LAN Connection Drops when OPENVPN(client) connected
-
Hi Experts!
I'm trying to figure out what went wrong here, i have added in a openvpn profile and manage to get openvpn connection up. I'm able to see the IP(internal) issued by the connection as well as public ip of openvpn. Problem comes in when openvpn is up, i lost my internet connection on my lan device unless i turn off my openvpn interface.
I've read a few tutorial but nothing seems to work. i've done the following:-
- Firewall rules: Lan connection for any to openvpn gateway
- NAT: manual, duplicating all wan connection to vpn
Any expert able to help me out here?
*OPENVPN Profile: Site to Site. Not subscribe VPN service.
Thanks for reading.

-
@enjawd said in LAN Connection Drops when OPENVPN(client) connected:
Firewall rules: Lan connection for any to openvpn gateway
This rule does not allow access to pfSense itself. So if your LAN devices are configured to use pfSense for DNS resolution, they will be blocked.
-
@viragomann hi! Sorry I’m fairly new to pfsense, how do I go about fixing this? I saw guide for VPN configuration seems like they only did NAT outbound to manual and set firewall rules to VPN gateway for OpenVPN interface
-
@enjawd said in LAN Connection Drops when OPENVPN(client) connected:
I saw guide for VPN configuration seems like they only did NAT outbound to manual and set firewall rules to VPN gateway for OpenVPN interface
And those guides suck in my professional and personal opinion ;)
There is no reason to use manual, just setup a hybrid to nat traffic you want to go out your vpn connection.
Forcing traffic via a firewall, ie policy routing without mentioning any thing about rules above that to allow access to say pfsense or other local networks.
I would suggest you read over the policy routing part of the docs.
https://docs.netgate.com/pfsense/en/latest/multiwan/policy-route.html
Pay attention to the bypass policy route section
https://docs.netgate.com/pfsense/en/latest/multiwan/policy-route.html#bypassing-policy-routing -
@johnpoz
 im not sure which part im doing wrongly. i still cant get my lan device connected to vpn
im not sure which part im doing wrongly. i still cant get my lan device connected to vpn 
-
@enjawd
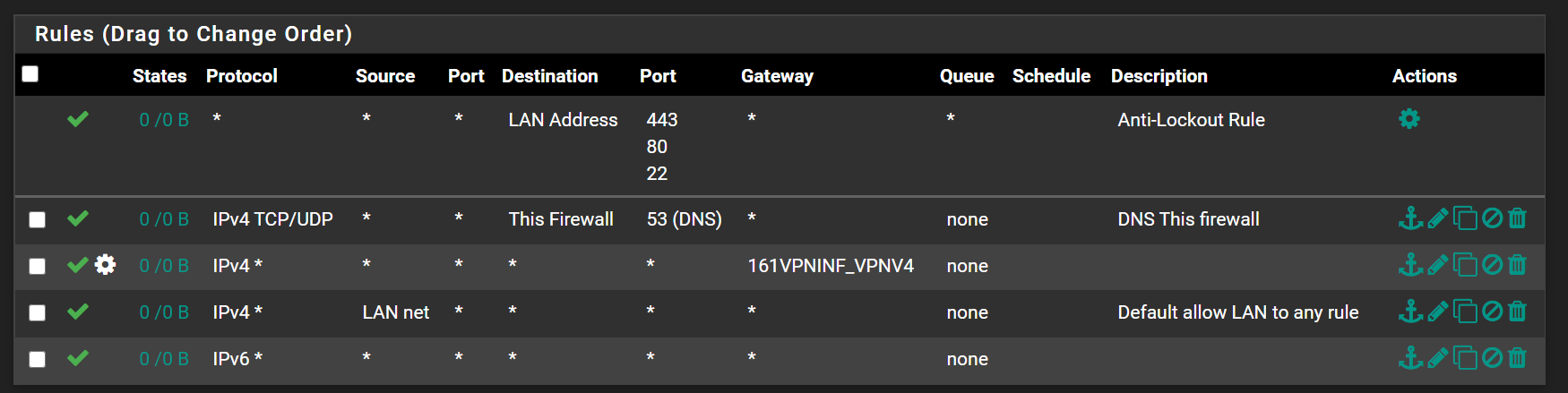
This LAN rule with stated gateway (policy routing) directs all traffic to the VPN server.
