Suricata not showing on menu after update to 5.0.2 or 5.0.2_1
-
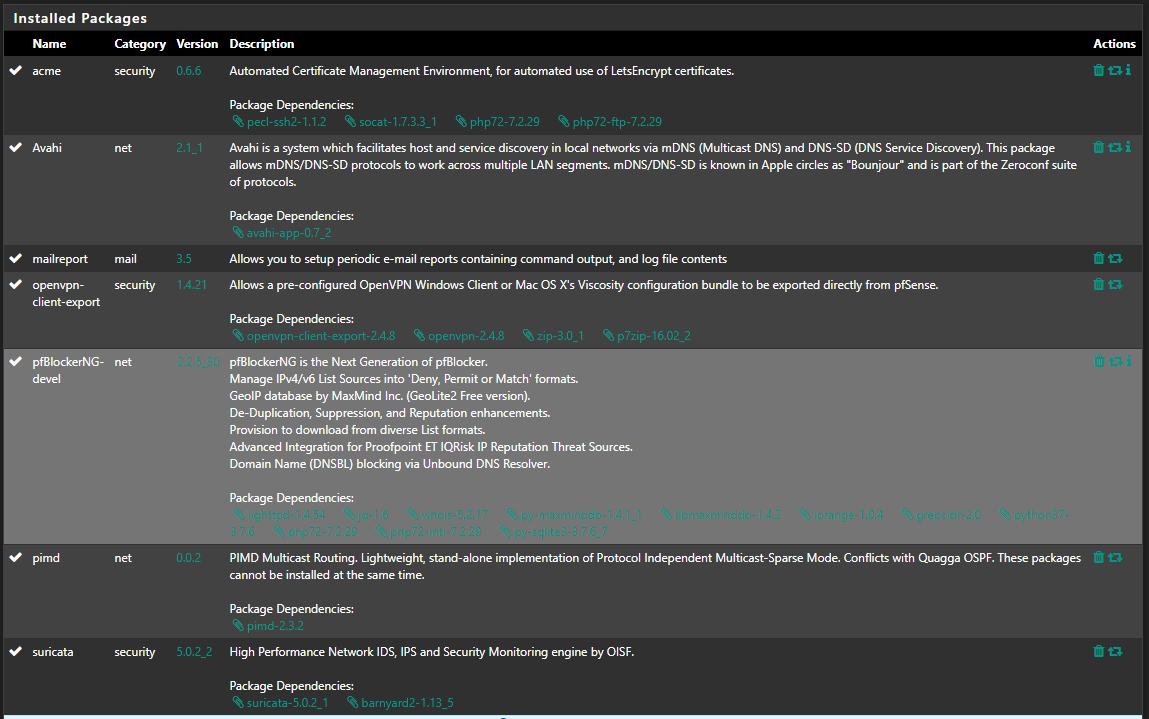
My upgrade to 2.4.5 went fine as did the original installation of Suricata 5.0.1. On Saturday I upgrade to 5.0.2 and found that the menu item had been removed and not installed. I tried reinstalling from packages, I also tried to do a complete removal and then a install again, nothing would bring it back. I am able to view the interface by going to: https://firewall/suricata/suricata_interfaces.php. I also note that the widget on the home page is gone. I then restored configuration from where the firewall was before I upgraded the package. This caused the menu option to show back up. Today, I loaded 5.0.2_1 and found the same problem again. I reviewed the config.xml and don't see anything out of the ordinary. When I compare the config before the install to now, I do see the menu item being removed. Here is the output of differences:
<sequence>system_information:col1:open:0,interfaces:col2:open:0,smart_status:col2:open:0,dyn_dns_status:col2:open:0,services_status:col2:open:0,gateways:col2:open:0,suricata_alerts:col2:open:0,ntp_status:col2:open:0,pfblockerng:col2:show</sequence> + <sequence>system_information:col1:open:0,interfaces:col2:open:0,smart_status:col2:open:0,dyn_dns_status:col2:open:0,services_status:col2:open:0,gateways:col2:open:0,ntp_status:col2:open:0,pfblockerng:col2:show</sequence> </widgets> <openvpn> <openvpn-server> @@ -3100,9 +3100,9 @@ <regdhcpstatic></regdhcpstatic> </unbound> <revision> - <time>1586200417</time> - <description><![CDATA[admin@10.0.0.206 (Local Database): Creating restore point before package installation.]]></description> - <username><![CDATA[admin@10.0.0.206 (Local Database)]]></username> + <time>1586200448</time> + <description><![CDATA[(system): Installed cron job for /usr/bin/nice -n20 /sbin/pfctl -q -t snort2c -T expire 3600]]></description> + <username><![CDATA[(system)]]></username> </revision> <cert> <refid>57d39949396e6</refid> @@ -3507,7 +3507,7 @@ <name>suricata</name> <website>http://suricata-ids.org/</website> <descr><![CDATA[High Performance Network IDS, IPS and Security Monitoring engine by OISF.]]></descr> - <version>5.0.2</version> + <version>5.0.2_2</version> <configurationfile>suricata.xml</configurationfile> </package> <acme> @@ -3595,12 +3595,6 @@ <description><![CDATA[PIMD multicast routing daemon]]></description> </service> <service> - <name>suricata</name> - <rcfile>suricata.sh</rcfile> - <executable>suricata</executable> - <description><![CDATA[Suricata IDS/IPS Daemon]]></description> - </service> - <service> <name>pfb_dnsbl</name> <rcfile>pfb_dnsbl.sh</rcfile> <executable>lighttpd_pfb</executable> @@ -3631,12 +3625,6 @@ <url>/status_mail_report.php</url> </menu> <menu> - <name>Suricata</name> - <tooltiptext>Configure Suricata settings</tooltiptext> - <section>Services</section> - <url>/suricata/suricata_interfaces.php</url> - </menu> - <menu> <name>pfBlockerNG</name> <section>Firewall</section> <url>/pfblockerng/pfblockerng_general.php</url> @@ -4736,6 +4724,7 @@ <sid_changes_log_limit_size>250</sid_changes_log_limit_size> <sid_changes_log_retention>336</sid_changes_log_retention> <auto_manage_sids>on</auto_manage_sids> + <dashboard_widget>suricata_alerts:col2:open:0</dashboard_widget> </config> <sid_mgmt_lists> <item>Here is the log from doing a fresh install as well:
