Firewalled traffic not being logged by GUI or tcpdump on pflog0
-
Hello,
I use the following command when I'm troubleshooting to show what the pf firewall is blocking:
tcpdump -n -e -ttt -i pflog0 <traffic to match>
However, I'm noticing more and more than some of the traffic being blocked by pf is not being shown.
As a test, I set up a rule to block ICMP from a specific host (x.x.x.x) to the LAN interface:
X Block IPv4 ICMP any x.x.x.x * LAN address * * none TestI issued this command on the router running 2.4.4:
tcpdump -n -e -ttt -i pflog0 host x.x.x.x
When I ping from the x.x.x.x host to the LAN interface I get no output at all from the above command, even though the traffic is not going through. I'm noticing the blocked traffic is not appearing in the GUI either (Status-->System Logs-->Firewall).
Is there a different way I should be doing this?
-
I also tried the 'tcpdump -n -e -ttt -i pflog0' command on a router running 2.4.5. It did display some TCP traffic being blocked, but it hasn't shown any blocked ICMP traffic so far.
-
Not sure what your doing exactly - but can not duplicate this.
Running 2.4.5p1
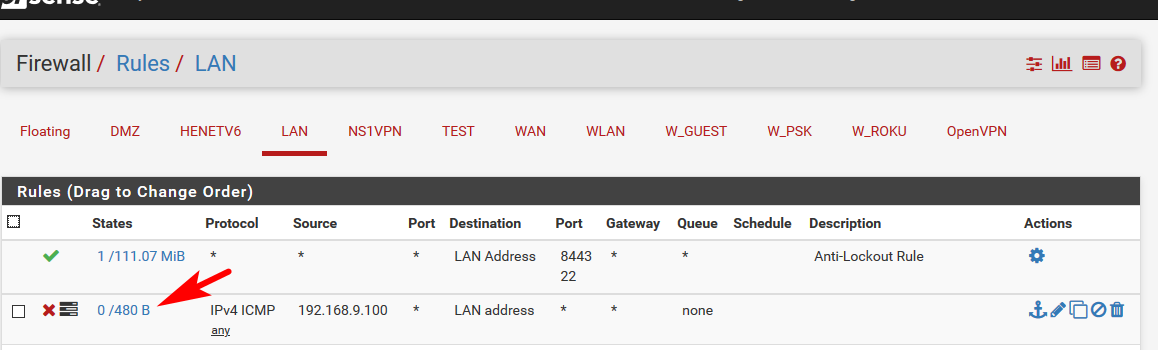
Setup a block rule, set it to log, top of the list so its evaluated before the any any rule.
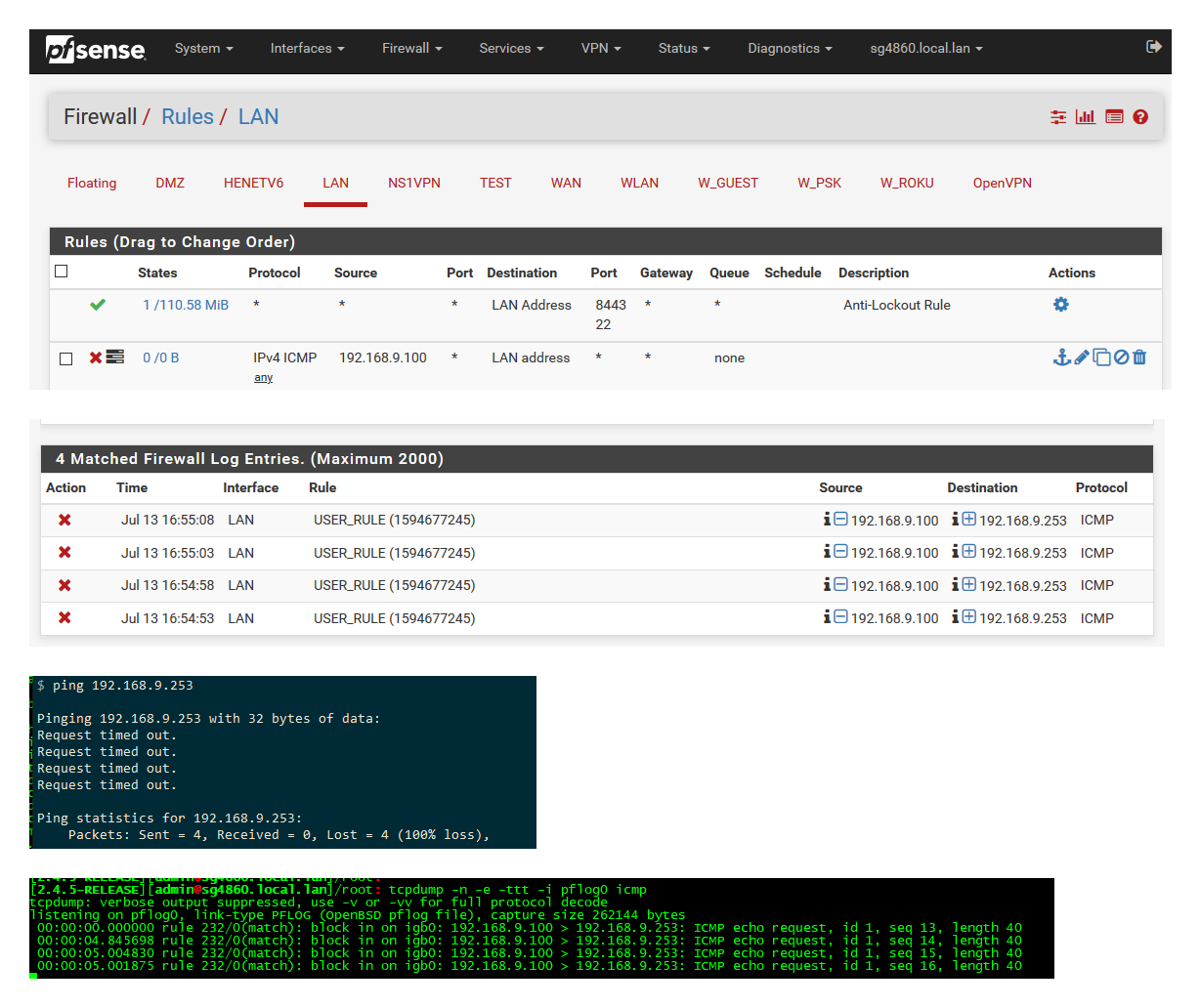
You can see entries are in the firewall log, I can also see them via the command line.
And clearly the traffic is blocked since can not ping.
If you set a rule to block and log, and your not seeing it logged.. My take would be that the rule is not evaluated, or you had a state already to allow it, so the rule not being triggered.
I can also see after some traffic blocked, that the rule shows traffic was hit on that rule.. the 0/480
