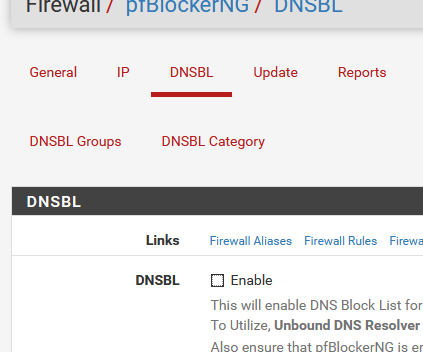
Bypassing DNSBL for specific IPs
-
This is really strange....
- If I remove the leading spaces, I cannot save the config
The following input errors were detected: The generated config file cannot be parsed by unbound. Please correct the following errors: [1586258288] unbound-checkconf[11766:0] error: local-data in redirect zone must reside at top of zone, not at zz.zeroredirect1.com 60 IN A 10.10.10.1 [1586258288] unbound-checkconf[11766:0] fatal error: Could not set up views- I had removed the leading "server:" in front of the last line to look like this:
include: /var/unbound/pfb_dnsbl.*confBut every time I login to pfsense and try to modify the unbound settings, it is back to this:
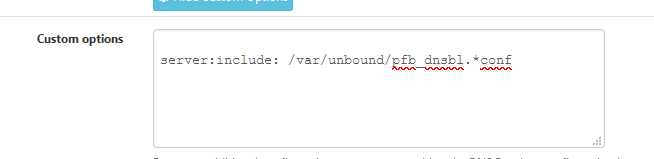
server:include: /var/unbound/pfb_dnsbl.*confIs the package pfblockerNG doing this???
-
@pftdm007 said in Bypassing DNSBL for specific IPs:
Is the package pfblockerNG doing this???
Yep.
You know now how pfBlockerNG-devel communicates the list with IPs to be blocked to unbound ^^Before you install, the custom options box (unbound) is empty :
When you dissable pfBlockerNG-debel, and re activate it :
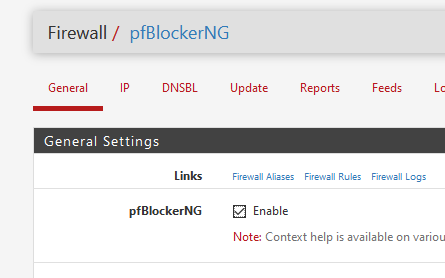
it will add this line to the custom options (unbound) :
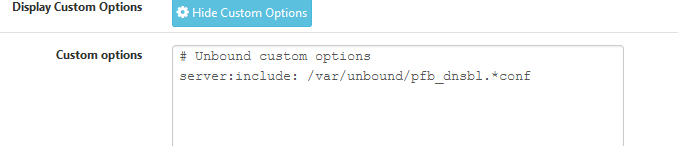
The first time you installed pfBockerng-devel, there was even a first comment line :
-
Okayyyy... but...? That doesnt explain why the custom options with views dont work (and dont work if I remove the leading spaces), and how to prevent pfblockerNG from adding the redundant "server:" statement in front of the line....
Others in this thread have successfully used views while using pfblockerNG so there's something I am doing wrong...
-
Which version of pfBlockerNG is installed?
Although I did upgrade mine last night to -deval 2.2.5_30 and quickly ran the same test and it still works fine.Note: upgrading, installing, disabling / enabling etc. will always add the "server:" prefix to the include line. I just have a note to always check and remove it. Am not aware of any workaround.
Based on your error there is another thread from 2016
DNS Resolver cannot be modified or changedSeems to be something regarding the System Domain Local Zone type setting. Mine is Transparent which seems to be OK and allows me to save the config and views do work. If its not this, there must be something else, so will need a little more info on your setup and config.
i.e. Do you have IPv6 configured? That will change a number of things that need additional configuration.
-
@pftdm007 said in Bypassing DNSBL for specific IPs:
and how to prevent pfblockerNG from adding the redundant "server:" statement in front of the line....
Well ...
Have a keyboard ?
