SG3100 Single WAN NAT Issues.
-
DDNS is public, how many public IPs do you have?
Do you know that 172.16.0.0/12 is not reachable through the Internet?
So, the DDNS will have your public IP address, which is your Internet IP address.The connections will reach your Internet IP address, and then the port forward will forward the connection to 172.30.30.40, or 172.30.30.50.
Port forward1:
Source any
Source port any
Destination Public IP (Your WAN IP, the IP your ISP gives to you, which is the DDNS IP).
Destination port 23
Forward to 172.30.30.40 on port 23 or any other port that telnet may be running if you changed it.Port forward2:
Source any
Source port any
Destination Public IP (Your WAN IP, the IP your ISP gives to you, which is the DDNS IP).
Destination port 223
Forward to 172.30.30.50 on port 223. -
@mcury My Public IP address is issued from the ISP. It is a 64.248.xxx.xx
example.com is hosted by WEB Hosting company
ddns.example.com is at my home hosting a amateur radio hobby server that people connect to from around the world.
I also operate my station remotely (hardware control). I also have friends ask to operate the station.My LAN network is similar to 172.30.30.1/24 my guest WiFi is 172.30.32.1/24. I know these are none routable IP address. I wanted to be off the beaten path.
I have the rules setup the way that you have described to a T!! I know from the internet (Public), the port forwarding will work perfectly!
You said that if I place ddns.example.com in the "Host overide" people will be able to get to the services on 175.30.30.40, but what happens if I try to get to ddns.example.com:18080 on 172.30.30.30
-
@wc2l said in SG3100 Single WAN NAT Issues.:
You said that if I place ddns.example.com in the "Host overide" people will be able to get to the services on 175.30.30.40, but what happens if I try to get to ddns.example.com:18080 on 172.30.30.30
The "Host override", is part of the Split DNS.
It's just for devices inside your network, to resolve the internal IP address directly.
Destination ddns.example.com at port 18080 will resolve to 172.30.30.30 port 18080, no need to port forward or anything.People on the Internet, won't use the "Host override", because they are using other DNS server.
Destination ddns.example.com at port 18080 will resolve to 64.248.xxx.xx port 18080.
Your Pfsense will receive that packet on port 18080, and then the port forward will work, forwarding the traffic to your internal server. -
@mcury I was just told that all I had to do is "Enable NAT Reflection for 1:1 NAT and Enable automatic outbound NAT for Reflection are set"
I did this and now it works! All of the other stuff appears to be working. Now I can look at pfBlocker at some point. Let me see how things go for a bit. I
-
This is considered a "hack", tried to show you the recommended way to do it.. But somehow I failed to explain, or you fail to understand, not sure what happened.
But hey, if it's working and you are happy, who am I to say otherwise.
https://docs.netgate.com/pfsense/en/latest/nat/reflection.html
NAT Reflection Caveats NAT reflection is a hack as it loops traffic through the firewall when it is not necessary. Because of the limited options pf allows for accommodating these scenarios, there are some limitations in the pfSense NAT + Proxy reflection implementation. Port ranges larger than 500 ports do not have NAT reflection enabled in NAT + Proxy mode, and that mode is also effectively limited to only working with TCP. The other modes require additional NAT to happen if the clients and servers are connected to the same interface of the firewall. This extra NAT hides the source address of the client, making the traffic appear to originate from the firewall instead, so that the connection can be properly established. Split DNS is the best means of accommodating large port ranges and 1:1 NAT. Maintaining a split DNS infrastructure is required by many commercial firewalls even, and typically isn’t a problem.Split DNS A preferable alternative to NAT reflection is deploying a split DNS infrastructure. Split DNS refers to a DNS configuration where, for a given hostname, public Internet DNS resolves to public IP address, and DNS on the internal network resolves to the internal, private IP address. The means of accommodating this will vary depending on the specifics of an organization’s DNS infrastructure, but the end result is the same. NAT reflection is not necessary because hostnames resolve to the private IP addresses inside the network and clients can reach the servers directly. Split DNS allows servers to see the true client IP address, and connections between servers and clients in the same subnet will go directly, rather than unnecessarily involving the firewall. The only case that does not work properly with split DNS is when the external and internal port numbers are different. With split DNS, the port number has to be the same in both places. -
@mcury OK well interestingly, the Guest WiFi may have stopped working. I need to figure out what caused it..
I can go back and uncheck it.. I will set the host over-ride. I'm a newbie and learning slowly.. If there was a way we could do this together would save some time ;-)
-
@wc2l said in SG3100 Single WAN NAT Issues.:
@mcury OK well interestingly, the Guest WiFi may have stopped working. I need to figure out what caused it..
I can go back and uncheck it.. I will set the host over-ride. I'm a newbie and learning slowly.. If there was a way we could do this together would save some time ;-)
Sure, I like to help.. why not? Also, my life has been destroyed by this pandemic, so I'm the one who is being helped by you.
What are your doubts?
-
@mcury lack of my skills.. This is a new world to me ;-)
OK, It appears that the guest WiFi VLAN has stopped working. My LAN WiFi is working. I didn't think that anything I did would have affected the Guest WiFi (using my phone as a test unit).
Not going to last too much tonight. I'm early riser. If you want, you can always email WC2L at YCCC dot ORG. I'm guessing most of this a couple of check marks somewhere. Will
-
@mcury Since we setup the split DNS, is there something I need to do to get the guest WiFi to work again?? I can't seem to get to the Internet, ddns.example.com or pretty much anything.. It is handing out DHCP from the SG3100. I'm guessing it is a routing issue. Just don't know how to address it.
