Help with VLANS
-
Hi,
I am looking to introduce VLANS to a small special school network.
Teacher / Student / School Admin - VLAN10 (192.168.10.x) - They access the same server / printer.
VOIP Network - VLAN20 (192.168.30.x)- Need access only to the outside world.
Guest Network - VLAN30 (192.168.50.x) - Need to provide only internet access and no access to printers / server.
I know VLAN10 have a few groups, but they all access the same server and printers.
Was thinking of having printers (2 x Copiers) on a separate VLAN, but is this necessary for such a small network ?
Look forward to you comments.
Thanks
-
uhm at a glace, I would have implemented different vlan's for teacher / students / school admin
even if it's only 1 device per vlan
you must have great faith in your students to not think that they would try to tamper with teacher and admin stuff
anyway put that printers in a new vlan, it's not a big deal even if they are only 2 -
Hi,
Thanks for your reply.
Okay, if I was to implement different VLAN for staff / students etc, how can they use the same printer, when the printer could be on a different subnet ?
Each staff & pupil laptop have the printer via IP address.
Thanks
-
optionally you can set vlan netmask to /29, use dhcp reservation to set static ip for the printers, after that you just need a firewall rules to permit traffic between students / teacher and printers
-
@vlan2 said in Help with VLANS:
VOIP Network - VLAN20 (192.168.30.x)- Need access only to the outside world.
Guest Network - VLAN30 (192.168.50.x) - Need to provide only internet access and no access to printers / server.The following would need rules like my screenshot:-
VOIP Network - VLAN20 (192.168.30.x)- Need access only to the outside world.
Guest Network - VLAN30 (192.168.50.x) - Need to provide only internet access and no access to printers / server.
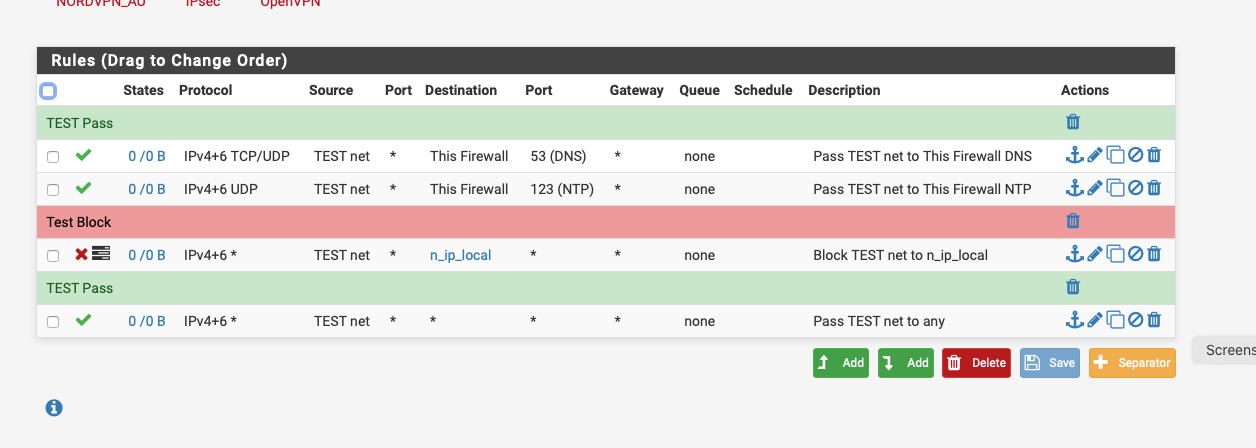
n_ip_local is an alias that contains my local subnets.
TEST net would be the VLAN.
-
indeed, the alias n_ip_local
contain something like this, to block traffic going to any rfc1918 and to be able to go only out of the wan
10.0.0.0/8
172.16.0.0/12
192.168.0.0/16 -
Hi,
Sorry if I sound confused. So if I put printers on a separate VLAN.
How do I get users to print between the VLANS ?
Do I put the firewalls rules in like as described by NogBadTheBad
Many Thanks
-
@vlan2 said in Help with VLANS:
Do I put the firewalls rules in like as described by NogBadTheBad
No my firewall rules are for your voice and guest vlans.
-
Do you have any reason to not use the native LAN? That's typical for the main network. For example, a few years ago, I set up a network in a seniors residence. The main LAN was used for the office computers, etc.. Then there was a VLAN for the office VoIP phones, one for the residents internet access and one for device management. In your case, you want similar, but with the students possibly on a VLAN, but needing to use the printers. You could allow routing from the student's VLAN to the printers, but then you'd have to configure the connections manually, as browsing wouldn't work, unless you had a domain controller. Another possibility would be to multi-home the print server on both office and student networks.
-
Hi JKnott,
That sounds like my network. We can always make adjustments as the network develops.
What do you think of : -
VLAN0 (Main LAN Network - Server, Laptops etc)
VLAN1 (VOIP Network)
VLAN2 (2 x Copiers)
VLAN3 (Guest Network)VLAN2 would need to communicate with VLAN0.
If the printers were on a different VLAN, how can I get other parts of the network to communicate with the printers, but not open to other parts of the network?
Thanks
-
Why do you want the copiers on a separate VLAN. As for what connects to where, that's all routing and rules. You have to decide what you want and go from there.
-
I would do it like this:
VLAN10 (192.168.10.0/24) - Main LAN with servers, laptops, workstations, and ALL printers
VLAN20 (192.168.20.0/24) - VOIP network
VLAN30 (192.168.30.0/24) - Guest networkI typically use a 2 digit VLAN tag scheme, some switches and other network gear use some of the single digit, like "VLAN1" as management access and cant be changed. That gear really shouldn't be used, but it is what it is. If you make the 3rd octet in your addresses the same number as the tag, it's really easy to spot and identify what's coming and going, and from where, in your firewall logs or GUI screens.
If you've got anybody VPN'ing into the network, throw them on a 192.168.40.0/24 network. Then you've got no overlapping of addresses, most likely.
Now, with a setup like above, you can set static DHCP leases for all the printers and copiers, easily add them to an alias, then create firewall rules to pass printing traffic to them, across your VLAN's.
Jeff