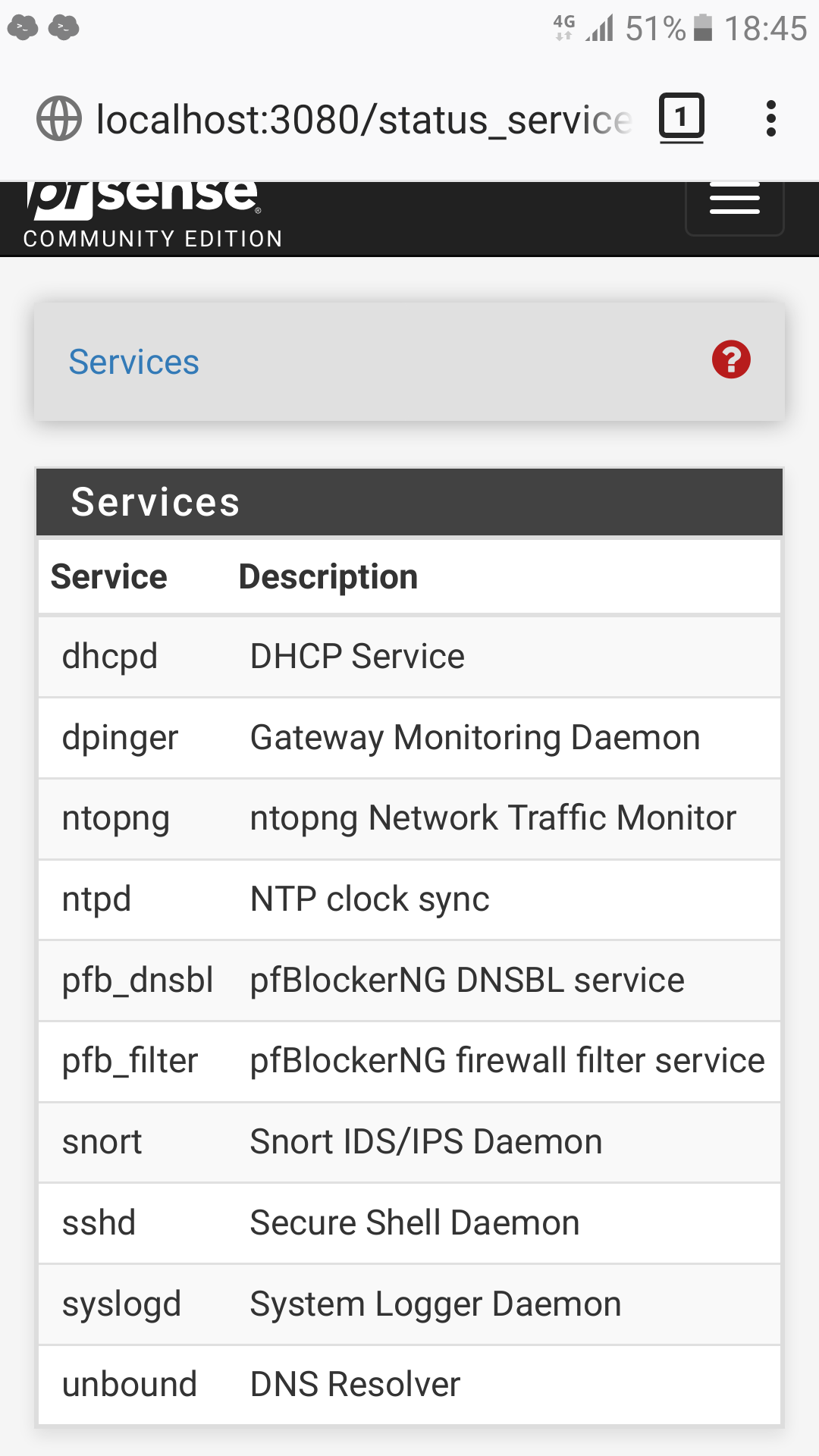
@johnpoz
UPnP is not running:
-
@bchan hey dude, im interested in this as i saw exactly the same thing this morning, about 5 low ports opened by upnp and incoming UDP traffic however i now have no idea what opened them up. Do you have a PS4 on the network as its the only thing i can think that would do this?