To allow DNS or other internal traffic you need an additional rule above of this one for internal access.
Don't know, what you need to access internal, if it's DNS to pfSense only add a rule for TCP/UDP protocol, dest = this firewall, dest. port 53 to the top of the rule set. -
@viragomann i realize i might need to rephrase my topic
 ...
...What I'm trying to achieve is for my computer to access the VPN connection. But when i set the NAT rule for LAN (gateway vpn selected), all my pc internet drop. When i disable the rule, internet connection resume for the pc's.
I don't need to access anything internal but just needed my pc to connect to the VPN that's all so it can access some files in the network
-
@enjawd
I was talking about DNS access. Usually people use DHCP on pfSense to set the network settings on the internal devices and by default this configures pfSense as DNS server.
So if your configuration is like this, the devices are configured to access pfSense LAN IP for DNS resolution and you need to allow it!!!Since you didn't tell us your settings, we have to assume, it is like this default one.
So simply establish the VPN and try to access an internet resource by its IP address, e.g. ping 8.8.8.8
If that works you will know it's a DNS issue, if it doesn't we can look further. -
This is the mini OpenVPN set up guide.
Good news : it's from the guys who made it.
Backup your config, do exactly what's show in the video, and check that's is working.
If still no ok, at least you know that's it's not 'pfSense related'.See also the other two official video's. They date a little bit, but still very valid.
-
@viragomann omg i've reach a dead end, i've no no idea what else i can try to do. with openvpn connection enabled, im still able to ping 8.8.8.8 via ssh but my LAN device still has no internet. So i believe it might have something to do with pfsense dns on my lan? what ip address do i need to specify on my dns for openvpn int? can i leave it at 8.8.8.8, tried this dns server but lan still does not have internet
-
@enjawd said in LAN Connection Drops when OPENVPN(client) connected:
im still able to ping 8.8.8.8 via ssh
via SSH? You mean pinging from pfSense? You should test it on a LAN device.
So as mentioned if your LAN devices use pfSense for DNS resolution, you have to allow it. So post your LAN rules, please, that we can verify.
And tell us what your intention is. Do you want to direct the whole traffic over the VPN or only partial?
-
@viragomann Yeah i did a ping from pfsense. on LAN device i cant ping 8.8.8.8.
My goal is to setup some device to go thru VPN network, while the rest will go thru my isp.
This is my current setting. For now i've set it as all device will have VPN access just to get this working first.
-
How would those rules allow access to 8.8.8.8 from a client?
Your rule there allows access to firewall IPs (sure not going to be 8.8.8.8)
Then you force everything out the vpn.. And don't even see any hits on your firewall rule or you access to the firewall for dns.
If you want clients to be able to go to the 8.8.8.8, put a rule above the vpn gateway rule that allows that..
Not sure why your vpn would not allow you to ping 8.8.8.8 though?
None of the those rules show any hits at all, are you even going through pfsense? I would expect your antilockout to show something..