Here it is :/usr/local/pkg/pfblockerng/pfblockerng.inc line 1289
$unbound_include = "server:include: {$pfb['dnsbl_file']}.*conf";Take note : this line is still added at the end of the unbound config file. No analyses is done for Custom options already present.
When pfBlockerng installs, or when you re-enable DNSBL mode, that line is added. -
@Gertjan
Nice!Keyboards still rule!, As "Alexa, please make change to pfSense /usr/local . . . . @ line 1289" just isn't going to hack it anytime soon :-)
-
I really wouldn't ask Alexa to do this ......
Anyway, I tried it myself.Disabled :
and forced a Update > Reload >All.
My Unbound > Custom options box is now empty.
I added a single (needed !) line :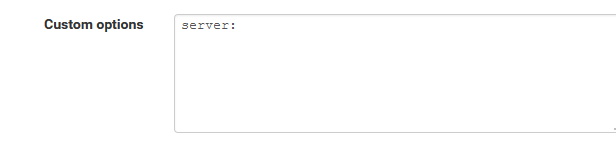
I edited the file mentioned above.
And activated DNSBL in pfBlokcerNG again :The result :
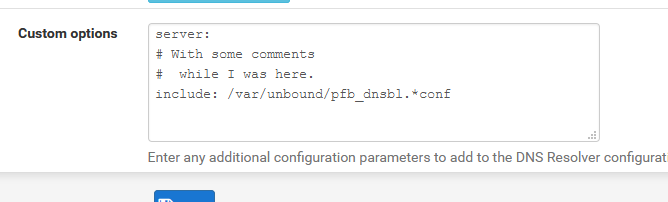
$unbound_include = "# With some comments\n# while I was here.\n include: {$pfb['dnsbl_file']}.*conf"; -
@horse2370 : pfBlockerNG-devel v2.2.5_30 is installed on my system. Seems to be the latest one. Also the thread you referred me to, seems to be a bug in Unbound or its implementation in pfsense? Still unfixed? The thread ends up dead with no answer.
If "upgrading, installing, disabling / enabling etc." will always put the "server:" statement back in unbound's custom options, then to me, pfBlockerNG's devs never intended their package to work with Unbound views. This is highly confirmed by @Gertjan's workaround to manually edit "/usr/local/pkg/pfblockerng/pfblockerng.inc"...
IMO, and this is only personal opinion, we should never have to fiddle with internal files like this way, even if it works. Especially on production systems. Will this file be overwritten once pfblockerNG is updated?
At least now I start to have a better picture on how these components interact with each others....
-
Just saw the last line of your post... No, I do not use IPV6 at all. Pretty much everything else is stock, with the exception of pfblockerNG and Snort. I also use VLAN's. Could you specify which setting you need more specifically? I will be glad to provide!
EDIT: some Unbound settings
Port 53
Enable SSL/TLS: Unchecked
SSL/TLS Cert: stock setting
Network ifaces: VLANs (see my initial post on this thread for details)
Outgoing ifaces: WAN
System Domain Local Zone Type: Transparent
DNSSEC: Checked
Python Module: Unchecked
DNS query FW: Unchecked
DHCP Registrations: Checked
Static DHCP: Checked
OpenVPN : Unchecked
Custom Options: (see my initial post on this thread for details) -
@pftdm007 said in Bypassing DNSBL for specific IPs:
Will this file be overwritten once pfblockerNG is updated?
It's part of the package - so a re install or upgrade will undo changes.
Or, before editing, make a copy of it.@pftdm007 said in Bypassing DNSBL for specific IPs:
pfBlockerNG's devs never intended their package to work with Unbound views.
It's just a way to have unbound to include a file with IP's - the scope is just 'server' (unbound dns) wide.
Btw : in my case, this file is empty, I'm not using DNSBL part of pfBlockerNG-devel - so it'a a no-op for me.
I could even wipe this line in the custom options.
( but shouldn't be surprised the DNDBL functionality wouldn't work anymore ) -
Does the order in which you put the networks in the custom configs make any difference? Like would
access-control-view: 192.168.2.0/24 bypass access-control-view: 192.168.1.0/24 dnsblbe any different than
access-control-view: 192.168.1.0/24 dnsbl access-control-view: 192.168.2.0/24 bypass?