Rules are evaluated top down, first rule to trigger wins.. If you have your block rule below the any any default rule than your rule would never trigger and would never be logged.. You didn't state if you were actually getting ping returns or not, for all i know you were not pinging the IP of your rule which was lan address. Or if you have a rule say in floating that would be evaluated and allow the traffic before your interface rule.
When you create a block rule, you need to make sure any states that might be already there are killed - because, states are evaluated before rules.
Also if your not getting responses but your not seeing anything logged, possible you have a block rule - say in floating or above your rule that is blocking but not set to log.. Or maybe ping is never actually getting to pfsense - always good idea when troubleshooting this sort of thing to validate your traffic is actually getting there via just a packet capture on pfsense.
In all my years of using pfsense, have never seen log not working be it blocked traffic or allowed traffic.
-
OK, I see, I didn't know I need to have 'log' applied to the firewall rule before it will log to the GUI or pflog0 .
Is there a way to temporarily apply 'log' to all firewall rules for troubleshooting?
-
Off the top of my head I don't think there is a way to have your existing block rules that not set to log, all log without changing them. Out of the box the default deny is logged.
-
I found the setting to log the deny all rule:
Status-->System Logs-->Settings-->Uncheck 'Log packets blocked by the default rule'
I can also issue:
pfctl -sr | grep block | grep -v logto find any block rules that aren't being logged.
-
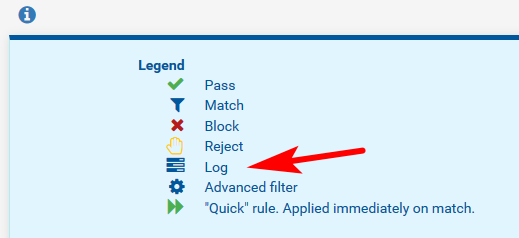
You could also just look at the gui ;) If its logged it shows the little icon next to the rule..