Can I use one of my 6 physical network ports to be a vpn port?
-
lol ok, I actually only bought it for it's POE conections so it is no loss but also after what you said and some googling it is not a very good/smart switch. I would prefer to create a physical port on pfsense to acheive what I am looking to do.
I am struggling with the correct terminology to find a good guide to follow, can you please recommend anything?
I did watch a video yesterday regarding policy routing the vpn connection so will check/double check and run dns leak tests!
You have been so helpful, thank you so much for your time.
-
@mbc0 said in Can I use one of my 6 physical network ports to be a vpn port?:
(TPLink TL-SG108PE)
Some TP-Link gear doesn't handle VLANs correctly. Best to avoid them, if you're planning on using VLANs.
-
Many thanks for chipping in, can I ask what is generally recommended for VLAN switches for future use please?
-
Pretty much anything other than TP-Link. I haven't heard of problems with other brands. They also have similar problems with some WiFi access points.
-
ah, ok thank you! I have a couple of standard gigabit switches which have never caused me an issue, a wireless ap which needed rebooting every day (went in the bin) so in future will avoid TP-Link, thank you
-
if your just going to use it as a dumb switch - then they should be fine... But doesn't seem like they actually understand how vlans are suppose to work ;) There are many a thread about here discussing them... I have one, which I got to test with because I couldn't believe what users were saying ;) heheheh
But they were correct - they leak vlans, they don't actually allow you to remove... Now they finally after almost a year came out with a firmware update for v3 of hardware, and recently found out (there is a thread about) where you can put the v3 firmware on the v2 hardware - and it seems to work ;)