My custom configs were working fine but something broke so I'm trying to nail down what it might be.
-
@pftdm007 Have you managed to save the config with the advanced options? Like remove everything and save, does that work? Just add the server: Include . . . line?
Then the views without the leading spaces?From the configuration provided, it looks very similar to mine, only real difference is I have forwarding enabled as I used SSL/TLS to my Internet DNS servers, but I had views working long before that and even before that config had to also be in custom options.
@denx I'm no expert, but based on my networking background, I don't why that would make any difference.
Best practice is general is always to have more specific matches first, but in your case they are both /24's -
@horse2370 Thanks! After messing around a bit, I discovered that the order in which you put the networks/hosts makes no difference. The culprit for my problems was, indeed, the "server" prefix in the last line. Deleting it solved the issue.
-
@denx Great - as for the server: unless you want to make the modification posted by Gertjan, keep checking if make any changes to pfBlocker as it will come back.
I have a note on in my "Change Log Documents" to verify so it doesn't bite me.To help out pfdm007, do you have leading spaces in your Custom Options?
TIA
-
Finally got to do some testing....
@horse2370 : Yes if I remove evething in Unbound's custom options box, it saves. I also managed to find a workaround:
- Shutdown DNSBL/pfblockerNG, it will remove its line in Unbound's options
- Keep everything else in Unbound's options
- Remove the leading spaces
- Save (no problems!)
- Start DNSBL, it puts back its line in Unbound's options
- Remove the "server:"
- Save the options
Now I need to check if the bypassing works, but at least I got past the saving issues....
-
After all, it seems it is working now. In retrospect, I think there are still some bugs and things to iron out, and DNSBL's devs should definitely support unbound views, but at least it all works at this moment. Big thanks to you guys!
-
I'm sure this is obvious and likely just not the way you want to go, but another solution is to create a separate interface (vlan) for certain hosts and exclude this interface from using unbound (and pfBlockerNG/DNSBL) altogether. Then just allow hosts on this interface/vlan to access "respectable" external DNS servers. I did this for a gaming PC so that I didn't have to compromise my tight pfBlockerNG/DNSBL config for the sake of a single computer that wanted to talk to the world.
-
While this solution may work for some, I would prefer to still have some blocking on the additional vlan. I just really wanted the ability to have policy based blocking like the Sensei plugin offers for Opnsense. I'm currently trying it out with the $9.99 home plan, and so far it has been working as expected. It was so easy to set up as well, it just sucks having to pay 10/month :P lol Really would prefer to go back to pfsense. My goal was to find basic ad blocking on some (adult) pc's, and much stricter blocking for my kids pc's and guest devices.
I could have used other options, like pi-hole or opendns for the kids, but I want it to all go through my router and not depend on other services. Thanks for all the input so far!
-
@mdngi said in Bypassing DNSBL for specific IPs:
I'm sure this is obvious and likely just not the way you want to go, but another solution is to create a separate interface (vlan) for certain hosts and exclude this interface from using unbound (and pfBlockerNG/DNSBL) altogether
That's exactly what I wanted to do since day 1. Read my original post on this thread:
Basically I want all traffic on a specific VLAN (named DMZ with 192.168.2.0/24) totally bypass pfblocker & DNSBL in both directions (incoming and outgoing)...
Does it mean that there is a simpler/more permanent way of doing this? You need to detail how because AFAIK, all interfaces have their traffic go through the same DNS resolver (Unbound) and the distinction between filtered or not is done at the resolver level via the line :
include: /var/unbound/pfb_dnsbl.*conf -
It's basically 4 things.
1). Configure unbound to not listen / respond to queries from clients on the excluded interface ("Network Interface" on the general tab of the DNS Resolver settings)
2). Don't configure any NAT / Port Forwarding for DNS on that interface (i.e. don't force DNS through pfSense like you probably would for the other interfaces)
3). Configure your DHCP settings for that interface with the DNS server(s) you want to use on the hosts for this zone (eg. Google, OpenDNS, etc) OR set the DNS server manually on the host.
4). Create the necessary FW rules for that interface to allow DNS out to the open internet / to the DNS servers you specified in #3.