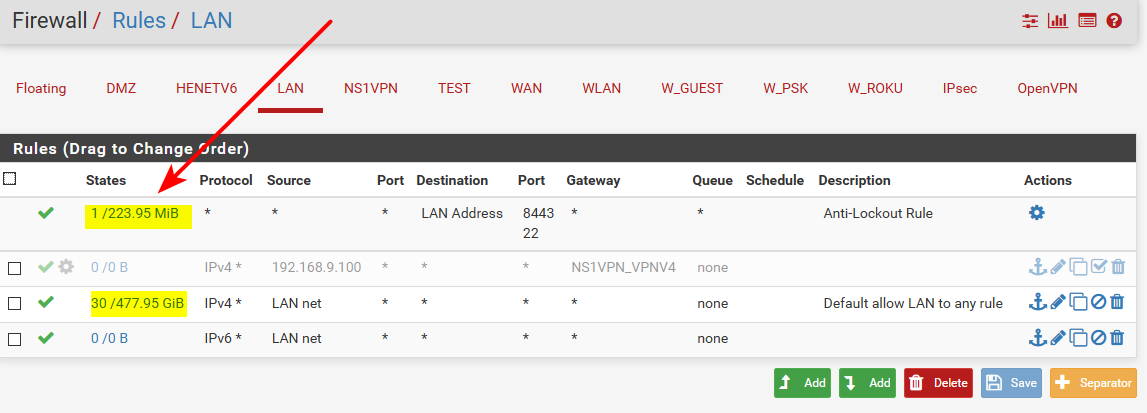
See how my antilock out shows traffic and currently 1 state.. While my normal rule shows 30 current states with 477GB moved since last the counters were reset.
-
@enjawd said in LAN Connection Drops when OPENVPN(client) connected:
Yeah i did a ping from pfsense. on LAN device i cant ping 8.8.8.8.
So you're not able to go through the VPN. If you can't ping 8.8.8.8 it' nothing with DNS.