What version (hardware) and firmware do you have of this tplink switch?
I have both the netgear and dlink low end ones as well (testing) I run cisco sg300s.. And they work fine from all the testing I have done on them.. But they just don't do all the features I want... But they are on shelf if need a switch for something - you never know ;)
-
Sadly mine is a V1.0 so I think it will just remain a dumb switch with POE :-)
I am going to attempt to see if I can work out how to get a port on my pfsense to be a VPN connection only so should be ok and not need a vlan (for now) ;-)
Thank you for taking the time to respond :-)
-
I am just following this guide from PIA
https://www.privateinternetaccess.com/forum/discussion/29231/tutorial-pia-on-pfsense-2-4
There is a section that says if you have an AES-NI it is advised to select BSD cryptodev engine but I can only see Intel RDRAND Engine? I have an i5-3470T which I bought because it has AES-NI
Thanks!
-
@mbc0 said in Can I use one of my 6 physical network ports to be a vpn port?:
Sadly mine is a V1.0 so I think it will just remain a dumb switch with POE :-)
You could do what I did with mine, I made it into a [data tap].(https://en.wikipedia.org/wiki/Network_tap)
-
@JKnott said in Can I use one of my 6 physical network ports to be a vpn port?:
@mbc0 said in Can I use one of my 6 physical network ports to be a vpn port?:
Sadly mine is a V1.0 so I think it will just remain a dumb switch with POE :-)
You could do what I did with mine, I made it into a [data tap].(https://en.wikipedia.org/wiki/Network_tap)
That looks like an interesting read! :-) Thank you!
-
Hi!
I have made good progress but have 2 questions! :-)
