Limit access between remote locations and local clients?
-
@netblues Sorry, I wasn't clear on that part. We have a Linux box at each remote location that will initiate the VPN connection. If necessary I can also run pfsense (or anything else) on those boxes. The devices themselves cannot run openvpn.
-
thats the classic roas warrior approach you are on.
and yes carefull gouping and rule set
is this a sort of TV setup sounds like
-
@DutchSamurai If you can't renumber, then you will need a proxy, or as it called, a jump host to access the devices.
So the linux box openvpn's to central and establishes ip connectivity.Users ssh to the linux box and then ssh to the iot device.
You could run a 1to 1 nat at the linux box and assign natted ip's for your devices.
However managing this won't be easy -
this has nothing to do with the topic.
this whole setup is of course interesting but hmmm a little fishyopen a topic " howto jump host with pfS"
-
@noplan ??
Since remote devices can't run any kind of vpn then it can't be a pure vpn solution. -
I can already ssh into the remote location on the VPN IP. But I really don't want to go that route as it will be unmanageable to give 3rd parties access and a lot of stuff they need to access at the remote location is browser based. The only viable solution is if users can setup a connection directly to their device. The openvpn client at the remote location should, one way or another, provide access/forward traffic to the remote location's LAN.
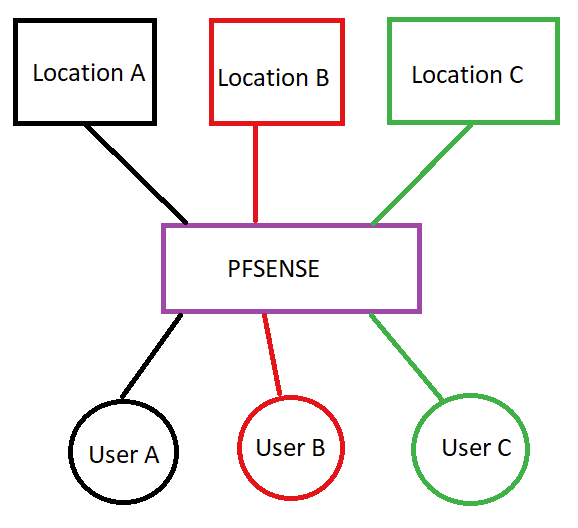
From a practical pov, can this be done using pfsense and if so how should I got about it? I can set up the VPN, I can do the firewall rules and CSO to give specific IP's, but the point I can't figure out is A) how to give access to the remote location's LAN and B) do so when remote locations will mostly be using the same LAN subnet.
-
@DutchSamurai There aren't any other options left than to do one to one nat at the remote location edge linux box.
You can assign a unique ip range at each location, and then configure a one to one nat to the local iot devices.
This will solve the conflicting ip range issue and give you direct http etc access to the non vpn enabled devices.
Linux will do that with iptables.
If there aren't many changes, it will do. -
@netblues Unfortunately I don't think that is going to work. I'll have to keep track of the settings and no doubt people will not remember their device IP isn't 192.168.0.100 but 10.10.10.100 or whatever.
Maybe setting up multiple openvpn servers is the only solution if I want the remote lan accessible as is? I could put a proxy with subdomains in front of pfsense so everybody can still connect to a single port. As far as I understand pfsense supports unlimited openvpn servers? I'm sure the GUI will suffer with a couple of hundred servers but hopefully performance will be ok'ish as all remote locations are low very low bandwidth and just idling most of the time anyway.
-
@DutchSamurai Maybe its time to introduce dns resolution for your devices.
No more ip's to remember.
Several hundred openvpn servers is also a nightmare to administer.
And one needs to connect to the correct vpn server to access.
The connect tab of openvpn client will be unmanageable.If you make a good plan, then anyone could find the nated device ip without looking it up if he knows the real device ip and the location subnet.
Its either renumber or nat, at the scale we are talking about.
-
i m out ....
now i can remember when i last got a call for such a setup ....
pay tv boxes callin over vpn tunnel content not avail in that region or
bypassin some other restrictionsorry for me the scale a 100+ vpnTunnels and seperated networks over a AWS hosted pfS
hmmm .... no me i am outnot something i want to get mixed up with
brNP -
@noplan I'm sorry you think that. This is a perfectly legit business use case. I'm simply asking if this can be done using pfsense as my experience with VPN's is limited and at this scale I am out of my depth.
@netblues I've actually seen a working solution with openvpn doing exactly what I want. Remote locations connect to a central server and remote users connect to the same central server and from there its tunneled to the remote location without the need for changing ip's etc. For ssh this requires a double tunnel but for browser based access you could setup a socks5 in the browser settings (localhost & some port) enabling access to the remote lan.
I've also seen another openvpn based solution that seems to subnet the openvpn tunnel for each remote location and allows access to each remote lan that way. No need for setting up socks or anything.
I don't know how they've actually set any of that up but it works. I think I should tell management I simply cannot do this by myself.
-
@DutchSamurai What you ask is straight forward.
pfsense with openvpn can do that.
In your particular case, there are remote lans with conflicting ip ranges and there isn't much one can do about it.
Its either nat, or renumber. Both will work fine.
It can be done either by installing pfsense at the remote locations, or just keeping the current linux gateways
Managing thousands of devices effectively does require some solid planning.