interface group rule not working ?
-
need help understanding...
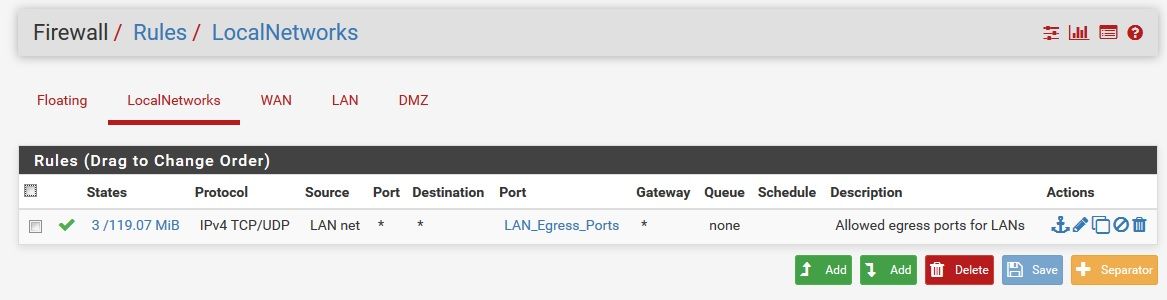
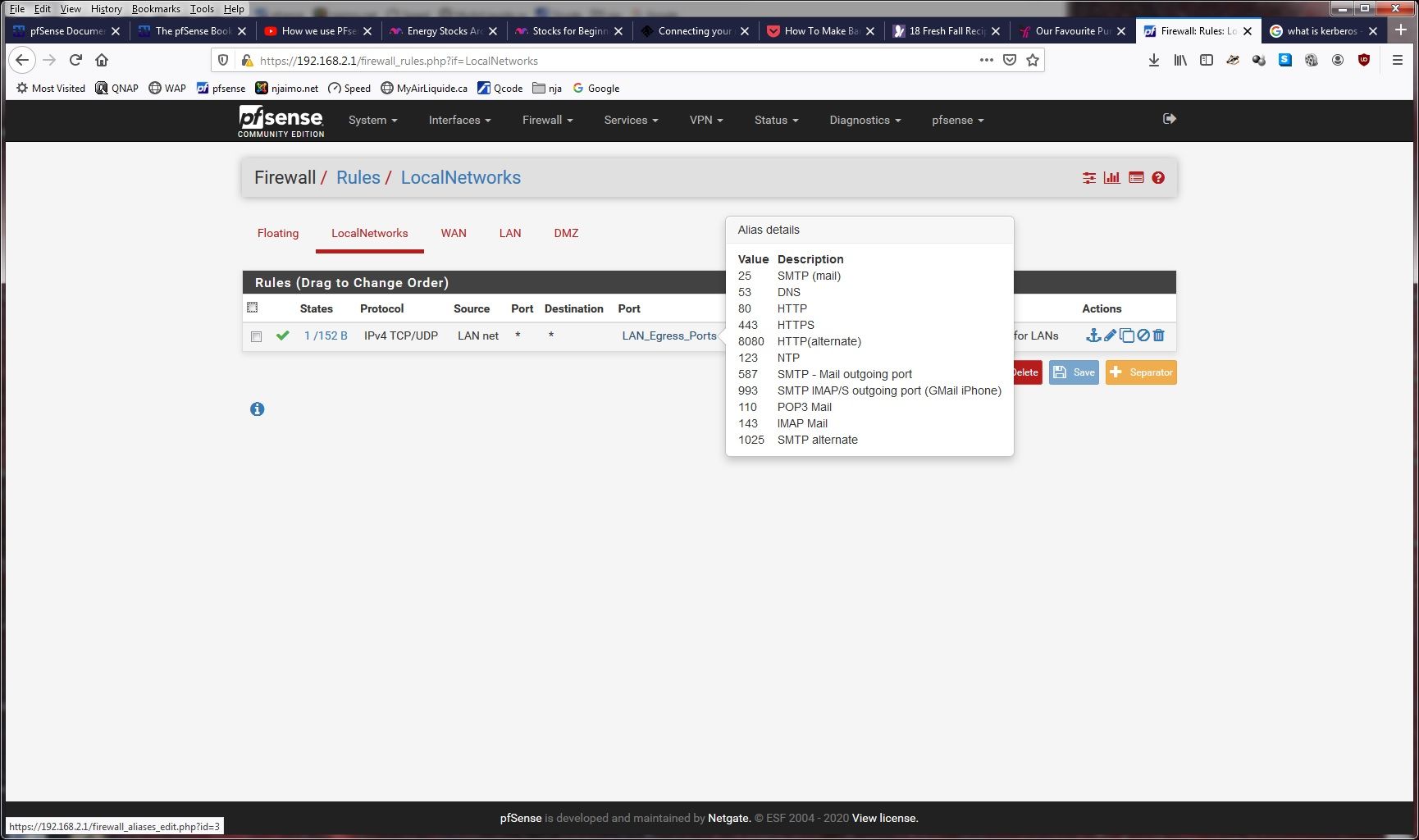
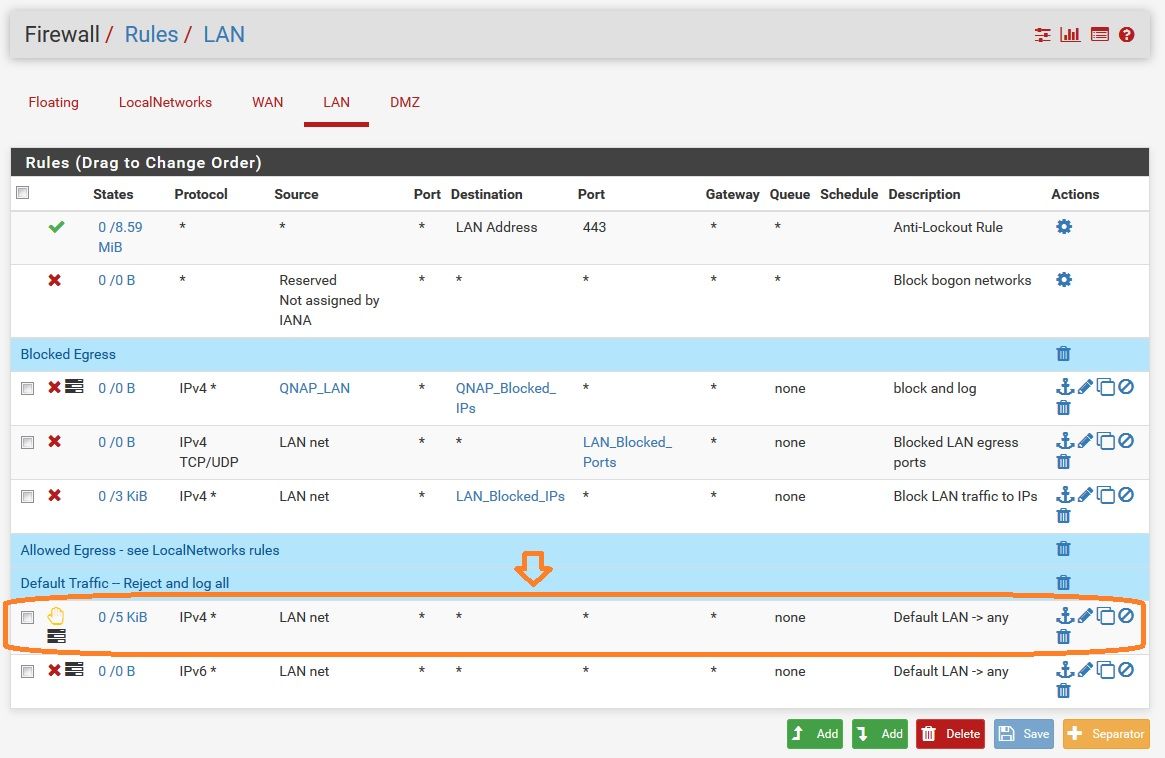
First, I am a noob at this... I have set up a pfSense firewall for a small network. The appliance has 3 hardware interfaces WAN, LAN, DMZ, and there is currently no hosts in the DMZ, so there is nothing there. I have no VLANs, no VPN yet. In anticipation of having DMZ traffic I set up an Interface Group called "LocalNetworks", and made a single rule allowing egress traffic through selected ports (including 443) -- please see attached screen-captures. I am blocking all other LAN egress traffic via rules in the LAN and DMZ interfaces, and logging what gets blocked to see if I need to allow it.
