OpenVPN will not connect
-
@erbalo said in OpenVPN will not connect:
Just which ports UDP or TCP and port number do i need to open on my modem/router?
That one your OpenVPN server is configured to listen to.
By default that's port 1194 UDP. -
Ok i did that but it didn't helped. Do i need to add NAT ports on pfsense box? There is a Firewall rule but NAT rule isn't created.
-
Some stupid ISP routers do NAT on inbound traffic. If that is the case and you cannot disable it, you have to uncheck "Block private networks" in the WAN interface settings.
Basically I'd suggest to replace the router by pfSense, bridging the modem if possible.
@erbalo said in OpenVPN will not connect:
Do i need to add NAT ports on pfsense box? There is a Firewall rule but NAT rule isn't created.
That depends on your setup. Provide more details about your configuration.
-
Can this be done not the brdiging the Modem/Router but Modem/Router set as DMZ?
-
Yes, the DMZ mode normally forwards all to the IP or MAC you can define there.
However, consider the possibility that the router may do NAT on incoming traffic as mentioned. -
@viragomann said in OpenVPN will not connect:
However, consider the possibility that the router may do NAT on incoming traffic as mentioned.
What do you mean here? Sorry for me a double check if i am understanding good.
When set my modem to forward all via DMZ to my PFsense Router, my pfsense maps all the NAT ports?
-
@erbalo
Many ISP routers and also other ones translate the source IP form incoming packets to their LAN IP when forwarding to an internal device.
If that is the case and you have and you cannot deactivate it, you have to remove the check from WAN settings as mentioned above. -
@viragomann said in OpenVPN will not connect:
@erbalo
Many ISP routers and also other ones translate the source IP form incoming packets to their LAN IP when forwarding to an internal device.
If that is the case and you have and you cannot deactivate it, you have to remove the check from WAN settings as mentioned above.Another ports forwards works fine, just this problem i don't have it. I have just set my Modem/Router on DMZ and just all forwardings goes via PFsense but VPN not working.. Tried via that Android explort client file on my Android OpenVPN app.
-
Again, you have to provide more details to get help here.
@erbalo said in OpenVPN will not connect:
but VPN not working
What do you get?
-
@viragomann said in OpenVPN will not connect:
Many ISP routers and also other ones translate the source IP form incoming packets to their LAN IP when forwarding to an internal device.
Like what devices do this - this would be utterly moronic.. Never seen this.. Sure you could do such a thing on pfsense. But you would have to do it on purpose, ie a source nat..
Never seen some soho router that would do source natting even if you wanted to, let a lone on its own.
Where is the sniff on the wan when trying to access the openvpn? Lets see this please..
-
@johnpoz said in OpenVPN will not connect:
Like what devices do this
Seen on a Fortigate B60, but also on others.
It's some kind of a "plug and play" setup. There is no need to configure the destination devices firewalls, cause the access seems to come from its own subnet.@johnpoz said in OpenVPN will not connect:
this would be utterly moronic
Absolutly agree.
-
@viragomann said in OpenVPN will not connect:
There is no need to configure the destination devices firewalls, cause the access seems to come from its own subnet.
Which is a utterly horrible idea ;) Sure its an option if the device doesn't have a gateway set, I do it myself to talk to one of my devices when I vpn in, because it doesn't have a gateway..
But to auto do that without the admin purposely having to enable - just horrible idea.
If that is the case and its coming from rfc1918, then just turn off the block rfc1918 rule.. As already mentioned.. But would still like to see the sniff of hist phone trying to access the vpn..
-
@johnpoz said in OpenVPN will not connect:
If that is the case and its coming from rfc1918, then just turn off the block rfc1918 rule.
Obviously it's not:
@erbalo said in OpenVPN will not connect:
Another ports forwards works fine, just this problem i don't have it.
But that's all he let us know...
-
@johnpoz said in OpenVPN will not connect:
@viragomann said in OpenVPN will not connect:
Many ISP routers and also other ones translate the source IP form incoming packets to their LAN IP when forwarding to an internal device.
Like what devices do this - this would be utterly moronic.. Never seen this.. Sure you could do such a thing on pfsense. But you would have to do it on purpose, ie a source nat..
