Filtering outgoing traffic
-
@MarianHlusek said in Filtering outgoing traffic:
it'll bypass the pfBlocker/DNS resolver
Says who? If your proxy uses pfsense as its dns, it would still be using pfblocker.
-
@johnpoz how can I check/assure that, please? If I use explicit proxy, I understood from few tutorials I have to have correctly filled the DN servers on the General Setup tab -> that's why I understood it will use these directly without going through the DNS resolver.
Seems my understanding was wrong. -
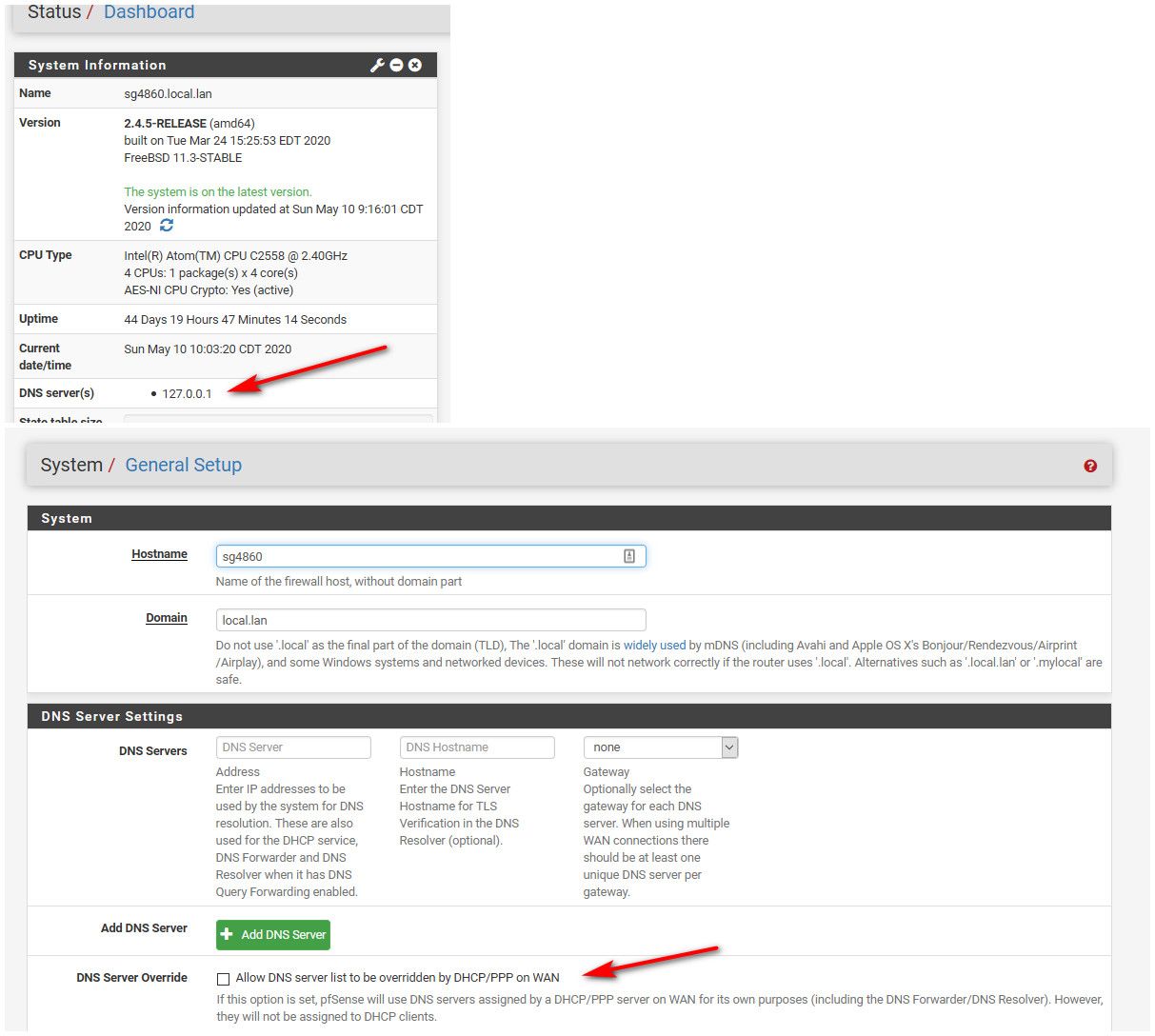
The only thing in general setup should be loopback 127.0.0.1.. Out of the box - this is how resolver works..
Are you letting dhcp set your dns? Uncheck that..
-
@johnpoz I just tried that, but that's probably not the right setup for me. Internet stops working.
Maybe because of NAT rules from each VLAN to 127.0.0.1 port 53?
-
No that would have nothing to do with it..
Are you actually resolving, or forwarding?
-
@johnpoz I am resolving. Forwarder is disabled.
-
Then this is only settings you need. As you saw from my system... That is how its setup..
Forwarding traffic to 127.0.0.1 would have zero to do with anything.
You didn't setup the resolver to forward? Did you you? Out of the box pfsense resolves.. Did you setup some forward to 1.1.1.1 with tls or something in the resolver?
There are 2 systems in pfsense, the resolver (unbound) which out of the box resolves, but can be setup to forward. Or the forwarder (dnsmasq)..
-
@johnpoz Yes, that was the catch ... I missed the tickbox forward in the resolver. Now it works just with the 127.0.0.1. Thanks.
Do you have any preference how to solve the above mentioned traffic filtering for the kid's LAN? -
Your proxy idea is the prob the best, because you can do categories..
I haven't filtered traffic for my kids for 20 some years ;) Back when they were teenage boys looking for p0rn ;) heheheh
I haven't looked into the pfblocker DNSBL lists you could use or setup.. But could be viable solution as well, might just be a bit more leg work.
-
@johnpoz Well, honestly ... I would love to use the pfBlocker, as this seems to me 'easier' solution as it is already implemented and working. The shallalist is available there as well ... the only thing I am not sure is how I split the filtering for:
parents -> DNSBL, Ads, IP
kids -> all the above + categories
But let's see, maybe someone else comes with some other views.
Thank you.