firewall rules to block ports not working
-
Hey all,
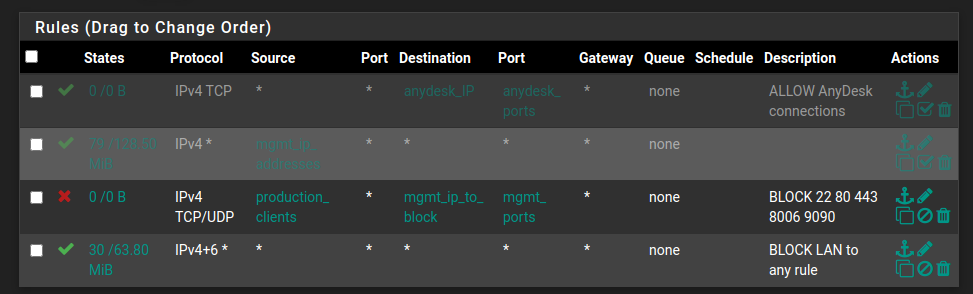
On pfsense I've set up a rule to try and block ports 22,80,443,8006,9090 from a range of client IP address to a range of server IP addresses, but it doesn't seem to work.
Misc:
Proxmox standalone server with OVS switch runs pfsense VM.
Proxmox cluster (3nodes) with OVS switches run misc VM's that need ports blocked.
Can someone look at this rule and please give me some guidance?Thank you!!!
-
Off the top of my head, I don't see anything wrong with your rules.
However, as a general rule of thumb, you want to position your BLOCK or DENY rules at the top of your rule list(s). Try that and see if it triggers. The way it is now, and I'm pretty sure you realize this, there is nothing getting "caught" by that block rule you've got in position 3.
Jeff
-
Yes.. rules are parsed from the top down. Any rule that trumps another rule must be on top of that rule.
-
Keep in mind that if there are existing states the rules are not evaluated.
If you want to block something, you need to make sure you clear any states that would match up with you rules.
Also can not tell what interface you have that rule on? Sure doesn't look like the normal lan, since I don't see the antilock out rule?
You need to place rules on the interface where traffic would enter pfsense. Rules are evaluated top down, first rule to trigger wins, no other rules will be evaluated.
If you are trying to place those rules in floating, you need to make sure you click quick on the rules and pick the correct interface for the direction your going to create the rule for (floating allows for inbound or outbound rules).
-
If you'll look, the top two rules are deactivated.
So the top, active rule is the blocking rule. -
I didn't say anything about those rules.. Block not working normally means it didn't match because it not setup correctly fort what your trying to block.. Or there is an existing state that is allowing it.
Or its on the wrong interface, etc.
Never in 11 some years of using pfsense have I ever see a block rule that didn't block what it was suppose to block ;) Be it my own setups, or any thread I can ever recall. If a block is not working, then there is a state allowing it. Or its not being evaluated for some reason.
-
@johnpoz That last response was not directly for you, but for those others that are posting to put the "block/deny" at the top.
Thanks for your help! -
@johnpoz BTW...someone on the proxmox forum said that pfsense will not block/deny within the same subnet. So if I try to block ports from systems within the network, it will not work. Only across other vlans/networks. Is this correct?
-
Yes - its not possible to block clients on the same network from talking to each other.. Why would a device on a network need to talk to the gateway to talk to its own network? You only need to talk to your gateway (pfsense) to get off your local network.
-
@johnpoz Thank you
-
if you need to block devices on the same network from talking to each other.. If they are wireless you would do that on the AP, with isolation. Different makers users slightly different names, AP isolation, client isolation, etc.
For wired clients your switch would need to support what is normally called private vlans, which can prevent clients from talking to each other.
If you want to do it and your L2 infrastructure doesn't support it, then you would normally split devices you don't want talking to each other into different vlans, so their traffic between each other would have to be routed (through pfsense) now you can filter it..
Other option is using host firewall on each device to block traffic you don't want to allow between hosts.
There are many ways to skin a cat, but no pfsense has no control over devices on the same L2 from talking to each other.