New user pfsense blocking own public ip address
-
Hi i have a linux machine with local ip example: 192.168.1.45 and i set public ip using 1:1 nat and make 192.168.1.45 translate to a public ip 184.1.1.1 but when i connect to that machine i try to wget the same public ip and a specific port shows connection time out:
[root@localhost ~]# wget --no-check-certificate https://184.1.1.1:2000
Connecting to 184.1.1.1:2000... failed: Connection timed out.
Retrying.the firewall is blocking this https://184.1.1.1:2000 ?
-
Where are you checking from? The firewall itself, something else local on our network? Check from outside.. Go to can you see me . org or something..
Or fire up your phone on your cell network.
-
im testing from a linux machine connected to pfsense firewall i setup in that machine an application that runs on port 2000
-
So your checking from the machine running the service, and you want to hit the public IP and get sent back in.. That would be a nat reflection - did you set that up?
Nat reflection should really be avoided if at all possible... If you setup a port forward.. Test from outside, if your having issues from outside - then follow the troubleshooting guide
https://docs.netgate.com/pfsense/en/latest/nat/port-forward-troubleshooting.html -
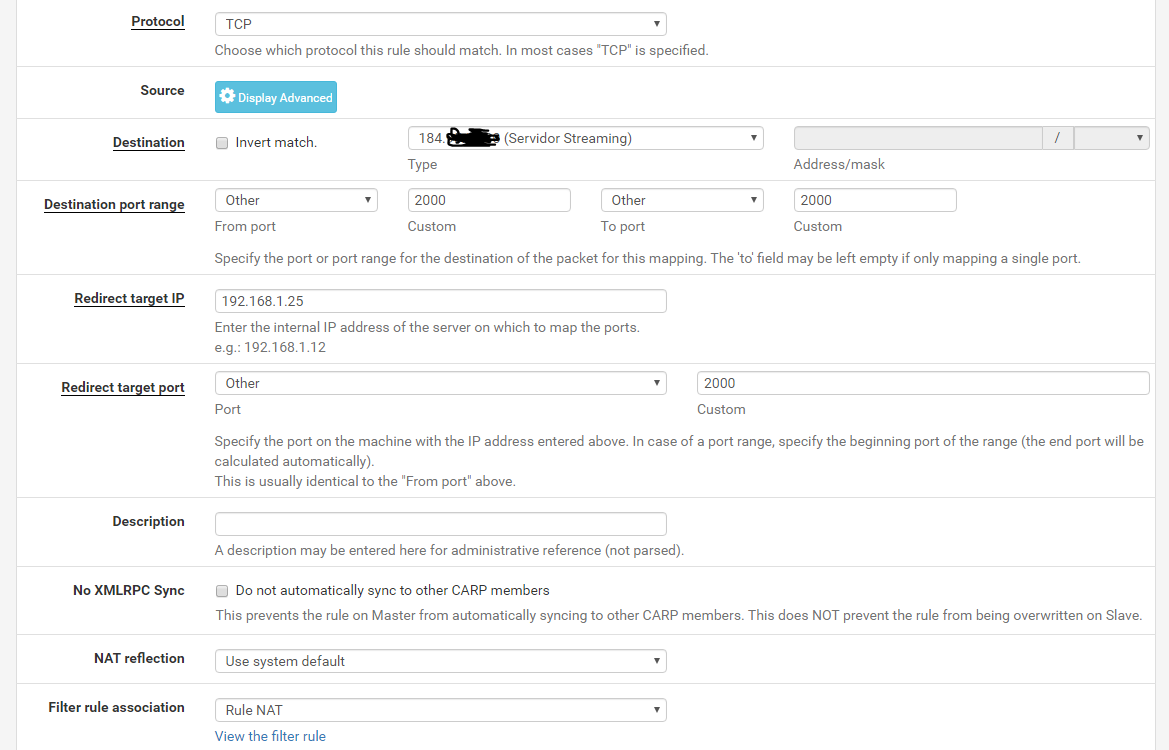
correct i set up a port forward (nat) nat reflection is set System default. Yeah from the outside works perfect, but service needs to hit the public ip itself from the same linux machine
-
-
@agaitan026 said in New user pfsense blocking own public ip address:
but service needs to hit the public ip itself from the same linux machine
Why that is just moronic!! Why would it not just talk to itself, ie loopback.
-
@johnpoz yeah i dont know why that application needs that :(
-
@johnpoz agreed, thank you so much i will talk with the developer of that application. I want to avoid nat reflection
-
@johnpoz see the answer :/ At this moment its a tough situation as the nginx configuration does need to talk to itself to proxy and cache some interfaces however using loopback/127.0.0.1 will cause a licensing error and the software does not currently have the ability to exclude parts of the software from licensing. We are working on this but currently it is required to connect to it's IP.
-
most software that checks license checks by domain etc. not IP as those can change. Not exactly sure what yours do, but checking the IP is ... a bit dumb. If it checks the domain, it's easy, just use the domain/hostname on your linux machine and put it in /etc/hosts -> et voila no more back&forth with the firewall but nginx talking with itself.
We have such stuff with hosting and NATting every day. And most licensing things we encounter are matched via the domain/URL and can be avoided that way. So just use the domain the software runs on in its configuration and also put it in the /etc/hosts if that works.