I have followed these instructions
https://www.privateinternetaccess.com/forum/discussion/29231/tutorial-pia-on-pfsense-2-4
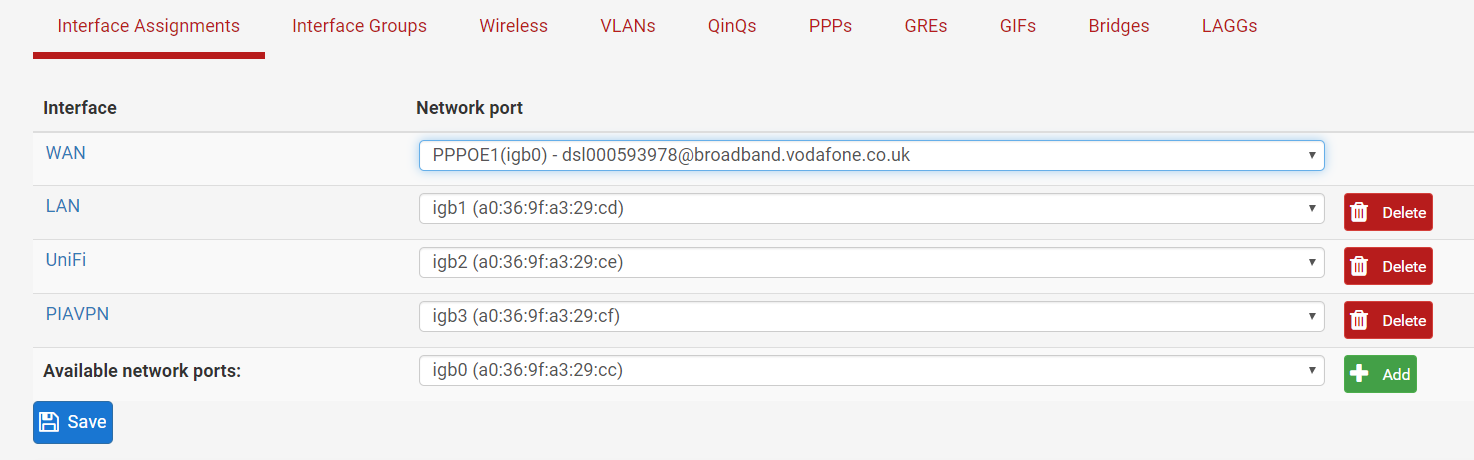
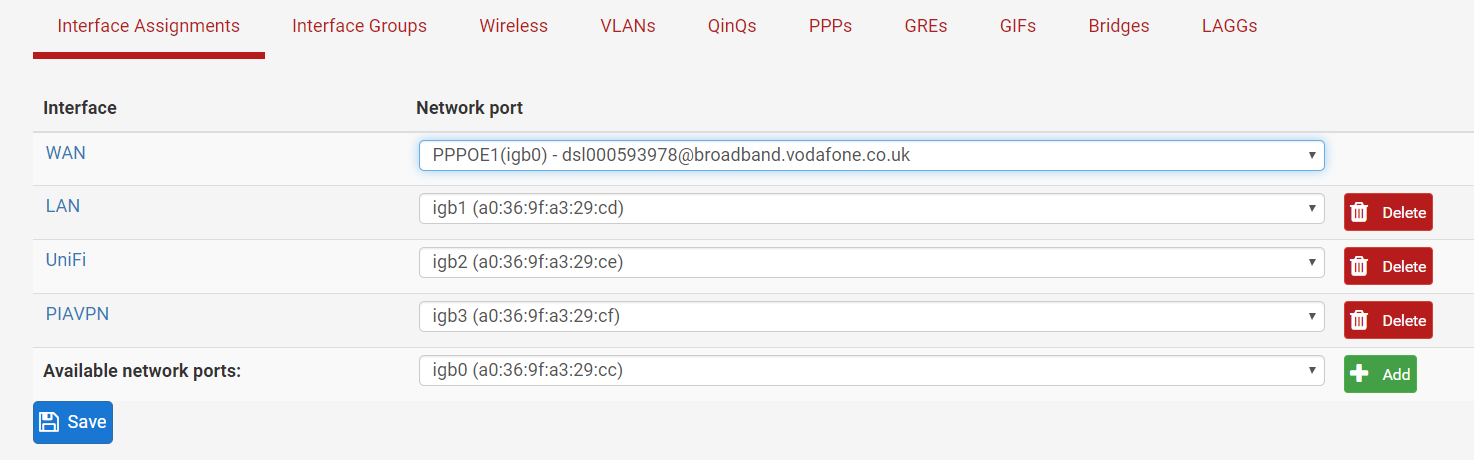
and now, my all 4 used interface ports are behind the vpn which is great that it is working but I now need to remove 3 of them so just a single port is behind the vpn in my case PIAVPN (igb3)
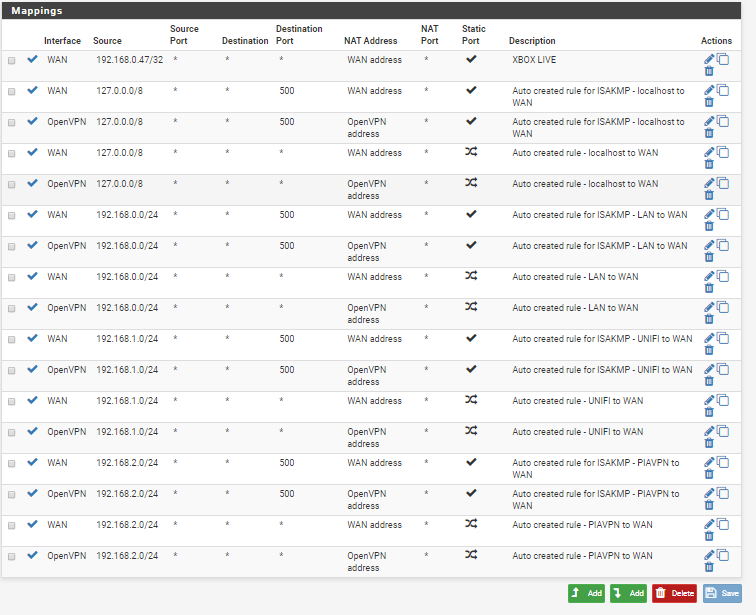
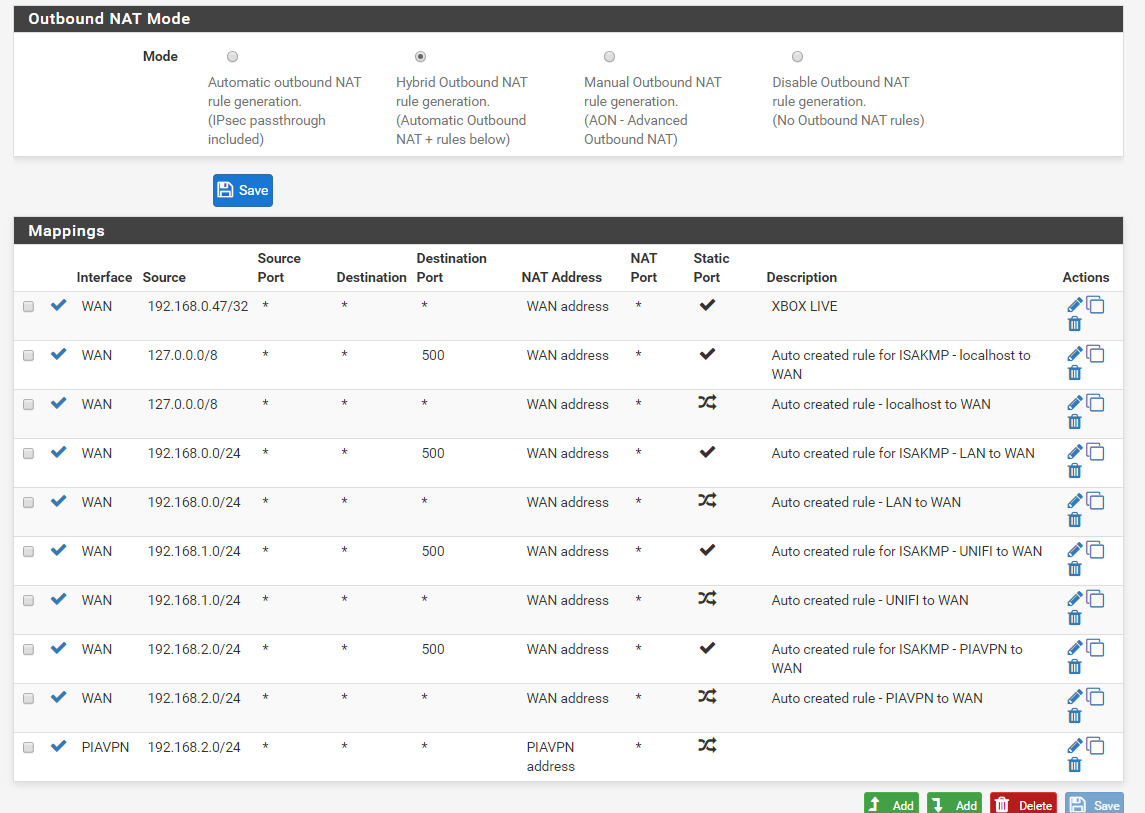
I see I had to create a new rule for each interface in Outbound nat (as per the guide) is that where I have gone wrong?
Any pointers greatly appreciated!!
Thank you
-
Well, I have googled the hell out of this and saw one guy on the forums get stroppy about it (now banned) , another that had spent 2 weeks trying to find a way but that is it? I am very sorry if this is such an easy thing to you but to someone like me it is incredibly hard to learn quickly, there is so much terminology to learn as well as understanding complex settings. If anyone has any time to just point me in the right direction of what I should be searching for or doing to resolve this I would really appreciate it!
If I go to Status/OpenVPN and start the service all interfaces then go through the VPN which is expected but I would only like 1 interface to go through the vpn (igb3)
Many Thanks :-) -
@mbc0 said in Can I use one of my 6 physical network ports to be a vpn port?:
start the service all interfaces then go through the VPN which
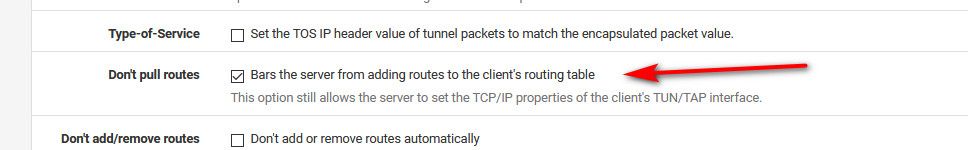
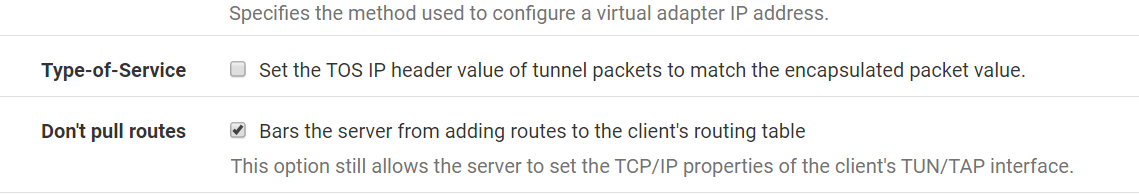
Most likely because you pulled routes when when you setup the vpn client in pfsense.. So yeah!
If you want to policy route, you can not pull routes from your vpn service because they will set your default route to go through them..
