Setting up a VLAN with pfSense, Ubiquiti, and ESXi
-
@pfSenseUser78 Then I'd go with the 2nd set of rules I posted. They'll be more streamlined for your use case.
-
@marvosa Ok. In the second setup you state "Alias for DNS servers"; I'm not sure what that means. Would I be putting in the 172.x.x.x addresses or am I creating something else?
Thanks!
Edit: Ok, found where to make the alias. Trying now.
-
-
@pfSenseUser78 Edited
I first said yes, but the looked at your rules again...hold on
-
@marvosa SSH is enabled. I created the port alias but I can't figure out how to apply that to the second firewall rule. It doesn't appear in the list of ports to block.
Edit: Found it here: https://docs.netgate.com/pfsense/en/latest/book/firewall/aliases.html
Testing now!
-
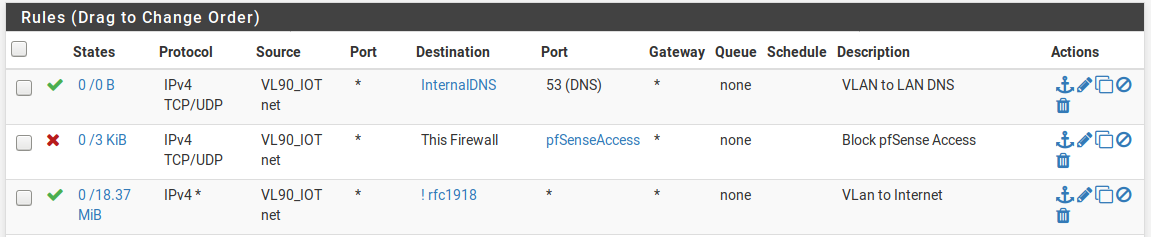
@pfSenseUser78 The last rule should be
Protocol = any
Source = VL90_IOT net
Destination = Invert match rfc1918 alias -
@marvosa Fixed.
When I join that network with my laptop I connect and get an IP. I cannot ping 8.8.8.8 or 1.0.0.1 nor can I ping the internal DNS servers (172.16.x.x). If I try to load a website nothing happens.
Not sure where I'm going wrong - is there anything else I can post that might help? I'll continue to google and see if I can find anything myself.
-
@pfSenseUser78 Port your new rules.
-
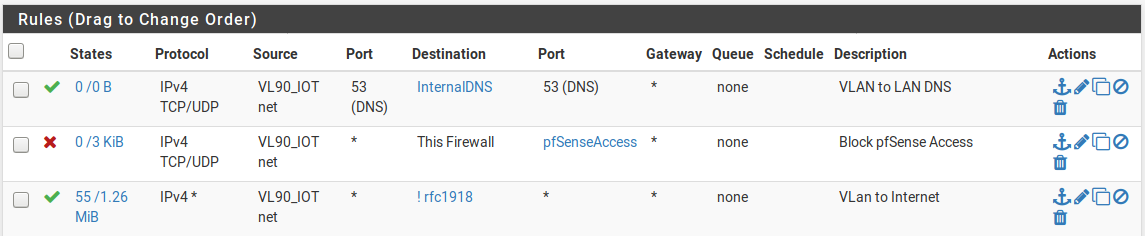
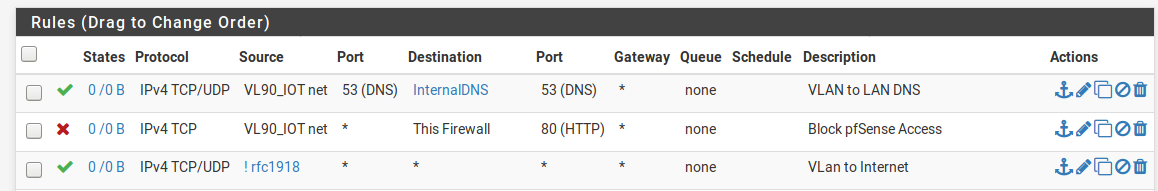
"InternalDNS" is the IP addresses of the two internal IP addresses (172.16.x.x) - devices on VLAN90 are assigned a 192.168.90.x IP address
"pfSenseAccess" is ports 20 and 80
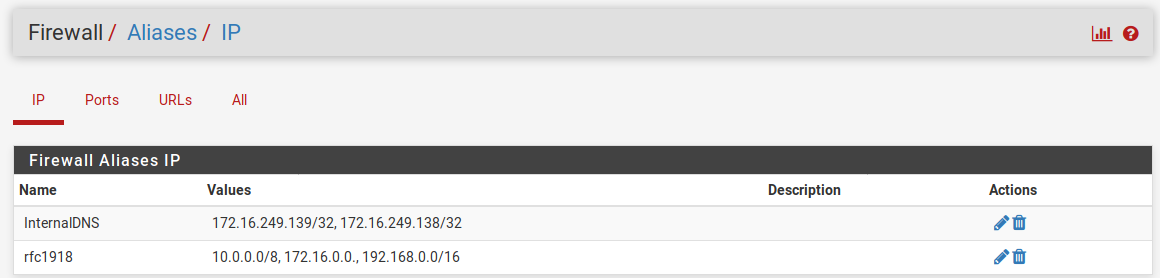
"rfc1918" is 10.0.0.0/8, 172.16.0.0., 192.168.0.0/16 -
-
@pfSenseUser78 You left off the mask on the 2nd range in your alias, but I'm guessing it was just a typo... as your rfc1918 alias should have 10.0.0.0/8, 172.16.0.0/12 and 192.168.0.0.16. Can you post a screenshot of your alias?