>>> Installing pfSense-pkg-suricata... Updating pfSense-core repository catalogue... pfSense-core repository is up to date. Updating pfSense repository catalogue... pfSense repository is up to date. All repositories are up to date. Checking integrity... done (0 conflicting) The following 17 package(s) will be affected (of 0 checked): New packages to be INSTALLED: pfSense-pkg-suricata: 5.0.2_2 [pfSense] suricata: 5.0.2_1 [pfSense] libyaml: 0.2.2 [pfSense] nss: 3.51 [pfSense] nspr: 4.25 [pfSense] cyrus-sasl: 2.1.27 [pfSense] libpcap: 1.9.1_1 [pfSense] libnet: 1.1.6_5,1 [pfSense] py37-yaml: 5.2 [pfSense] jansson: 2.12 [pfSense] hyperscan: 4.7.0_3 [pfSense] hiredis: 0.13.3 [pfSense] barnyard2: 1.13_5 [pfSense] broccoli: 1.101,1 [pfSense] python27: 2.7.17_1 [pfSense] mysql57-client: 5.7.29 [pfSense] protobuf: 3.9.2,1 [pfSense] Number of packages to be installed: 17 The process will require 180 MiB more space. [1/17] Installing nspr-4.25... [1/17] Extracting nspr-4.25: .......... done [2/17] Installing cyrus-sasl-2.1.27... *** Updated user `cyrus'. [2/17] Extracting cyrus-sasl-2.1.27: .......... done [3/17] Installing python27-2.7.17_1... [3/17] Extracting python27-2.7.17_1: .......... done [4/17] Installing protobuf-3.9.2,1... [4/17] Extracting protobuf-3.9.2,1: .......... done [5/17] Installing libyaml-0.2.2... [5/17] Extracting libyaml-0.2.2: ......... done [6/17] Installing nss-3.51... [6/17] Extracting nss-3.51: .......... done [7/17] Installing libpcap-1.9.1_1... [7/17] Extracting libpcap-1.9.1_1: .......... done [8/17] Installing libnet-1.1.6_5,1... [8/17] Extracting libnet-1.1.6_5,1: .......... done [9/17] Installing py37-yaml-5.2... [9/17] Extracting py37-yaml-5.2: .......... done [10/17] Installing jansson-2.12... [10/17] Extracting jansson-2.12: .......... done [11/17] Installing hyperscan-4.7.0_3... [11/17] Extracting hyperscan-4.7.0_3: .......... done [12/17] Installing hiredis-0.13.3... [12/17] Extracting hiredis-0.13.3: .......... done [13/17] Installing broccoli-1.101,1... [13/17] Extracting broccoli-1.101,1: .......... done [14/17] Installing mysql57-client-5.7.29... [14/17] Extracting mysql57-client-5.7.29: .......... done [15/17] Installing suricata-5.0.2_1... [15/17] Extracting suricata-5.0.2_1: .......... done [16/17] Installing barnyard2-1.13_5... [16/17] Extracting barnyard2-1.13_5: ...... done [17/17] Installing pfSense-pkg-suricata-5.0.2_2... [17/17] Extracting pfSense-pkg-suricata-5.0.2_2: .......... done Saving updated package information... done. Loading package configuration... done. Configuring package components... Loading package instructions... Custom commands... Executing custom_php_install_command()...