Vlan in different subnets cannot connect...
-
Hi all!
I have setup 3 vlans in my pfsense...
192.168.30.0 / 16 vlan 1
192.168.40.0 / 16 vlan 2
10.0.0.0 / 16 vlan 3For some reason, I can go to 192.168.30.x from 192.168.40.x and vice versa... but I am not able to go to 10.0.0.x from 192.168.30.x or 192.168.40.x. I am thinking maybe the subnet mask is different which is blocking... but with VLANs, my understanding is that pfsense would allow inter-vlan connections...
Can anyone help or let me know the issue on hand?
Thanks!
-
Is there a reason you're using a /16 subnet mask on your VLANs? Normally, a /24 is used, the /16 is an extremely LARGE number of possible addresses. Unless this is specifically needed, you should switch the masks back to /24.
And also, to "go to" one subnet from another, you have to have appropriate firewall rules setup on each subnet. Can you post a picture of your 3x VLAN firewall rules?
Jeff
-
@sho1sho1sho1 said in Vlan in different subnets cannot connect...:
192.168.30.0 / 16 vlan 1
192.168.40.0 / 16 vlan 2I don't see how pfsense would even let you do that... Since those are the same network and would overlap..
Did you set that on your clients? That sure and the hell wouldn't work, since to something on the 192.168.30/16 an IP address at 192.168.40.x is local, and would never send the traffic to the gateway.
-
Good call! I typed that wrong...
192.168.30.0 / 24 vlan 1
192.168.40.0 / 24 vlan 2
10.0.0.0 / 16 vlan 3As for using 10.0.0.0 / 16 subnet, we have systems that come and go. For the first batch, we use 10.0.0.x, for the second batch, we use 10.0.1.x. That way, I don't ever have to worry about duplicate ip in our dhcp file and we keep a log of mac addresses.
Now for the firewall rules,
vlan1
protocol Source Port Destination Port Gateway Queue
ipv4 TCP vlan1 * vlan2 * * nonevlan2
ipv4 TCP vlan2 * vlan1 * * nonevlan3
ipv4 TCP vlan3 * vlan1 * * noneWith these rules, I can connect from vlan1 192.168.30.x to vlan2 192.168.40.x
But I cannot connect vlan 1 192.168.30.x to vlan3 10.0.0.xInter-vlan routing should work for vlans of different subnet masks, right?
-
Yeah.. You prob running into a host firewall issue.. Can your devices ping the IP of pfsense interface in the 10 vlan?
Oh.. your rules are TCP only? - so you wouldn't be able to ping.. Make those any..
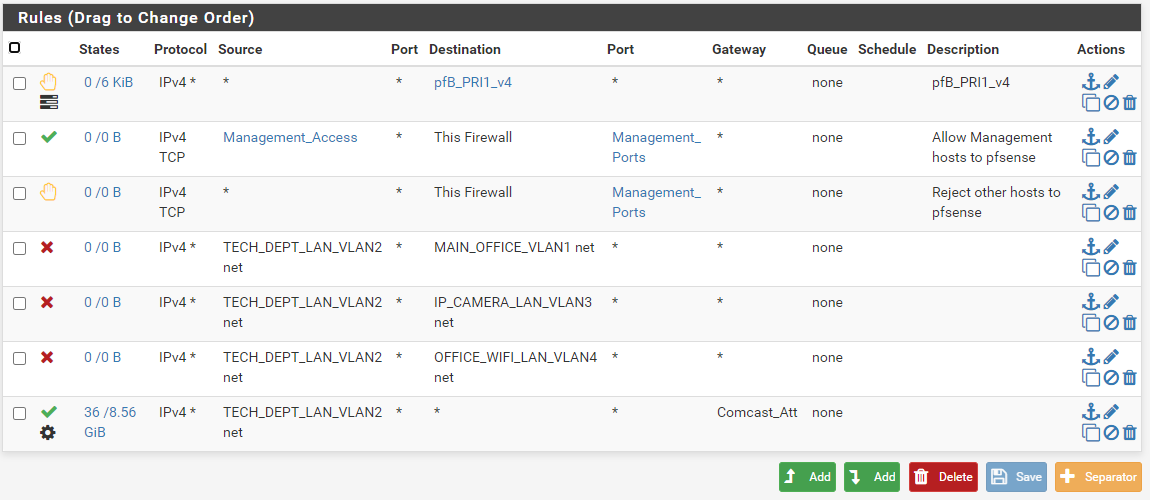
And your rules are not allowing access to vlan3 from vlan 1 or 2?? Screenshots are always better!
-
MAIN_OFFICE is 192.168.30.x / 24
TECH_DEPT is 10.0.0.x / 16
OFFICE_WIFI is 192.168.40.x /24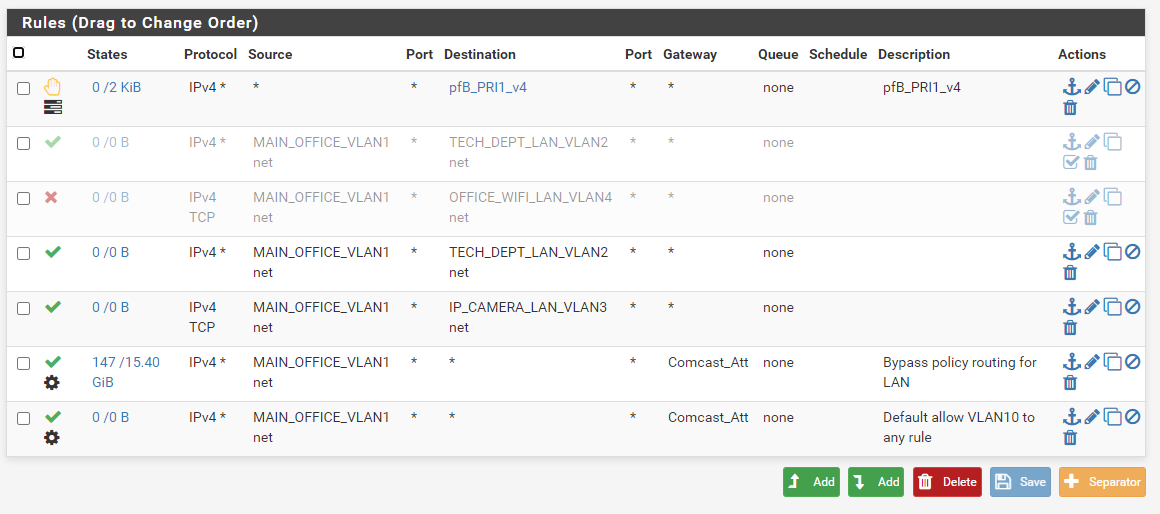
-
Your forcing traffic out a gateway.. If you want a vlan to get to your other networks, you have to allow for that before you force traffic out a gateway
-
@johnpoz Can you eloborate more on that? Which rule should I change? Or do I swap around the rule order?
-
On your last pic your not allowing access to anything, above the last rule that forces traffic out the gateway... So how would that vlan get anywhere? Other than out the gateway... And comcast_att sure isn't going to let you access your other vlans.
-
@johnpoz But if I only want my staff to only be able to connect from Main office vlan 1 to tech dept vlan 2 and not the other way... is that possible?
I think that's why I put allow rule with source vlan 1 and disallow rule with source vlan 2.
-
You can allow or block anything you want... Rules are evaluated top down, first rule to match wins, no other rules are evaluated.
Why exactly are you forcing traffic out that gateway, is that not the default gateway, or only gateway?
-
@sho1sho1sho1 said in Vlan in different subnets cannot connect...:
As for using 10.0.0.0 / 16 subnet, we have systems that come and go. For the first batch, we use 10.0.0.x, for the second batch, we use 10.0.1.x. That way, I don't ever have to worry about duplicate ip in our dhcp file and we keep a log of mac addresses.
Maybe you should move to IPv6. You'd be extremely unlikely to see a duplicate in 18.4 billion, billion addresses. If you do, you could start investing in lottery tickets.

