MS activated DoH at the operating system level, in this "great" 20H2 release...?!
-
@johnpoz said in MS activated DoH at the operating system level, in this "great" 20H2 release...?!:
Not saying you haven't found something odd. But I don't agree with your wording. That its at the os level.
Yes sir, but :-)
I agree with you in a super way...
please try this "image" even on a VM... or other way
if you think, I'll upload it for you somewhere...I feel myself completely stupid about that...
-
@johnpoz said in MS activated DoH at the operating system level, in this "great" 20H2 release...?!:
My 20h2 system is doing normal dns to msftncsi
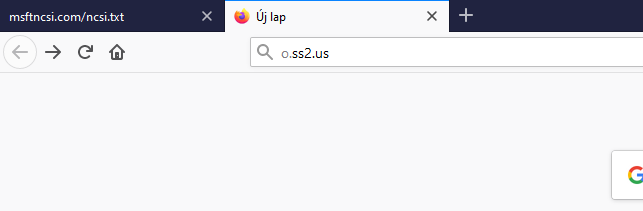
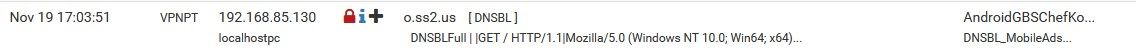
--- o.s22.us
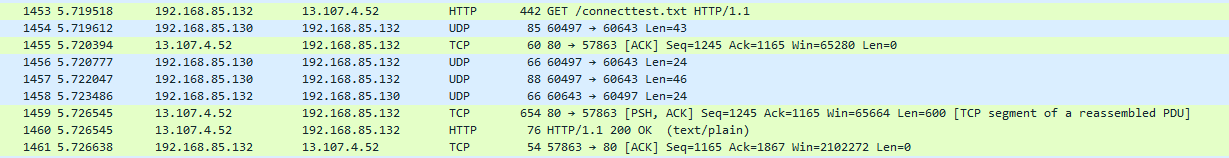
I'll show you again,
this domain is blocked by us..., o.ss2.us via DNSBL feedWin1909:

test PC on clean 20H2:
network setup:
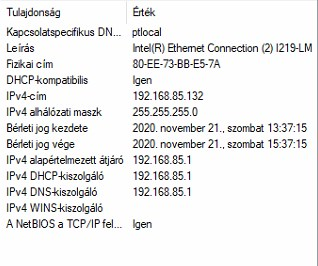
pfSense IP is: 192.168.85.1
igen = yes
DHCP kiszolgáló = DHCP server(sorry for the hungarian OS language)
more over:

192.168.85.130 on Win1909
no entry from 192.168.85.132 on win 20H2
-
You would prob get better help on some MS forum.. While this I guess could be related to pfblocker.. If said device doesn't ask pfblocker for dns, that is not pfsense or pfblocker that keeps the client from doing that.
Why said client doesn't use your assigned dns, would be up to the client.. No matter what you hand it via dhcp.
I wouldn't block that mfsft site for sure.. That is a well known domain in how windows check if it has internet, etc. Blocking it could for sure kick in other methods of the OS trying to see if it has any sort of internet connectivity..
-
@johnpoz said in MS activated DoH at the operating system level, in this "great" 20H2 release...?!:
You would prob get better help on some MS forum..
you're just kidding me now, aren't you?

@johnpoz "I wouldn't block that mfsft site for sure.."
it's just a matter of taste

so as I wrote above we run an external connecttest server, this is not an MS denial...it was just enough of the voyeur or something...
not really a pfSense or pfBlockerNG theme (issue), yet ... you are right (let's say it's a simple statement)but it will be....?!
I knew that, you will be the first to respond to my post, knowing your DoH hate...
(we are rowing in the same boat)do not think that, the future will not come
you cannot delay it, by denying it...+++edit:
I would willingly to give you this "image 20H2 VLSC" if you think, try it on a VM, you don't have to activate it for a few days and you'll see what the future holds I say kindly

-
it would be a much more expedient test, if the leaderboard poster also tried what I am talking about... or anyone else who is willing...
@johnpoz don't get me wrong I seriously respect you