===== Message from cyrus-sasl-2.1.27: -- You can use sasldb2 for authentication, to add users use: saslpasswd2 -c username If you want to enable SMTP AUTH with the system Sendmail, read Sendmail.README NOTE: This port has been compiled with a default pwcheck_method of auxprop. If you want to authenticate your user by /etc/passwd, PAM or LDAP, install ports/security/cyrus-sasl2-saslauthd and set sasl_pwcheck_method to saslauthd after installing the Cyrus-IMAPd 2.X port. You should also check the /usr/local/lib/sasl2/*.conf files for the correct pwcheck_method. If you want to use GSSAPI mechanism, install ports/security/cyrus-sasl2-gssapi. If you want to use SRP mechanism, install ports/security/cyrus-sasl2-srp. If you want to use LDAP auxprop plugin, install ports/security/cyrus-sasl2-ldapdb. ===== Message from python27-2.7.17_1: -- Note that some standard Python modules are provided as separate ports as they require additional dependencies. They are available as: bsddb databases/py-bsddb gdbm databases/py-gdbm sqlite3 databases/py-sqlite3 tkinter x11-toolkits/py-tkinter -- ===> NOTICE: This port is deprecated; you may wish to reconsider installing it: EOLed upstream. It is scheduled to be removed on or after 2020-12-31. ===== Message from mysql57-client-5.7.29: -- This is the mysql CLIENT without the server. for complete server and client, please install databases/mysql57-server ===== Message from suricata-5.0.2_1: -- If you want to run Suricata in IDS mode, add to /etc/rc.conf: suricata_enable="YES" suricata_interface="<if>" NOTE: Declaring suricata_interface is MANDATORY for Suricata in IDS Mode. However, if you want to run Suricata in Inline IPS Mode in divert(4) mode, add to /etc/rc.conf: suricata_enable="YES" suricata_divertport="8000" NOTE: Suricata won't start in IDS mode without an interface configured. Therefore if you omit suricata_interface from rc.conf, FreeBSD's rc.d/suricata will automatically try to start Suricata in IPS Mode (on divert port 8000, by default). Alternatively, if you want to run Suricata in Inline IPS Mode in high-speed netmap(4) mode, add to /etc/rc.conf: suricata_enable="YES" suricata_netmap="YES" NOTE: Suricata requires additional interface settings in the configuration file to run in netmap(4) mode. RULES: Suricata IDS/IPS Engine comes without rules by default. You should add rules by yourself and set an updating strategy. To do so, please visit: http://www.openinfosecfoundation.org/documentation/rules.html http://www.openinfosecfoundation.org/documentation/emerging-threats.html You may want to try BPF in zerocopy mode to test performance improvements: sysctl -w net.bpf.zerocopy_enable=1 Don't forget to add net.bpf.zerocopy_enable=1 to /etc/sysctl.conf ===== Message from barnyard2-1.13_5: -- Read the notes in the barnyard2.conf file for how to configure /usr/local/etc/barnyard2.conf after installation. For addtional information see