The VPN is connected and the VPN gateway is shown as up?
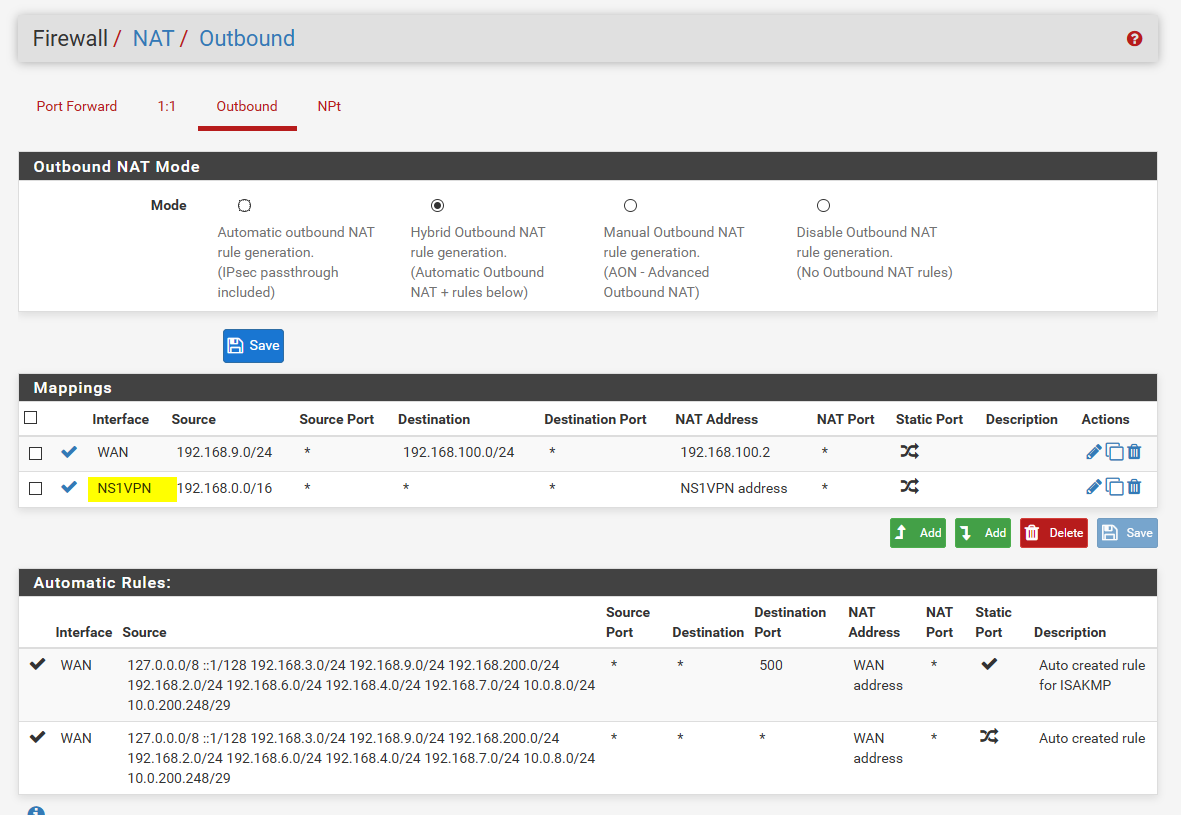
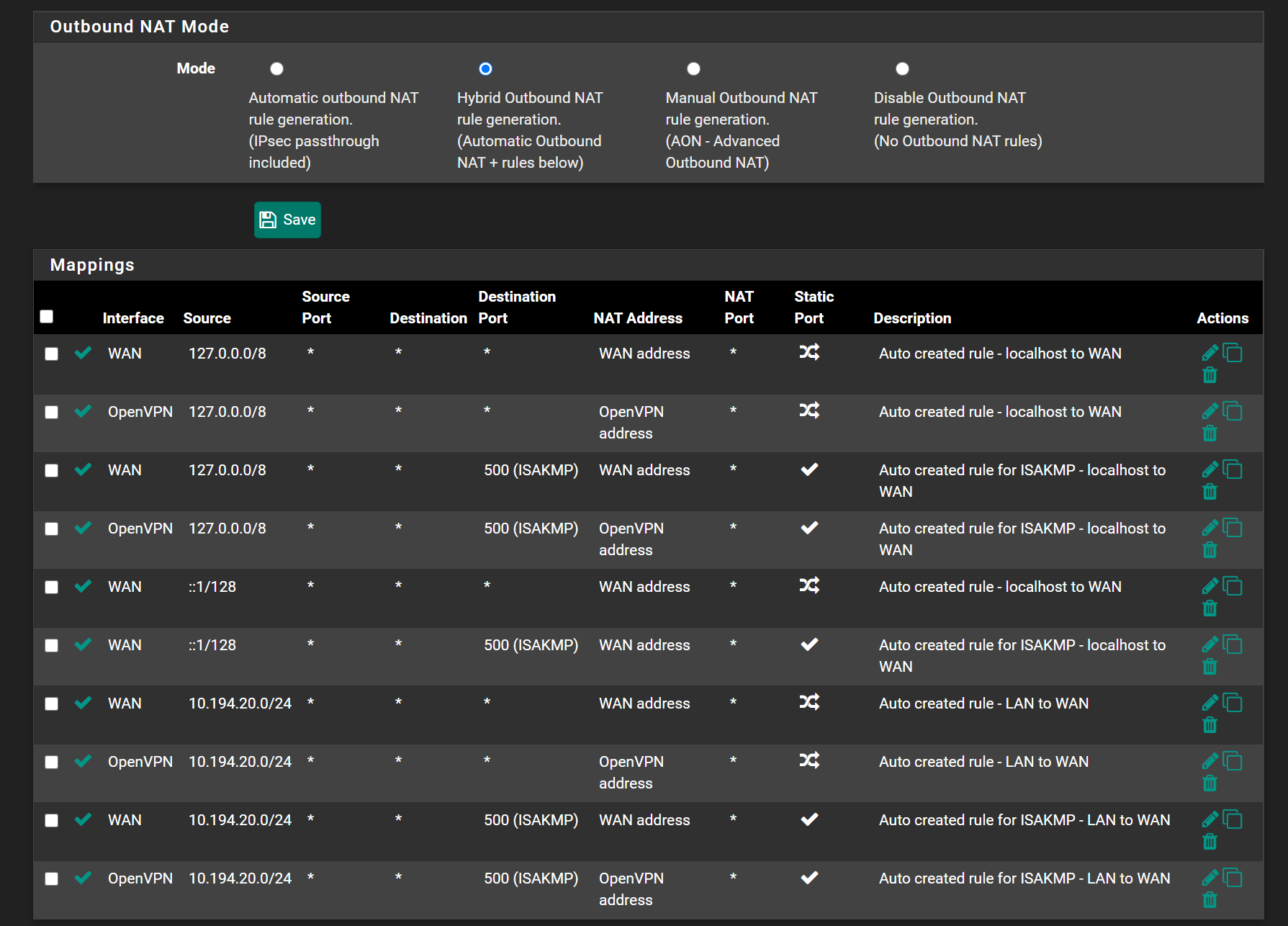
So recheck oubound NAT. Is it in hybrid or manual mode? Post the rules. -
@viragomann said in LAN Connection Drops when OPENVPN(client) connected:
you're not able to go through the VPN. If you can't ping 8.8.8.8 it' nothing with DNS.