-
You are unable to ping your DNS server's because the DNS rule is only allowing TCP/UDP traffic destined to your DNS servers on port 53.
-
After re-examining your DNS rule, the source port should be any. Remove that 53.
Things should start working after that.
-
-
@marvosa said in Setting up a VLAN with pfSense, Ubiquiti, and ESXi:
Destination = Invert match rfc1918 alias
Awesome.
Try blocking to RFC1918 and then passing to any.
-
-
Didn't work; I can't get any website to load. NSLookup returns an error.
I have several LAN firewall rules that prevent DNS from anything other than my two internal DNS servers (that, now that I know about aliases can be condensed but that's a project for another time) - could this be causing issues?
Thanks
-
@Derelict Isn't that what I'm doing in the third rule (in one rule)?
-
Do not block traffic with pass rules. Block the traffic you want to block then pass anything else. For reasons. Either take my advice or don't. Plenty of smart people disagree with me. I despise the practice.
In your configuration, however, if all of these conditions are true:
- The VL90_IOT clients have their DNS servers set to only 172.16.249.138 and 172.16.249.139
- 172.16.249.0/24 is another interface on the firewall
- The DNS servers have the pfSense address on that interface as their default gateway
- The DNS servers at 172.16.249.138 and 172.16.249.139 can resolve names from the internet
Then the DNS servers are broken. Perhaps they themselves have a firewall or DNS server policy or configuration prohibiting them from resolving names from VL90_IOT.
From a host on VL90_IOT what is the output of this command:
dig @172.16.249.138 www.google.comIf you don't have
dig, get it. -
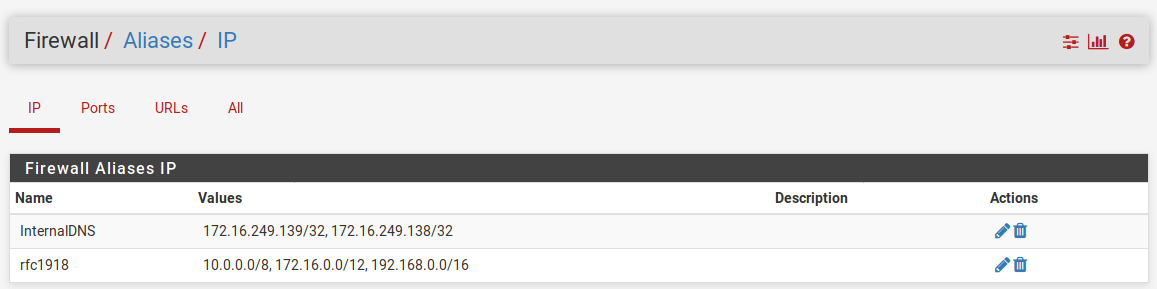
@pfSenseUser78 Ok, so the rfc1918 alias got fixed. Although, it raises the question of how the mask was left off in the first place as the system automatically adds the mask if the type is set to Network(s).
The next issue to address is DNS. If you notice, there are no hits on your DNS rule, so we need to figure out where your queries are going.
-
Assuming there are no typos in your InternalDNS alias, re-verify your clients are using 172.16.249.138 and 172.16.249.139 for DNS.
-
On your InternalDNS alias, I would change the type to Host(s) instead of Network(s). It should work out the same, but at this point, you never know.
-
Do you have Squid or anything else configured that may be intercepting DNS queries?
-
Do your browsers have DNS-over-HTTPS enabled?
-
What firewall events are you seeing during your testing?
-
-
@pfSenseUser78 said in Setting up a VLAN with pfSense, Ubiquiti, and ESXi:
Didn't work; I can't get any website to load. NSLookup returns an error.
WHAT error?
Do the hosts at least get a DHCP lease?
-
@Derelict said in Setting up a VLAN with pfSense, Ubiquiti, and ESXi:
Block the traffic you want to block then pass anything else.
While I think I am one of the ones that he is talking about disagreeing - we have had many discussions over the years about this practice ;)
While I believe you can do the ! network as an allow rule... It is more complex setup for sure, and if your unsure of everything that is going on, and understand how a vip might cause you grief here, etc. etc. It can end up being an issue.. And it is easier to make a mistake with..
So I do agree with @Derelict that explicit block(s), then allow any is the cleaner, easier to understand and less prone to issues method.. If you are having any sort of issues at all with your rules - this is the method you should utilize to get the rules working how you want..
I have removed my use of the ! rfc1918 rules and have adopted the explicit reject rfc1918 above my any as cleaner method.
-
@johnpoz said in Setting up a VLAN with pfSense, Ubiquiti, and ESXi:
I have removed my use of the ! rfc1918 rules and have adopted the explicit reject rfc1918 above my any as cleaner method.
If it saves a single rule set it's worth it.

-
This post is deleted!