-
Show some screenshots of your config.
And no, split DNS wouldn't cause internet outage.
-
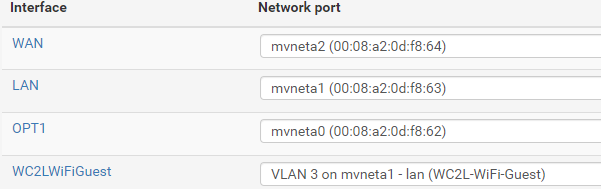
@mcury
Not sure what screens you want to see.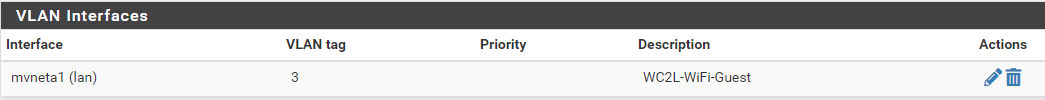
-
@wc2l Can users in this guest WiFi ping 8.8.8.8?
-
@mcury NOPE

-
@wc2l Are these users getting IP address from the DHCP?
-
@mcury Yes.. I just connected a Surface to the Guest WiFi..
It got the expected IP address -
@wc2l Ok, it was working before? Problem started with the host override inside DNS Resolver?
Try to remove the host override and try again. -
@mcury no change
Both ways shows that DNS servers are not responding
DNS_PROBE_FINISHED_NO_INTERNET -
@wc2l Ok, what DNS server are these users using?
Are your firewall rules allowing connections to this DNS server on port 53 UDP/TCP? -
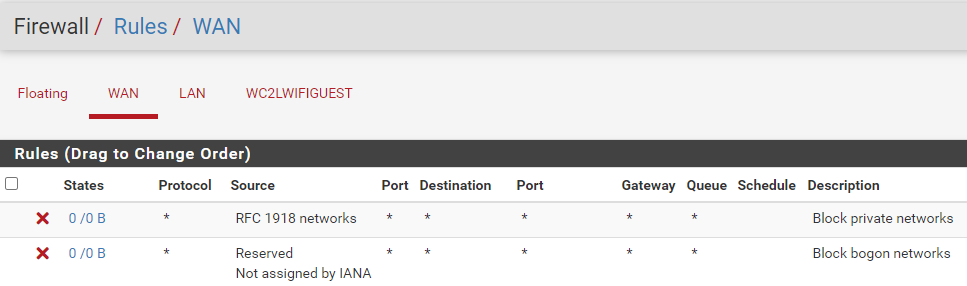
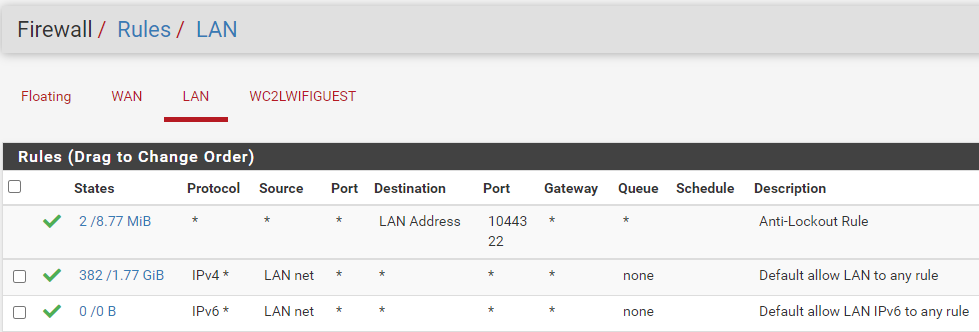
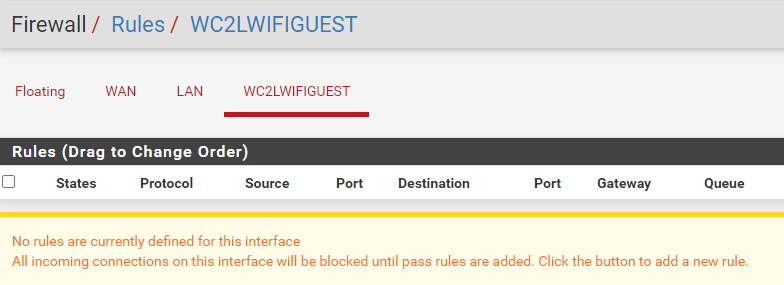
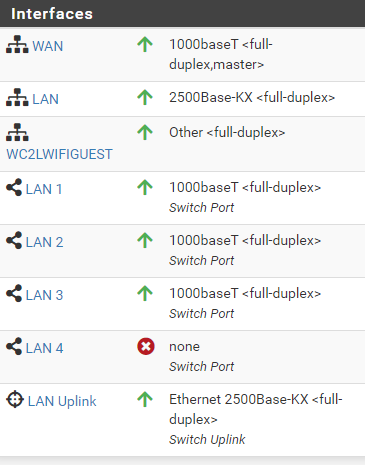
-
@wc2l You need firewall rules inside this last image, WC2LWIFIGUEST
You need to allow the GUEST network to go out to the internet.Do you see the difference between LAN and WC2LWIfIGUEST?
The last two rules in LAN, try to create them inside WC2LWIfIGUEST, this will allow internet access for these guests.