Never seen some soho router that would do source natting even if you wanted to, let a lone on its own.
Where is the sniff on the wan when trying to access the openvpn? Lets see this please..
What do you mean about sniff on my Phone and WAN? i don't understand the question sorry.
If you mean where my phone then located i have tried all the time WIFI disabled on my phone.
-
Sniff on your pfsense wan, via diag, packet capture menu item for the port your listening on for openvpn. Then try and make a connection from your phone - or other client that is not on your network..
example
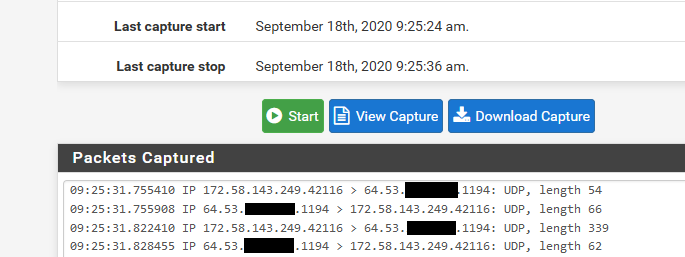
That is my phone coming from the 172.58 address (t-mobile) hitting my openvpn port (1194 udp) on my wan IP 64.53.x.x
-
@johnpoz said in OpenVPN will not connect:
Sniff on your pfsense wan, via diag, packet capture menu item for the port your listening on for openvpn. Then try and make a connection from your phone - or other client that is not on your network..
example
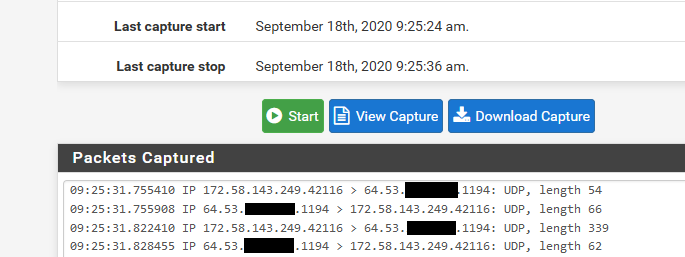
That is my phone coming from the 172.58 address (t-mobile) hitting my openvpn port (1194 udp) on my wan IP 64.53.x.x
Ohh learned something news!! Did that but nothing to see there. Tested another port which i have use for other thinks and i see that as well.
-
@erbalo said in OpenVPN will not connect:
Did that but nothing to see there
Well if you do not see anything there when you attempt to access vpn.. Then how would you connect? Pfsense can only work with traffic it actually sees.
You have something upstream blocking access then, so no you would never be able to connect to pfsense vpn until traffic actually gets to pfsense.
-
@johnpoz said in OpenVPN will not connect:
@erbalo said in OpenVPN will not connect:
Did that but nothing to see there
Well if you do not see anything there when you attempt to access vpn.. Then how would you connect? Pfsense can only work with traffic it actually sees.
You have something upstream blocking access then, so no you would never be able to connect to pfsense vpn until traffic actually gets to pfsense.
Thats right my problem, i can't get any traffic via VPN client to the pfsensen. I think should be somehting with my NAT port... What did you fill in here as Target IP address? Should that be the the Gateway IP address of my Pfsense?