the Securixlive FAQ at http://www.securixlive.com/barnyard2/faq.php. In order to enable barnyard2 to start on boot, you must edit /etc/rc.conf with the appropriate flags, etc. See the FreeBSD Handbook for syntax: http://www.freebsd.org/doc/en_US.ISO8859-1/books/handbook/configtuning-rcng.html For the various options available, type % barnyard2 -h after install or read the options in the startup script - in /usr/local/etc/rc.d. Barnyard2 can process unified2 files from snort or suricata. It can also interact with snortsam firewall rules as well as the sguil-sensor. Those ports must be installed separately if you wish to use them. >>> Cleaning up cache... done. SuccessPackage output as well:
Any thoughts?
Thanks so much,
Craig
-
Forgot to include system log:
Apr 6 15:36:28 php /etc/rc.packages: Beginning package installation for suricata . Apr 6 15:36:28 check_reload_status Syncing firewall Apr 6 15:36:28 php /etc/rc.packages: Beginning configuration backup to https://acb.netgate.com/save Apr 6 15:36:31 php /etc/rc.packages: End of configuration backup to https://acb.netgate.com/save (success). Apr 6 15:36:31 php [Suricata] Installing free GeoLite2 country IP database file in /usr/local/share/suricata/GeoLite2/... Apr 6 15:36:31 php [Suricata] Checking for updated MaxMind GeoLite2 IP database file... Apr 6 15:36:31 php [Suricata] ALERT: The Account ID or License Key for MaxMind GeoLite2 is invalid. Apr 6 15:36:31 php [Suricata] ERROR: GeoLite2-Country IP database update check failed. The GeoIP database was not updated! Apr 6 15:36:32 pkg-static pfSense-pkg-suricata-5.0.2_2 installed -
Your GeoIP database installation is failing. Look at the last log snippet you posted from the system log.
Most likely you do not have a proper MaxMind GeoIP license key. Starting a few releases back this became mandatory if you enabled GeoIP database downloads.
You either need to get a proper MaxMind key or else disable that option. To disable, browse to https://firewall/suricata/suricata_global.php and uncheck the GeoIP box. Or else obtain a proper MaxMind license key and type in the license key. Save the change.
Then remove the package and try installing it again. It's not showing up in the menu because either the install is not completing and/or you are navigating away from the installation screen too soon. Make sure you stay on that page until you see the "success" text in green font. One of the last things that happens right before that green "success" is printed is the final pieces of package installation data are written to the
config.xmlfile. If that process is interrupted by say navigating away from the package installation screen too early, then the keys that show the package fully installed (and thus available on the SERVICES menu) do not get written and saved. -
@bmeeks Thank you so much. That worked perfectly. I saw it failing but falsely assumed that the install would continue, especially when the package screen said it was successful.
Thanks again!