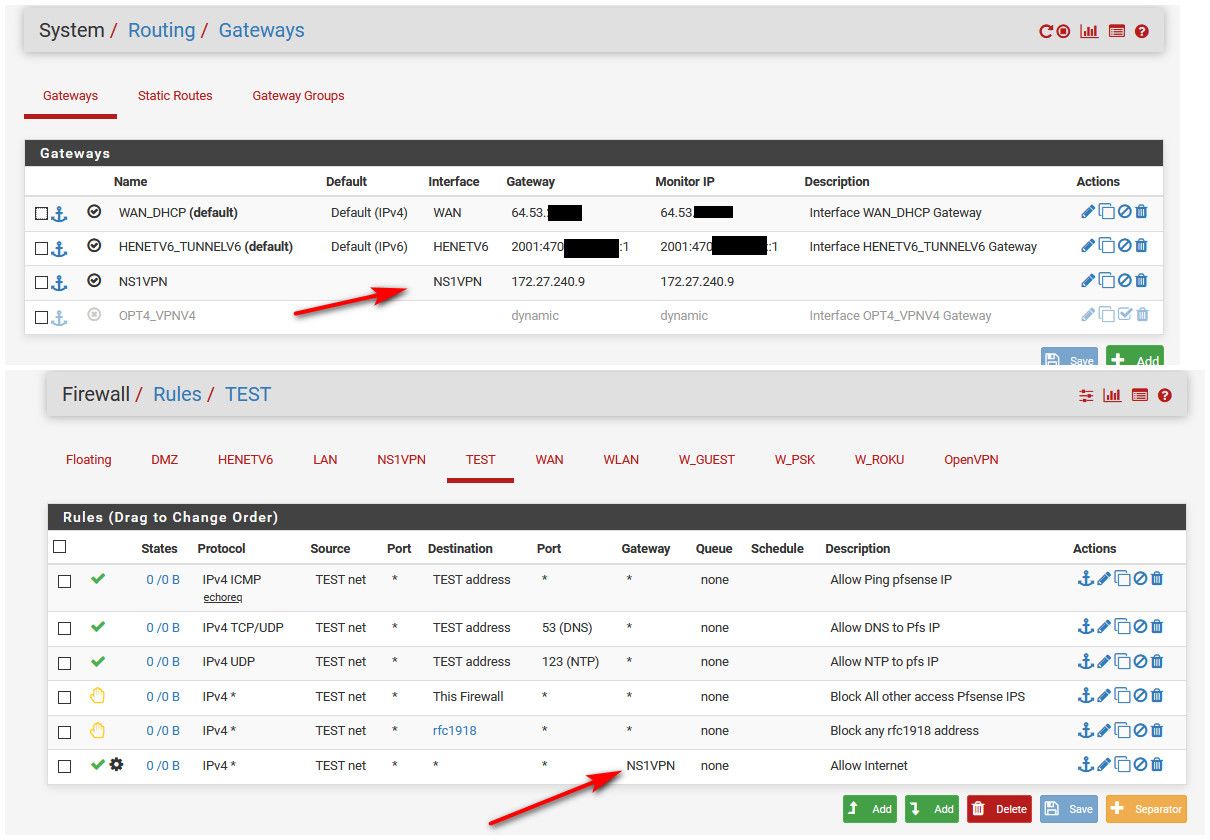
So do not pull routes! Here example setup in my vpn client setup on pfsense..
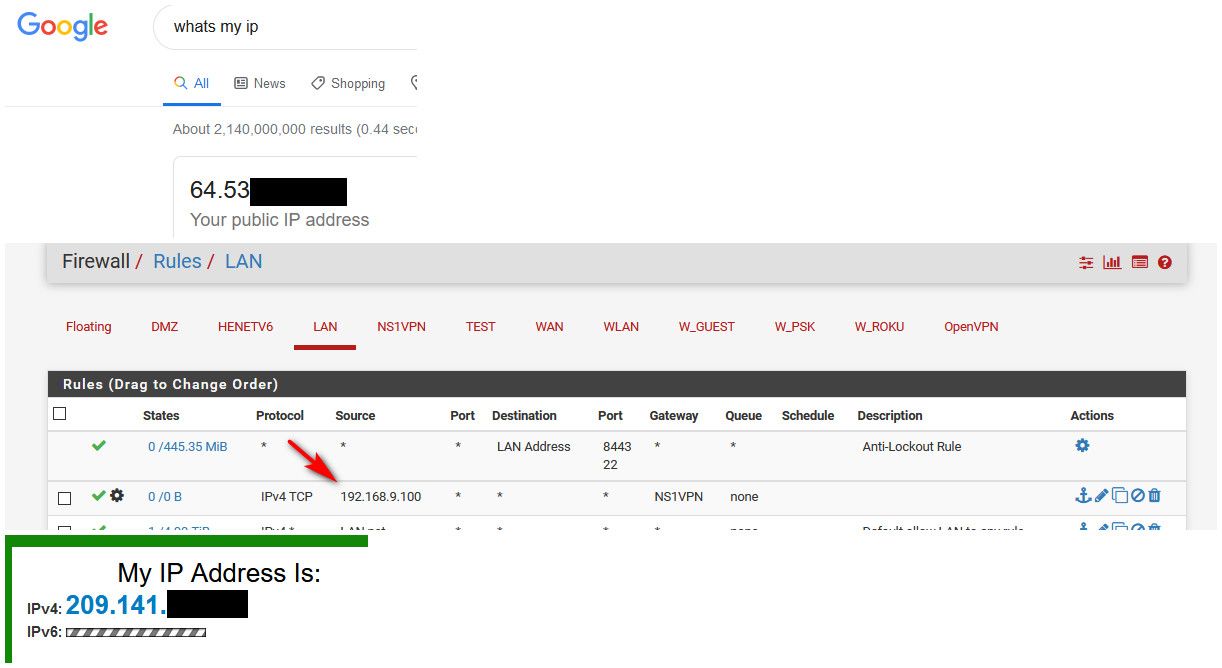
Then setup your firewall rules to go out that gateway.. example..
-
Thanks so much for this!
