Question on OpenVPN restricting IPs
-
Hello,
We have users using OpenVPN on pfsense.
I was wondering if there was a way to restrict certain users to only accessing a single IP on our network. Currently these users can access any.Thank you!
-
Depending on the amount of users in each category (needing access to anything or only a few IPs), you'd either create a second OpenVPN server instance with another dialup IP range that you can filter.
Or you can use semi-static IPs based on the client cert or username (with FreeRadius) and create a client specific override if it's only a few hosts. CSOs match the certificate and you can then define what IP in your OVPN tunnel network they should get. Of course that doesn't work well if you allow users to dial in mulitple times with the same credentials/cert package as you can only hand out a single IP. -
^^ this.
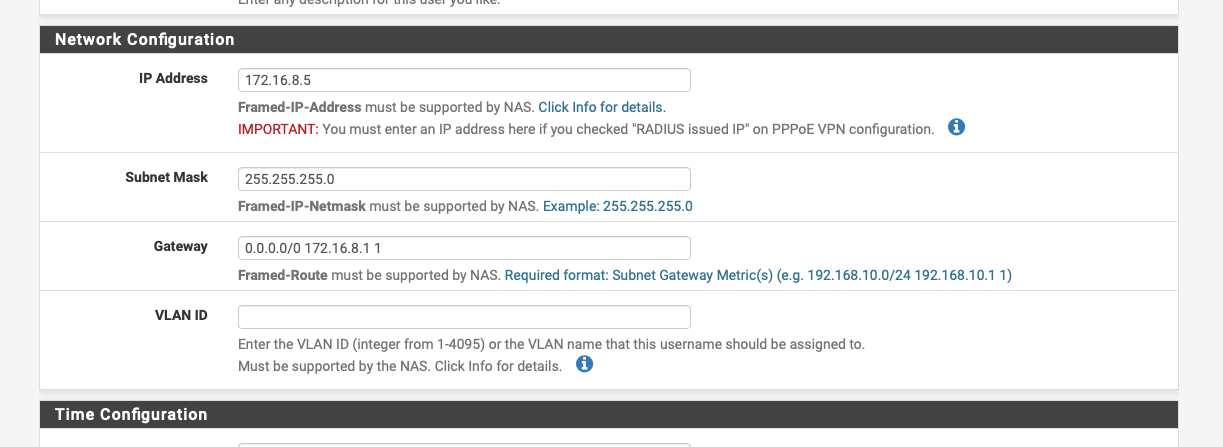
I use IPSec & Freeradius, Freeradius hands out framed-ip addresses based on username and I have firewall rules on the IPSec interface.
-
Right, if you use OpenVPN for Remote Access with FreeRadius on pfSense, you can use those IP Address and Subnet Mask fields, too. They are directly pushed to OpenVPN and the client as you dial in and spares you setting up a OVPN Client Specific Override (CSO) based on a cert. So you can even make that work for OpenVPN RAS scenarios where you only use User/Pass (without certificates) with older clients or remote/IoT devices that don't support them.
Actually that's one point why I'm propagating the use of FreeRadius together with pfSense' OpenVPN in RAS scenarios, as it's much easier to handle than creating CSOs based on the CN of certificates. Also it minimizes the probability to make configuration errors that would allow VPN users to access pfSense WebUI with their only-for-VPN user when using internal authorization.
-
@JeGr said in Question on OpenVPN restricting IPs:
Actually that's one point why I'm propagating the use of FreeRadius together with pfSense' OpenVPN in RAS scenarios, as it's much easier to handle than creating CSOs based on the CN of certificates. Also it minimizes the probability to make configuration errors that would allow VPN users to access pfSense WebUI with their only-for-VPN user when using internal authorization.
Yeah it's just a bit of a pain adding the users by hand, I did pop a redmine in for a copy function in the Freeradius package a couple of years ago.
https://redmine.pfsense.org/issues/8031