The VPN is connected and the VPN gateway is shown as up?
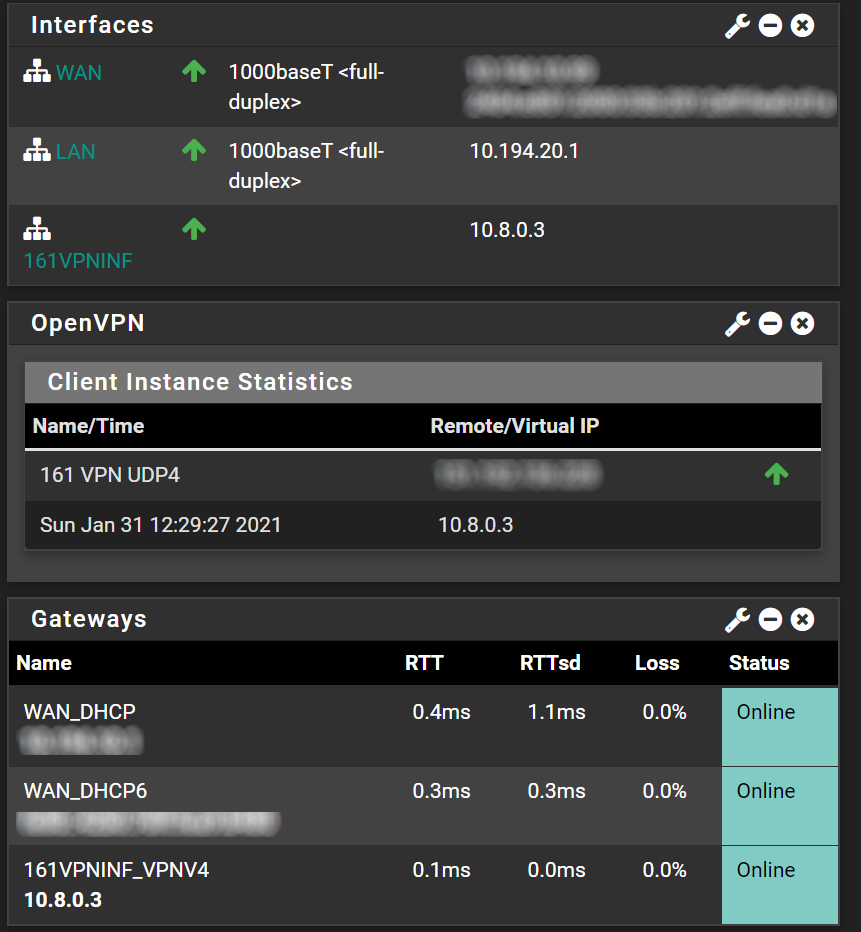
So recheck oubound NAT. Is it in hybrid or manual mode? Post the rules.@viragomann i've attach screenshot of dashboard as well as NAT setting. On OpenVPN, the remote/virtual is correct ip of my remote connection
-
@enjawd
You have assigned the interface 161VPNINF to your client, so also have to use this interface in the outbound NAT. -
Go back to auto, deleted all the other rules. then go to hybrid and create your rule for your boubound nat for your vpn.