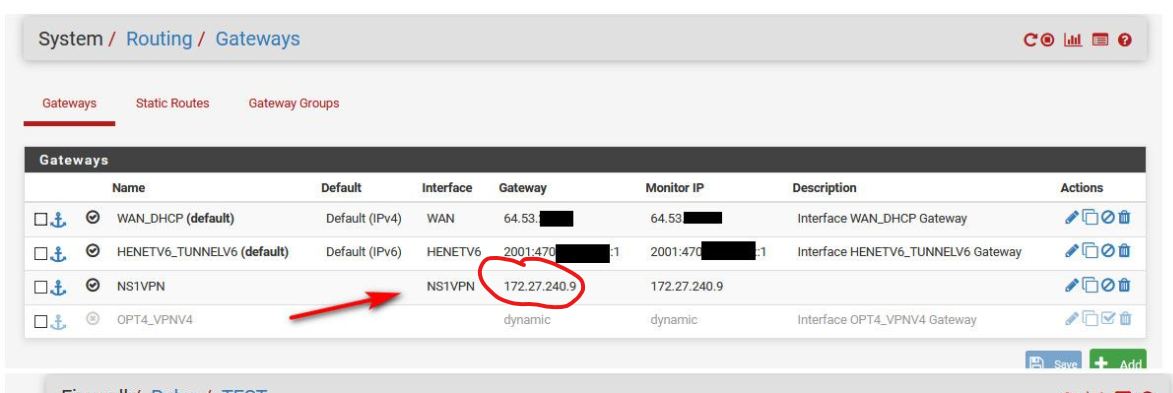
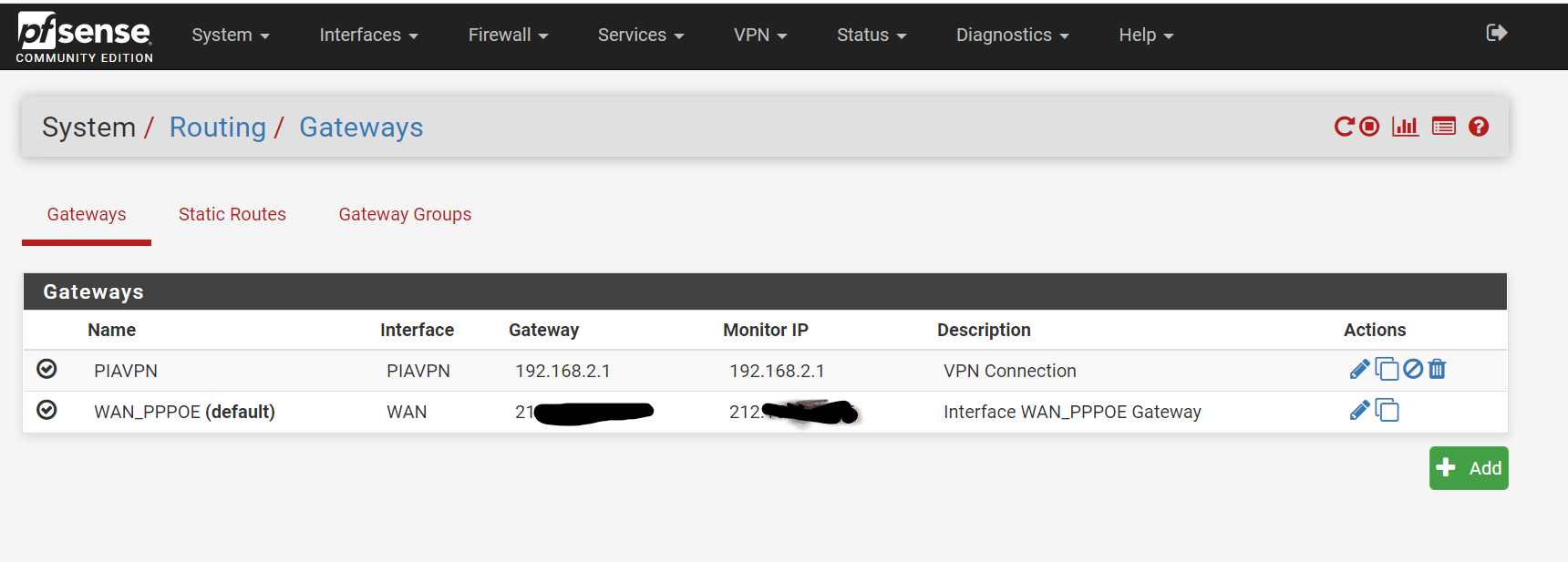
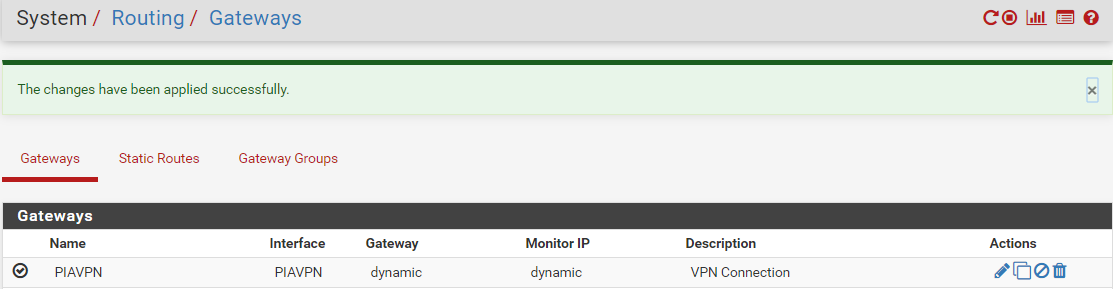
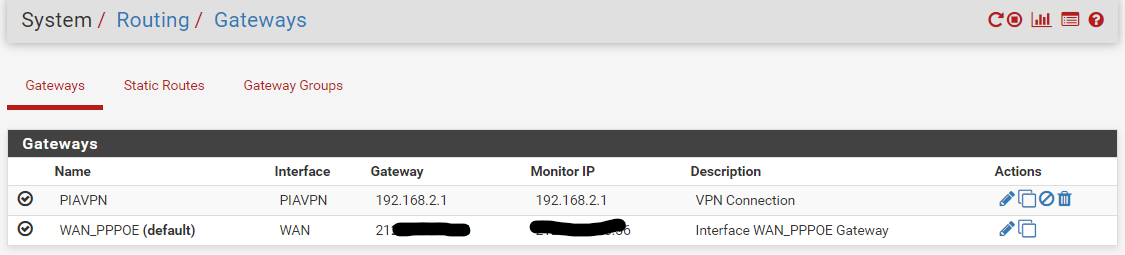
I think I must be really close now but I do not understand where you get the ip for System/Routing/Gateways?