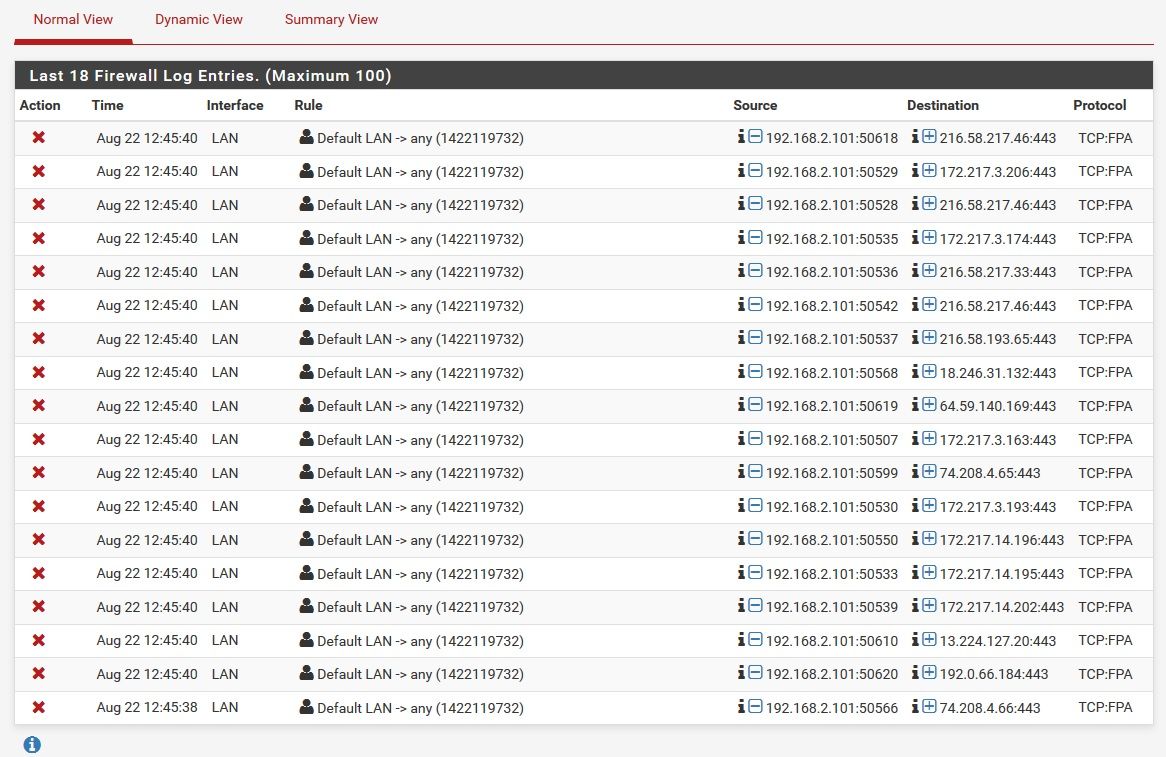
During "normal" operation all seems to work fine, the LAN group rule lets all allowed egress traffic out, and I have gotten no blocked LAN traffic, however I have noticed something that seems unusual to me upon restarting a host on the LAN from a sleep state, i.e. Windows Sleep. Upon "awakening" from sleep, pfSense logs show a whole bunch of blocked traffic by the LAN interface rule, traffic that should have been allowed by the LAN Group rule -- see attached images, and highlighted blocking rule on LAN interface. Once the machine is awake, there are no more blockages to port 443 by the LAN interface rule, which shows the LAN Group rule is working as it should be, as it is allowed by the LAN group rule. It would seem that the interface group rule is not active, or not processed upon "awakening", but the LAN interface rule is ?
I should mention that the host in question has several webpages in a Firefox window that are in the awakening desktop (i.e. the Firefox window was not closed at sleep time, and thus is being re-started), which are the source of the outgoing traffic upon awakening.
What am I failing to understand in this behavior ?
-
... so I removed the interface group completely, and placed the rule allowing port 443 egress (along with the other ports) out of my LAN, before the "default deny rule"
...same issue, upon "waking" my PC from sleep, it sends several packets from my LAN to the WAN on port 443 -- they all get blocked by the default deny rule, instead of being allowed to egress given the "egress ports" rule placed above. After the machine is completely "awake" no other outbound port 443 requests get blocked (as should be given the allowed ports egress rule).
I have received no relies to this post -- have I've missed something very obvious ? I am happy to be told so ;), really But I am puzzled by this...
-
@njaimo
The blockages the screenshot shows are "out of state", i.e. pfSense has already closed the connection.
You can see it on the flag. pfSense logs only the first packet of a connection (Syn flag). If the first packet has another one than a Syn it gets dropped (when pfSense has no state for it).Obviously the web browser on the machine tries to resume its connections after awaking, but they are already closed by pfSense and so they are dropped. The browser will detect that and open new connections.
-
THANK YOU (!!) for the explanation ! ...makes sense, and is something I was not aware of -- Thanks Again !