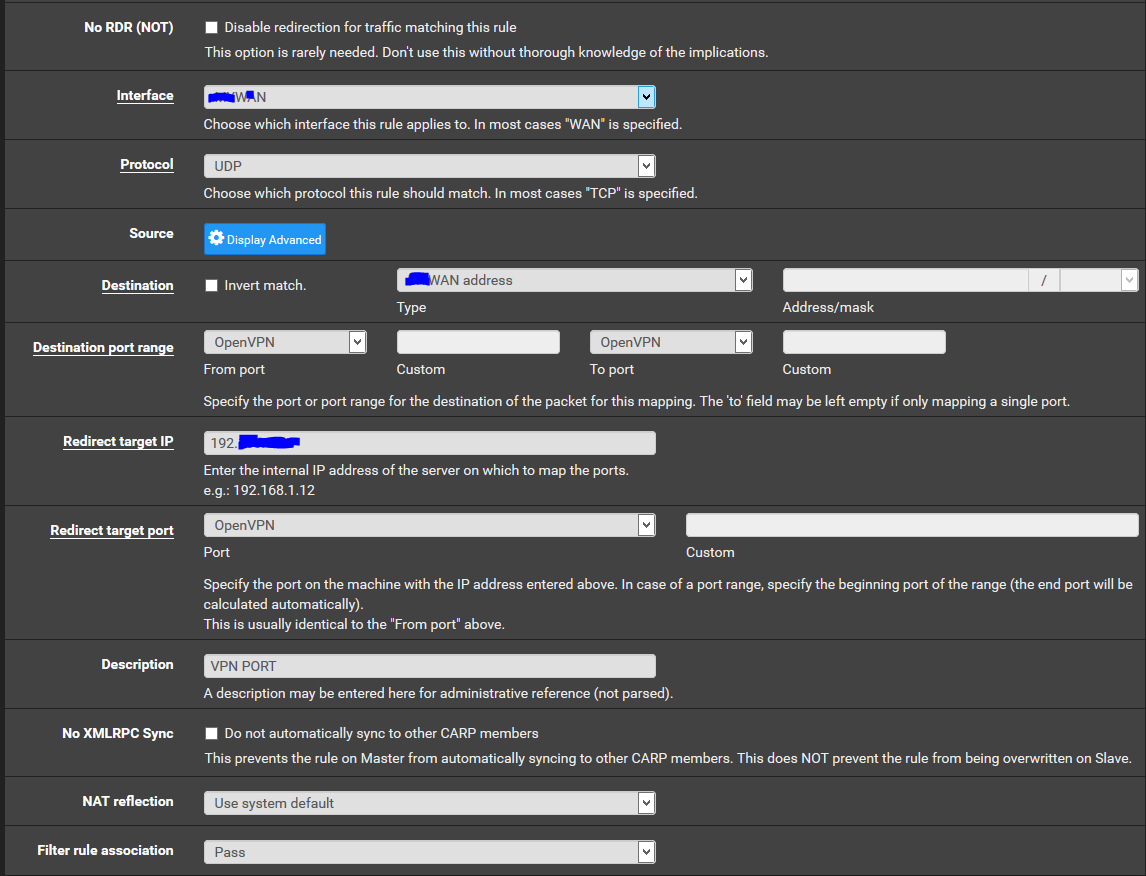
-
@erbalo said in OpenVPN will not connect:
What did you fill in here as Target IP address? Should that be the the Gateway IP address of my Pfsense?
What? The openvpn wizard will setup the firewall rule to pfsense wan address.. You would not be doing a port forward for openvpn. Unless openvpn server was behind pfsense, and that is going to have its own problems with most likely asymmetrical traffic flow.
Again if you do not see traffic on pfsense WAN, then how would openvpn work? You need to validate your client is actually trying to talk to PUBLIC pfsense wan IP.. or if you have something natting in front of pfsense. Than that PUBLIC ip and that whatever is natting in front of pfsense is sending to pfsense wan IP.
-
@johnpoz said in OpenVPN will not connect:
@erbalo said in OpenVPN will not connect:
What did you fill in here as Target IP address? Should that be the the Gateway IP address of my Pfsense?
What? The openvpn wizard will setup the firewall rule to pfsense wan address.. You would not be doing a port forward for openvpn. Unless openvpn server was behind pfsense, and that is going to have its own problems with most likely asymmetrical traffic flow.
Again if you do not see traffic on pfsense WAN, then how would openvpn work? You need to validate your client is actually trying to talk to PUBLIC pfsense wan IP.. or if you have something natting in front of pfsense. Than that PUBLIC ip and that whatever is natting in front of pfsense is sending to pfsense wan IP.
On the all off the tutorials people saying "Via Wizard hit at the end to create firewall rules also, ports should be open on the NAT.." i am stuck on here

I think there somehting with my openVPN config or OpenVPNexport. Because i don't see any traffic when connecting from client, that file is not correct or is not comunicating with that public IP. Also on that Wizard i don't see any option to fill my public IP address..