-
@johnpoz I have tried using the ip of my interface for igb3 which is the port I want for PIA and although I can connect to the port, windows says there is internet but there actually isn't? I cannot see the outside world?
-
Your gateway is right there, its called PIAVPN - that is what you would select for the policy route, under advanced on the rule pick that as the gateway... Not the IP..
It pulls that IP from the vpn server it connects too.
Also did you switch to manual outbound nat? Yeah that is going to be problematic - you should leave it as auto, and just create a hybrid outbound nat for your vpn connection... And the tunnel network used by the vpn can not overlap any network your actually using locally.
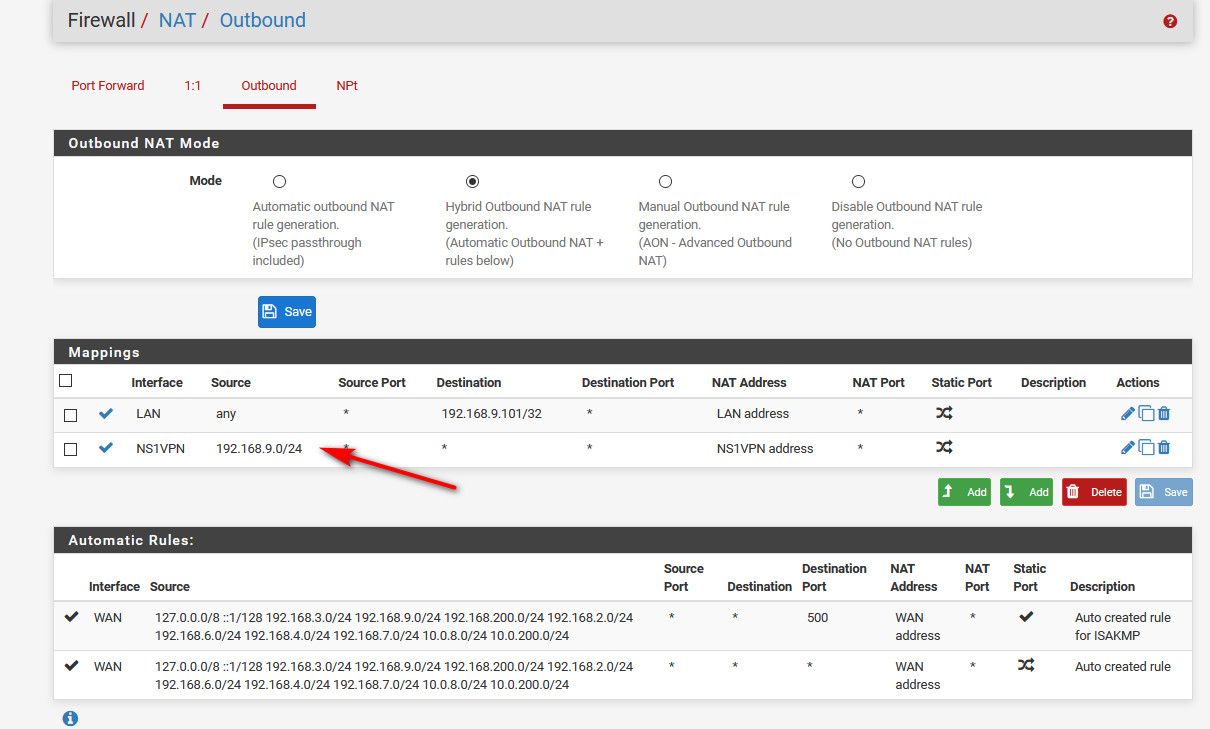
Don't pay attention to that hybrid lan nat, that is a source nat so I can get to a box without a gateway... Has nothing to do with policy routing.
-
@johnpoz said in Can I use one of my 6 physical network ports to be a vpn port?:
Also did you switch to manual outbound nat? Yeah that is going to be problematic - you should leave it as auto, and just create a hybrid outbound nat for your vpn connection
I followed the privateinternetaccess pfsense guide mentioned in post #12, here is an excerpt from it.
