pfSense blocking outgoing OpenVPN traffic
-
Hi,
We have a firewall with an OpenVPN incoming connection on port 1194.
Now I want from behind this fw to connect to a remote system with also port 1194 but the traffic never arrives there. An other external system does work, but that uses port 1195.
Is it possible to get this working?
Should I make some nat-rule or so? -
You have to break down where it's failing. My bet is on routing.
-
My money are on the "dual use" of 1194
/Bingo
-
pfSense/OpenVPN is using a random dynamic port for client connections by default, you can have hundreds outgoing OpenVPN connections to port 1194 with no problem.
-Rico
-
Given those 2 1194s are on different systems means that is not a problem. The IP sockets are based on port number and address. The source port is a random number that is not reserved for any service.
-
@rico
@JKnott
I read it as he had an OpenVPN "Server daemon" running on his fw, listening on incomming 1194.And ... dooh (seems my money are lost)

He uses a random outbound port towards the "other" 1194.My initial thought was that the OpenVPN Server daemon took exclusive ownership of 1194, but that would be inbound.
Always glad to discover new stuff
/Bingo
-
Too many unknowns. By default, no outgoing traffic is blocked on PFsense, so without more insight into both networks, all we can do is start looking at the usual suspects. Is the initial connection from the client to the server being made? If not, I'd start looking at the logs on the edge firewall on the client-side. Is there an edge device on the remote side also? If so, that's another point of failure to be investigated along with PFsense on the remote end.
If the tunnel is up, but no traffic is passing, then we'd need to start looking at the server-side config, routing tables, and firewall rules on both ends including edge devices.
-
To be more specific: I have 3 locations: my home, a work location and where I host my servers. All 3 locations have OpenVPN server, my home at port 1195 the other 2 at port 1194. From home I can connect to both locations and from my work I can access my home. But from work I cannot reach where my server is hosted. Someone has been packetsniffing there and no traffic comes in from my work location.
So I assumed that the server at work is blocking the outgoing traffic to my hostsite. All sites run latest version 64-bit. -
@warnerthuis said in pfSense blocking outgoing OpenVPN traffic:
To be more specific: I have 3 locations: my home, a work location and where I host my servers. All 3 locations have OpenVPN server, my home at port 1195 the other 2 at port 1194. From home I can connect to both locations and from my work I can access my home. But from work I cannot reach where my server is hosted. Someone has been packetsniffing there and no traffic comes in from my work location.
So I assumed that the server at work is blocking the outgoing traffic to my hostsite. All sites run latest version 64-bit.Thanks for the info. Although, it's still way too high level. What is the topology between the 3 sites... mesh, hub-and-spoke, etc? PKI or Shared Key setup? Are all three locations running PFsense at the edge? Are the OpenVPN server(s) running on PFsense or something else?
-
@marvosa The 3 sites are at different geographical locations, so in between is 'internet'. All 3 are running on PFSense. Home is behind a NAT on a DMZ with everything forwarded on a physical machine. The other 2 are connected directly to internet. Work is running on a physical machine, hosting server is running on a virtual machine on ProxMox.
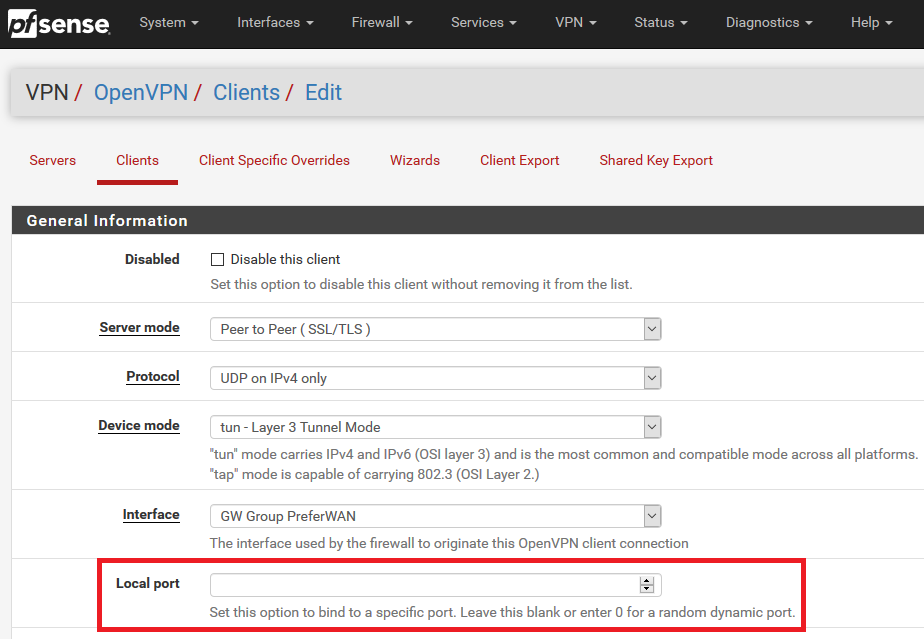
At work it is layer3-tunnel mode, TLS-key, encryption AES-265-CBC, NCP AES-128-GCM, servermode: Remote Access ( SSL/TLS + User Auth ) -
@warnerthuis So, the issue lies in the tunnel between work and the hosting site. Post the server1.conf from the server and client1.conf from the client.