Do you really have 65K devices coming and going?
-
@johnpoz I setup a redundant gateway group. I have Comcast and ATT. I haven't figured out how to get redundant gateway group to work with VPN yet... so the default gateway is Comcast alone... With the rule, I had to put in the redundant gateway group or else traffic only goes out Comcast... I wonder if my setup is somewhat correct... I set these all up by studying the wiki

Let me study more in-depth about the rules and see if I can get it to work... but can you tell me the /24 and /16 should not be the issue?
-
@JKnott I still haven't dug myself into ipv6 yet... Maybe soon though. I won't have 65k devices coming and going... but the batch of systems that I get might be a batch of 2 or as large as a batch of 500. So some ip 10.0.1.x, I would only use 10.0.1.1 and 10.0.1.2... and I move on to 10.0.2.1 for the next batch... Maybe there could be a better system out there...

-
Well, with databases, you need at least one unique key. Seems to me the MAC address would do that and just allow duplicate IP addresses. Also, with a /16 and 65K addresses, it would take a long time to go through all those addresses. You can play with lease time for this. Also, the expire time is much longer than the lease time, so that will cause an address to not be reused for a significant time. I don't know if there's a setting for that though. An expired address won't be used until all free addresses are used.
-
@sho1sho1sho1 said in Vlan in different subnets cannot connect...:
but can you tell me the /24 and /16 should not be the issue?
No that is not an issue as long as the networks don't overlap.. and since one is 10.x and the others 192. there is no way they could.
There is a whole section about policy routing, which is what your doing when you set a gateway on a rule. And you have to allow intervlan traffic that you want to allow above where you force the traffic out a gateway. Pretty sure its in the multiwan parts of the doc.
But if you say what you want to allow and what you want to block - and post your rules happy to validate them for you.
And don't forget host firewalls, they don't like other non local vlans normally.. There be a flood of those threads as of late.