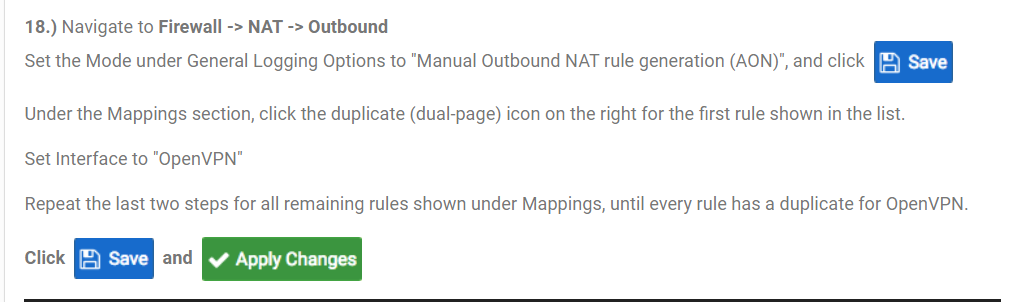
So, here is what my screens look like now
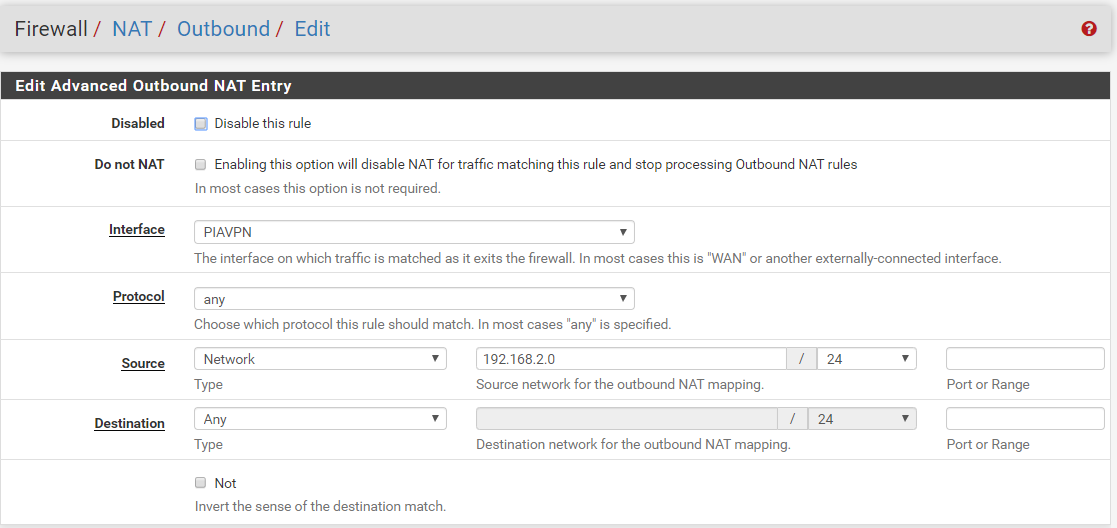
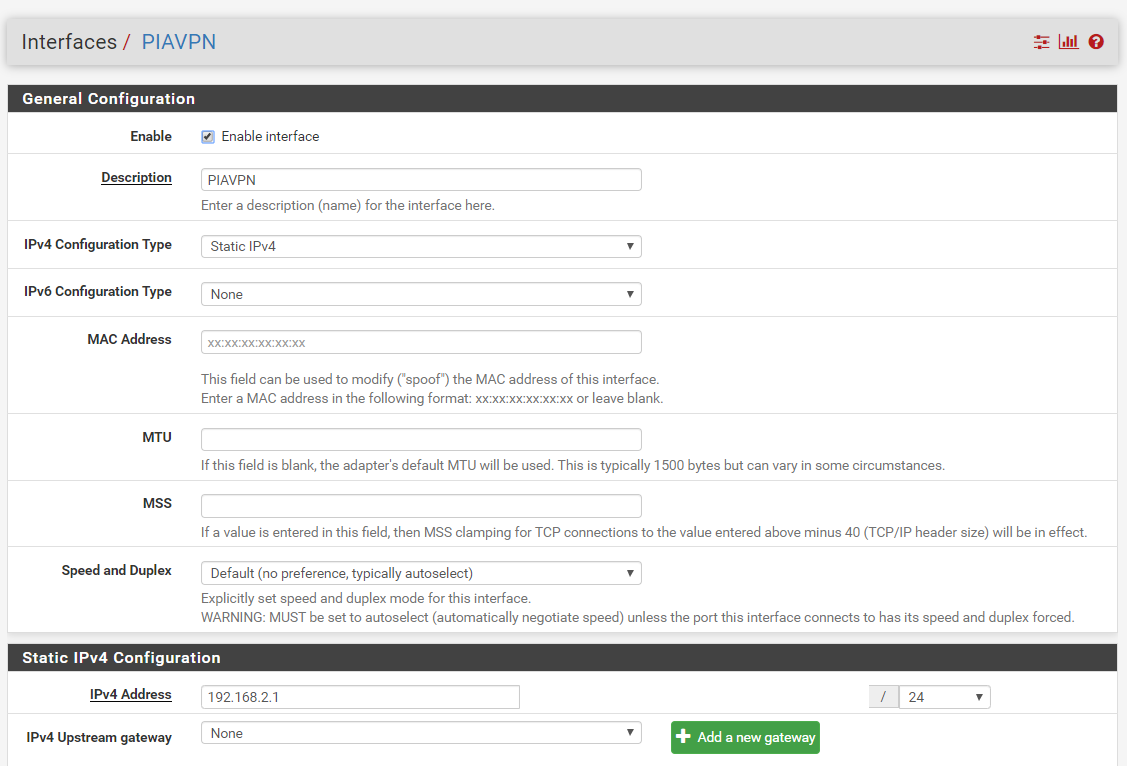
I have tried setting the ip of the source network to 192.168.2.1 as this is the ip of the interface but it automatically changes it back to 192.168.2.0
As things stand the OpenVPN PIA Service is running and connected but nothing on the LAN is running through that.
If I connect to the igb3 port on pfsense (PIAVPN) I can ping anything on the LAN but cannot connect to anything (unraid, ip cameras etc) I also cannot connect to the outside world from this port.
I think that if the instructions from pia to change to manual outbound nat is incorrect then there is probably more mis-information in that guide. Is there an alternative guide you are aware of or am I still missing something?
Many thanks for your time and patience so far, it is really appreciated!