one more time...
I did not share this to seek for advice, just I reported a fact...
(it will affect, everyone in the community)so the defensive behavior is unnecessary in this case...
this is not a pfSense theme yet, but it will be...(maybe the Wireshark isn't lying??!!)
so I’m not going to comment on that anymore, because the stiff rejection isn’t good...who is brave ask me for a "image 201H2" in PM
-
It really wouldn't surprise me if you aren't seeing the start of microsoft following what the other's have already done.
It seem's like everytime I update edge on a machine at the shop I have to go through the setting's and disable a bunch of crap and they advertise that edge is secure what a joke.
-
@DaddyGo said in MS activated DoH at the operating system level, in this "great" 20H2 release...?!:
this is not a pfSense theme yet, but it will be...
Not trying to be defensive, but no this will never be a pfsense anything.. What some OS does, be it linux, be it windows, be it beos or bsd, mac osx, etc. etc..
The only way this would have anything to do with pfsense would be if freebsd decided to only allow for doh, etc.. ;)
-
@johnpoz said in MS activated DoH at the operating system level, in this "great" 20H2 release...?!:
Not trying to be defensive, but no this will never be a pfsense anything..
You are absolutely right in this, but we defend against this in the background... or not(?!)
F.E.:
pfBlockerNG DoH server list feeds or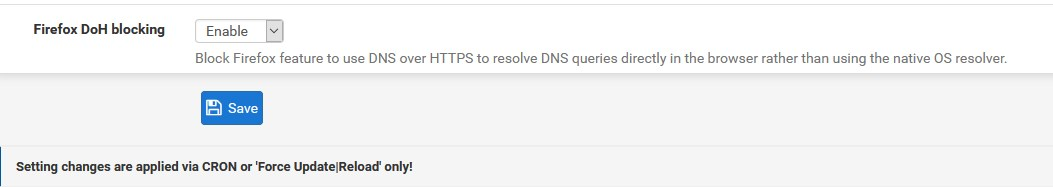
I came back, because I was worried about what I found...
FYI, John
The MS support team confirmed that the DoH is supported at OS level, in the "image" which I downloaded from our VLSC account.
Next year, everyone will get this great improvement in the 21H2 image and will not be able to be disabled from the registry.
https://techcommunity.microsoft.com/t5/networking-blog/windows-insiders-can-now-test-dns-over-https/ba-p/1381282
So no one can escape
 ..., -towards Linux only
..., -towards Linux only 
sorry for the bad news
-
Where does it state that is will on by default.. That you can do it is one thing, that you can't turn it off is another.
In that article you list, no where does it list that you are forced to use doh.. Just that the OS supports it..
That article states it will use doh if you have one of the following already set as your dns..
"Now that the DoH client is active, Windows will start using DoH if you already have one of these servers configured:"
And shows you how to setup and point to your own doh.. And sure it states once this is no longer insider you will not have to do the registry.. But I see nowhere that says or states that its going to use doh be it you like it or not..
I am just not seeing that.. Enabling doh to be used, and to use it if your pointing at some doh enabled IP is completely different than enabling it and using it without letting you not do it..
From everything I have read it not forced upon you.. If I point to 192.168.1.1 as my dns - that will be what is used.
What is a concern is what if you are using one of their doh IPs that they list - and you don't want to use doh? Because sure doh is more secure - its also freaking SLOWER!!! Guess the take is if your worried about dns speed or being able to see what is being queried from your local clients - you would use a local dns.
While they currently only list quad9, cloudflare and google for doh servers. Who wants to bet that MS has their own doh up and running before this goes live? ;)
-
@DaddyGo All these DNS providers, dangling this 'carrot'. Eat this one, it's more secure than that one... Free. My mom taught me that when someone says free, run away. It seems that no one is taught that anymore these days... But I digress. I agree with johnpoz, MS will have something, just wait. Genuine MS DNS servers doing DOH. Collecting market data they can cash in on. Nobody does something expensive for free. But as long as the OS abides by what I set for DNS servers, I'm good. And it looks like it will.
It looks like you are using Firefox. I would be more concerned with that, because it can use its own DNS and DOH and ignore what you have set in the OS. This is more worrisome than Windows DOH IMO. How dare they ignore what I have set on my computer. You can imagine parents who have set one of those DNS server services that block adult stuff, only to discover that the child's browser is not using it.
-
@Tzvia said in MS activated DoH at the operating system level, in this "great" 20H2 release...?!:
You can imagine parents who have set one of those DNS server services that block adult stuff, only to discover that the child's browser is not using it.
That is great example of this doh shit can shoot you in the foot for sure..
The browsers and other apps doing this is WAY worse than the OS supporting it.. So if the OS supports it - you think the browsers will adhere to using what your OS is using vs their own circumvention of the users wishes of using what dns they want?
And that is opt out vs opt in total utter BS!!! I don't care how freaking stupid they think the users are - we are doing this for their own good my f'ing ASS!!!!!
Its not spying on where your going - if you ask me for dns ;)
-
@johnpoz said in MS activated DoH at the operating system level, in this "great" 20H2 release...?!:
Where does it state that is will on by default..
Since we have been MS partner and insider for almost 15 years.
I called our contact person at the support group, here I got this information and point at the end of the sentence.