-
@hulleyrob said in Had my pfSense been compromised?:
Do you have a PS4 on the network as its the only thing i can think that would do this?
I am running a small office and have no PS4 and have not enabled any uPnP.
-
@bchan ah ok i do have upnp enabled but have the same problem you are and cannot see after the even which computer opened up the ports just that there was a rule and its been deleted.
-
Which is exactly how upnp would work.. So it creates a rule to allow whatever was requested.. It then would delete that rule when request is removed.. So in the logs you would see just the rule ID..
Look with sockstat do you see miniupnpd running? Vs just the status, could be process that didn't shutdown or something.. Also look to see if the ports used are listening 1900, and I think maybe even 2189 or 5351 could be used.
here I enabled it for test
[2.4.4-RELEASE][admin@sg4860.local.lan]/root: sockstat | grep miniupnpd root miniupnpd 18015 4 tcp6 *:2189 *:* root miniupnpd 18015 5 dgram -> /var/run/logpriv root miniupnpd 18015 6 tcp4 *:2189 *:* root miniupnpd 18015 7 udp4 *:1900 *:* root miniupnpd 18015 8 udp6 *:1900 *:* root miniupnpd 18015 9 udp4 192.168.9.253:1920 *:* root miniupnpd 18015 10 udp6 *:44710 *:* root miniupnpd 18015 12 stream /var/run/php-fpm.socket root miniupnpd 18015 13 stream /var/run/php-fpm.socket root miniupnpd 18015 14 udp4 192.168.9.253:5351 *:* root miniupnpd 18015 16 udp6 *:5351 *:*Then turned it off
[2.4.4-RELEASE][admin@sg4860.local.lan]/root: sockstat | grep miniupnpd [2.4.4-RELEASE][admin@sg4860.local.lan]/root: -
@johnpoz is there any log or place i can look that would tell me what IP address requested the deleted rule to be added after the event?
My poroblem isnt that upnp is enabled as that is required for multiple PS4's to work on my network but that I cannot tell what device caused the open ports and requested the upnp rules once they are deleted. -
Wouldn't the dest IP in the log tell you who opened it?
I don't use UPnP... its horrible idea from a general security point of view.. When I did have it enabled for my sons playstation, the play station was on isolated vlan, and UPNP was restricted to only allow requests from his ps ip.. And also restricted in what ports could be allowed also - sure and the F do not need 53 inbound, or 88.. Its not doing freaking kerb inbound, etc..
The lack of documentation in these game consoles and what is actually required is just horrific... How freaking hard is it to say game X needs ABC inbound, and EFG outbound..
Some of them lists ports.. but then they don't call out if inbound or outbound or both, etc.. For example why would they need 80 inbound... This isn't even viable on many home connections because their isp AUP prevents running services and block such a port anyway, etc..
So sorry off the top of my head I don't know that much about how its implemented in pfsense - other than not something I would suggest any one run ;)
-
@johnpoz haha fair enough, i did set up manual rules but gave up after a while especially as there are 2 playstations on the network its just easier.
The IP it shows is just the external IP I cant see which internal IP requested the rule, ive had other things on the network do this as well and its always a pain to see where it originated after the event. I was just hoping someone knew an easier way to find out. Weird how I also have the same IP addresses and ports connecting to my network as OP. -
Not sure call it weird, he had or still has UPnP running - this for explains what he saw in the logs.
-
@johnpoz sorry i meant weird how we both had connections from the same IP address and the same ports. But i aggree it does look like upnp is running on his firewall.
-
Suppose this could be any number of IoT's phoning home? TV, etc.?
-
@provels yeah I thought that too but I tried them one by one tonight and didn't see anything however looking closer at the rules that were opened up it all seems to be Microsoft authentication stuff and I don't run Windows.
Also I have now added a rule to the ACLs for upnp to stop low ports being opened. -
@hulleyrob Maybe it's "Steven's Phone"...
https://alltvspots.com/tag/xfinity-stevens-phone/ -
@provels haha yeah is windows phone even a thing anymore? Could be anything i suppose but I’m going to keep a more careful eye on it for a while.