-
@mbc0 said in Can I use one of my 6 physical network ports to be a vpn port?:
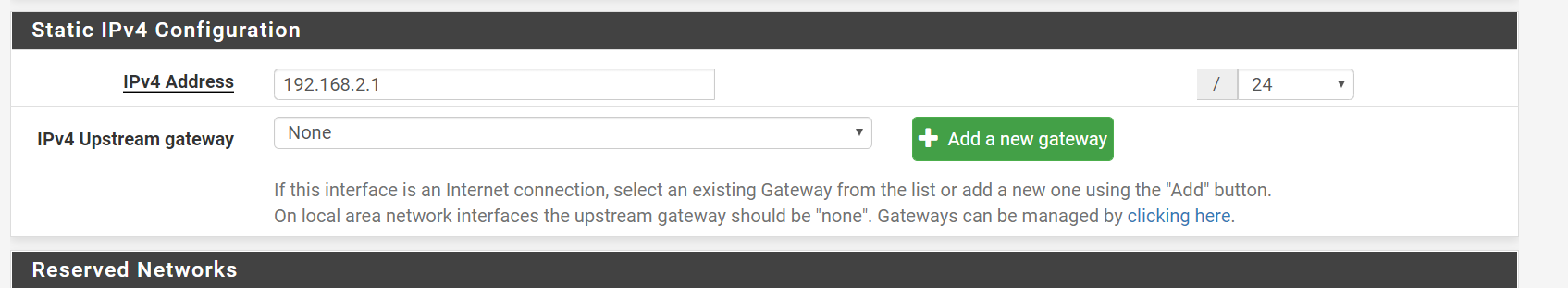
I have tried setting the ip of the source network to 192.168.2.1
Why are you trying to set an IP... You would NOT set an ip on a vpn client connect to some vpn service..
Their guides are written by idiots for their idiot users.. Sorry but that is my personal opinion of these nonsense service..
Point to me in their guide where it says to set an IP on your interface???
Lets say you where required to set a static on the interface - you still can not have the same network locally as your tunnel network.. You can not use 192.168.2/24 on one of your networks, and 192.168.2/24 as your tunnel to the vpn service..
Where is your gateway??? You manually created that gateway pointing to your own local interface on 192.168.2.1??
So you didn't follow there guide at all!! Is what your saying - your just saying you did... Because no where in there does it say to do that...
What I would suggest is just remove ALL the settings for any vpn anything... Switch to normal automatic and then get this new network working... Then setup your vpn!
-
Hi,
Firstly, I understand your frustration and I totally get it! I am an engineer of 30 years and find it very frustrating explaining things to people that just cannot understand what I am explaining. Please remember I am a complete novice trying my best to understand and follow what I thought was an official guide from PIA which has in it's defence worked for all my interfaces but I need it to work for just one interface, the guide does not cover that.
> Why are you trying to set an IP... You would NOT set an ip on a vpn client connect to some vpn service..]
I was doing this as unless I specified an IP it just stays at dynamic and does not show an IP
> Their guides are written by idiots for their idiot users.. Sorry but that is my personal opinion of these nonsense service..]
I understand your opinion :-)
> Point to me in their guide where it says to set an IP on your interface???
It does not say this anywhere in the guide as their guide is only to put all interfaces behind the vpn which as I previously stated works, I cannot find any guide or understand any way to do this for just one interface.
> Lets say you where required to set a static on the interface - you still can not have the same network locally as your tunnel network.. You can not use 192.168.2/24 on one of your networks, and 192.168.2/24 as your tunnel to the vpn service..
I am so sorry I am not fully understanding this, I have 4 interfaces in use
wan
lan - I set an IP of 192.168.0.10
Unifi - I set an IP of 192.168.1.5
PIAVPN - I set an IP of 192.168.2.1> Where is your gateway??? You manually created that gateway pointing to your own local interface on 192.168.2.1??
So you didn't follow there guide at all!! Is what your saying - your just saying you did... Because no where in there does it say to do that...
Yes I did follow the guide completely and it worked perfectly but for all interfaces, I need this to be on just one interface.
What I would suggest is just remove ALL the settings for any vpn anything... Switch to normal automatic and then get this new network working... Then setup your vpn!
I have had this interface working fine the whole time and have been using it for some months before trying to get OpenVPN working.
In a nutshell
All interfaces have been working fine for some time now.
I followed the PIA Guide and all worked great for all interfaces then the problem is trying to get it to work just on one interface.Again, I really am genuinly sorry as I know how frustrating this must be.
Thanks
-
Dude... You can do this with 1 interface, 100 interfaces... Doesn't matter its a simple policy route... You have gateway that is the vpn connection... creat a rule that sends who you want when they want go X out the gateway... its that freaking simple..
All that is required for you to do this, is follow their stupid guide and don't pull the routes. Then nobody will be using the vpn
Other than their nonsense about deleting your wan outbound nats as their kill switch.. OMG!!!
Now create a rule that points either the whole network or a specific IP out the gateway...
That is ALL there is too it... Have you read the policy routing documentation?
https://docs.netgate.com/pfsense/en/latest/routing/directing-traffic-with-policy-routing.html
edit: Here... I just created a firewall rule to point my client out the vpn.. Its as simple as changing the gateway from default to the vpn.. That is all there is too it... When you pull the routes, they change your DEFAULT to use the vpn... For anything to no use the vpn you would have to force it out your wan gateway..
Reason the other site for IP is different, is I didn't want to flush my states, so I went somewhere different (not google) to create a new state on the firewall and use the vpn connection, vs the previous states that were using my wan.