Since I also asked if it could be turned off in the registry, i got this link where it is strongly highlighted that it will not be possible to do so!I’m just giving you data and I’m not arguing, so that’s it for me.
It’s all about projecting the future forward, so as not to be surprised, John let’s talk about from this then in half a year or maybe one...The image (20H2 clean) can still be tried, I would only post anything after that...
+++edit:
I leave this machine hanging on a Wireshark and post some pcap files in a while to analyze and see...
right now this is most of what I do -
@Tzvia said in MS activated DoH at the operating system level, in this "great" 20H2 release...?!:
dangling this 'carrot'. Eat this one, it's more secure than that one... Free.
Thanks for this mindful post, do you have your own opinion and experience?
I’m happy to give you the "image", you give it a try and talk about it...
Carrots what? cool
-
Sounds to me that though it's supported, it's not enforced. What would happen to those of us using the resolver and talking to the roots?
-
@provels said in MS activated DoH at the operating system level, in this "great" 20H2 release...?!:
Sounds to me that though it's supported, it's not enforced. What would happen to those of us using the resolver and talking to the roots?
This is exactly my concern, but since I have the information from an official source, I have no doubt.
We manage nearly 800 Win OP system licenses and even more Office suite licenses.There’s direct contact at MS and it’s unbelievable, but that’s what they said on the phone.
The "mortals"
 will only get this "image" next year, via the system update, which will be mandatory (21H2).
will only get this "image" next year, via the system update, which will be mandatory (21H2).This raises serious concerns.
in the meantime anything can happen, but I thought I would share this with you...
I don't know anything about the server side and AD background yet, but they will definitely have a great idea for that too.
but anyway, all my evidence for the operation of DoH is above, now I dive deeper and share it here.
I don't usually open a topic here in the forum, but I thought it was important, it is an annoying statement DoH and I am confused by it...
The fact that everyone is just talking about it, but no one dares to try this bastard "image", ergo we deny...
BTW:
what interest I would have to spread horror news, this is a concrete experience and curiosity of course
-
@provels said in MS activated DoH at the operating system level, in this "great" 20H2 release...?!:
What would happen to those of us using the resolver and talking to the roots?
You have your windows machine resolving? You still point to something that is not a doh server even if you were.. You would point to loopback if you were running some resolving software on your windows machine.
I am for sure against this whole central dns nonsense - send us your dns queries, your isp is spying on you..
As no disable it.. Again to use doh have to point know the fqdn that is on the cert.. If I don't point one of the doh servers and I point to something else - how could it be using doh? If it looks up shit via doh while I specifically point to 192.168.1.1 - then yes that is the beginning of the end.. And I move to linux..
Its like the IPv6, you can not really disable it.. You can just not use it.. Even turning it "off" still leaves it enabled... That is how I think this doh support is going to work.
Guess we will see when 21H2 comes out - which isn't all that far from now..
BTW - give me a link to download it from, I will fire it up as a VM.
-
So the fear is that MS/whoever and browsers will hardcode DoH servers and they'll bypass unbound by using 443? Other than being a bit slower, what would be the harm? Most any website uses an encrypted connection anyway. ISPs can't read encrypted traffic anyway. Or am I not paranoid enough? :)
-
@provels said in MS activated DoH at the operating system level, in this "great" 20H2 release...?!:
and they'll bypass unbound
That is the concern yes.. I can filter, I can split dns when you point to my own dns. If you bypass I have to trust what that is - I can not resolve..
How do I even resolve my own local resources if your pointing to something on the public.. So I can not even resolve host.localdomain.tld if your going to ask some doh server on the public internet - even if I point to local dns.
The encryption or being slower not all that big of concern - but they deciding that they should bypass what I as the system owner and network operator set for my clients to use is the big issue here.
If you encrypt what is being asked - I can not even tell what is even being asked... Even from my own machine.
If they want to enable the possibility of using doh, that is fine - the concern is doing it without my explicit consent to do so... Maybe I don't want app xyz to be able to resolve something.. Yet again taking control away from the operator if you bypass what I say to use for dns, or use something else for any sort of lookups..
-
The MS article posted (from last spring) said it would only apply if certain DNS servers were configured. Doesn’t sound like that’s the case per the OP.
Down sides: 1) bypass any restrictions (malware detection, adult sites, betting, sports, whatever employees shouldn’t do on company time), 2) hopefully won’t bypass company network DNS (Windows domain, split DNS), 3) entities providing it get data from what web sites are visited (like Google DNS), and 4) no local DNS caching.
-
@johnpoz
It seems then that there would be plenty of web security gateway providers who would be against this, as well as all of corporate world.